当前位置:网站首页>A complete attack chain
A complete attack chain
2022-07-05 04:57:00 【zh0u9527】
A complete attack chain
The complete attack chain includes information collection 、 Exploit 、 Build a stronghold 、 Elevated privileges 、 Authority maintenance 、 Move horizontally 、 Seven steps with clear traces , Although this site has only experienced the first four steps , But it is also highly representative , Combine vulnerabilities to form an attack chain , Take down the administrative authority .
Full band stop : Remember an authorized network attack and defense drill ( On )
Full band stop : Remember an authorized network attack and defense drill ( Next )
边栏推荐
- mysql審計日志歸檔
- 2021 electrician cup idea + code - photovoltaic building integration plate index development trend analysis and prediction: prediction planning issues
- 2022/7/1学习总结
- Autocad-- dynamic zoom
- 669. Prune binary search tree ●●
- Unity intelligent NPC production -- pre judgment walking (method 1)
- 中国溶聚丁苯橡胶(SSBR)行业研究与预测报告(2022版)
- Rip notes [rip three timers, the role of horizontal segmentation, rip automatic summary, and the role of network]
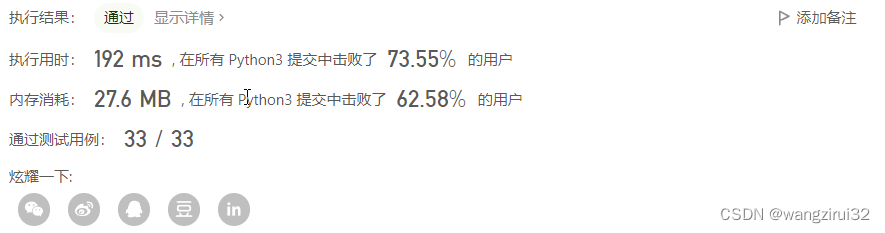
- 【acwing】836. Merge sets
- PR first time
猜你喜欢
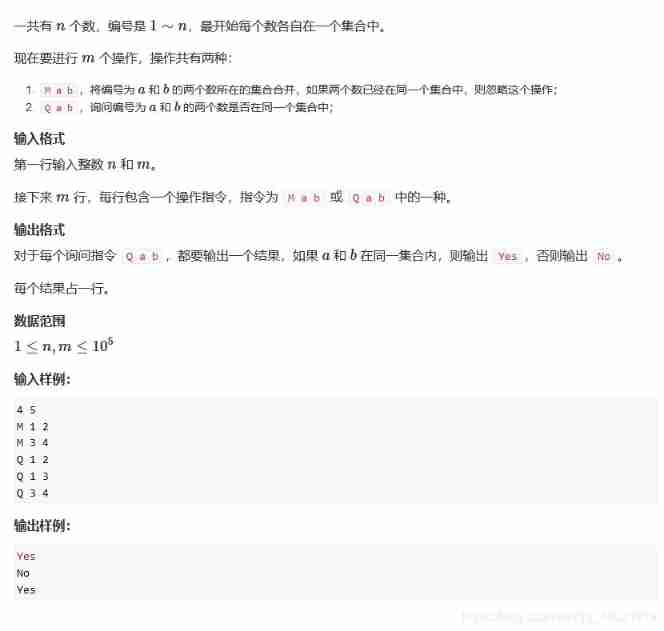
【acwing】836. Merge sets
![[groovy] closure (closure call is associated with call method | call () method is defined in interface | call () method is defined in class | code example)](/img/03/329adb314606f29c8a4cb2260e84c8.jpg)
[groovy] closure (closure call is associated with call method | call () method is defined in interface | call () method is defined in class | code example)
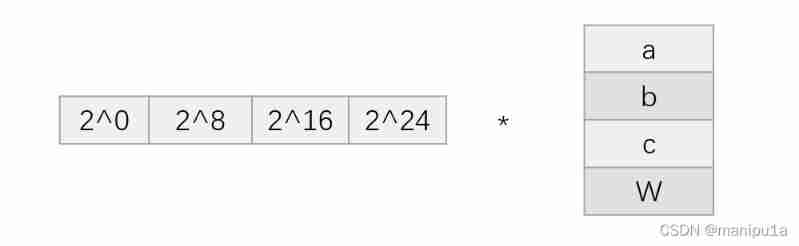
Understand encodefloatrgba and decodefloatrgba
2022 thinking of mathematical modeling D problem of American college students / analysis of 2022 American competition D problem
【Leetcode】1352. Product of the last K numbers

Introduction to JVM principle and process

JVM 原理和流程简介

XSS injection
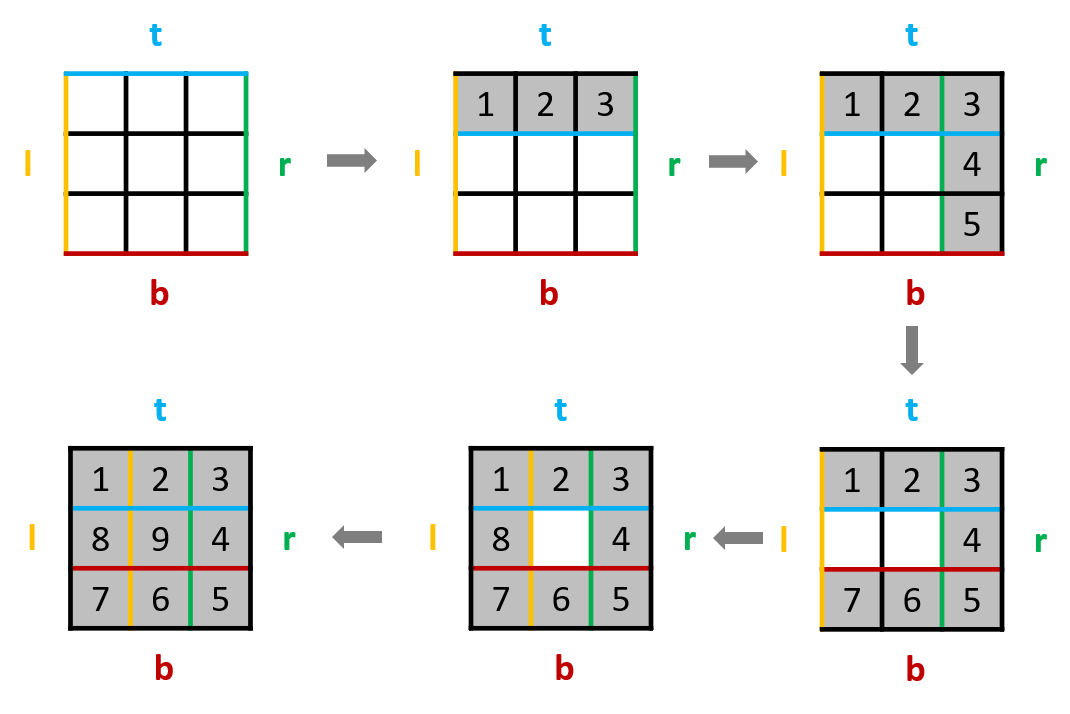
54. Spiral matrix & 59 Spiral matrix II ●●
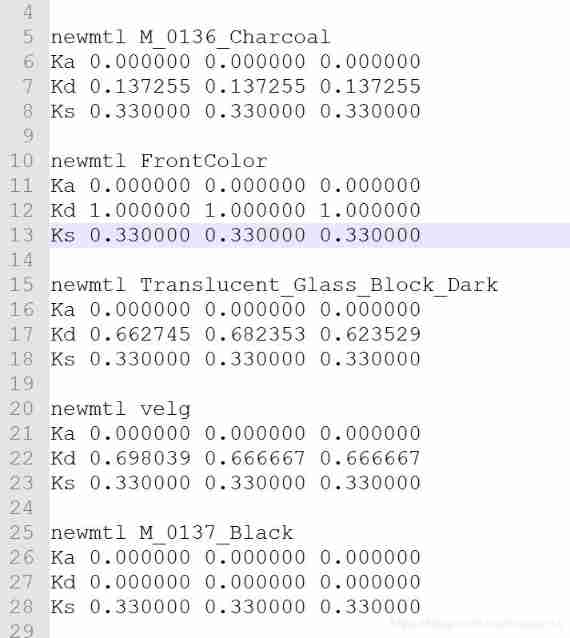
Use assimp library to read MTL file data
随机推荐
Number theoretic function and its summation to be updated
[groovy] closure (closure call | closure default parameter it | code example)
How much do you know about 3DMAX rendering skills and HDRI light sources? Dry goods sharing
2022 thinking of Mathematical Modeling B problem of American college students / analysis of 2022 American competition B problem
AutoCAD - scaling
54. Spiral matrix & 59 Spiral matrix II ●●
[ideas] 2021 may day mathematical modeling competition / May Day mathematical modeling ideas + references + codes
Unity and database
中国金刚烷行业研究与投资预测报告(2022版)
Detailed explanation of the ranking of the best universities
2021 Higher Education Club Cup mathematical modeling national tournament ABCD problem - problem solving ideas
django连接数据库报错,这是什么原因
Fluent objects and lists
Sqlserver stored procedures pass array parameters
Research and forecast report on China's solution polymerized styrene butadiene rubber (SSBR) industry (2022 Edition)
Introduction to JVM principle and process
2022 American College Students' mathematical modeling ABCDEF problem thinking /2022 American match ABCDEF problem analysis
C # perspective following
Establish cloth effect in 10 seconds
Looking at Chinese science and technology from the Winter Olympics: what is the mystery of the high-speed camera that the whole people thank?