当前位置:网站首页>Distributed cache architecture - cache avalanche & penetration & hit rate
Distributed cache architecture - cache avalanche & penetration & hit rate
2022-07-05 12:32:00 【vx-Yang_ Gaige】
Cache penetration and cache avalanche
Cache avalanche
The cause of cache avalanche
Cache avalanche is simply understood as : Due to the original cache failure ( Or the data is not loaded into the cache ), Period before new cache ( Cache normally from Redis In order to get , Here's the picture ) All requests that should have access to the cache are going to query the database , And for databases CPU And memory , Serious will cause database downtime , Cause the system to crash .
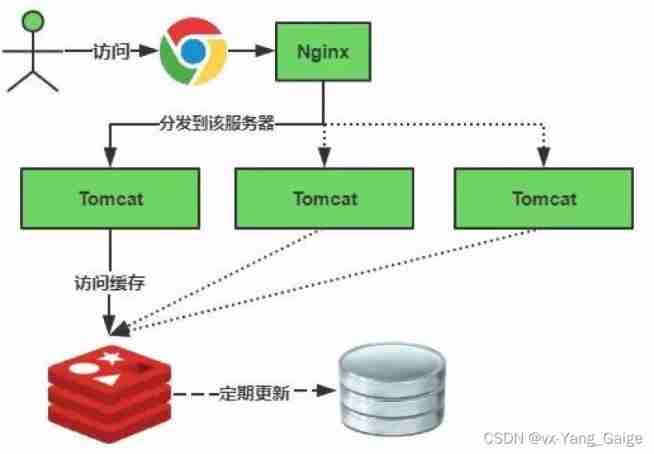
When the cache fails, see the figure below :
边栏推荐
- What is digital existence? Digital transformation starts with digital existence
- Instance + source code = see through 128 traps
- Embedded software architecture design - message interaction
- Principle and performance analysis of lepton lossless compression
- Four operations and derivative operations of MATLAB polynomials
- Understanding the architecture type of mobile CPU
- The solution of outputting 64 bits from printf format%lld of cross platform (32bit and 64bit)
- MySQL stored procedure
- Intern position selection and simplified career development planning in Internet companies
- Detailed steps for upgrading window mysql5.5 to 5.7.36
猜你喜欢
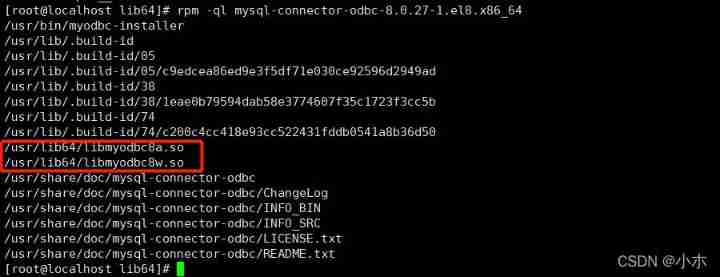
ZABBIX ODBC database monitoring
Master the new features of fluent 2.10
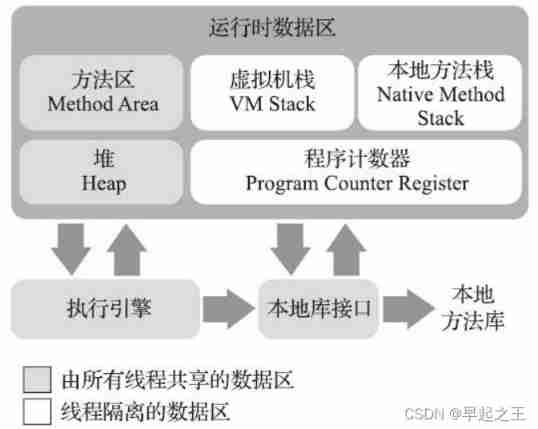
Learn the memory management of JVM 02 - memory allocation of JVM
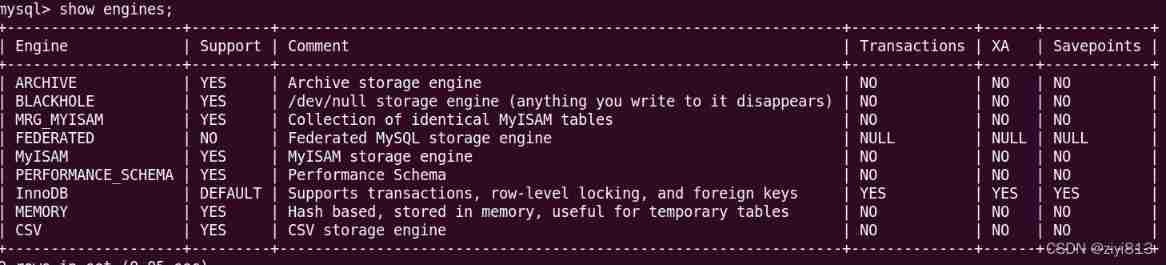
MySQL storage engine
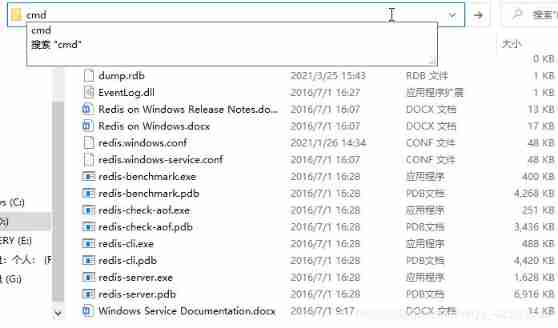
Redis clean cache

什么是数字化存在?数字化转型要先从数字化存在开始
Matlab imoverlay function (burn binary mask into two-dimensional image)
C language structure is initialized as a function parameter
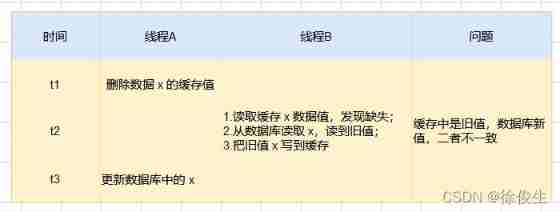
Solve the problem of cache and database double write data consistency
How to clear floating?
随机推荐
信息服务器怎么恢复,服务器数据恢复怎么弄[通俗易懂]
Tabbar configuration at the bottom of wechat applet
Four operations and derivative operations of MATLAB polynomials
Redis highly available sentinel mechanism
Halcon template matching actual code (I)
Is investment and finance suitable for girls? What financial products can girls buy?
Yum only downloads the RPM package of the software to the specified directory without installing it
Select drop-down box realizes three-level linkage of provinces and cities in China
Want to ask, how to choose a securities firm? Is it safe to open an account online?
Handwriting blocking queue: condition + lock
[superhard core] is the core technology of redis
Redis's memory elimination mechanism, read this article is enough.
struct MySQL
Learn the memory management of JVM 02 - memory allocation of JVM
Seven ways to achieve vertical centering
The survey shows that traditional data security tools cannot resist blackmail software attacks in 60% of cases
Introduction to GNN
Pytoch through datasets Imagefolder loads datasets directly from files
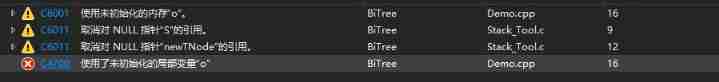
Instance + source code = see through 128 traps
Get the variable address of structure member in C language