当前位置:网站首页>[sword finger offer] 60 Points of N dice
[sword finger offer] 60 Points of N dice
2022-07-06 18:18:00 【LuZhouShiLi】
The finger of the sword Offer 60. n The number of dice
subject
hold n A dice on the ground , The sum of the points on the up side of all dice is s. Input n, Print out s The probability that all possible values of the . You need to return the answer with an array of floating-point numbers , Among them the first i The elements represent this n The number of points that a die can roll i The probability of the smaller one .
Ideas
- First, use the first dimension of the array to represent the stage , That is, throw a few dice
- Then use the second dimension representation of the array to roll these dice , Possible points
- The value of the array represents , The number of points in this stage
Code
class Solution {
public:
vector<double> dicesProbability(int n) {
int dp[12][70];
memset(dp,0,sizeof(dp));// All initialization 0
for(int i = 1; i <= 6; i++)
{
dp[1][i] = 1;// Status array initialization
}
for(int i = 2; i <= n; i++)
{
// The maximum number of points It must be 6 * i
for(int j = i; j <= 6 * i; j++)
{
for(int cur = 1; cur <= 6; cur++)
{
if(j - cur <= 0)
{
break;
}
// But look No i A dice , Points may be 1 2 3 4 5 6 So points j The number of occurrences is determined by the end of the throw i - 1 A dice Corresponding points j - 1 j - 2 j - 6 The sum of the number of occurrences is transformed
dp[i][j] += dp[i - 1][j - cur];
}
}
}
int all = pow(6,n);// All possibilities
vector<double> ret;
for(int i = n; i <= n * 6; i++)
{
ret.push_back(dp[n][i] * 1.0 / all);
}
return ret;
}
};
边栏推荐
- Distiller les connaissances du modèle interactif! L'Université de technologie de Chine & meituan propose Virt, qui a à la fois l'efficacité du modèle à deux tours et la performance du modèle interacti
- 编译原理——预测表C语言实现
- Easy to use PDF to SVG program
- Heavy! Ant open source trusted privacy computing framework "argot", flexible assembly of mainstream technologies, developer friendly layered design
- IP, subnet mask, gateway, default gateway
- 2022暑期项目实训(三)
- Coco2017 dataset usage (brief introduction)
- celery最佳实践
- 传输层 拥塞控制-慢开始和拥塞避免 快重传 快恢复
- F200 - UAV equipped with domestic open source flight control system based on Model Design
猜你喜欢
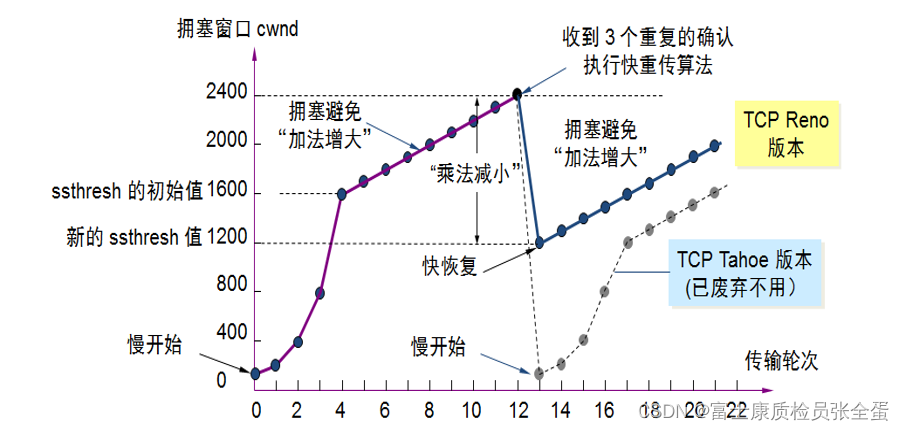
传输层 拥塞控制-慢开始和拥塞避免 快重传 快恢复
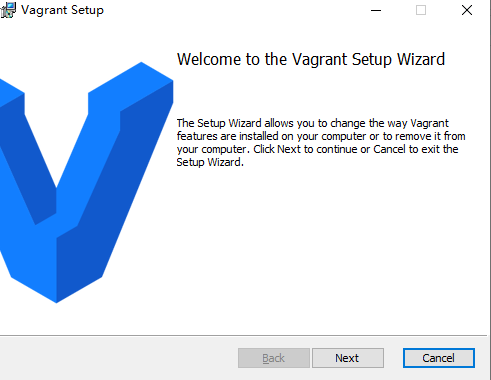
虚拟机VirtualBox和Vagrant安装

Four processes of program operation

I want to say more about this communication failure

Olivetin can safely run shell commands on Web pages (Part 1)
Kivy tutorial: support Chinese in Kivy to build cross platform applications (tutorial includes source code)

带你穿越古罗马,元宇宙巴士来啦 #Invisible Cities
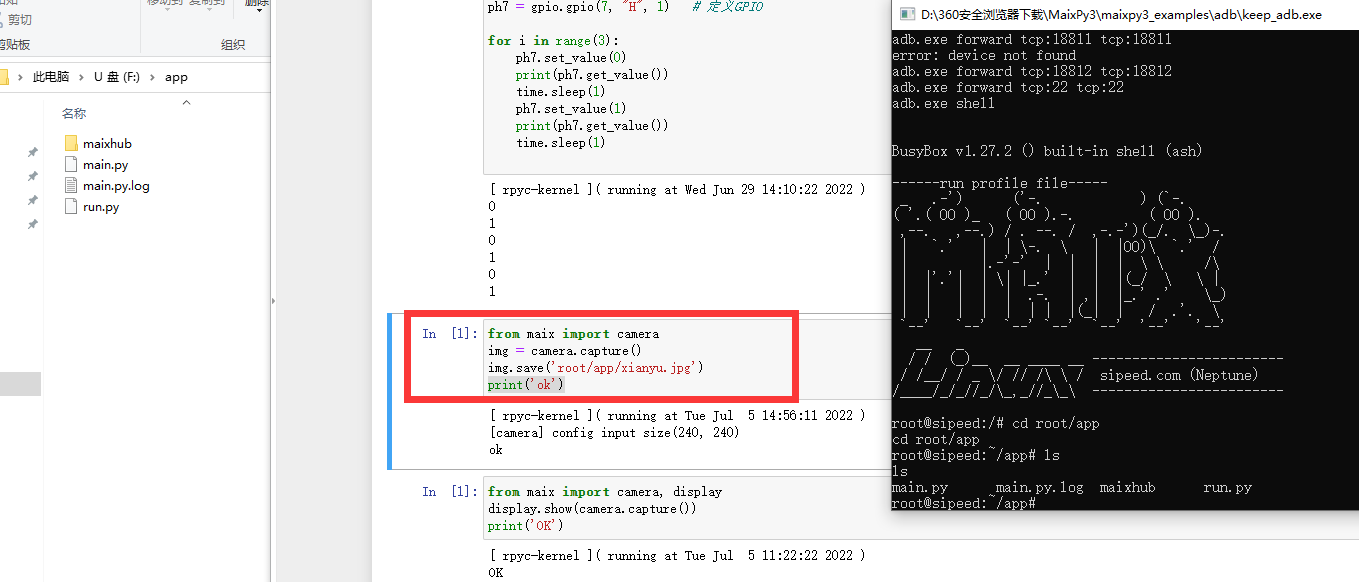
Maixll dock camera usage

关于这次通信故障,我想多说几句…
SAP Fiori 应用索引大全工具和 SAP Fiori Tools 的使用介绍
随机推荐
F200——搭载基于模型设计的国产开源飞控系统无人机
STM32+ESP8266+MQTT协议连接OneNet物联网平台
CRMEB 商城系统如何助力营销?
win10系统下插入U盘有声音提示却不显示盘符
Maixll-Dock 摄像头使用
On time and parameter selection of asemi rectifier bridge db207
Stealing others' vulnerability reports and selling them into sidelines, and the vulnerability reward platform gives rise to "insiders"
Recommend easy-to-use backstage management scaffolding, everyone open source
TOP命令详解
Prophet模型的简介以及案例分析
epoll()无论涉及wait队列分析
Distiller les connaissances du modèle interactif! L'Université de technologie de Chine & meituan propose Virt, qui a à la fois l'efficacité du modèle à deux tours et la performance du modèle interacti
F200 - UAV equipped with domestic open source flight control system based on Model Design
MS-TCT:Inria&SBU提出用于动作检测的多尺度时间Transformer,效果SOTA!已开源!(CVPR2022)...
Fleet tutorial 13 basic introduction to listview's most commonly used scroll controls (tutorial includes source code)
Jielizhi obtains the currently used dial information [chapter]
2019阿里集群数据集使用总结
当保存参数使用结构体时必备的开发技巧方式
Cocos2d Lua 越来越小样本 内存游戏
Jielizhi obtains the customized background information corresponding to the specified dial [chapter]