当前位置:网站首页>Deployment of external server area and dual machine hot standby of firewall Foundation
Deployment of external server area and dual machine hot standby of firewall Foundation
2022-07-06 20:52:00 【51CTO】
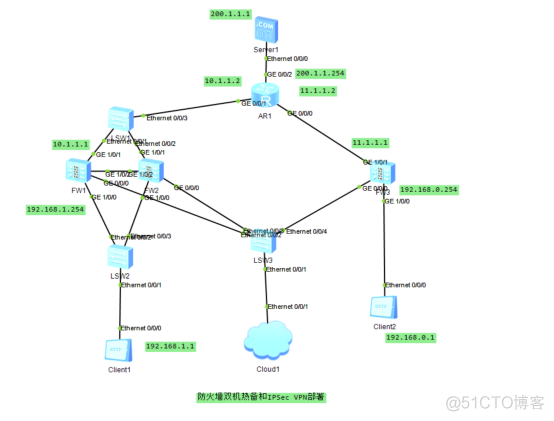
Firewall dual machine hot standby and branch and headquarters access external network server deployment
Principle overview :
A firewall ( English :Firewall) Technology is through the organic combination of all kinds of software and hardware equipment for safety management and screening , Help the computer network in it 、 Build a relatively isolated protective barrier between the external networks , A technology to protect user data and information security .
The function of firewall technology is to discover and deal with the possible security risks when the computer network is running 、 Data transmission and so on , The treatment measures include isolation and protection , At the same time, it can record and test all operations in computer network security , To ensure the security of computer network operation , Guarantee the integrity of user data and information , Better for users 、 More secure computer network experience .
So-called “ A firewall ” It refers to an intranet and public access network ( Such as Internet) The way of separation , It is actually an applied security technology based on modern communication network technology and information security technology , Isolation technology . It is more and more used in the interconnection environment of private network and public network , Especially with access Internet The Internet is the most important .
Firewall is a protective barrier between the internal and external network environment with the help of hardware and software , So as to block the unsafe network factors of the computer . Only with the consent of the firewall , Users can enter the computer , If you don't agree, you'll be blocked out , The alarm function of firewall technology is very powerful , When an external user wants to enter the computer , The firewall will quickly send out the corresponding alarm , And remind users of their behavior , And make self judgment to decide whether to allow external users to enter the interior , As long as the user is in the network environment , This kind of firewall can carry out effective query , At the same time, the information found will be displayed to the user , Then users need to implement corresponding settings for the firewall according to their own needs , Block the disallowed user behavior . Through the firewall, you can also effectively view the traffic of information data , And it can also master the speed of uploading and downloading data information , It is convenient for users to have good control judgment on the use of computers , The internal situation of the computer can also be viewed through this firewall , It also has the function of starting and closing the program , And the internal log function of the computer system , In fact, it is also a summary of the real-time situation of the firewall and the internal security of the computer system .
Firewall is a kind of access control scale which is executed when two networks communicate , It can prevent hackers from accessing your network to the maximum extent . It's set up on different networks ( Such as trusted intranet and untrusted public network ) Or a combination of components between network security domains . It is the only access to information between different networks or network security domains , Be able to control according to the safety policy of the enterprise ( allow 、 Refuse 、 monitoring ) Information flow in and out of the network , And it has strong anti attack ability . It's about providing information security services , Infrastructure for network and information security . Logically , The firewall is a separator , A limiter , It's also an analyzer , Effectively monitored the intranet and Internet Any activity between , Ensure the security of the internal network .
The firewall scans its network traffic , This will filter out some attacks , In case it is executed on the target computer . Firewalls can also shut down unused ports . And it can also disable outgoing traffic on specific ports , Block the Trojan horse . Last , It can disable access from special sites , To prevent all communications from unknown intruders .
The barrier of network security
A firewall ( As a blocking point 、 The control points ) It can greatly improve the security of an internal network , And reduce risk by filtering unsafe Services . Because only carefully selected application protocols can pass through the firewall , So the network environment becomes more secure . For example, firewalls can prohibit such as well-known unsafe NFS Protocol access to protected network , In this way, it is impossible for external attackers to use these fragile protocols to attack the internal network . Firewalls can also protect the network from routing based attacks , Such as IP Source routing attacks and ICMP Redirection path in redirection . The firewall should be able to reject all messages of the above types of attacks and notify the firewall administrator .
Strengthen network security strategy
Configure through a firewall centric security scheme , All security software ( Like a password 、 encryption 、 Identity Authentication 、 Audit, etc ) Configure on the firewall . Compared with dispersing network security issues to various hosts , Centralized security management of firewall is more economical . For example, during network access , The one-time password system and other identity authentication systems do not have to be scattered on each host , And focus on the firewall .
Monitoring audit
If all access passes through the firewall , that , The firewall can record these accesses and log them , At the same time, it can also provide statistical data of network usage . When something suspicious happens , The firewall can give appropriate alarm , And provide detailed information on whether the network is monitored and attacked . in addition , It is also very important to collect the usage and misuse of a network . The first reason is to know whether the firewall can resist the detection and attack of attackers , And know whether the control of firewall is sufficient . Network usage statistics are also very important for network demand analysis and threat analysis .
Prevent the leakage of internal information
By using firewall to divide the internal network , It can realize the isolation of key network segments of intranet , Thus, the impact of local key or sensitive network security issues on the global network is limited . also , Privacy is an issue of great concern to the intranet , An unnoticed detail in an internal network may contain clues about security and attract the interest of external attackers , Some security vulnerabilities of the internal network have even been exposed . Using a firewall, you can hide those internal details, such as Finger,DNS Etc .Finger Displays the registered names of all users of the host 、 real name , Last login time and use shell Type, etc . however Finger The information displayed is very easy for attackers to learn . An attacker can know how often a system is used , Whether there are users connecting to the Internet in this system , Whether the system is noticed when being attacked, etc . Firewalls can also block information about internal networks DNS Information , The domain name of such a host and IP The address will not be known to the outside world . In addition to safety , The firewall also supports Internet Service enterprise internal network technology system VPN( Virtual private network ).
Logging and event notification
All data entering and leaving the network must pass through the firewall , The firewall records it through logs , It can provide detailed statistical information of network use . When a suspicious event occurs , The firewall can alarm and notify according to the mechanism , Provide information on whether the network is threatened .
The topology :
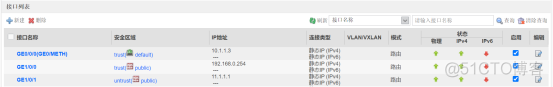
Basic configuration :
Headquarters firewall :

Branch firewall :
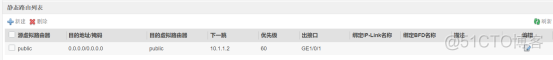
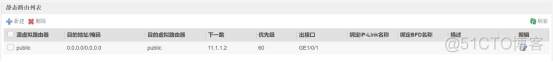
Configure the default route :
Headquarters firewall :
Branch firewall :
To configure NAT:
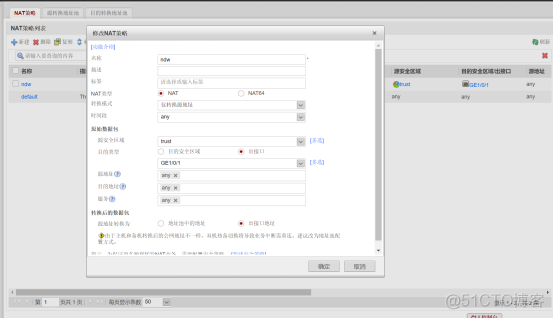
Headquarters firewall :
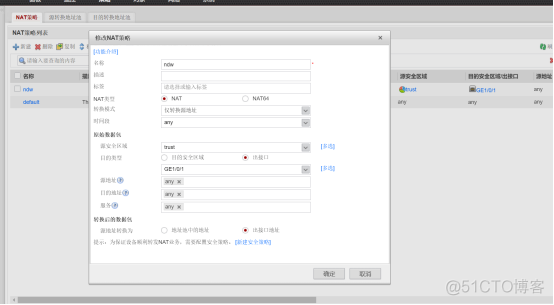
Branch firewall :
Configure dual hot standby :


Routing configuration :
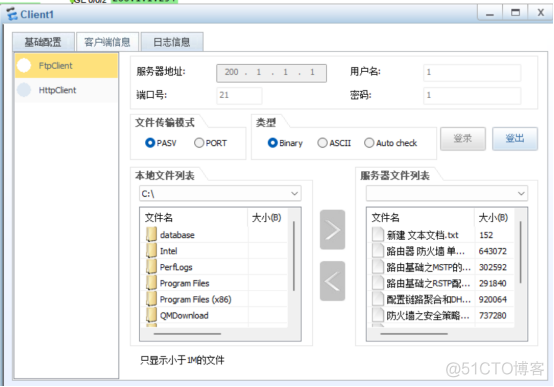
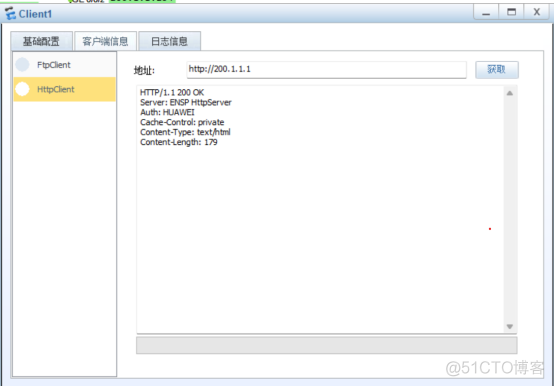


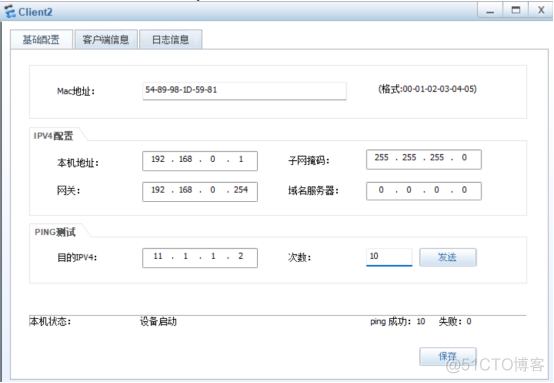
End of experiment ;
remarks : If there is a mistake , Please understand !
This article is my study notes , For reference only ! If there is a repetition !!! Please contact me
边栏推荐
- [DIY]如何制作一款個性的收音機
- R语言可视化两个以上的分类(类别)变量之间的关系、使用vcd包中的Mosaic函数创建马赛克图( Mosaic plots)、分别可视化两个、三个、四个分类变量的关系的马赛克图
- Number of schemes from the upper left corner to the lower right corner of the chessboard (2)
- 硬件开发笔记(十): 硬件开发基本流程,制作一个USB转RS232的模块(九):创建CH340G/MAX232封装库sop-16并关联原理图元器件
- Mécanisme de fonctionnement et de mise à jour de [Widget Wechat]
- 性能测试过程和计划
- [200 opencv routines] 220 Mosaic the image
- Pat 1078 hashing (25 points) ⼆ times ⽅ exploration method
- 1_ Introduction to go language
- Implementation of packaging video into MP4 format and storing it in TF Card
猜你喜欢
Gui Gui programming (XIII) - event handling
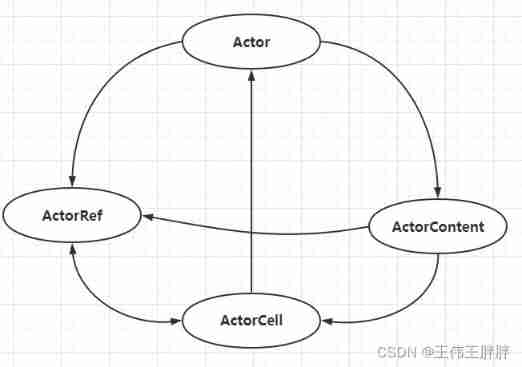
Detailed introduction of distributed pressure measurement system VIII: basic introduction of akka actor model
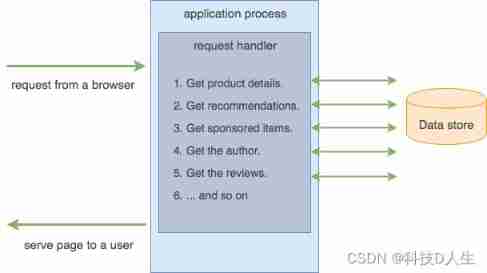
Kubernetes learning summary (20) -- what is the relationship between kubernetes and microservices and containers?

SQL injection 2
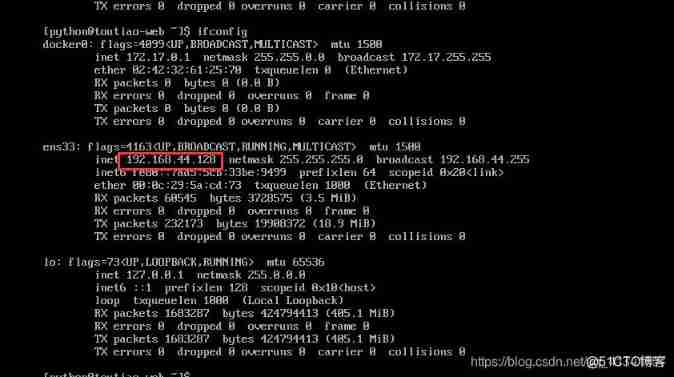
Pycharm remote execution
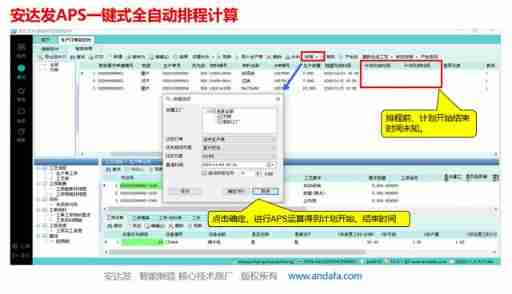
Value of APS application in food industry

Detailed explanation of knowledge map construction process steps
2022 portal crane driver registration examination and portal crane driver examination materials
![[DIY]自己设计微软MakeCode街机,官方开源软硬件](/img/a3/999c1d38491870c46f380c824ee8e7.png)
[DIY]自己设计微软MakeCode街机,官方开源软硬件
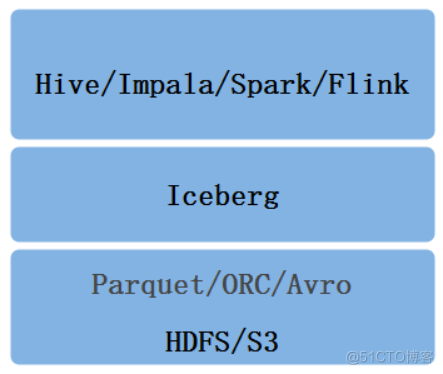
数据湖(八):Iceberg数据存储格式
随机推荐
Trends of "software" in robotics Engineering
2022 construction electrician (special type of construction work) free test questions and construction electrician (special type of construction work) certificate examination
New database, multidimensional table platform inventory note, flowus, airtable, seatable, Vig table Vika, Feishu multidimensional table, heipayun, Zhixin information, YuQue
APS taps home appliance industry into new growth points
基于STM32单片机设计的红外测温仪(带人脸检测)
Application layer of tcp/ip protocol cluster
How does kubernetes support stateful applications through statefulset? (07)
Tips for web development: skillfully use ThreadLocal to avoid layer by layer value transmission
全网最全的新型数据库、多维表格平台盘点 Notion、FlowUs、Airtable、SeaTable、维格表 Vika、飞书多维表格、黑帕云、织信 Informat、语雀
自定义限流注解
Rhcsa Road
Spark SQL chasing Wife Series (initial understanding)
2022 Guangdong Provincial Safety Officer C certificate third batch (full-time safety production management personnel) simulation examination and Guangdong Provincial Safety Officer C certificate third
正则表达式收集
知识图谱构建流程步骤详解
全网最全的知识库管理工具综合评测和推荐:FlowUs、Baklib、简道云、ONES Wiki 、PingCode、Seed、MeBox、亿方云、智米云、搜阅云、天翎
Taylor series fast Fourier transform (FFT)
SAP Fiori应用索引大全工具和 SAP Fiori Tools 的使用介绍
Mécanisme de fonctionnement et de mise à jour de [Widget Wechat]
Math symbols in lists