当前位置:网站首页>C language makes it easy to add, delete, modify and check the linked list "suggested collection"
C language makes it easy to add, delete, modify and check the linked list "suggested collection"
2022-07-05 18:39:00 【Full stack programmer webmaster】
Hello everyone , I meet you again , I'm your friend, Quan Jun .
notes : Simple pursuit of code simplicity , So the writing may not be standard .
// Take it for the first time c Start writing data structures , Because of what I wrote , Pursue less code , And College ppt Not quite the same. . Please point out the mistakes
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
typedef struct node// Define the node
{
int data;
struct node * next;
}Node;// Function introduction
void printlist(Node * head)// Print linked list
int lenlist(Node * head)// Return the length of the list
void insertlist(Node ** list,int data,int index)// Insert elements
void pushback(Node ** head,int data)// Tail insertion
void freelist(Node ** head)// Empty the list
void deletelist(Node ** list,int data)// Remove elements
Node * findnode(Node ** list,int data)// lookup
void change(Node ** list,int data,int temp)// Change the value void printlist(Node * head)// Print linked list
{
for(;head!=NULL;head=head->next) printf("%d ",head->data);
printf("\n");// Print for other functions , Last line break
}Chain length
int lenlist(Node * head)// Return the length of the list
{
int len;
Node * temp = head;
for(len=0; temp!=NULL; len++) temp=temp->next;
return len;
}Insert elements
void insertlist(Node ** list,int data,int index)// Insert elements , use *list take head Pointers and next Unified expression
{
if(index<0 || index>lenlist(*list))return;// Judge illegal input
Node * newnode=(Node *)malloc(sizeof(Node));// establish
newnode->data=data;
newnode->next=NULL;
while(index--)list=&((*list)->next);// Insert
newnode->next=*list;
*list=newnode;
}Add element to tail
void pushback(Node ** head,int data)// Tail insertion , ditto
{
Node * newnode=(Node *)malloc(sizeof(Node));// establish
newnode->data=data;
newnode->next=NULL;
while(*head!=NULL)head=&((*head)->next);// Insert
*head=newnode;
}Empty the list
void freelist(Node ** head)// Empty the list
{
Node * temp=*head;
Node * ttemp;
*head=NULL;// The pointer is set to null
while(temp!=NULL)// Release
{
ttemp=temp;
temp=temp->next;
free(ttemp);
}
}Delete
void deletelist(Node ** list,int data)// Delete the linked list node
{
Node * temp;// It's just convenient free
while((*list)->data!=data && (*list)->next!=NULL)list=&((*list)->next);
if((*list)->data==data){
temp=*list;
*list=(*list)->next;
free(temp);
}
}lookup
Node * findnode(Node ** list,int data)// lookup , Return the pointer to the node , If no return is empty
{
while((*list)->data!=data && (*list)!=NULL) list=&((*list)->next);
return *list;
}Change value
void change(Node ** list,int data,int temp)// change
{
while((*list)->data!=data && (*list)->next!=NULL)list=&((*list)->next);
if((*list)->data==data)(*list)->data=temp;
}Final test
int main(void)// test
{
Node * head=NULL;
Node ** gg=&head;
int i;
for(i=0;i<10;i++)pushback(gg,i);
printf(" The list elements are in turn : ");
printlist(head);
printf(" The length is %d\n",lenlist(head));
freelist(gg);
printf(" The length after release is %d\n",lenlist(head));
for(i=0;i<10;i++)pushback(gg,i);
deletelist(gg,0);// head
deletelist(gg,9);// tail
deletelist(gg,5);
deletelist(gg,100);// non-existent
printf(" Create the list again , After deleting a node \n");
printlist(head);
freelist(gg);
for(i=0;i<5;i++)pushback(gg,i);
insertlist(gg,5,0);// head
insertlist(gg,5,5);
insertlist(gg,5,7);// tail
insertlist(gg,5,10);// non-existent
printlist(head);
printf(" find %d\n hold 3 Turn into 100",*findnode(gg,5));
change(gg,3,100);
change(gg,11111,1);// non-existent
printlist(head);
}Publisher : Full stack programmer stack length , Reprint please indicate the source :https://javaforall.cn/149821.html Link to the original text :https://javaforall.cn
边栏推荐
- Introduction to the development function of Hanlin Youshang system of Hansheng Youpin app
- sample_rate(采樣率),sample(采樣),duration(時長)是什麼關系
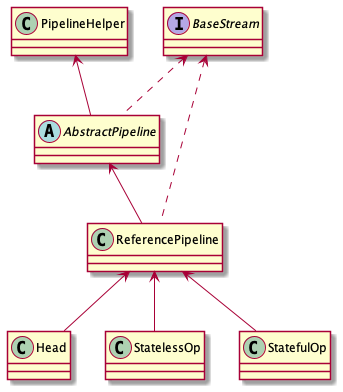
- Take a look at semaphore, the current limiting tool provided by JUC
- 瀚升优品app翰林优商系统开发功能介绍
- Personal understanding of convolutional neural network
- Electron installation problems
- How to obtain the coordinates of the aircraft passing through both ends of the radar
- 深入底层C源码讲透Redis核心设计原理
- Record eval() and no in pytoch_ grad()
- vulnhub之darkhole_2
猜你喜欢
集合处理的利器
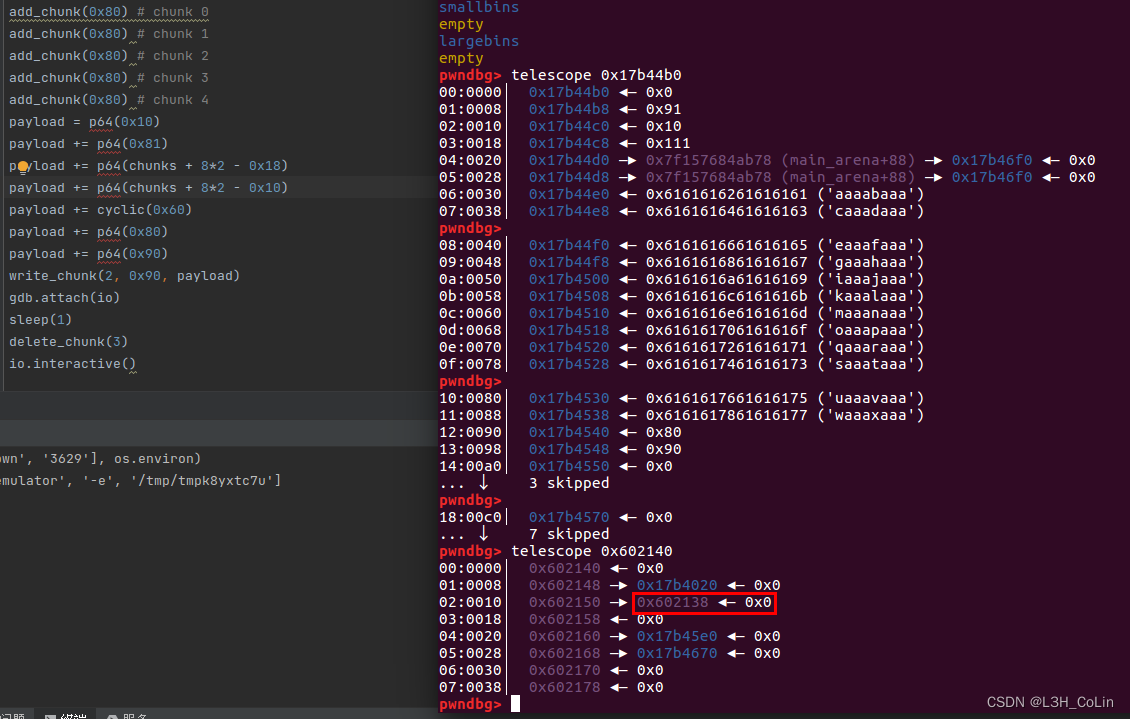
buuctf-pwn write-ups (9)
Reptile 01 basic principles of reptile
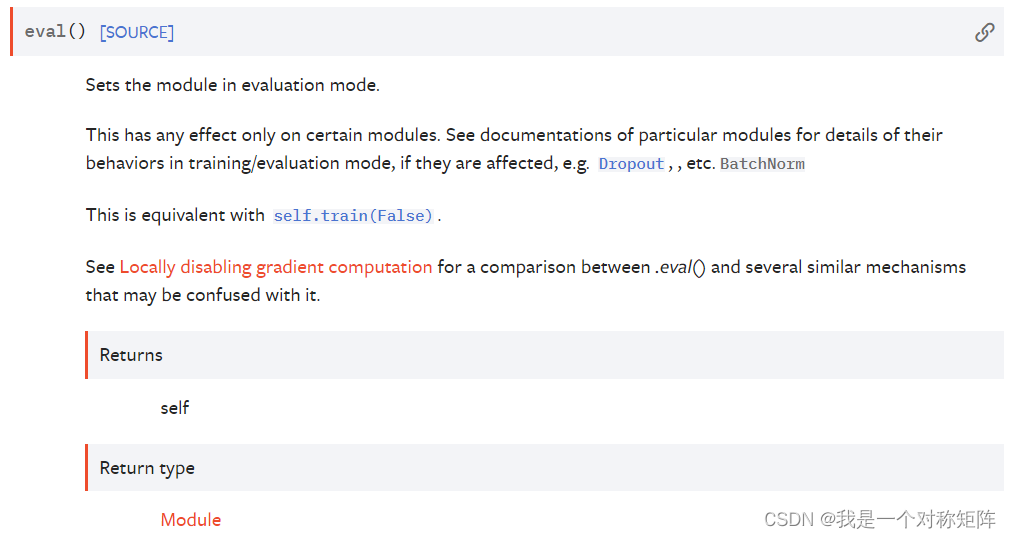
记录Pytorch中的eval()和no_grad()
node_exporter内存使用率不显示
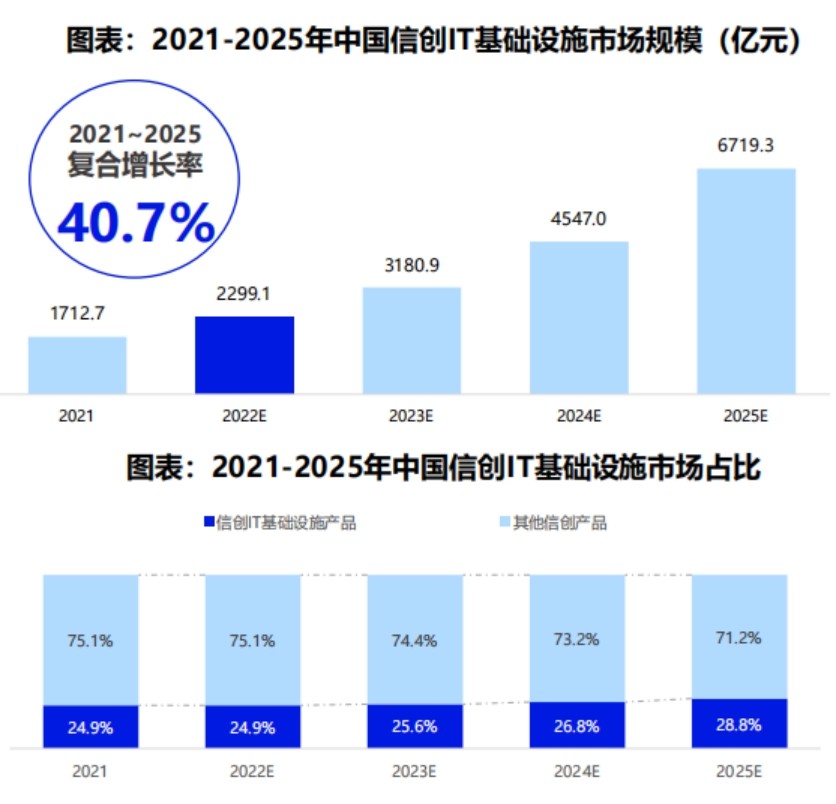
The 2022 China Xinchuang Ecological Market Research and model selection evaluation report released that Huayun data was selected as the mainstream manufacturer of Xinchuang IT infrastructure!
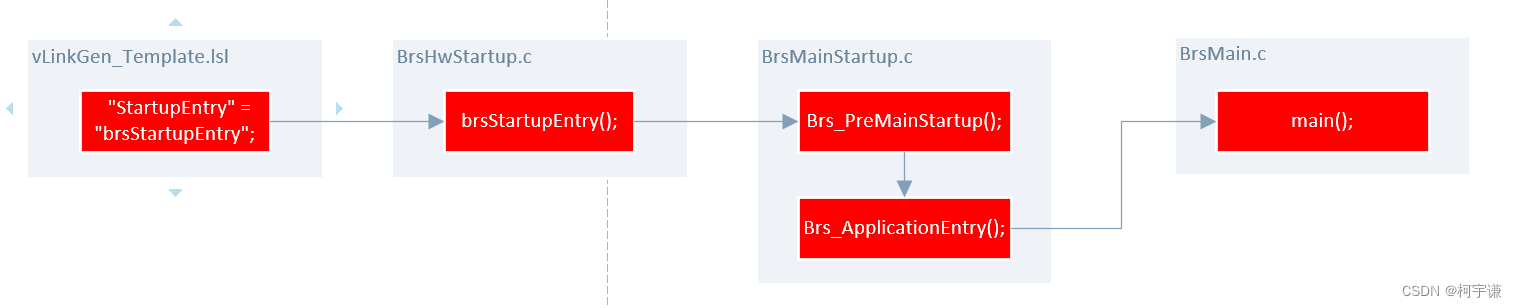
【Autosar 十四 启动流程详解】

第十一届中国云计算标准和应用大会 | 云计算国家标准及白皮书系列发布 华云数据全面参与编制
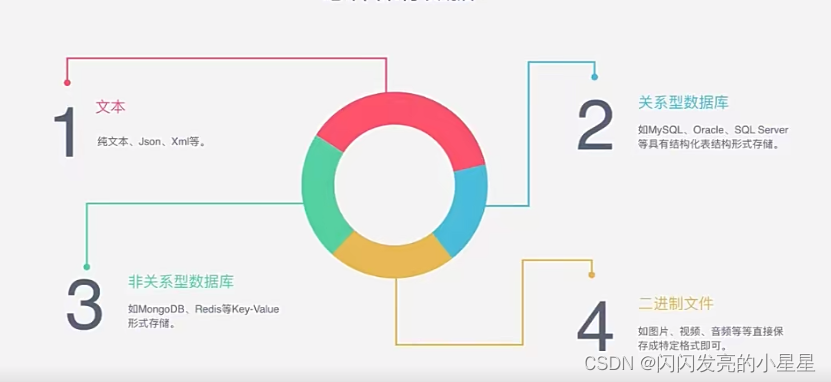
爬虫01-爬虫基本原理讲解
视频自监督学习综述
随机推荐
IDEA配置npm启动
The 2022 China Xinchuang Ecological Market Research and model selection evaluation report released that Huayun data was selected as the mainstream manufacturer of Xinchuang IT infrastructure!
The 11th China cloud computing standards and Applications Conference | China cloud data has become the deputy leader unit of the cloud migration special group of the cloud computing standards working
Clickhouse (03) how to install and deploy Clickhouse
瀚升优品app翰林优商系统开发功能介绍
爬虫01-爬虫基本原理讲解
Deep copy and shallow copy [interview question 3]
buuctf-pwn write-ups (9)
解决 contents have differences only in line separators
Einstein sum einsum
【pm2详解】
《2022中国信创生态市场研究及选型评估报告》发布 华云数据入选信创IT基础设施主流厂商!
彻底理解为什么网络 I/O 会被阻塞?
Use of websocket tool
Case sharing | integrated construction of data operation and maintenance in the financial industry
分享:中兴 远航 30 pro root 解锁BL magisk ZTE 7532N 8040N 9041N 刷机 刷面具原厂刷机包 root方法下载
pytorch yolov5 训练自定义数据
7-1 linked list is also simple fina
Copy the linked list with random pointer in the "Li Kou brush question plan"
《ClickHouse原理解析与应用实践》读书笔记(5)