当前位置:网站首页>[HCIA continuous update] overview of dynamic routing protocol
[HCIA continuous update] overview of dynamic routing protocol
2022-07-02 03:14:00 【Kawakami 2001】
Overview of dynamic routing protocol
Classification of dynamic routing protocols
Sort by work area
IGP( Internal gateway protocol )
RIP
OSPF
IS-IS
EGP External gateway protocol
BGP
Classified by working mechanism and algorithm
Distance vector routing protocol
RIP
Link state routing protocol
OSPF
IS-IS
Distance vector routing protocol
1、 Routers running distance vector routing protocols periodically flood their own routing tables . Interaction through routing , Each router learns routing from its neighbors , And load it into your own routing table
2、 For all routers in the network , The router doesn't know the topology of the network , Just simply know where you want to go and where the direction is , How far is the distance . This is the essence of distance vector algorithm
Link state routing protocol
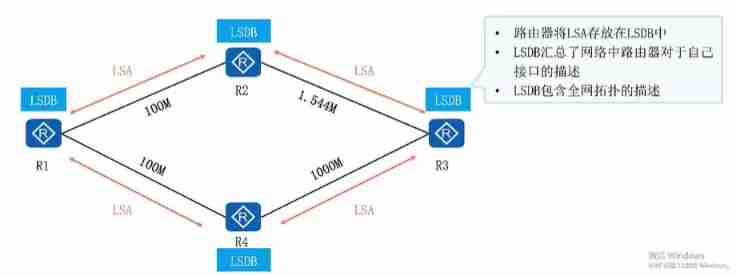
Different from distance vector routing protocol , The link state routing protocol advertises the link state rather than the routing table . A neighbor relationship of the protocol will be established between the routes running the link state routing protocol , Then they interact with each other LSA( Link status report )

Link state routing protocol —— LSDB To form a
Every router generates LSAS, The router will receive LSAS Put in your own LSDS( Routing status database ). The router goes through LSDB, Master the topology of the whole network
Link state routing protocol —— SPF Calculation
Each router is based on LSDB, Use SPF( Shortest path first ) Algorithm to calculate . Each router calculates a tree with its own root 、 Acyclic 、 With the shortest path “ Trees ”. With this tree “ Trees ”, The router already knows the preferred path to every corner of the network

Summary of link state routing protocols
OSPF brief introduction
1、OSPF It is a typical link state routing protocol , It is widely used in the industry IGP One of the agreements
2、 Currently for IPV4 The protocol uses OSPF Version 2 (RFC2328); in the light of IPV6 Agreement to use OSPF Version 3 (RFC2740) Unless otherwise specified, the subsequent references in this chapter refer to OSPF Are all OSPF Version 2
3、 function OSPF The interaction between routers is LS Information , Instead of direct interactive routing .LS Information is OSPF Key information for normal topology and routing calculation
4、OSPF The router will be in the network LS Gather information , Stored in the LSDB in . Routers know the network topology in the area , This is related to the calculation of acyclic paths by routers
5、 Each station OSPF All routers take SPF The algorithm calculates the shortest path to the destination . The router forms routes based on these paths and loads them into the routing table
6、OSPF Support VLSM( Variable length subnet mask ), Support manual routing and congregation
7、 The multi area design makes OSPF can Support larger networks
OSPF Application in campus network
OSPF Basic terms :
Area
1、OSPF Area Used to identify a OSPF Region
2、 Area is the logical division of devices into different groups , Each group is identified by an area number
Router——ID
1、Router——ID, Used in a OSPF Uniquely identify a router in the domain
2、Router——ID The setting of can be configured manually , Or use the method of automatic configuration of the system
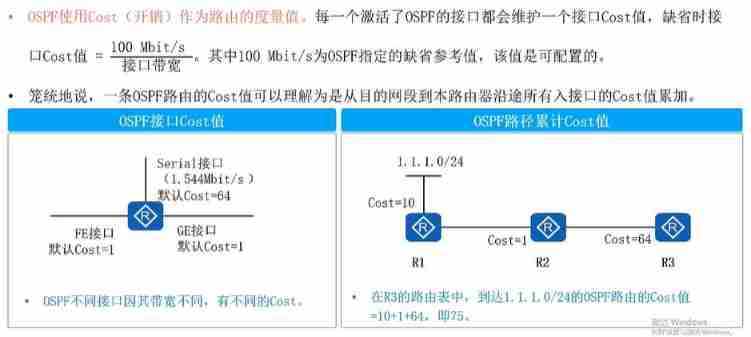
measurements
OSPF Protocol message type
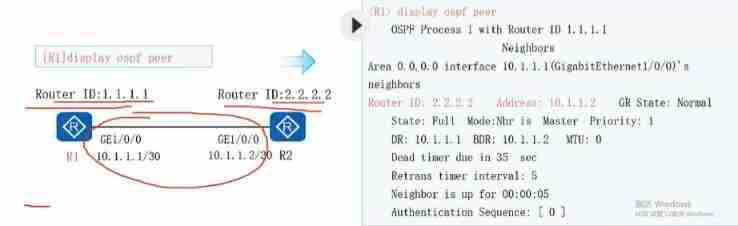
OSPF Three major table items —— Neighborhood watch
OSPF There are three important items ,OSPF Neighborhood watch 、LSDB Table and OSPF Routing table . about OSPF My neighbor table , Need to know ;
- OSPF Before transmitting link status information , You need to establish OSPF Neighborhood
- OSPF Through interaction Hello Message establishment
- SOPF The neighbors table shows OSPF Neighbor status between routers , Use display ospf peer see
about OSPF Of LSDB surface , Need to know :
1、LSDB Will save what they produce and receive from their neighbors LSA Information , In this case R1 Of LSDB Contains three LSA
2、Type identification LSA The type of ,AdvRouter ID send LSA The router
3、 Using the command line display ospf lsdb see LSDB surface
边栏推荐
- verilog 并行块实现
- How to develop digital collections? How to develop your own digital collections
- The video number will not be allowed to be put on the shelves of "0 yuan goods" in the live broadcasting room?
- [staff] pitch representation (bass clef | C1 36 note pitch representation | C2 48 note pitch representation | C3 60 note pitch representation)
- 流线线使用阻塞还是非阻塞
- 2022-2028 global nano abrasive industry research and trend analysis report
- Redis set command line operation (intersection, union and difference, random reading, etc.)
- 自定义组件的 v-model
- 3124. Word list
- PHP array processing
猜你喜欢

Discrimination between sap Hana, s/4hana and SAP BTP
el-table的render-header用法
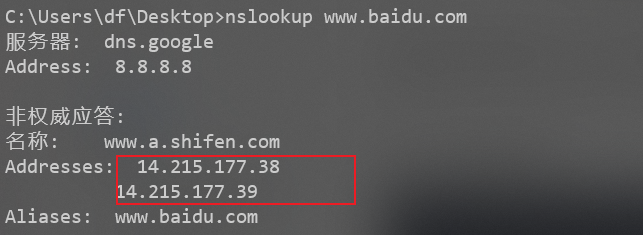
Batch detect whether there is CDN in URL - high accuracy

浅谈线程池相关配置

Share the basic knowledge of a common Hongmeng application
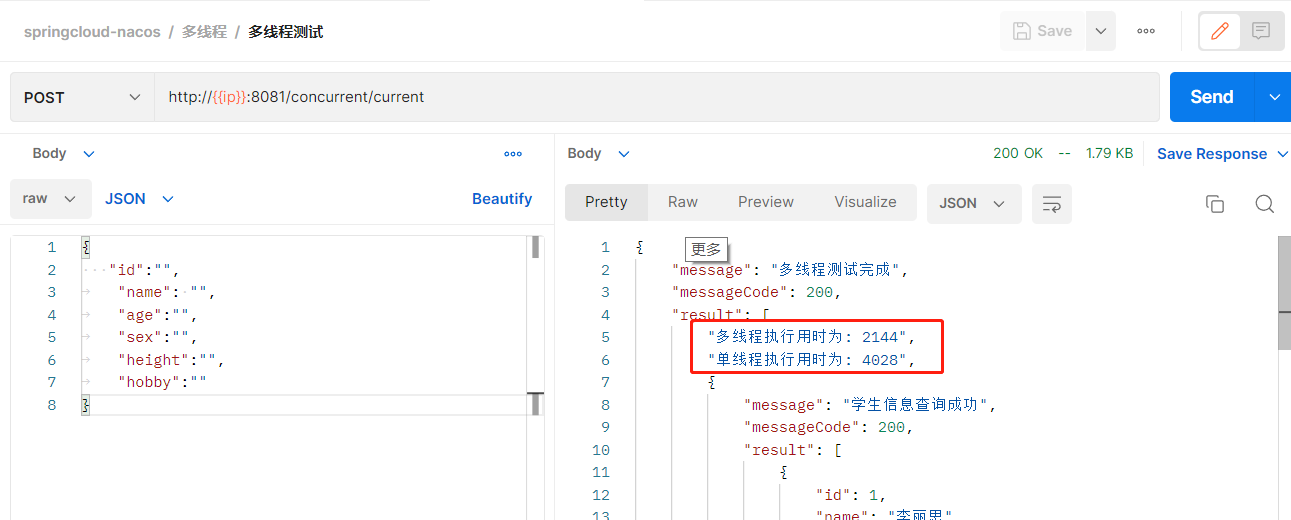
Multi threaded query, double efficiency

After marriage
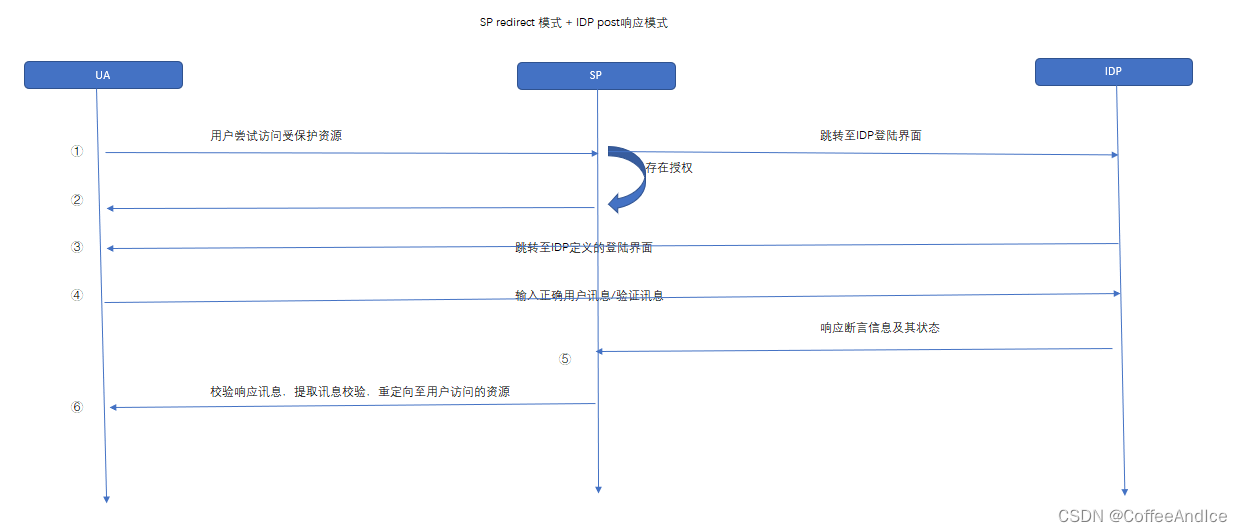
SAML2.0 notes (I)

2022-2028 global deep sea generator controller industry research and trend analysis report

Verilog state machine
随机推荐
Framing in data transmission
V-model of custom component
Share the basic knowledge of a common Hongmeng application
跟着CTF-wiki学pwn——ret2shellcode
Gradle 笔记
Addition without addition, subtraction, multiplication and division (simple difficulty)
2022-2028 global deep sea generator controller industry research and trend analysis report
Apple added the first iPad with lightning interface to the list of retro products
初出茅庐市值1亿美金的监控产品Sentry体验与架构
Redis set command line operation (intersection, union and difference, random reading, etc.)
OSPF LSA message parsing (under update)
终日乾乾,夕惕若厉
Global and Chinese markets for ultrasonic probe disinfection systems 2022-2028: Research Report on technology, participants, trends, market size and share
ORA-01547、ORA-01194、ORA-01110
Grpc quick practice
Qualcomm platform wifi-- WPA_ supplicant issue
Sentry experience and architecture, a fledgling monitoring product with a market value of $100million
Form custom verification rules
数据传输中的成帧
The number one malware in January 2022: lokibot returned to the list, and emotet returned to the top