当前位置:网站首页>电脑通过Putty远程连接树莓派
电脑通过Putty远程连接树莓派
2022-07-04 06:56:00 【思考实践】
确保你的电脑和你的树莓派连接同一个热点
1.让你的树莓派与你的电脑连接你的手机热点
树莓派使用命令行配置wifi连接 - 哔哩哔哩 (bilibili.com)
输入指令看到wlan0的RX与TX不是0就代表连接热点成功了
[email protected]:~$ sudo ifconfig wlan0
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.243.125 netmask 255.255.255.0 broadcast 192.168.243.255
inet6 2409:8914:244:b7f:1f05:f093:abf3:30ce prefixlen 64 scopeid 0x0<global>
inet6 fe80::ceda:dbd1:2893:9ff9 prefixlen 64 scopeid 0x20<link>
ether dc:a6:32:29:13:8d txqueuelen 1000 (Ethernet)
RX packets 866 bytes 106471 (103.9 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 478 bytes 71486 (69.8 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0判断是否能访问Internet,可以Ping www.baidu.com
[email protected]:~$ ping www.baidu.com
PING www.a.shifen.com (39.156.66.18) 56(84) bytes of data.
64 bytes from 39.156.66.18 (39.156.66.18): icmp_seq=1 ttl=50 time=44.7 ms
64 bytes from 39.156.66.18 (39.156.66.18): icmp_seq=2 ttl=50 time=58.7 ms
64 bytes from 39.156.66.18 (39.156.66.18): icmp_seq=3 ttl=50 time=59.0 ms
64 bytes from 39.156.66.18 (39.156.66.18): icmp_seq=4 ttl=50 time=41.8 ms
64 bytes from 39.156.66.18 (39.156.66.18): icmp_seq=5 ttl=50 time=42.4 ms
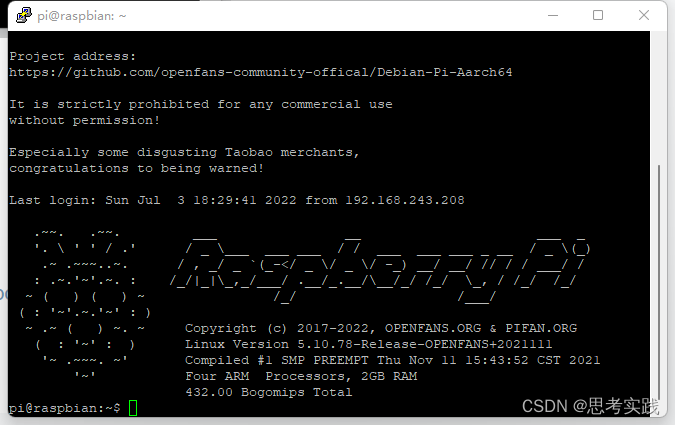
2.使用Putty连接树莓派
1>下载一个Putty
Download PuTTY - a free SSH and telnet client for Windows
2> 查看树莓派的ip地址,在树莓派终端输入 sudo ifconfig,里面的192.168.243.125就是我们要的ip地址
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.243.125 netmask 255.255.255.0 broadcast 192.168.243.255
inet6 2409:8914:244:b7f:1f05:f093:abf3:30ce prefixlen 64 scopeid 0x0<g
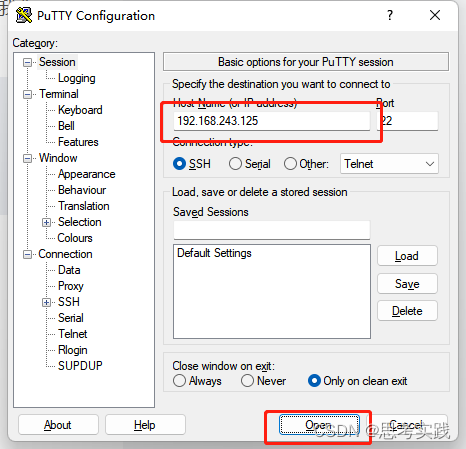
3> 输入地址,然后连接
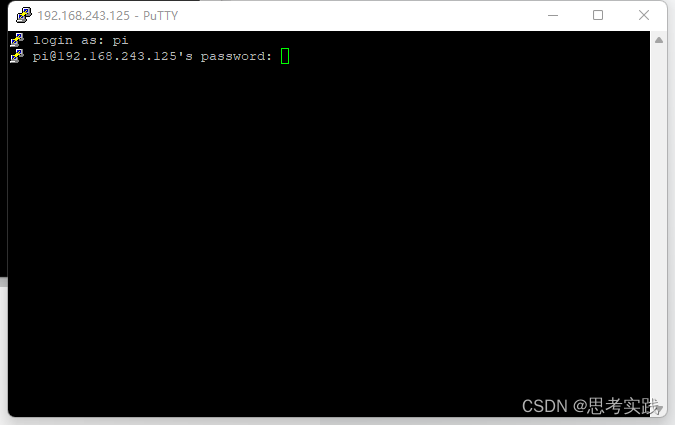
这里填写你的树莓派用户名,一般是 pi

这里填写你的树莓派密码,一般是raspberry
参考资料
(177条消息) SSH远程连接访问树莓派【无公网IP做内网穿透】_LisaCpolar的博客-CSDN博客_树莓派ssh连接
边栏推荐
- 【网络数据传输】基于FPGA的百兆网/兆网千UDP数据包收发系统开发,PC到FPGA
- centos8安装mysql.7 无法开机启动
- Tar source code analysis 4
- Su Weijie, a member of Qingyuan Association and an assistant professor at the University of Pennsylvania, won the first Siam Youth Award for data science, focusing on privacy data protection, etc
- ABCD four sequential execution methods, extended application
- Deep profile data leakage prevention scheme
- Mysql 45讲学习笔记(十二)MySQL会“抖”一下
- Cochez une colonne d'affichage dans une colonne de tableau connue
- Lottery system test report
- 【FPGA教程案例7】基于verilog的计数器设计与实现
猜你喜欢
The most effective futures trend strategy: futures reverse merchandising
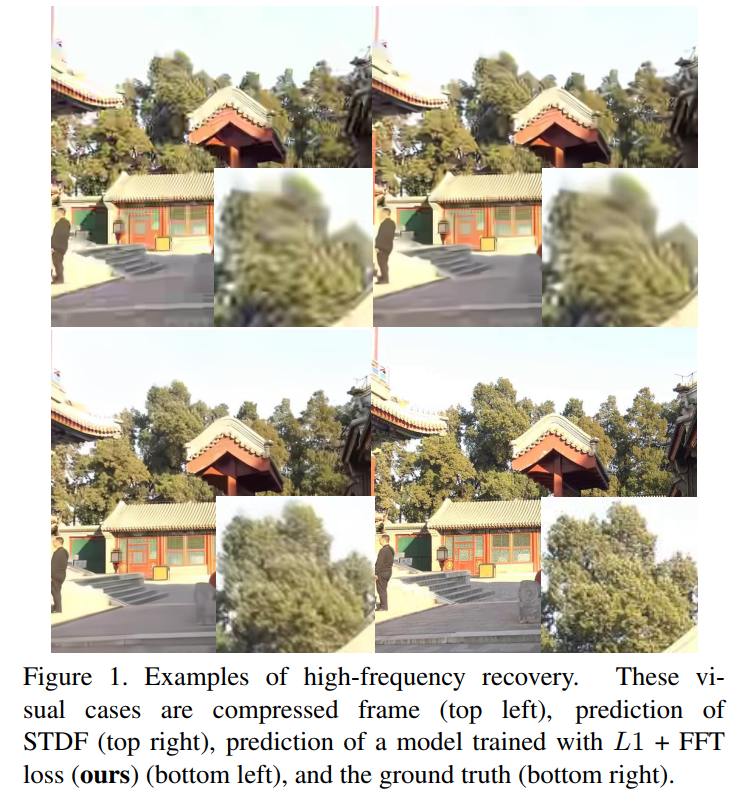
Boosting the Performance of Video Compression Artifact Reduction with Reference Frame Proposals and

What is industrial computer encryption and how to do it
![[network data transmission] FPGA based development of 100M / Gigabit UDP packet sending and receiving system, PC to FPGA](/img/71/1d6179921ae84b1ba61ed094e592ff.png)
[network data transmission] FPGA based development of 100M / Gigabit UDP packet sending and receiving system, PC to FPGA
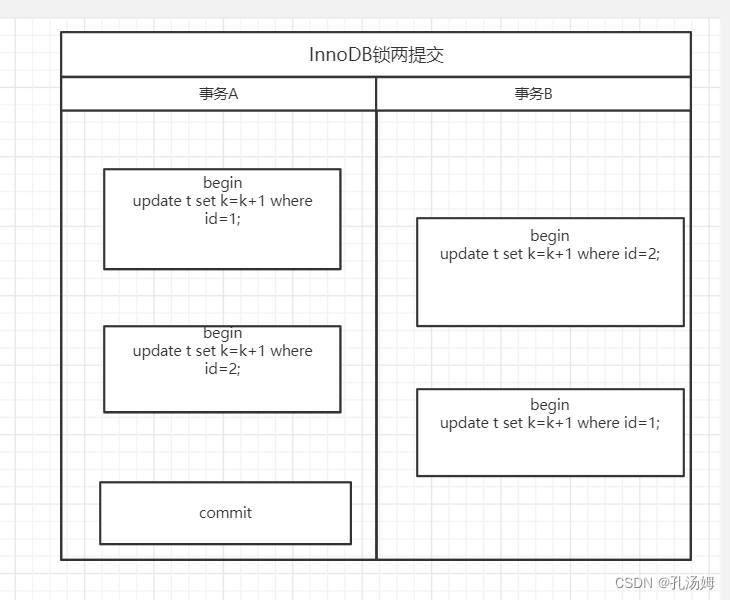
MySQL 45 lecture learning notes (VII) line lock
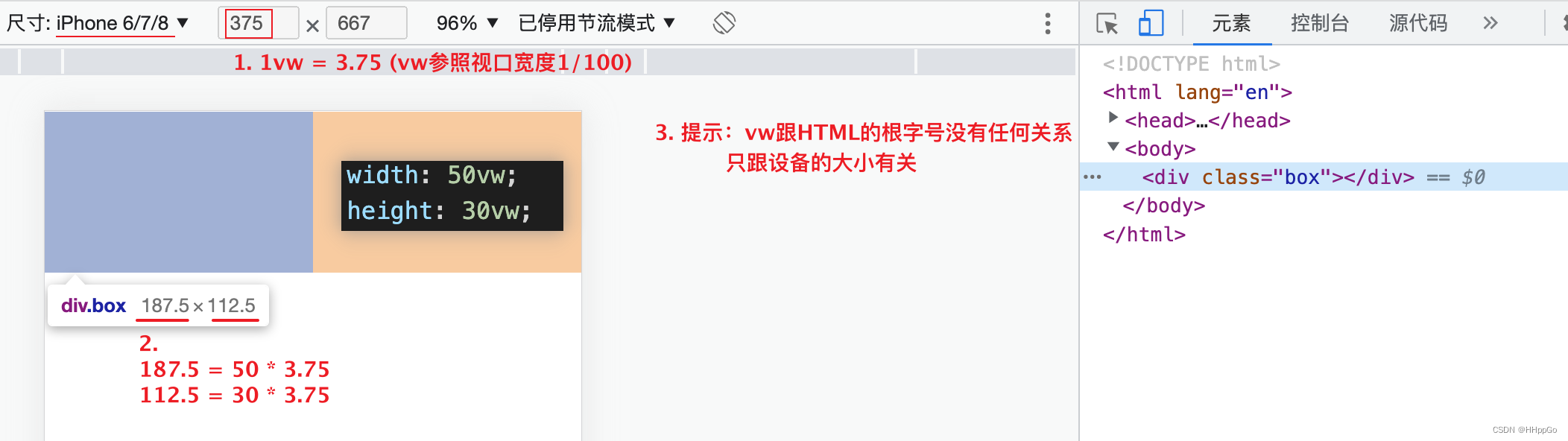
Mobile adaptation: vw/vh

A new understanding of how to encrypt industrial computers: host reinforcement application
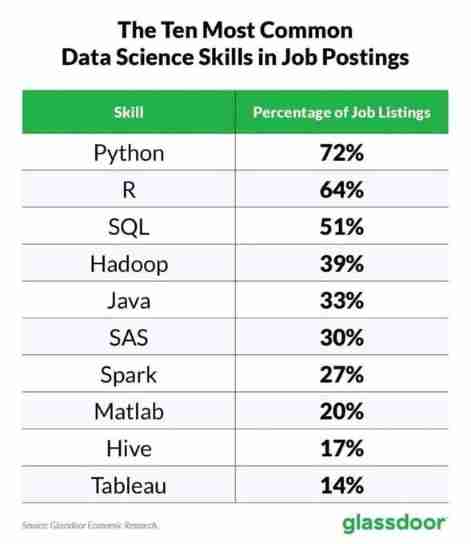
List of top ten professional skills required for data science work
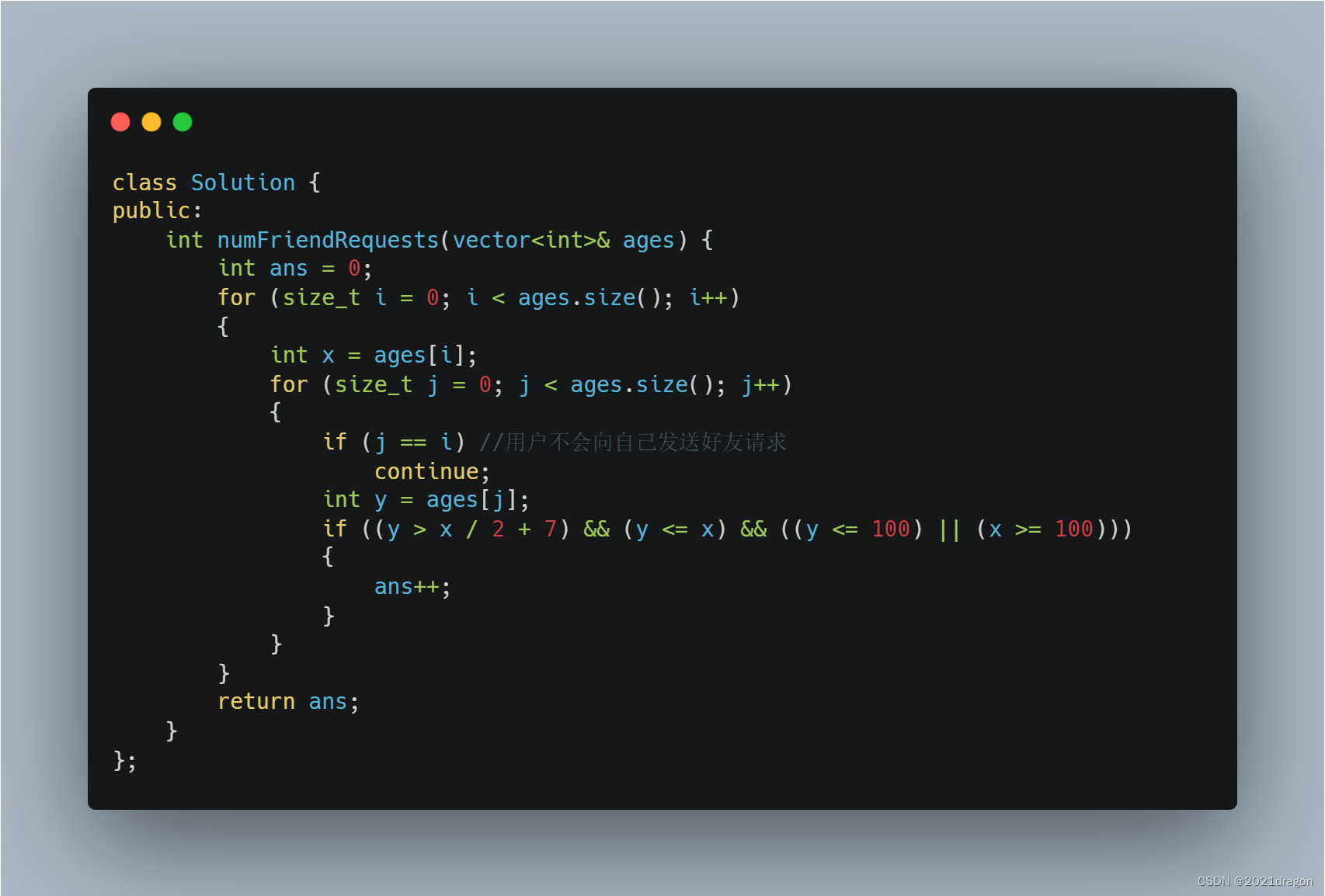
leetcode825. Age appropriate friends
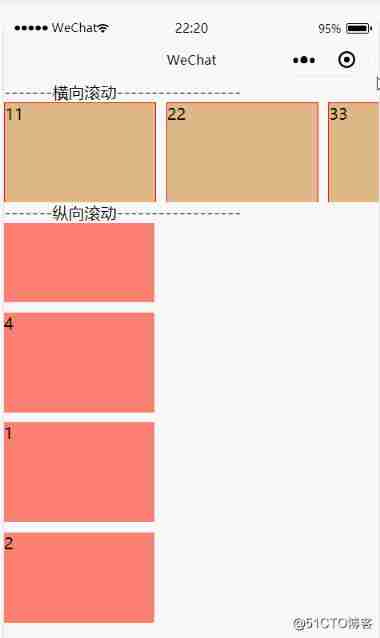
Wechat applet scroll view component scrollable view area
随机推荐
Google Chrome Portable Google Chrome browser portable version official website download method
响应式——媒体查询
What is the "relative dilemma" in cognitive fallacy?
thread priority
Cochez une colonne d'affichage dans une colonne de tableau connue
Wechat applet scroll view component scrollable view area
Flink memory model, network buffer, memory tuning, troubleshooting
Centos8 install mysql 7 unable to start up
Review of enterprise security incidents: how can enterprises do a good job in preventing source code leakage?
the input device is not a TTY. If you are using mintty, try prefixing the command with ‘winpty‘
How can the old version of commonly used SQL be migrated to the new version?
Responsive - media query
移动适配:vw/vh
Explain in one sentence what social proof is
Selection (023) - what are the three stages of event propagation?
Background and current situation of domestic CDN acceleration
Novel website program source code that can be automatically collected
tars源码分析之5
Recursive Fusion and Deformable Spatiotemporal Attention for Video Compression Artifact Reduction
请问旧版的的常用SQL怎么迁移到新版本里来?