当前位置:网站首页>Happy gathering time
Happy gathering time
2022-07-07 23:23:00 【Full stack programmer webmaster】
Hello everyone , I meet you again , I'm the king of the whole stack .
The day before yesterday, several students in the class went to the happy gathering era to take the written exam . I had a try mentality , As a result, I received a notice the next day . After asking the students who went with him, they all said they didn't receive .
Monday I 10::10 We rushed to Huagong hotel , I am a 10:30 Divide that batch , After signing, wait patiently on the seat . The results are 11:15 I haven't called my name yet . It's only good to ask the front desk if it's called. I didn't hear it ( In fact, the original intention is to urge ), The staff said they would check , Let me wait outside , The rush really worked , After a few minutes, a staff member called my name .
After going in . The interviewer didn't let me introduce myself , Directly into the theme . He opened Baidu page with his mobile phone . Enter search keyword, With keyword The input of , There is a drop-down list below that shows the prediction search keyword, example : Enter Guangzhou , The drop-down list will show Guangzhou University ; Guangzhou Haixinsha, etc . Ask what data structure is used to realize this function . At that time, I was stunned , Ask such a profound question when you come , I thought about it and said that I would use the dictionary tree to realize , Then I roughly described the dictionary tree and its advantages .
Here I feel that the description was not very good , The correct approach should be to describe the narrative at the same time . While using paper and pen to describe it concretely , This can deepen the impression of the interviewer , It can also prove that you really understand rather than half a bucket of water with half a knowledge .
The second question the interviewer asked was : Now there is 15w Your users are connected to your server, ask server How to deal with the sending and receiving of user information .
I'll introduce myself to the interviewer first socket Programming . After the introduction, the interviewer interrupted me and said that you were talking about a user . existing 15w user , How to solve .
I said, : With multiple threads . Each thread processes a user's request .
interviewer :15w User connections are loaded into memory . Can you ? I said, : If there is not enough memory, you can consider multiple server, Then according to the user's ip The address range is divided into multiple server Top processing . interviewer : Now suppose there is only one server. One thread , How to deal with . ok , You win . Just a good answer, I don't know how to deal with , And let the interviewer answer how to deal with : The user's ip Address and port Save up , Put the user on server The initiated request is added to the message queue . Use multiple threads to process messages in the message queue ( According to the saved user ip And port Return to the user ).
Third question : Two administrators need to access the salary of employees in the database , If the salary is lower than 3000 Plus 300 Wages . Ask to write sql sentence .
The database didn't learn well , I don't understand . interviewer : I mainly want to ask how to prevent two people from accessing data at the same time and changing data at the same time .
I just remember to lock the data , As for the locking statement, I forgot .
Then the interviewer asked two more multiple-choice questions in the written exam , Just say it's over , Ask me what else I want to ask him , The whole process is 10 More minutes , I knew it was over .
Publisher : Full stack programmer stack length , Reprint please indicate the source :https://javaforall.cn/116216.html Link to the original text :https://javaforall.cn
边栏推荐
猜你喜欢

海内外技术人们“看”音视频技术的未来
十三、系统优化
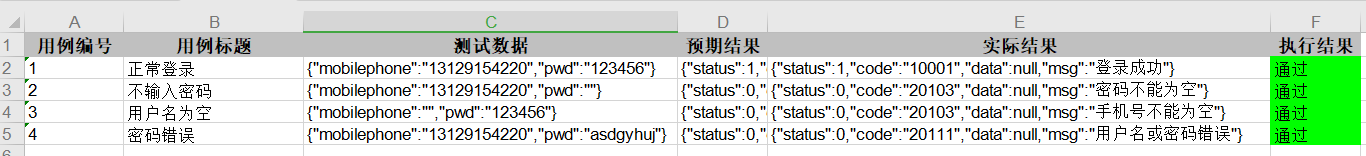
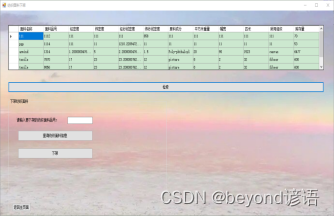
JMeter interface automated test read case, execute and write back result
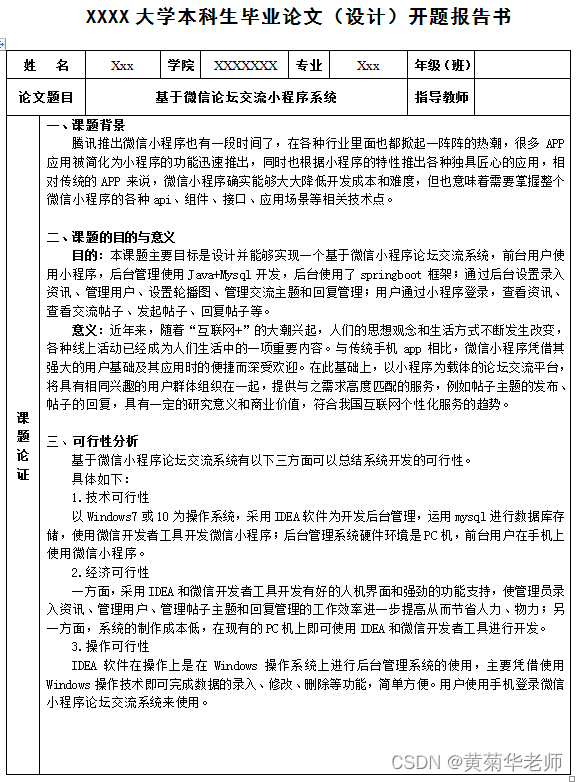
Wechat forum exchange applet system graduation design completion (4) opening report
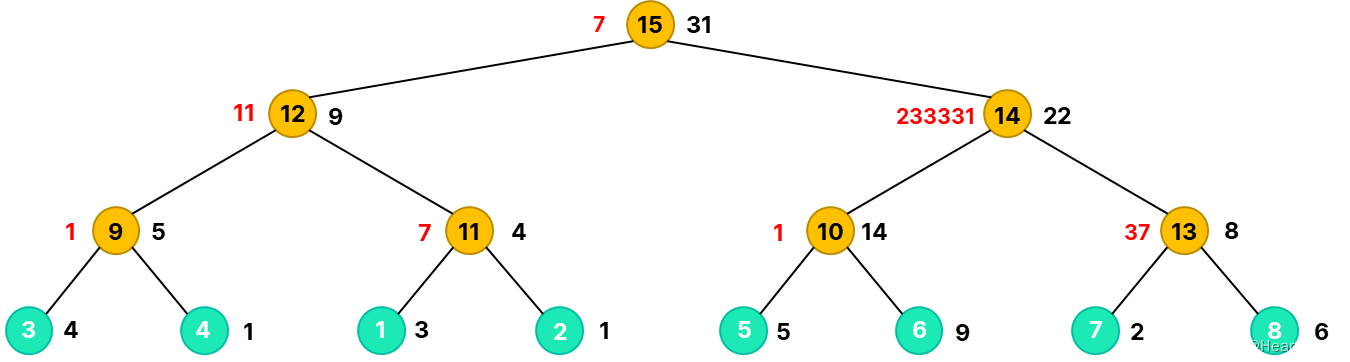
2021icpc Shanghai h.life is a game Kruskal reconstruction tree
13、 System optimization

Oracle database backup and recovery

Adults have only one main job, but they have to pay a price. I was persuaded to step back by personnel, and I cried all night
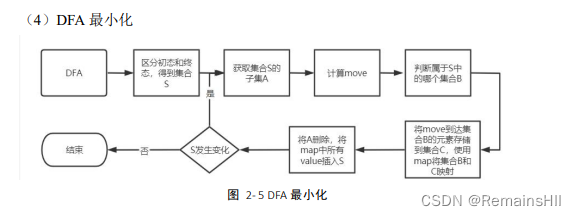
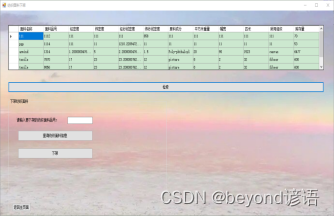
【编译原理】词法分析设计实现
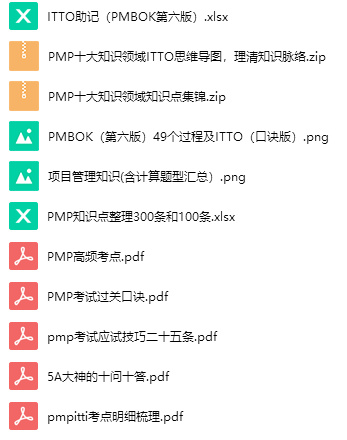
PMP项目管理考试过关口诀-1
随机推荐
二叉树(Binary Tree)
Install a new version of idea. Double click it to open it
Redhat下安装fedora
Unity3d learning notes 5 - create sub mesh
微信论坛交流小程序系统毕业设计毕设(1)开发概要
系统架构设计师备考经验分享:论文出题方向
PCI-Express接口的PCB布线规则
LDO穩壓芯片-內部框圖及選型參數
FreeLink开源呼叫中心设计思想
PMP project management exam pass Formula-1
2021ICPC上海 H.Life is a Game Kruskal重构树
Wechat forum exchange applet system graduation design completion (4) opening report
LM12丨Rolling Heikin Ashi二重K线滤波器
Installing spss25
Network security CSRF
leetcode-520. 检测大写字母-js
网格(Grid)
三问TDM
LDO稳压芯片-内部框图及选型参数
The 19th Zhejiang Provincial College Programming Contest 2022 f.easyfix chairman tree