当前位置:网站首页>Luo Gu P1170 Bugs Bunny and Hunter
Luo Gu P1170 Bugs Bunny and Hunter
2022-07-06 01:25:00 【zjsru_ Beginner】
Title Description
Bugs Bunny hid in the orchard next to the forest . The orchard has M×N tree , Form a M That's ok N Columns of the matrix , The distance between two horizontally or vertically adjacent trees is 1. Bugs Bunny is under a fruit tree .
The hunter walked into the orchard with his shotgun on his back , He climbed up a fruit tree , Ready to kill bugs bunny .
If there are no other fruit trees between the hunter and Bugs Bunny , The hunter can see bugs bunny .
Now we know the location of the hunter and bugs bunny , Write a program to determine whether the location of the rabbit is safe .
Input format
First act nn, Express nn Group data , The first line of each set of data is two positive integers ax and ay, Indicates the location of the Hunter , The second line is two positive integers bx and by, Indicates the location of bugs bunny .
Output format
share n That's ok , Every act yes or no Indicates whether Bugs Bunny's position is safe .
I/o sample
Input #1 Copy
1 1 1 1 2
Output #1 Copy
no
explain / Tips
1≤n≤1051≤ax,ay,bx,by≤108.
Their thinking
This question is very misleading at the beginning , When I just finished reading the topic , I think most people should think that there is only one circle around the hunter 8 One point is dangerous . In fact, this is incomplete . Suppose the hunter is the origin except for the appeal 8 There are many other points besides, for example (2,1)(1,4) Wait, but these points also have rules to follow . Hunters want to kill rabbits. Rabbits only happen when the absolute value of the coordinate difference of their stations is mutual prime .
#include<bits/stdc++.h>
using namespace std;
int n, rx, ry, lrx, lry;
int gcd(int x, int y)
{
if (y == 0) return x;
else return (gcd(y, x % y));
}
int main()
{
cin >> n;
for (int i = 1; i <= n; i++)
{
cin >> lrx >> lry >> rx >> ry;
if (gcd(abs(lrx - rx), abs(lry - ry)) == 1) cout << "no\n";
else cout << "yes\n";
}
return 0;
}
Computer 202 yjq
边栏推荐
- Introduction to robotics I. spatial transformation (1) posture, transformation
- Blue Bridge Cup embedded stm32g431 - the real topic and code of the eighth provincial competition
- How does the crystal oscillator vibrate?
- Huawei converged VLAN principle and configuration
- Condition and AQS principle
- leetcode刷题_平方数之和
- Une image! Pourquoi l'école t'a - t - elle appris à coder, mais pourquoi pas...
- 3D模型格式汇总
- The basic usage of JMeter BeanShell. The following syntax can only be used in BeanShell
- How does Huawei enable debug and how to make an image port
猜你喜欢
How to extract MP3 audio from MP4 video files?
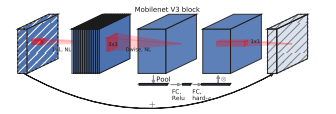
Mobilenet series (5): use pytorch to build mobilenetv3 and learn and train based on migration
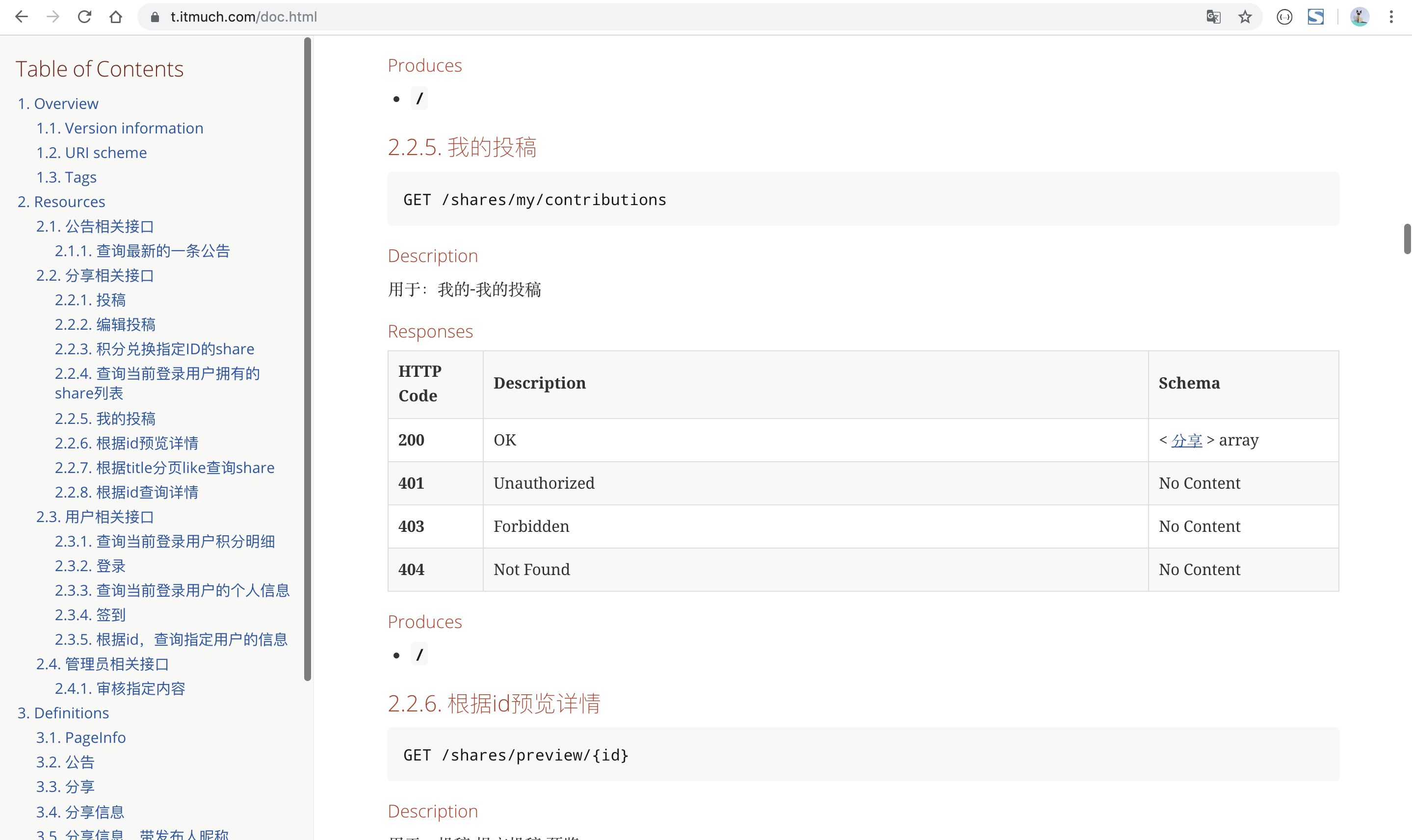
【已解决】如何生成漂亮的静态文档说明页
Vulhub vulnerability recurrence 75_ XStream

Pbootcms plug-in automatically collects fake original free plug-ins

1791. Find the central node of the star diagram / 1790 Can two strings be equal by performing string exchange only once

What is the most suitable book for programmers to engage in open source?

Alibaba-Canal使用详解(排坑版)_MySQL与ES数据同步
Mathematical modeling learning from scratch (2): Tools
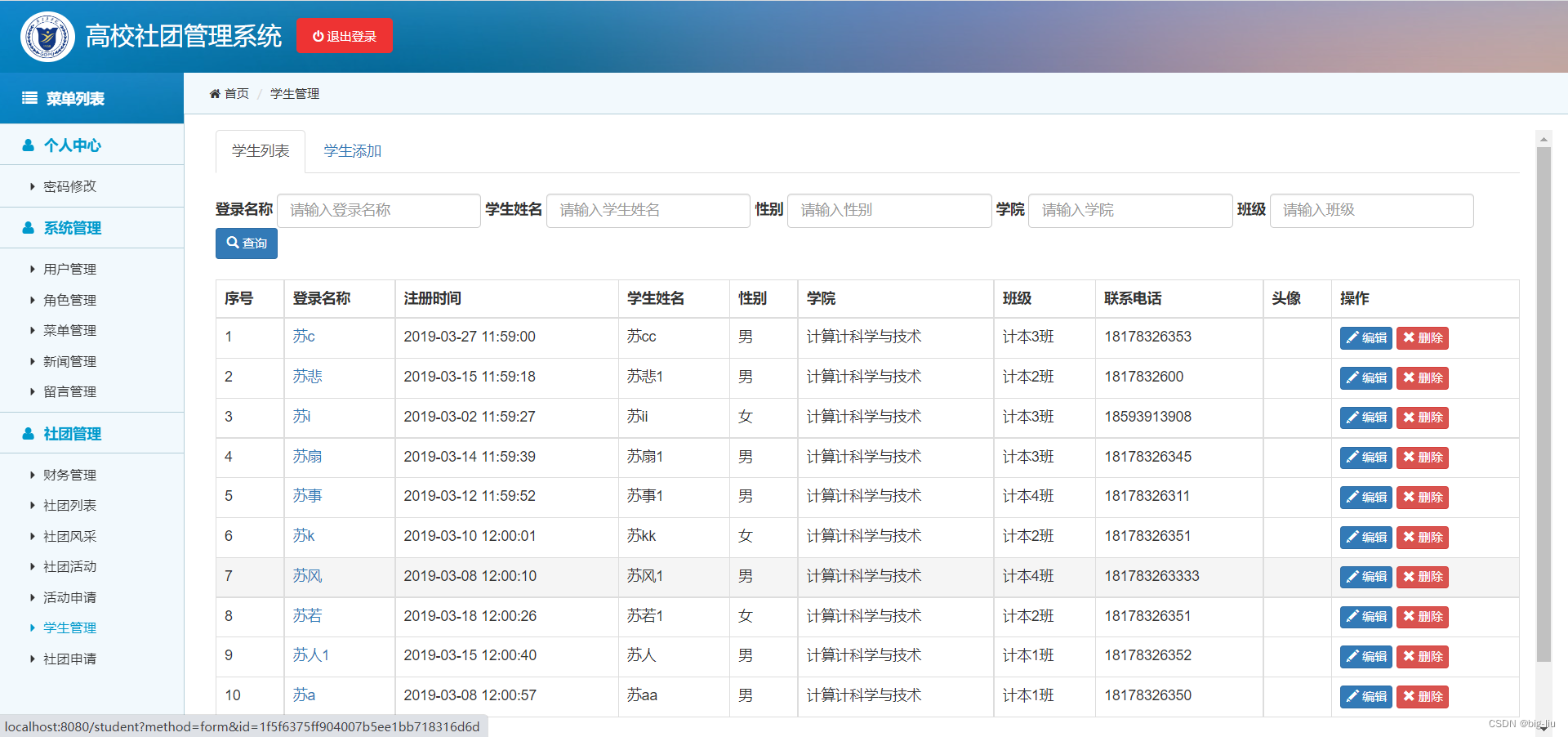
BiShe - College Student Association Management System Based on SSM
随机推荐
VMware Tools installation error: unable to automatically install vsock driver
Vulhub vulnerability recurrence 75_ XStream
Basic process and testing idea of interface automation
[Yu Yue education] Liaoning Vocational College of Architecture Web server application development reference
Mobilenet series (5): use pytorch to build mobilenetv3 and learn and train based on migration
DOM introduction
[solved] how to generate a beautiful static document description page
在产业互联网时代,将会凭借大的产业范畴,实现足够多的发展
Vulhub vulnerability recurrence 74_ Wordpress
3D model format summary
Recommended areas - ways to explore users' future interests
Code Review关注点
Mysql--- query the top 5 students
Daily practice - February 13, 2022
Pbootcms plug-in automatically collects fake original free plug-ins
伦敦银走势中的假突破
After 95, the CV engineer posted the payroll and made up this. It's really fragrant
servlet(1)
The inconsistency between the versions of dynamic library and static library will lead to bugs
SSH login is stuck and disconnected