当前位置:网站首页>Devsecops software R & D security practice - release
Devsecops software R & D security practice - release
2022-07-06 23:02:00 【Hua Weiyun】
Preface
When it comes to publishing , Will think of deployment , The deployment release discussed in this article is based on DevOps The background of . stay 《DevOps Practice Guide 》 These two words are clearly defined in , Deployment refers to installing a specified version of software in a specific environment , Publishing is to provide a feature or group of features to all customers or some customers . One is environment oriented technology operation , One is user oriented business decision . thus it can be seen , Deployment is the premise of release , Through continuous deployment , To support the on-demand release of business .
After software release , Software security problems caused by errors in the running phase account for a large proportion of all security problems . Release as The last line of defense before the software goes online , Have a pivotal position .
How to do a good job of safety release
Do a good job of safety release We focus on the incident response plan 、 Safety inspection 、 Look at the software signature certificate from three aspects .
Event response plan
In the software release stage , Enterprises need to establish a set of safety release Standards , There are corresponding release safety procedures and specifications , Safety incident response plan and release decision , Ensure that the release activities can be carried out safely and orderly .
Event response plan , Including but not limited to standard safety incident response process 、 Emergency safety incident response process , Person in charge of safety and contact information . Even products that do not contain any known vulnerabilities at the time of release , It may also face emerging threats in the future . It should be noted that , If the product contains third-party code , You also need to leave the contact information of the third party and join the event response plan , So that when a problem occurs, you can find the corresponding person .
Perfect safety incident response plan , After the software is released, the software supply chain security events 、 Software security vulnerability disclosure events can carry out rapid security response , Control and eliminate security threats and adverse effects caused by security incidents , Then trace and solve the root cause of the security incident .
Safety inspection
Before release , You need to use security analysis tools to conduct a comprehensive vulnerability scan , Execute the corresponding vulnerability repair plan according to the vulnerability scanning results . Vulnerability scanning can be done from the host 、 Mirror image 、Web、 Terminal applications 、 Scan multiple dimensions of network and database , Ensure full scene coverage .
Security check includes but is not limited to environment security deployment verification 、 Security configuration baseline detection 、 Image security scan 、 Virus scanning 、 Host vulnerability scanning and other activities , If possible, we can conduct a secondary review of all previous work , Conduct the final safety assessment according to the inspection results , Take the evaluation results as a precondition for release .
Release Stage The security problems solved are all security problems in the real production environment , Therefore, we should thoroughly check the configuration differences between the production environment and the development environment . Studies have shown that , Security vulnerabilities caused by security configuration errors in existing application systems have become one of the main sources of system vulnerabilities . Configuration management tools are a key factor in ensuring security during the release phase , Configuration management tools provide visibility into infrastructure configuration , Then you can audit and check the system configuration , Protect the runtime environment infrastructure . Common configuration management tools in the industry include Chef、Ansible、Puppet、Terraform and SaltStack.
During the release , Conduct security check at the security check node , There is a corresponding alarm mechanism , If you encounter problems and risks in the release, you can implement the security fallback and backup mechanism , Follow the safety incident response plan . At the same time, it is suggested to adopt a low-risk release strategy , Such as Canary release and blue-green release .
Software signatures and certificates
In order to prevent the software package from being maliciously tampered with during delivery or after release , Enterprises will add digital signatures to software codes , To ensure the authenticity and integrity of the code , Authenticity is to convince users of the source of this software , Integrity is to ensure that the software is not tampered with after it is released .
The code signing certificate is usually issued by a trusted third party CA Issued by , Compared with unsigned code , Code with certificates has higher reliability . Software developers can use code signing certificates to sign kernel code .sys file 、ActiveX file 、 .exe 、 and dll Documents and mobile application software developed by smart phones . Digital signatures protect users from viruses 、 By malicious code and spyware , It also protects the interests of software developers , So that the software can be released quickly and safely on the Internet .
After software release , Archive all kinds of problems and documents encountered , Help with emergency response and product upgrades .
Huawei cloud security release practice
Huawei cloud's multi scenario high-precision vulnerability scanning capability , It is a powerful guarantee to walk the last mile before the software goes online .
- Full scenario vulnerability coverage : Cover Web、 host 、 Mirror image 、 Binary system 、 Full scenario vulnerability scanning capability of terminal applications , Support for HUAWEI 、OWASP And so on , Support the insurance 0 Equal standard .
- Professional repair advice : Provide a typical Web Precise vulnerability detection , stay CVE Vulnerability assessment is closer to the real threat ; stay APK Open source component scanning and information leakage detection , With more accurate detection ability , Therefore, more professional repair suggestions can be provided .
- Scalable vulnerability detection capabilities : Focus on the latest security vulnerabilities , Dynamically expand scanning capabilities ; Flexible integration of third-party vulnerability scanning engine , Unified report presentation , Support loopholes to duplicate , It can also be integrated into third-party continuous integration / In the continuous release pipeline .
meanwhile , According to the release and deployment regulations of Huawei cloud , Developing 、 Deploy 、 In the process of going online , Self check must be completed , And promise to meet the operational requirements of online . For low-risk cloud services , Go online after passing the self inspection . The self inspection results are also submitted to the audit synchronously . Self inspection includes but is not limited to integrity verification 、 Engineering Baseline Review 、 Service self check 、 Promise safety and credibility 、 Container and infrastructure security, etc , At the same time, it will conduct retrospective analysis on safety problems , Rectify safety problems , Ensure the safety and credibility of the released products . For high-risk cloud services , Through more investment 、 In a short time to implement more stringent online testing and approval , Make sure it goes online in time and safely , Protect the interests of tenants .
At the end
Completing the security release is not the last step , Once the application is deployed in the online production environment and stabilized , It is necessary to start safety monitoring and operation and maintenance . As more and more development teams continue to improve their processes and adopt new tools , Security issues are becoming more and more important , Enterprises need to take it seriously .DevSecOps It's a circular process , It should be iterated continuously and applied to every new code deployment . Exploits and attackers are evolving , The development of security skills of software teams is also crucial .
Refer to appendix
1.《 Huawei cloud security white paper 》. Huawei Technology Co., Ltd .
2.《 R & D white paper on operational security 》. Cloud computing Open Source Industry Alliance .
3.《DevOps Practice Guide 》.Gene Kim,Jez Humble,Patrick Debois,John Willis. People's post and Telecommunications Press .
边栏推荐
- Windows Auzre 微软的云计算产品的后台操作界面
- MySQL实现字段分割一行转多行的示例代码
- Hard core observation 545 50 years ago, Apollo 15 made a feather landing experiment on the moon
- 【无标题】
- ACL 2022 | small sample ner of sequence annotation: dual tower Bert model integrating tag semantics
- ThreadLocal详解
- HDU 5077 NAND (violent tabulation)
- ICLR 2022 | pre training language model based on anti self attention mechanism
- MySQL中正则表达式(REGEXP)使用详解
- #DAYU200体验官# 在DAYU200运行基于ArkUI-eTS的智能晾晒系统页面
猜你喜欢
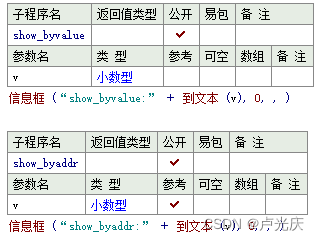
Aardio - does not declare the method of directly passing float values
金融人士必读书籍系列之六:权益投资(基于cfa考试内容大纲和框架)
None of the strongest kings in the monitoring industry!

Hard core observation 545 50 years ago, Apollo 15 made a feather landing experiment on the moon

动作捕捉用于蛇运动分析及蛇形机器人开发
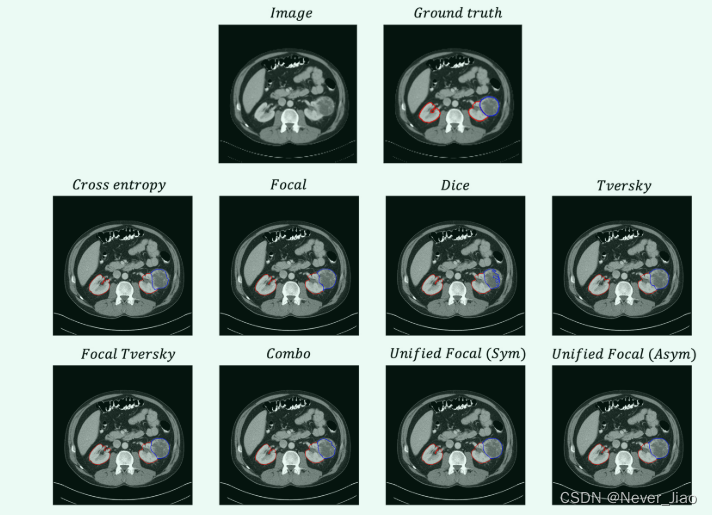
Unified Focal loss: Generalising Dice and cross entropy-based losses to handle class imbalanced medi
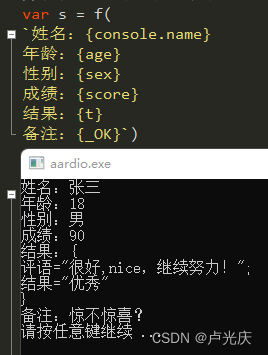
Aardio - integrate variable values into a string of text through variable names
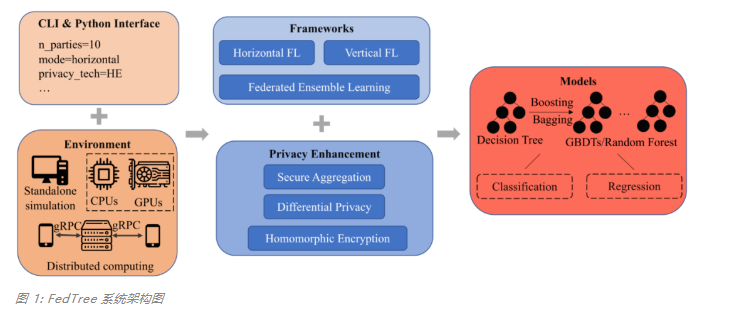
专为决策树打造,新加坡国立大学&清华大学联合提出快速安全的联邦学习新系统
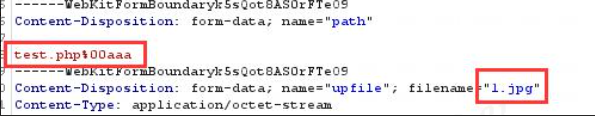
On file uploading of network security
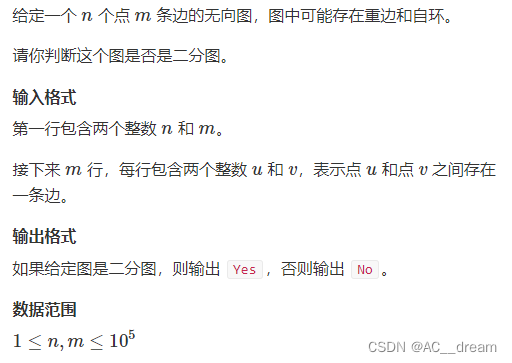
Bipartite graph determination
随机推荐
#DAYU200体验官# 首页aito视频&Canvas绘制仪表盘(ets)
UVa 11732 – strcmp() Anyone?
Chapter 19 using work queue manager (2)
关于声子和热输运计算中BORN电荷和non-analytic修正的问题
Puppeter connects to the existing Chrome browser
Designed for decision tree, the National University of Singapore and Tsinghua University jointly proposed a fast and safe federal learning system
COSCon'22 社区召集令来啦!Open the World,邀请所有社区一起拥抱开源,打开新世界~
How to achieve text animation effect
让我们,从头到尾,通透网络I/O模型
案例推荐丨安擎携手伙伴,保障“智慧法院”更加高效
poj 1094 Sorting It All Out (拓扑排序)
OpenSSL: a full-featured toolkit for TLS and SSL protocols, and a general encryption library
Children's pajamas (Australia) as/nzs 1249:2014 handling process
Aardio - integrate variable values into a string of text through variable names
DR-Net: dual-rotation network with feature map enhancement for medical image segmentation
服务器的系统怎么选者
【全网首发】Redis系列3:高可用之主从架构的
MySQL实现字段分割一行转多行的示例代码
树的先序中序后序遍历
UE4 blueprint learning chapter (IV) -- process control forloop and whileloop