当前位置:网站首页>Code debugging core step memory
Code debugging core step memory
2022-07-07 02:41:00 【Handsome drop point C】
Location method :
- gdb:
- adopt gdb For memory break points (watch) , See who illegally accessed the memory area . Then gradually narrow the scope . Until the corresponding function segment is found , such as :
- For example, discovery 0x800 The address is trampled .
- First, judge whether the address is legal , That is to say 0x800 Whether it should exist , If it should not exist , Then you can watch This address , You can also keep the code running , During this period, the address is continuously printed , See which code has been modified .
- For example, discovery 0x800 The address is trampled .
- limited
- The problem occurs in the startup phase , There is no time to set a breakpoint , Bad positioning ,
- Some systems do not support gdb
- Trampled address is not fixed
- adopt gdb For memory break points (watch) , See who illegally accessed the memory area . Then gradually narrow the scope . Until the corresponding function segment is found , such as :
- Problems like memory leaks , Predetermination , Post positioning , Through memory proc Information (meminfo/media-mem) Judgment is a specific module , Memory segment . It can also be used. MMU(linux You can use mrotect) Protect specific areas
- limited
- MMU The smallest unit of protection is a memory page , The area that may be trampled is small , No use mmu To protect
- limited
- Subtraction reduces the range , Clipping module , Modify the application , Find the smallest scene
- Add print , Print out the abnormal and suspicious address ; It's fine too dump Output the data of the trampled address , View data characteristics , Analyze where it comes from according to data characteristics .
- valgrind+effence+ksan Tools such as
Common questions
- Type conversion error
- For example, small to large , Including common char and int, And custom structures
- Including formal parameters
- Use the address that has been released
- such as malloc Or use without applying for control
- The requested memory is too small , Not enough use , Similar and cross-border
How to avoid
- Function nesting should not be too deep
- Code should be symmetrical ,malloc The corresponding position must be released
- Pay attention to the size of the array
边栏推荐
- Difference and the difference between array and array structure and linked list
- Common fitting models and application methods of PCL
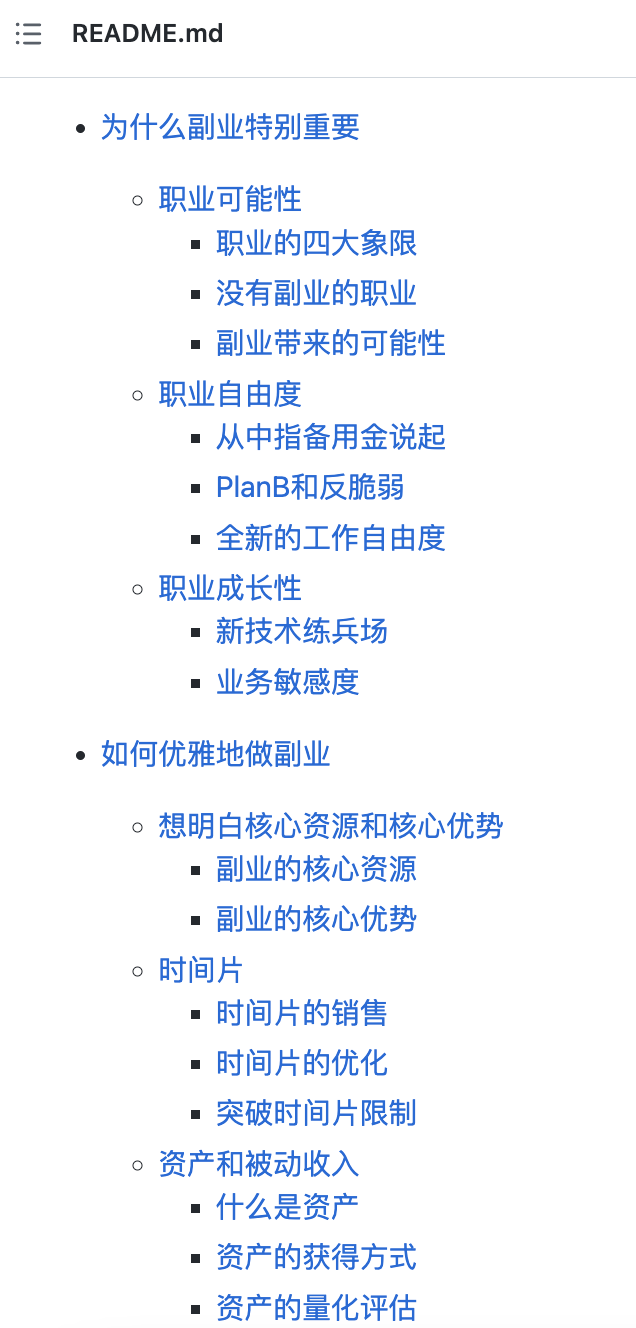
- 企业中台建设新路径——低代码平台
- postgresql 之 数据目录内部结构 简介
- [paper reading | deep reading] graphsage:inductive representation learning on large graphs
- QT常见概念-1
- fiddler的使用
- 所谓的消费互联网仅仅只是做行业信息的撮合和对接,并不改变产业本身
- Pgadmin4 of PostgreSQL graphical interface tool
- Here comes a white paper to uncover the technology behind Clickhouse, a node with 10000 bytes!
猜你喜欢
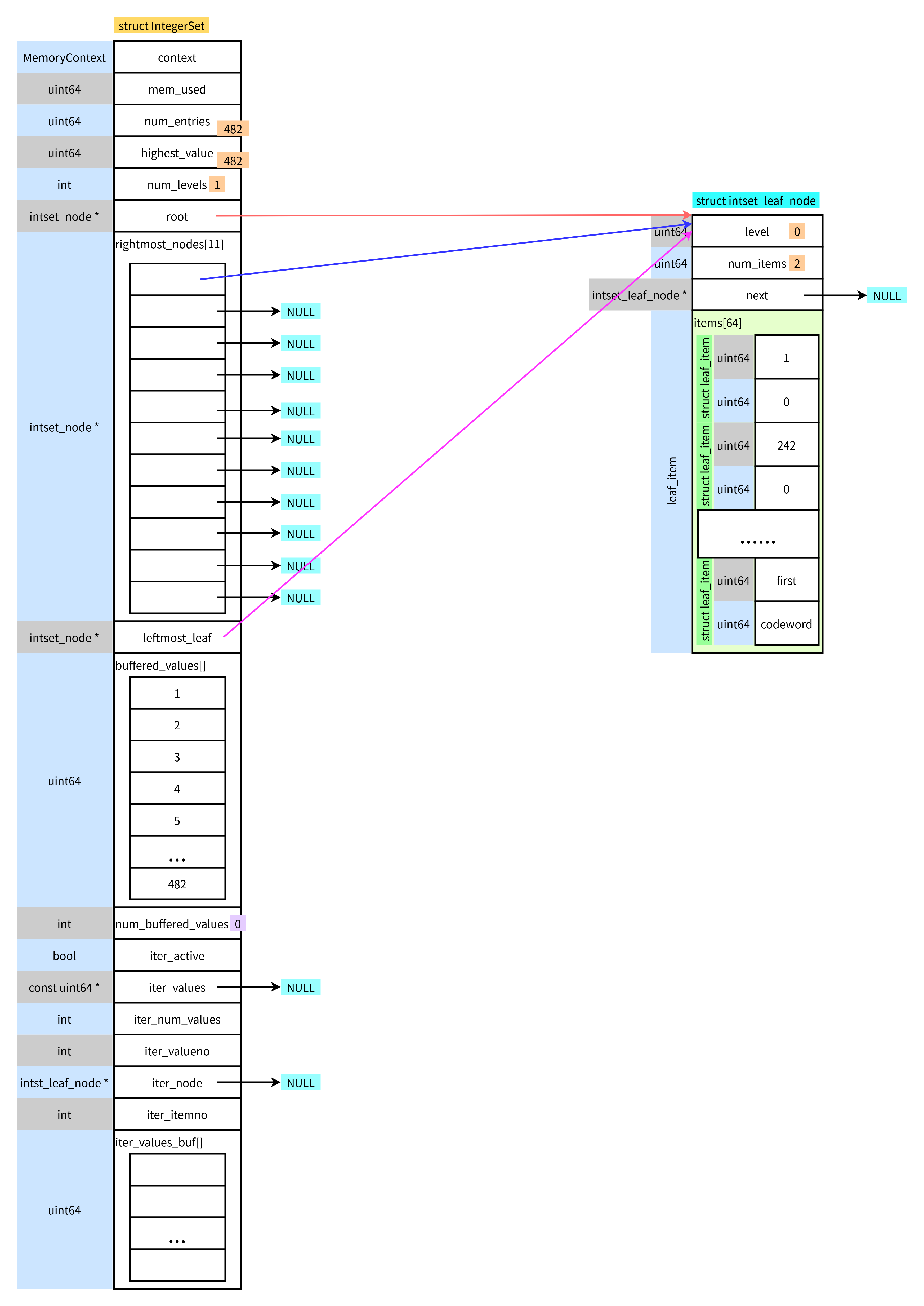
Integerset of PostgreSQL
Niuke programming problem -- double pointer of 101 must be brushed
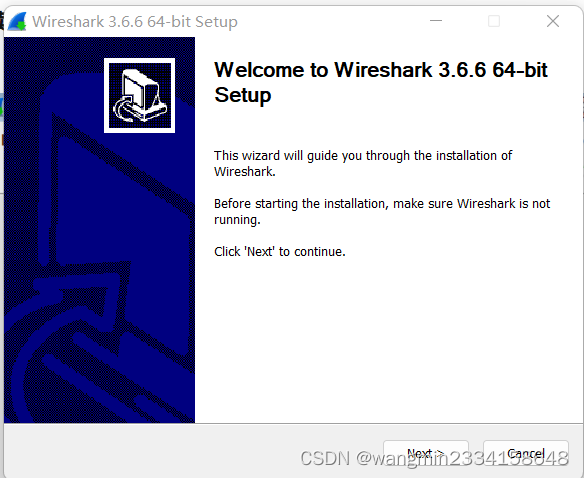
Wireshark installation
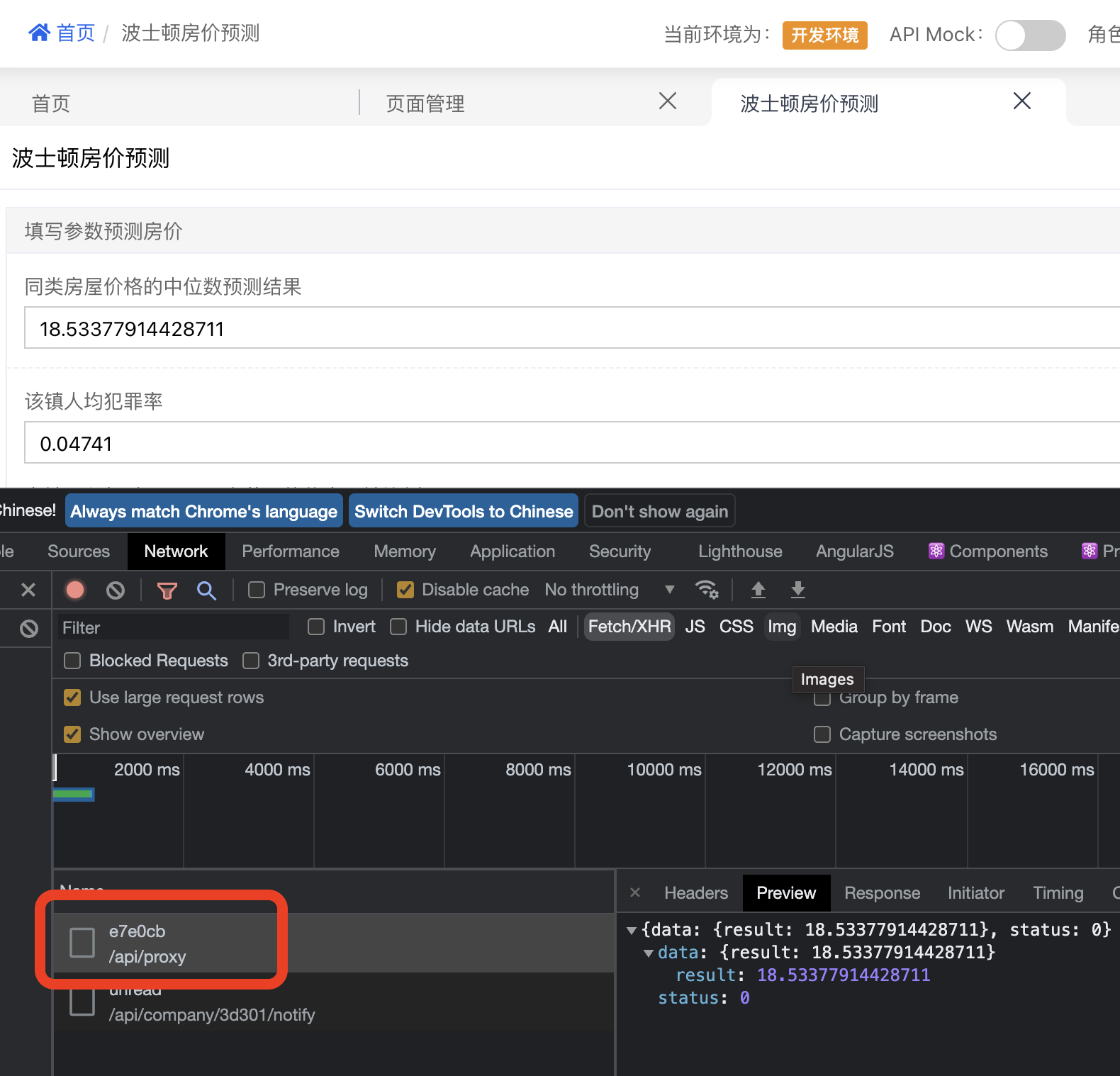
Data connection mode in low code platform (Part 1)
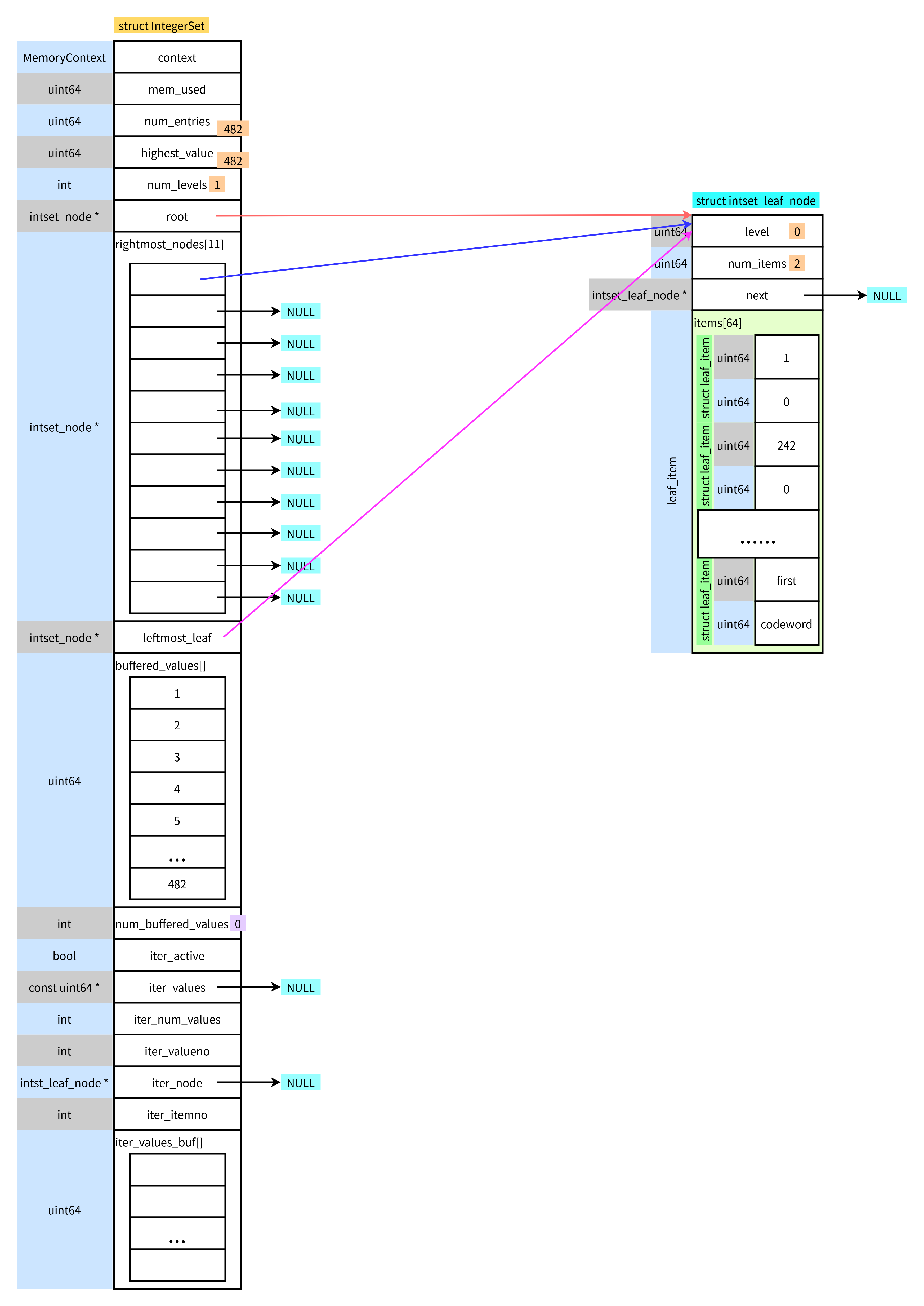
postgresql之integerset
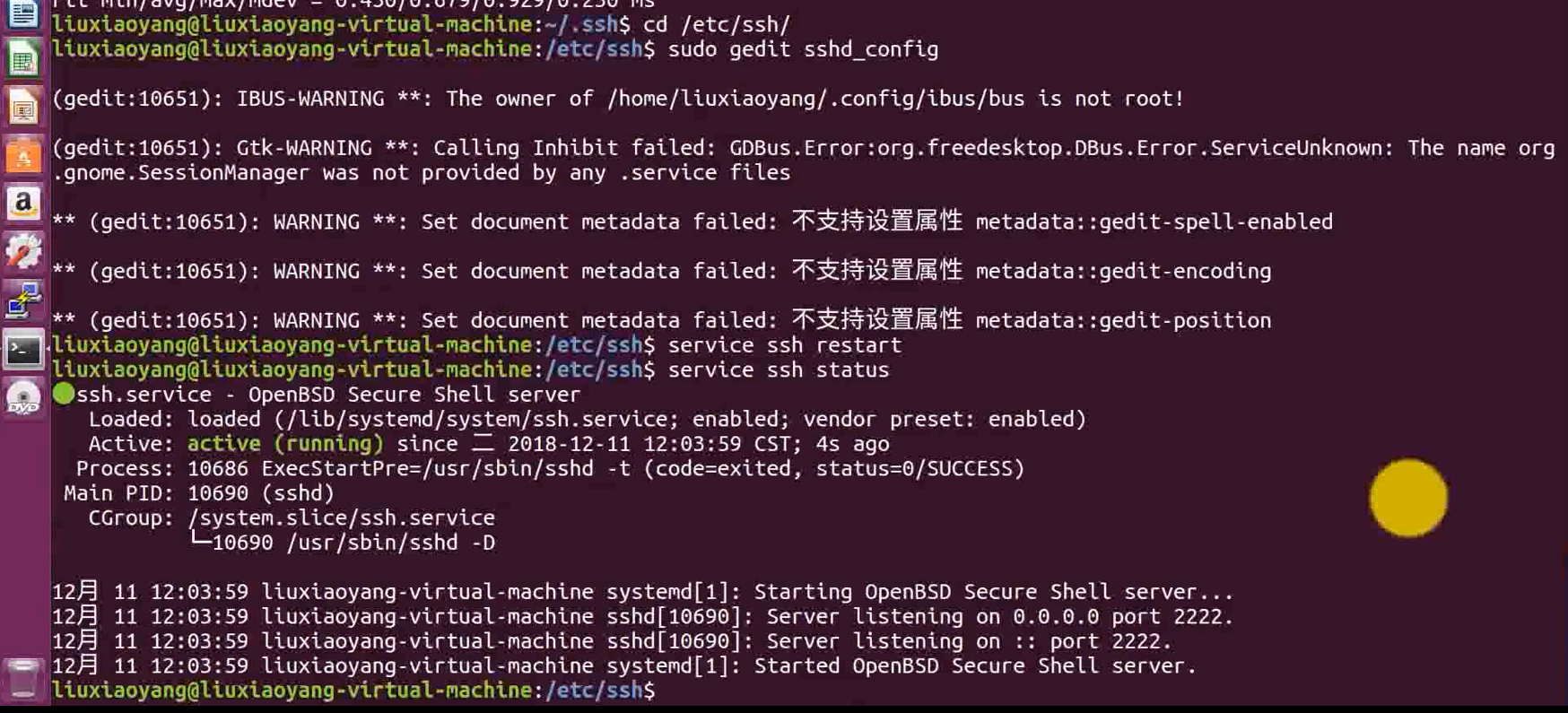
6-6 vulnerability exploitation SSH security defense
This week's hot open source project!
![leetcode:5. Longest palindrome substring [DP + holding the tail of timeout]](/img/62/d4d5428f69fc221063a4f607750995.png)
leetcode:5. Longest palindrome substring [DP + holding the tail of timeout]

Electrical engineering and automation
KYSL 海康摄像头 8247 h9 isapi测试
随机推荐
[unity notes] screen coordinates to ugui coordinates
[leetcode]Search for a Range
测试优惠券要怎么写测试用例?
HAVE FUN | “飞船计划”活动最新进展
B站6月榜单丨飞瓜数据UP主成长排行榜(哔哩哔哩平台)发布!
Electrical engineering and automation
Google Earth Engine(GEE)——Landsat 全球土地调查 1975年数据集
How to build a 32core raspberry pie cluster from 0 to 1
Draco - gltf model compression tool
MySQL - common functions - string functions
所谓的消费互联网仅仅只是做行业信息的撮合和对接,并不改变产业本身
Mmdetection3d loads millimeter wave radar data
unity webgl自适应网页尺寸
Why am I warned that the 'CMAKE_ TOOLCHAIN_ FILE' variable is not used by the project?
Data connection mode in low code platform (Part 1)
PostgreSQL图形化界面工具之pgAdmin4
运维管理系统有哪些特色
[C # notes] use file stream to copy files
MySQL --- 常用函数 - 字符串函数
Cloud Mail .NET Edition