当前位置:网站首页>Complex network modeling (II)
Complex network modeling (II)
2022-07-07 08:06:00 【Dam head count】
Betweenness
Intermediate numbers are divided into node intermediate numbers and edge intermediate numbers , It reflects the role and influence of nodes or edges in the whole network .
The number of nodes Bi Defined as
B i = ∑ j ≠ l ≠ i [ N j l ( i ) / N j l ] B_i=\sum_{j\neq l\neq i}^{}[N_{jl}(i)/N_jl] Bi=j=l=i∑[Njl(i)/Njl]
among ,Njl Representation node Vj And nodes Vl The number of shortest paths between ,Njl(i) Representation node Vj And nodes Vl The shortest path between nodes Vi The article number .
The intermediate number of edges Bij Defined as
B i j = ∑ ( l , m ) ≠ ( i , j ) [ N l m ( e i j ) / N l m ] B_{ij}=\sum_{ {(l,m)}\neq (i,j)}^{}[N_{lm}(e_{ij})/N_lm] Bij=(l,m)=(i,j)∑[Nlm(eij)/Nlm]
In style ,Nlm Representation node Vl and Vm The number of shortest paths between ,Nlm(eij) Representation node Vl and Vm The shortest path between passes through the edge eij The article number .
Nuclear degree
A graph of k- Core refers to the value of repeated removal degree less than k Node and its connection , Remaining subgraphs , The number of nodes of the subgraph is the size of the kernel .
The maximum value of the node kernel degree is called the network kernel degree .
Network density
Network density refers to the degree of tightness between nodes in a network . The Internet G Network density d(G) Defined as
d ( G ) = 2 M / [ N ( N − 1 ) ] d(G)=2M/[N(N-1)] d(G)=2M/[N(N−1)]
M Is the number of connections actually owned in the network ,N Is the number of network nodes , When the network is fully connected , The density is 1.
边栏推荐
- The legend about reading the configuration file under SRC
- Leetcode 40: combined sum II
- Few shot Learning & meta learning: small sample learning principle and Siamese network structure (I)
- 【无标题】
- DNS server configuration
- Qt学习26 布局管理综合实例
- Relevant data of current limiting
- 青龙面板--整理能用脚本
- 2022 welder (elementary) judgment questions and online simulation examination
- Lattice coloring - matrix fast power optimized shape pressure DP
猜你喜欢
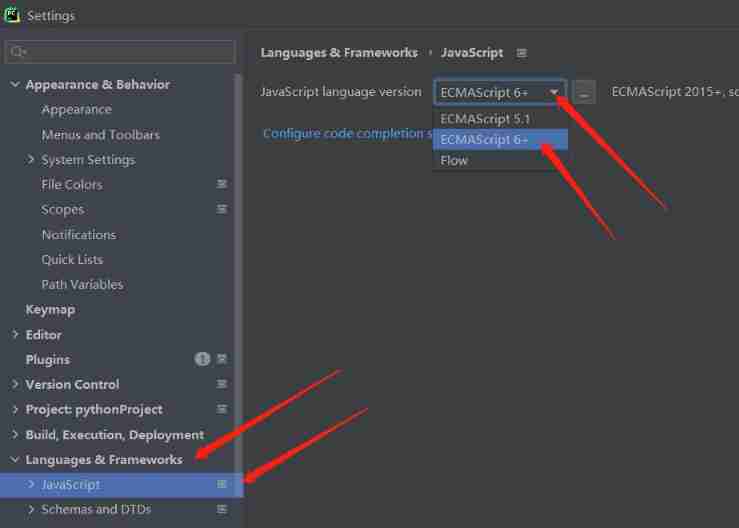
JS quick start (I)
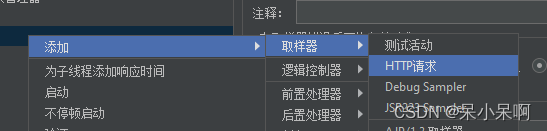
Jmeter 的使用
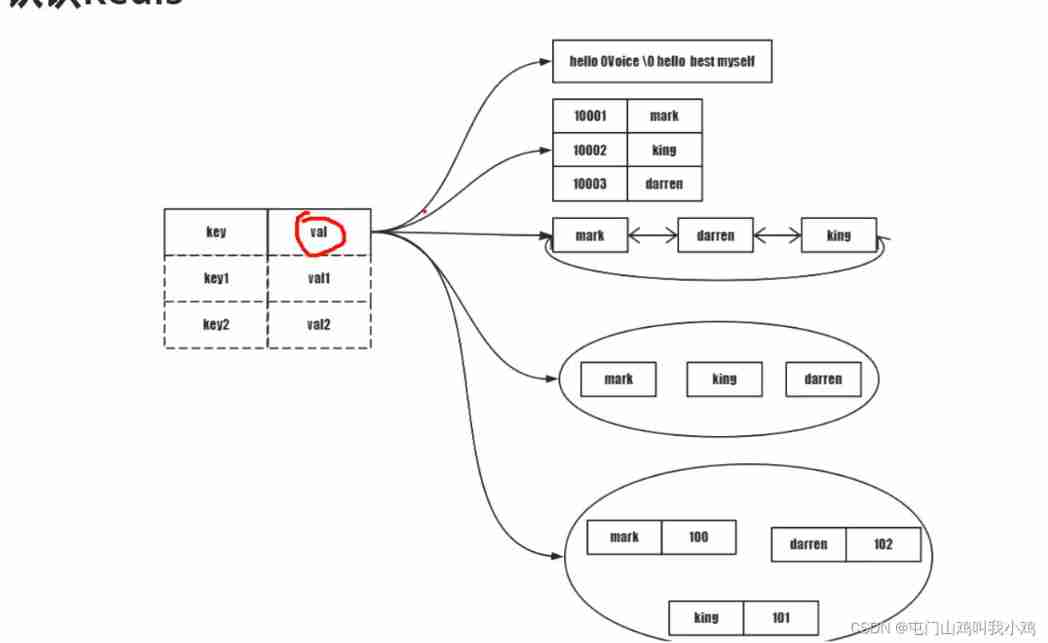
Linux server development, detailed explanation of redis related commands and their principles

2022年茶艺师(中级)考试试题及模拟考试
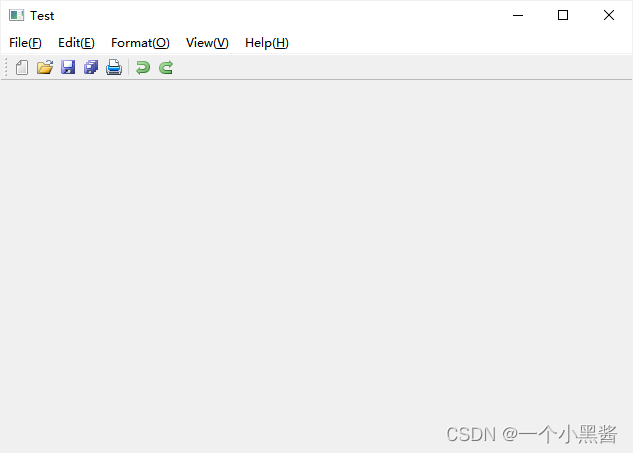
Qt学习28 主窗口中的工具栏
Linux server development, MySQL index principle and optimization
Detailed explanation of Kalman filter for motion state estimation

2022 National latest fire-fighting facility operator (primary fire-fighting facility operator) simulation questions and answers
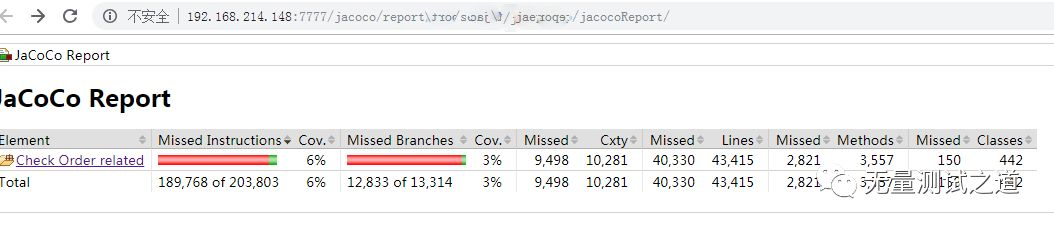
快速使用 Jacoco 代码覆盖率统计

Shell 脚本的替换功能实现
随机推荐
Force buckle 145 Binary Tree Postorder Traversal
Summary of redis functions
3D reconstruction - stereo correction
Custom class loader loads network class
MySQL multi column index (composite index) features and usage scenarios
Linux server development, detailed explanation of redis related commands and their principles
Linux server development, SQL statements, indexes, views, stored procedures, triggers
Topic not received? Try this
JS cross browser parsing XML application
[UVM practice] Chapter 1: configuring the UVM environment (taking VCs as an example), run through the examples in the book
buureservewp(2)
JS quick start (I)
json 数据展平pd.json_normalize
Wechat applet data binding multiple data
Blob 對象介紹
Dedecms collects content without writing rules
LeetCode简单题之字符串中最大的 3 位相同数字
[VHDL parallel statement execution]
2022 simulated examination question bank and online simulated examination of tea master (primary) examination questions
2022茶艺师(初级)考试题模拟考试题库及在线模拟考试