当前位置:网站首页>DNS server configuration
DNS server configuration
2022-07-07 08:04:00 【redcell5】
linux build dns The server
Requirements are as follows : Configure the domain name :test.com—>192.168.114.2
Modify the following documents :
/etc/named.conf
/var/named/named.domain.zones
/var/named/named. Custom domain name .zone, Such as :/var/named/named.test.com.zone
First step : edit /var/named/named.test.com.zone, The contents are as follows
$TTL 1D
@ IN SOA @ rname.invalid. (
0 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ; minimum
)
NS @
A 192.168.114.2
www A 192.168.114.2
The second step : edit /var/named/named.domain.zones, The contents are as follows
zone "test.com" IN {
type master;
file "named.test.com.zone";
};
The third step : Set up dns port , Modify the following contents in the file :/etc/named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
options {
listen-on port 53 {
any; };
listen-on-v6 port 53 {
any; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
secroots-file "/var/named/data/named.secroots";
recursing-file "/var/named/data/named.recursing";
allow-query {
any; };
/*
- If you are building an AUTHORITATIVE DNS server, do NOT enable recursion.
- If you are building a RECURSIVE (caching) DNS server, you need to enable
recursion.
- If your recursive DNS server has a public IP address, you MUST enable access
control to limit queries to your legitimate users. Failing to do so will
cause your server to become part of large scale DNS amplification
attacks. Implementing BCP38 within your network would greatly
reduce such attack surface
*/
recursion yes;
dnssec-enable yes;
dnssec-validation yes;
managed-keys-directory "/var/named/dynamic";
pid-file "/run/named/named.pid";
session-keyfile "/run/named/session.key";
/* https://fedoraproject.org/wiki/Changes/CryptoPolicy */
include "/etc/crypto-policies/back-ends/bind.config";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones";
include "/etc/named.root.key";
include "/var/named/named.domain.zones";
Step four : restart dns service
systemctl restart named
Step five :linux Specify domain name server
[[email protected] ~]# cat /etc/resolv.conf
# Generated by NetworkManager
# nameserver 200.200.10.199
nameserver 192.168.114.2
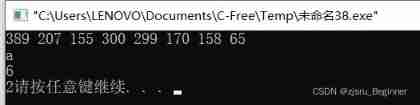
Step six : test
[[email protected] ~]# nslookup test.com
Server: 192.168.114.2
Address: 192.168.114.2#53
Name: test.com
Address: 192.168.114.2
[[email protected] ~]# nslookup www.test.com
Server: 192.168.114.2
Address: 192.168.114.2#53
Name: www.test.com
Address: 192.168.114.2
[[email protected] ~]#
Reference material :https://www.cnblogs.com/reader/p/5616181.html
Learn knowledge
"sed -i 's/port\s+\d+\s*{/port hash[:port]{/g' /etc/named.conf"
"sed -i '/named.domain.zones/d' /etc/named.conf" # Delete include named.domain.zones Line of string
"echo 'include \"#{domain_zones_file}\";' >> /etc/named.conf"
"sed 's/::1;/any;/g' -i #{named_conf_file}" # Replace a string
边栏推荐
- 2022 Inner Mongolia latest advanced fire facility operator simulation examination question bank and answers
- Common method signatures and meanings of Iterable, collection and list
- 这5个摸鱼神器太火了!程序员:知道了快删!
- Linux server development, detailed explanation of redis related commands and their principles
- 2022 tea master (intermediate) examination questions and mock examination
- Common validation comments
- mysql多列索引(组合索引)特点和使用场景
- Sign up now | oar hacker marathon phase III, waiting for your challenge
- 2022年全国最新消防设施操作员(初级消防设施操作员)模拟题及答案
- 追风赶月莫停留,平芜尽处是春山
猜你喜欢

2022年茶艺师(中级)考试试题及模拟考试
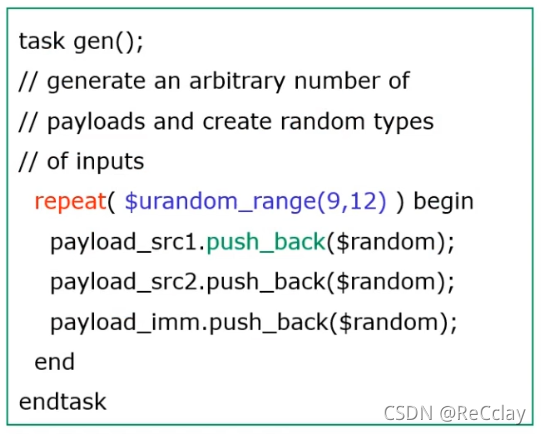
【数字IC验证快速入门】12、SystemVerilog TestBench(SVTB)入门
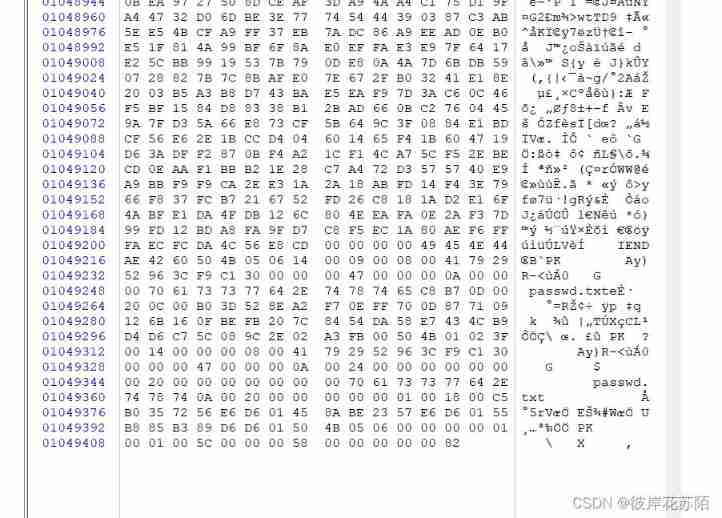
Bugku CTF daily one question chessboard with only black chess
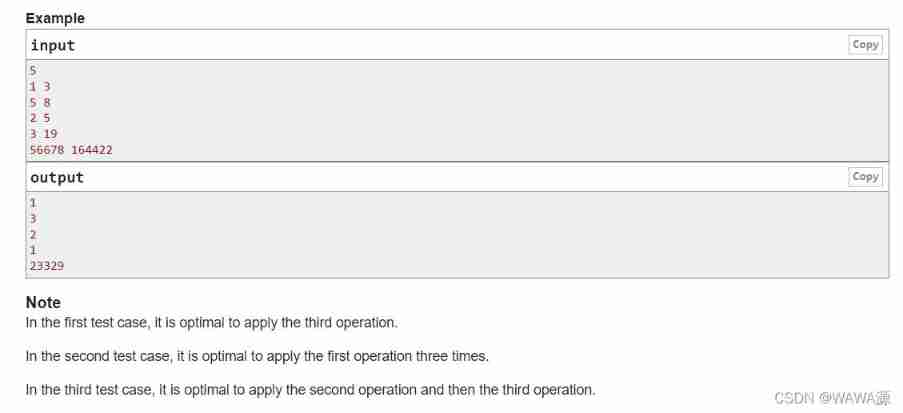
Codeforce c.strange test and acwing

3D reconstruction - stereo correction
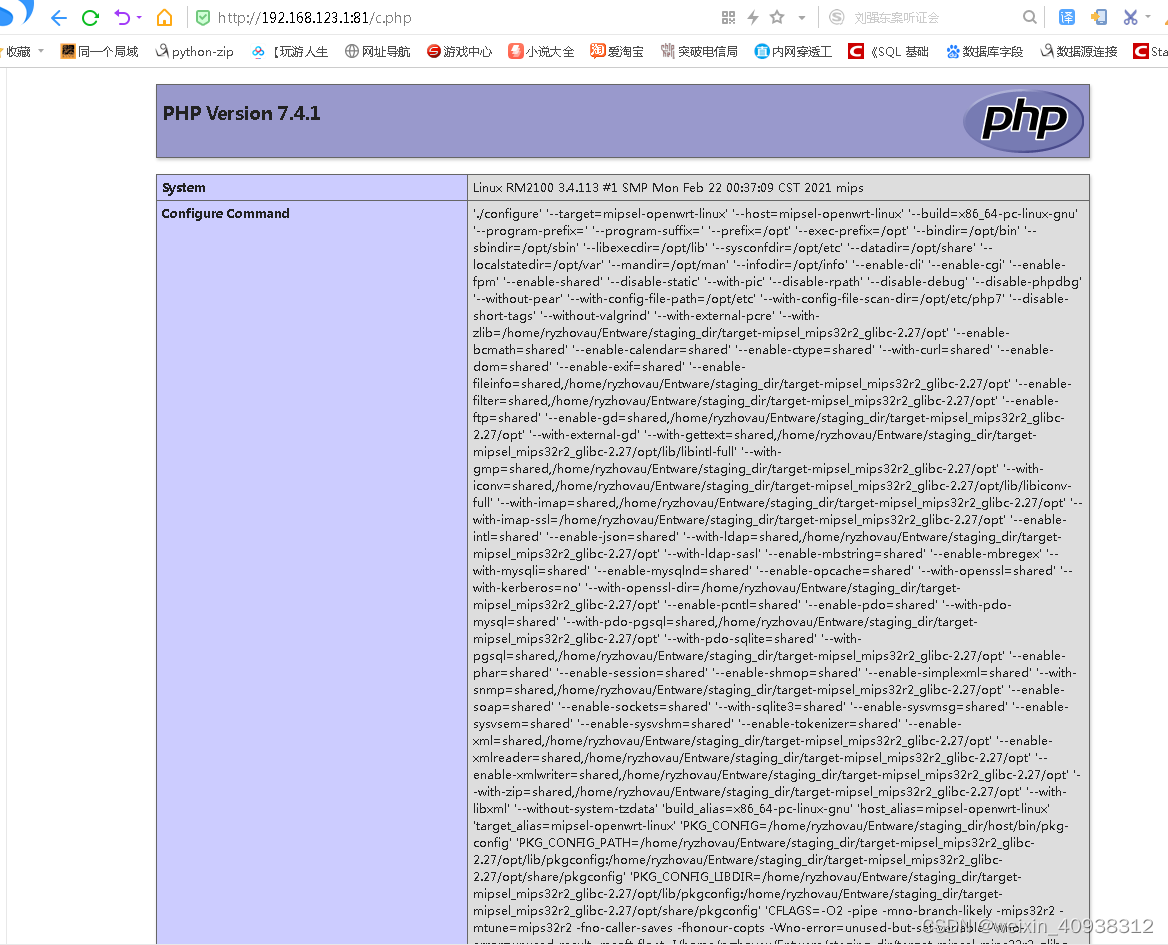
padavan手动安装php
Yugu p1020 missile interception (binary search)

Shell 脚本的替换功能实现

Content of string
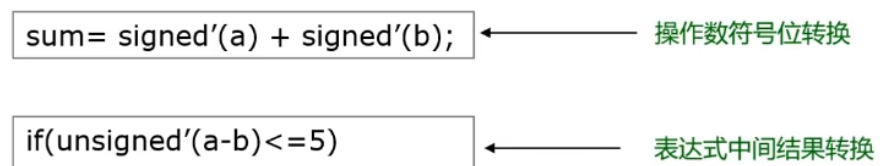
【数字IC验证快速入门】15、SystemVerilog学习之基本语法2(操作符、类型转换、循环、Task/Function...内含实践练习)
随机推荐
央视太暖心了,手把手教你写HR最喜欢的简历
微信小程序基本组件使用介绍
Common method signatures and meanings of Iterable, collection and list
QT learning 28 toolbar in the main window
Linux server development, redis source code storage principle and data model
Record a stroke skin bone error of the skirt
Who has docker to install MySQL locally?
[2022 ciscn] replay of preliminary web topics
Installing postgresql11 database under centos7
[matlab] when matrix multiplication in Simulink user-defined function does not work properly, matrix multiplication module in module library can be used instead
Numbers that appear only once
【数字IC验证快速入门】10、Verilog RTL设计必会的FIFO
Content of string
【数字IC验证快速入门】13、SystemVerilog interface 和 program 学习
[UVM basics] summary of important knowledge points of "UVM practice" (continuous update...)
Topic not received? Try this
Implementation of replacement function of shell script
Main window in QT learning 27 application
即刻报名|飞桨黑客马拉松第三期等你挑战
Leetcode 43 String multiplication (2022.02.12)