当前位置:网站首页>F. Min cost string problem solving Report
F. Min cost string problem solving Report
2022-07-05 15:25:00 【wch(】
F. Min Cost String Problem solving report
label : character string structure
subject
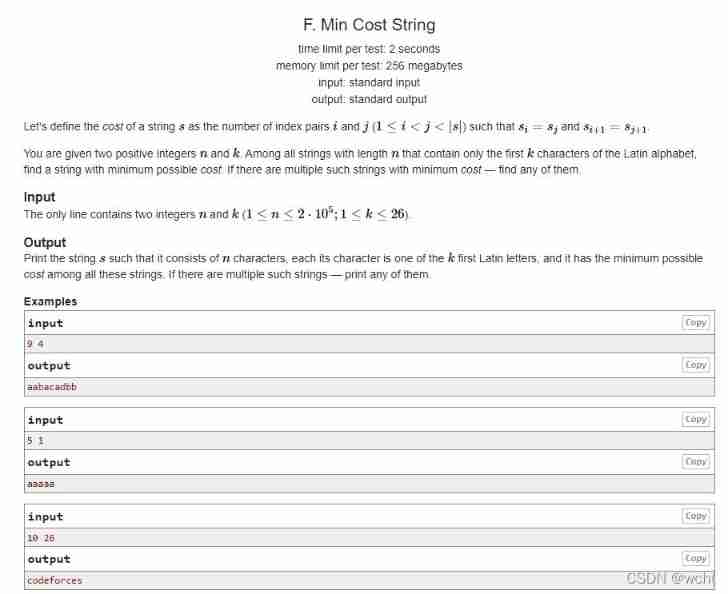
The question :
Give constant n,k, Let's use before k Lowercase letters are constructed with a length of n String
Letters can be in front k Any use or no use within the scope , But it is required to minimize the index pairs in the output string
When s[i]=s[j] And is s[i+1]=s[j+1] (1≤i<j<|s|) It constitutes an index pair
Their thinking :
To minimize index pairs , We can divide the string into one-to-one pairs ,
such as s=aaba At this time, we see three pairs aa ab ba It has been taken
Then the next idea is to list all Character pair Add to s in
If the string length is greater than or equal to n Before output n Characters
If the length of the character string is less than n
Because all the character pairs that can be formed are already in s It's in No matter what you add, there will be index pairs
We let s += s Until the length is greater than n Before interception n Character output
resize Function usage
When n The length is less than the string s The length of s.resize(n), Intercept s front n Characters
When n The length is greater than the string s The length of char a; s.resize(n,a), stay s Add characters after a until s Length up to n
Code implementation
#include <iostream>
#include <string>
using namespace std;
int main(){
long long n,k;
cin>>n>>k;
string s("");
for(int i=0;i<k;i++){
s+='a'+i;
for(int j=i+1;j<k;j++)
{
s+='a'+i;
s+='a'+j;
}
}
while(s.size()<n)s+=s;
s.resize(n);
cout<<s<<endl;
}
边栏推荐
- What are CSRF, XSS, SQL injection, DDoS attack and timing attack respectively and how to prevent them (PHP interview theory question)
- P6183 [USACO10MAR] The Rock Game S
- OSI 七层模型
- Bugku telnet
- How to paste the contents copied by the computer into mobaxterm? How to copy and paste
- MySQL表字段调整
- lvgl 显示图片示例
- Magic methods and usage in PHP (PHP interview theory questions)
- 当代人的水焦虑:好水究竟在哪里?
- Bugku's Ah Da
猜你喜欢

CSRF, XSS science popularization and defense
做研究无人咨询、与学生不交心,UNC助理教授两年教职挣扎史
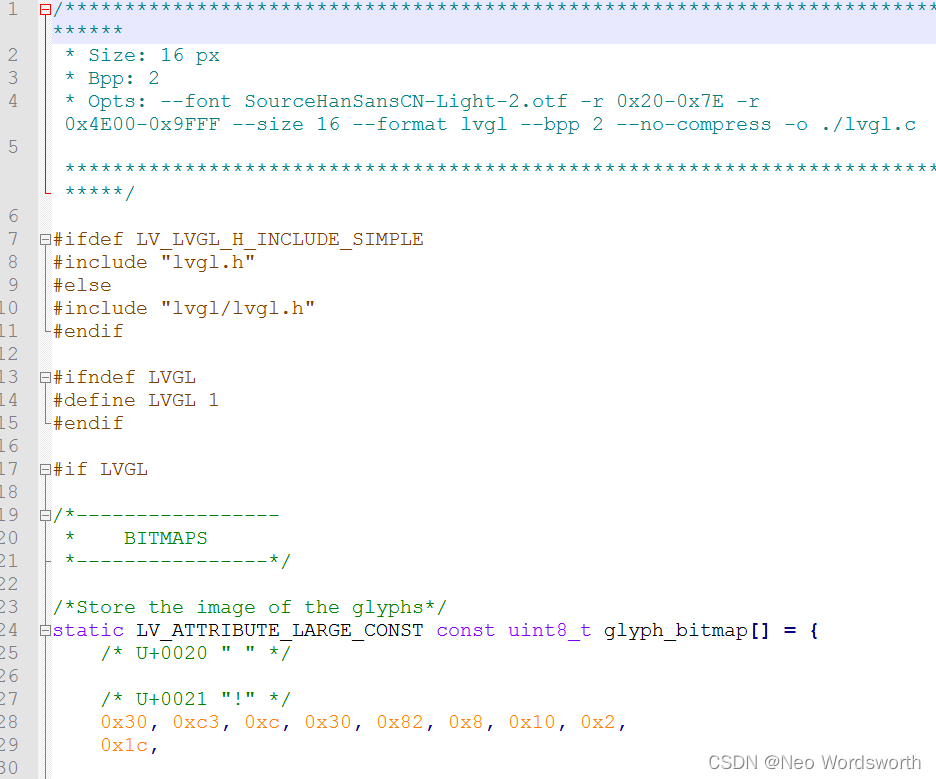
lv_font_conv离线转换

P1451 求细胞数量/1329:【例8.2】细胞

Stop B makes short videos, learns Tiktok to die, learns YouTube to live?

Bugku's steganography
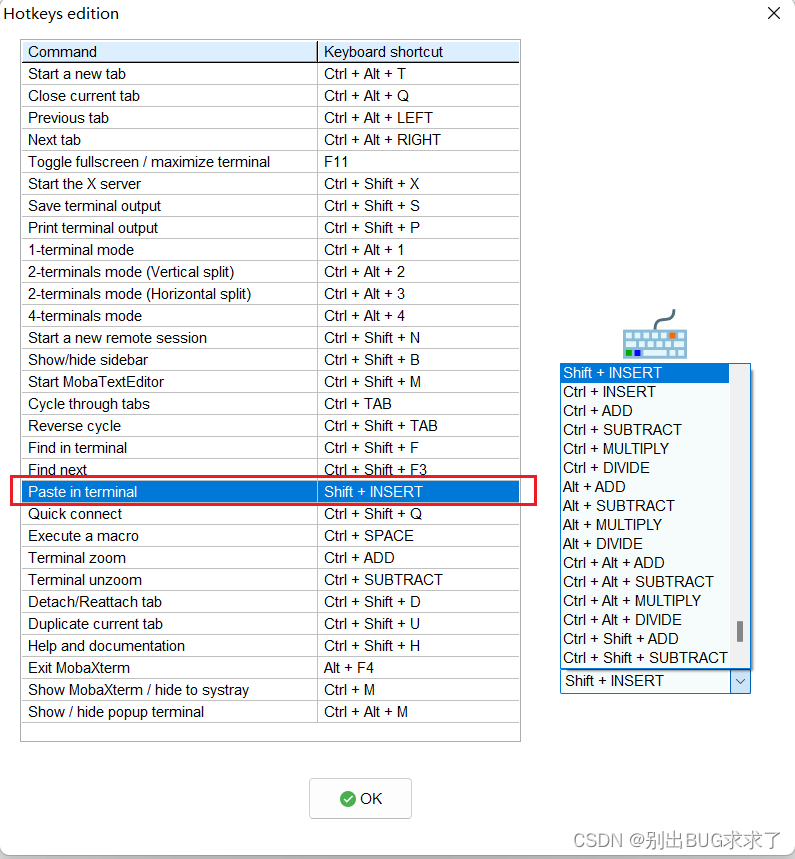
How to paste the contents copied by the computer into mobaxterm? How to copy and paste
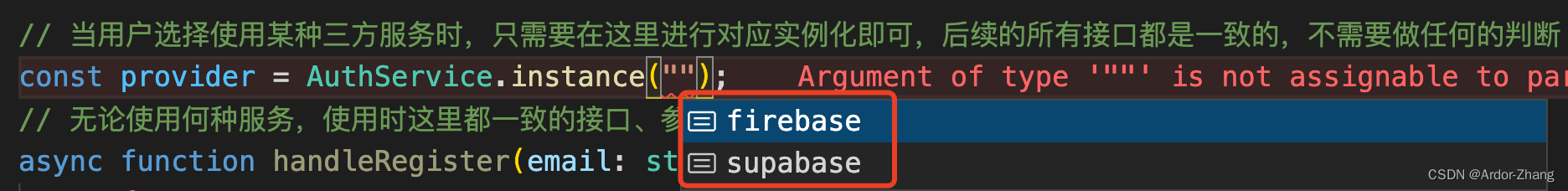
把 ”中台“ 的思想迁移到代码中去
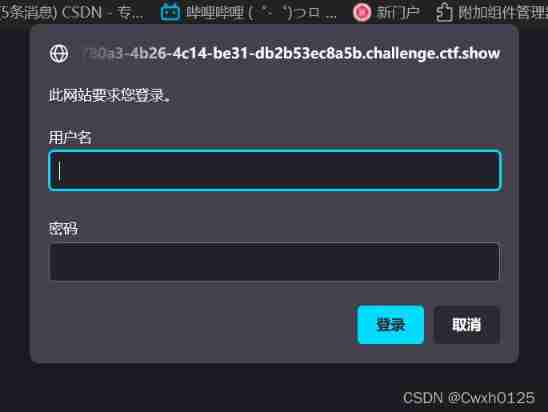
Ctfshow web entry explosion

社区团购撤城“后遗症”
随机推荐
Visual task scheduling & drag and drop | scalph data integration based on Apache seatunnel
Creation and optimization of MySQL index
Bugku easy_ nbt
Go learning ----- relevant knowledge of JWT
Huiyuan, 30, is going to have a new owner
mapper.xml文件中的注释
机器学习笔记 - 灰狼优化
R 熵权法计算权重及综合得分
Ctfshow web entry command execution
I spring and autumn blasting-1
P6183 [USACO10MAR] The Rock Game S
Common redis data types and application scenarios
CPU design practice - Chapter 4 practical task 2 using blocking technology to solve conflicts caused by related problems
No one consults when doing research and does not communicate with students. UNC assistant professor has a two-year history of teaching struggle
Calculate weight and comprehensive score by R entropy weight method
Live broadcast preview | how to implement Devops with automatic tools (welfare at the end of the article)
Usage and usage instructions of JDBC connection pool
[JVM] operation instruction
SQL Server learning notes
CPU design practice - Chapter 4 practice task 3 use pre delivery technology to solve conflicts caused by related issues