当前位置:网站首页>[the 300th weekly match of leetcode]
[the 300th weekly match of leetcode]
2022-07-06 18:20:00 【ღCauchyོꦿ࿐】
List of articles
Decrypt the message
subject
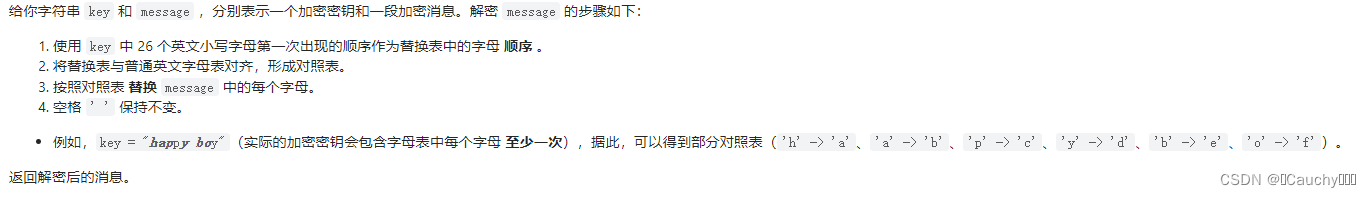
Ideas
- simulation , Just mark it .
Code
class Solution {
public:
string decodeMessage(string key, string message) {
string res = "";
int n = key.size();
bool st[26] = {
0};
map<char, int> mp;
int now = 0;
for (int i = 0; i < n; i++) {
if(key[i] == ' ') continue;
if(!st[key[i] - 'a']) {
st[key[i] - 'a'] = true;
mp[key[i]] = now;
now ++;
}
}
for (int i = 0; i < message.size(); i++) {
if(message[i] == ' ') res += ' ';
else {
res += mp[message[i]] + 'a';
}
}
return res;
}
};
Spiral matrix IV
subject
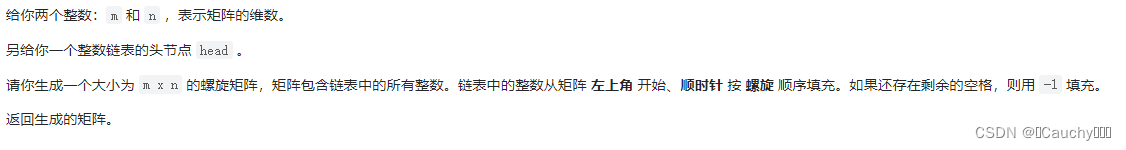
Ideas
- Set the current direction n o w now now,(0、1、2、3) Corresponding direction array w a l k walk walk.
- Set up, down, left and right (lx、rx、ly、ry) Four borders , Adjust when turning the direction .
Code
class Solution {
public:
vector<vector<int>> spiralMatrix(int m, int n, ListNode* head) {
vector<vector<int>> res(m, vector<int>(n, -1));
ListNode *p = head;
if(p == nullptr) return res;
vector<int> v;
while(p) {
v.push_back(p->val); p = p->next; }
int x = 0, y = -1;
int walk[4][2] = {
0, 1, 1, 0, 0, -1, -1, 0};
int now = 0;
int lx = 0, rx = m - 1, ly = 0, ry = n - 1;
for (int i = 0; i < v.size(); i++) {
int dx = x + walk[now][0], dy = y + walk[now][1];
if(dx > rx || dx < lx || dy > ry || dy < ly) {
if(now == 0) lx += 1;
if(now == 1) ry -= 1;
if(now == 2) rx -= 1;
if(now == 3) ly += 1;
now = (now + 1) % 4;
dx = x + walk[now][0], dy = y + walk[now][1];
}
res[dx][dy] = v[i];
x = dx, y = dy;
}
return res;
}
};
Number of people who know the secret
subject
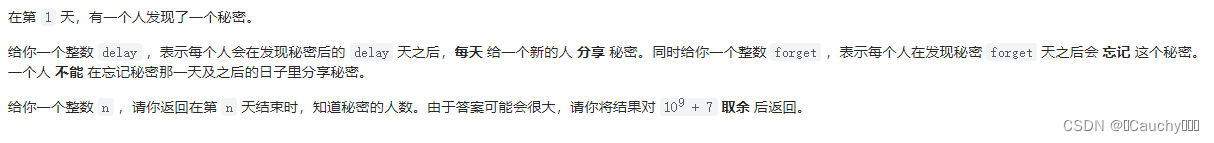
Ideas
I thought at first , Just take a dynamic array , Simulated deletion 、 The process of adding people . But time , The space cost is bound to be great .
This needs to be optimized :
- It is found that for the i i i God : In the current collection Everyone who can share secrets ( i > = x + d e l a y i>=x+delay i>=x+delay), New people added , Their state ( Time is the beginning i i i God 、delay、forget) All are consistent .( This is equivalent to that we don't need to add everyone one by one , Instead, you can directly replace it with a variable equivalent )
- Find that time is monotonically increasing , Parameters d e l a y 、 f o r g e t delay、forget delay、forget Is constant , Then the latter must be later than the former .
Here I use m a p < i n t , i n t > map<int, int> map<int,int> For storage : The first i i i God , The number of j j j.
Code
class Solution {
public:
constexpr static int mod = 1e9 + 7;
int peopleAwareOfSecret(int n, int delay, int forget) {
map<int, int> mp;
int res = 0;
mp[1] = 1;
for (int i = 2; i <= n; i++) {
int cnt = 0;
for (auto &x: mp) {
int a = x.first, b = x.second;
if(i >= a + forget) {
mp.erase(a); continue; }
if (i >= a + delay) cnt = (cnt + b) % mod;
}
mp.insert({
i, cnt});
}
for (auto &x: mp) res = (res + x.second) % mod;
return res % mod;
}
};
The number of incremental paths in the grid graph
subject
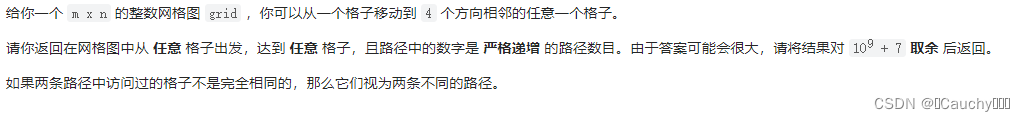
Ideas
- Memory search
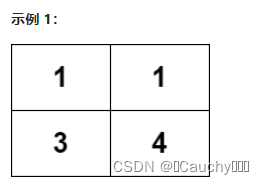
Consider the example illustration
3->4:1
1->3、1->3->4: 2
Adjacent can arrive , State shift d p [ i ] [ j ] = d p [ x ] [ y ] + 1 dp[i][j] = dp[x][y] + 1 dp[i][j]=dp[x][y]+1.
Code
class Solution {
public:
constexpr static int mod = 1e9 + 7;
int n, m;
int walk[4][2] = {
0, 1, 1, 0, 0, -1, -1, 0};
int dfs(int x, int y, vector<vector<int>>& grid, vector<vector<int>>& dp) {
int s = 0;
for (int i = 0; i < 4; i++) {
int dx = x + walk[i][0];
int dy = y + walk[i][1];
if(dx >= n || dx < 0 || dy >= m || dy < 0) continue;
if(grid[x][y] >= grid[dx][dy]) continue;
if(dp[dx][dy]) {
s += dp[dx][dy] + 1; continue; }
s += dfs(dx, dy, grid, dp) + 1;
s %= mod;
}
dp[x][y] = (s + dp[x][y]) % mod;
return dp[x][y];
}
int countPaths(vector<vector<int>>& grid) {
n = grid.size(), m = grid[0].size();
vector<vector<int>> dp(n, vector<int>(m, 0));
for (int i = 0; i < n; i++) {
for (int j = 0; j < m; j++) {
if(!dp[i][j]) {
dfs(i, j, grid, dp);
}
}
}
int res = 0;
for (int i = 0; i < n; i++)
for (int j = 0; j < m; j++)
res = (res + dp[i][j] + 1) % mod;
return res;
}
};
边栏推荐
- Virtual machine VirtualBox and vagrant installation
- 随着MapReduce job实现去加重,多种输出文件夹
- bonecp使用数据源
- 用友OA漏洞学习——NCFindWeb 目录遍历漏洞
- 【LeetCode第 300 场周赛】
- Take you through ancient Rome, the meta universe bus is coming # Invisible Cities
- std::true_type和std::false_type
- C language exchanges two numbers through pointers
- Cocos2d Lua 越来越小样本 内存游戏
- Stealing others' vulnerability reports and selling them into sidelines, and the vulnerability reward platform gives rise to "insiders"
猜你喜欢

J'aimerais dire quelques mots de plus sur ce problème de communication...
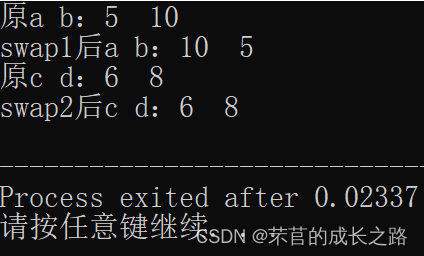
C language exchanges two numbers through pointers

44所高校入选!分布式智能计算项目名单公示
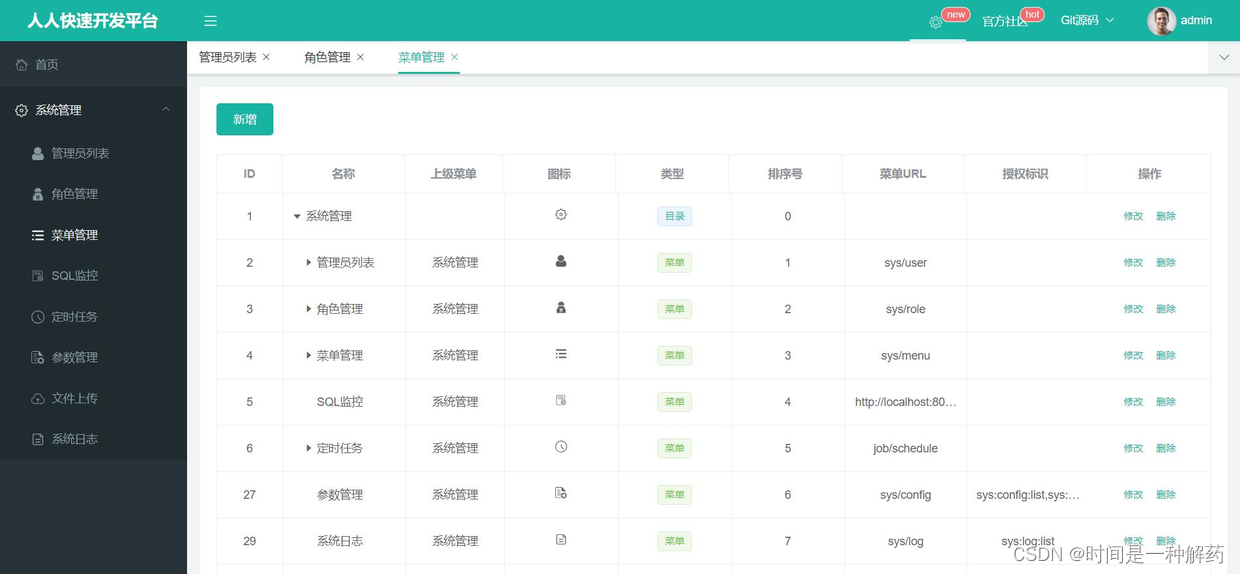
Recommend easy-to-use backstage management scaffolding, everyone open source
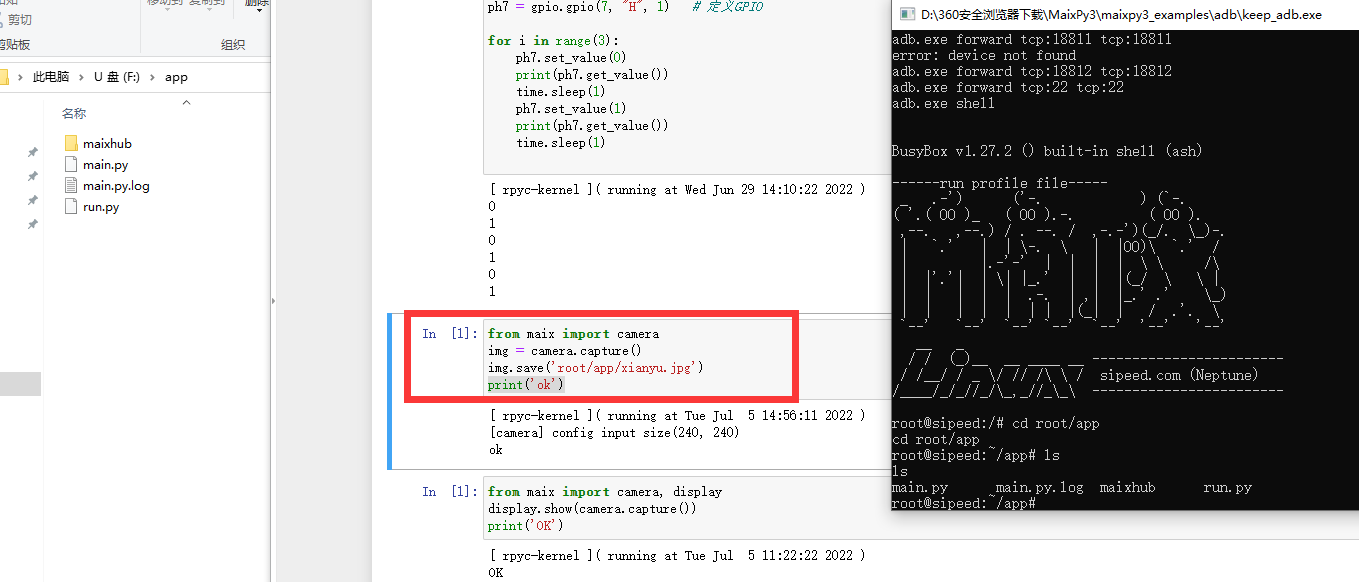
Maixll-Dock 摄像头使用

小程序在产业互联网中的作用
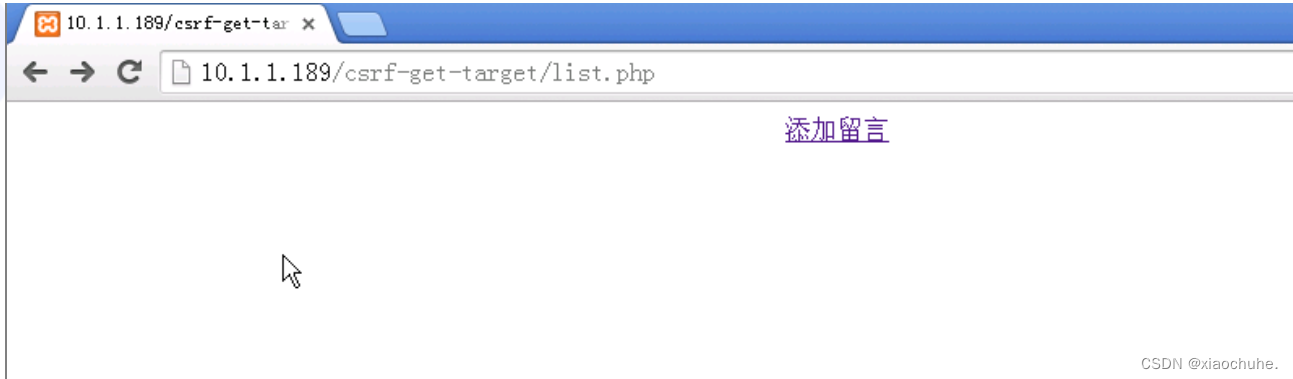
CSRF漏洞分析
Kivy tutorial: support Chinese in Kivy to build cross platform applications (tutorial includes source code)
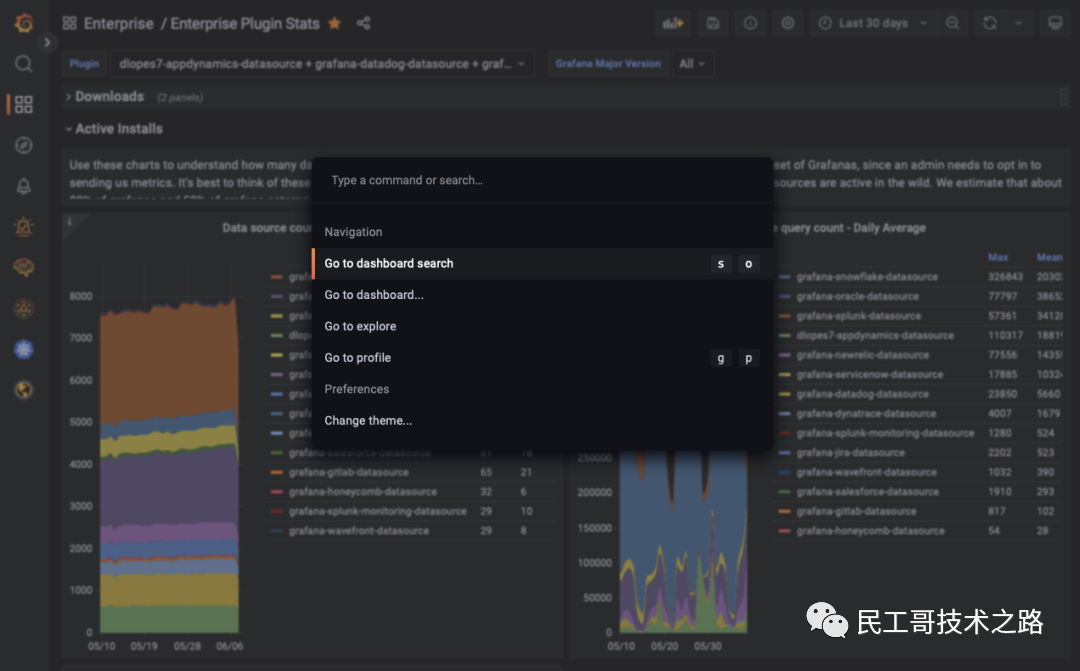
Grafana 9.0 正式发布!堪称最强!
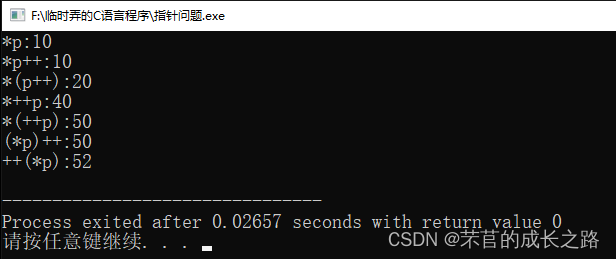
Comparative examples of C language pointers *p++, * (p++), * ++p, * (++p), (*p) + +, +(*p)
随机推荐
重磅硬核 | 一文聊透对象在 JVM 中的内存布局,以及内存对齐和压缩指针的原理及应用
【.NET CORE】 请求长度过长报错解决方案
Reprint: defect detection technology of industrial components based on deep learning
关于这次通信故障,我想多说几句…
Coco2017 dataset usage (brief introduction)
STM32+MFRC522完成IC卡号读取、密码修改、数据读写
Compilation principle - top-down analysis and recursive descent analysis construction (notes)
Interview shock 62: what are the precautions for group by?
Open source and safe "song of ice and fire"
Scratch epidemic isolation and nucleic acid detection Analog Electronics Society graphical programming scratch grade examination level 3 true questions and answers analysis June 2022
Jerry's watch reads the file through the file name [chapter]
Excel usage record
重磅硬核 | 一文聊透对象在 JVM 中的内存布局,以及内存对齐和压缩指针的原理及应用
随着MapReduce job实现去加重,多种输出文件夹
解读云原生技术
POJ 2208 已知边四面体六个长度,计算体积
高精度运算
Declval (example of return value of guidance function)
Four processes of program operation
CSRF漏洞分析