当前位置:网站首页>When to use pointers in go?
When to use pointers in go?
2022-07-04 12:40:00 【Red hat spongebob】
1 Using pointers in methods
What is? receiver?
func (t T) method_name(t T){
}
Inside T Namely receiver
- Use receiver As a method parameter
func main() {
r := receiver{
Name: "zs"}
fmt.Println(r)
r.methodA()
fmt.Println(r)
}
type receiver struct {
Id int
Name string
Age int
}
func (receiver receiver) methodA() {
receiver.Name = "ls"
}
func (receiver *receiver) methodB() {
receiver.Name = "ls"
}
result :
{0 zs 0}
{0 zs 0}
- Use *receiver As a method parameter
func main() {
r := receiver{
Name: "zs"}
fmt.Println(r)
r.methodB()
fmt.Println(r)
}
type receiver struct {
Id int
Name string
Age int
}
func (receiver receiver) methodA() {
receiver.Name = "ls"
}
func (receiver *receiver) methodB() {
receiver.Name = "ls"
}
result :
{0 zs 0}
{0 ls 0}
2 Use pointers in structures
- Mode one
func main() {
student := Student{
Map: map[string]int{
"S": 0}, ReceiverA: receiver{
Name: "A"}, ReceiverB: &receiver{
Name: "B"}}
fmt.Println(student, *student.ReceiverB)
student.updateA()
fmt.Println(student, *student.ReceiverB)
}
type receiver struct {
Id int
Name string
Age int
}
type Student struct {
No int
Map map[string]int
ReceiverA receiver
ReceiverB *receiver
}
func (stu Student) updateA() {
stu.Map["a"] = 1
stu.ReceiverA = receiver{
Name: "ww"}
stu.ReceiverB = &receiver{
Name: "ww"}
}
func (stu *Student) updateB() {
stu.Map["b"] = 2
stu.ReceiverA = receiver{
Name: "ww"}
stu.ReceiverB = &receiver{
Name: "ww"}
}
result :
{0 map[S:0] {0 A 0} 0xc0000b4000} {0 B 0}
{0 map[S:0 a:1] {0 A 0} 0xc0000b4000} {0 B 0}
- Mode two
func main() {
student := Student{
Map: map[string]int{
"S": 0}, ReceiverA: receiver{
Name: "A"}, ReceiverB: &receiver{
Name: "B"}}
fmt.Println(student, *student.ReceiverB)
student.updateA()
fmt.Println(student, *student.ReceiverB)
}
type receiver struct {
Id int
Name string
Age int
}
type Student struct {
No int
Map map[string]int
ReceiverA receiver
ReceiverB *receiver
}
func (stu Student) updateA() {
stu.Map["a"] = 1
stu.ReceiverA = receiver{
Name: "ww"}
stu.ReceiverB = &receiver{
Name: "ww"}
}
func (stu *Student) updateB() {
stu.Map["b"] = 2
stu.ReceiverA = receiver{
Name: "ww"}
stu.ReceiverB = &receiver{
Name: "ww"}
}
result :
{0 map[S:0] {0 A 0} 0xc0000b4000} {0 B 0}
{0 map[S:0 b:2] {0 ww 0} 0xc0000b4060} {0 ww 0}
3 When to use the pointer
When should a function be done with pointer type receiver It has always been a headache for beginners . Here are some common judgment guides .
- If receiver yes
map、funcperhapschan, Don't use the pointer - If receiver yes
sliceAnd this function does not modify this slice, Don't use the pointer - If this function will be modified receiver, At this point, be sure to use the pointer
- If receiver yes
structAnd contains mutually exclusive typessync.Mutex, Or similar synchronous variables ,receiver It has to be a pointer , This avoids copying objects - If receiver It's bigger
structperhapsarray, Using pointers is more efficient . How old is big ? hypothesis struct All members of the function must be passed in as function variables , If you think there are too many data at this time , Namely struct Too big - If receiver yes
struct,arrayperhapsslice, And one of them element Points to a variable , At this time receiver Selecting pointers makes the intent of the code more obvious - If receiver Make smaller
structperhapsarray, And its variables are invariants 、 Constant , for exampletime.Time,value receiver More suitable , because value receiver It can reduce the amount of garbage that needs to be recycled . - Last , If you are not sure which one to use , Using pointer class receiver
Reference article :
https://zhuanlan.zhihu.com/p/395747448
边栏推荐
- Global and Chinese market of cardiac monitoring 2022-2028: Research Report on technology, participants, trends, market size and share
- C language function
- Detailed explanation of NPM installation and caching mechanism
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 21
- Recommend a cool geospatial data visualization tool with low code
- R语言--readr包读写数据
- Kivy教程之 08 倒计时App实现timer调用(教程含源码)
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 23
- [Chongqing Guangdong education] National Open University spring 2019 2727 tax basis reference questions
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 11
猜你喜欢
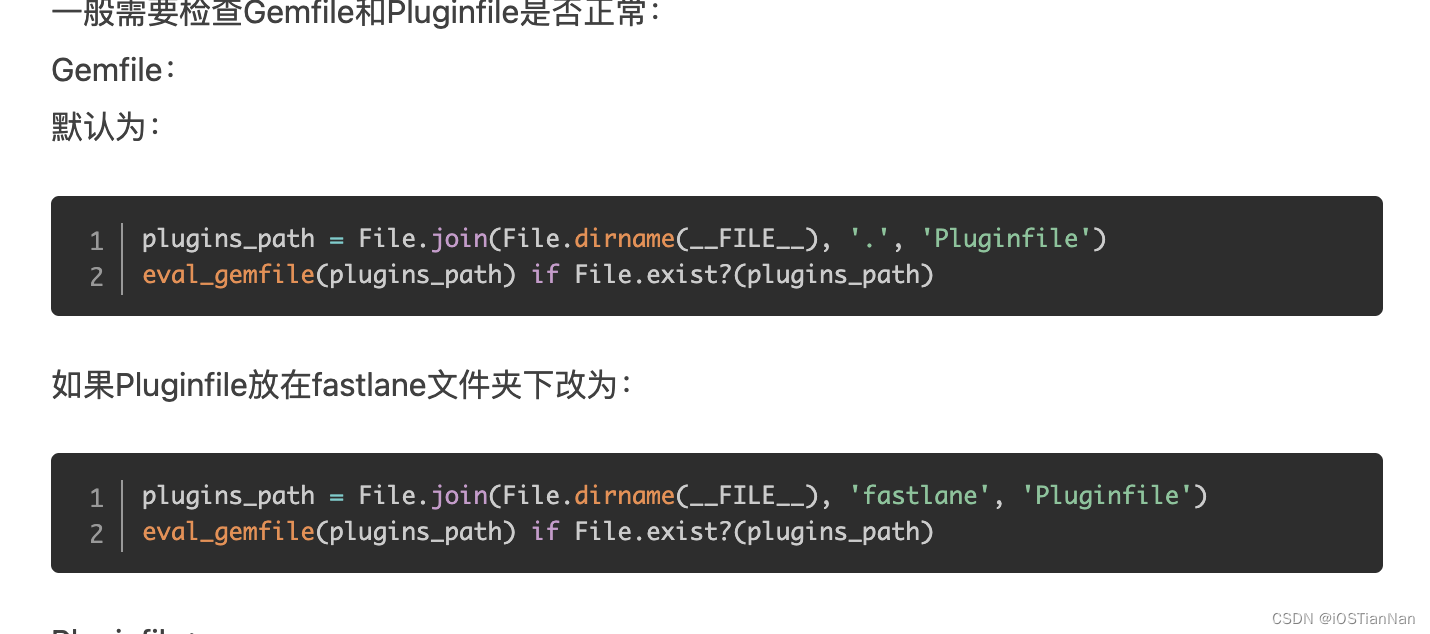
Fastlane one click package / release app - usage record and stepping on pit
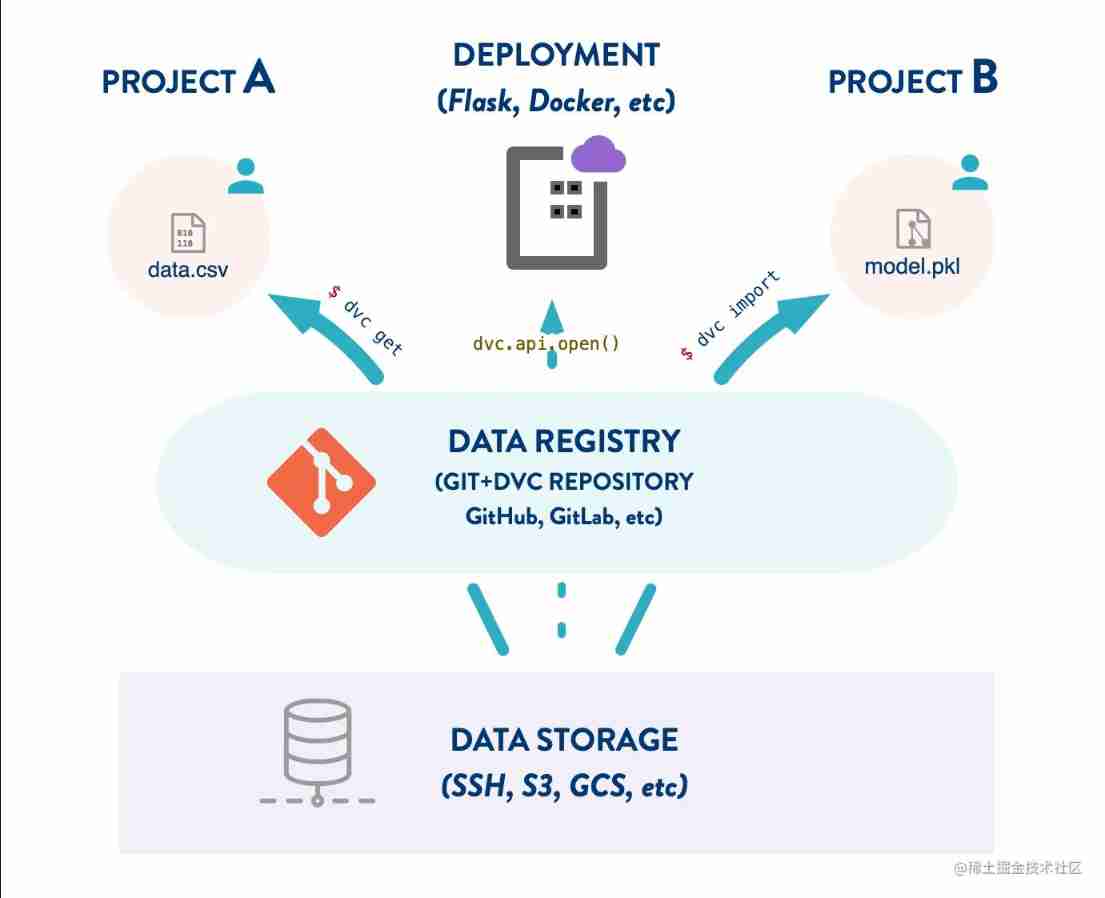
DVC use case (VI): Data Registry
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 16](/img/c3/f3746b161012acc3751b2bd0b8f663.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 16

What if the chat record is gone? How to restore wechat chat records on Apple Mobile
JD home programmers delete databases and run away. Talk about binlog, the killer of MySQL data backup
《天天数学》连载57:二月二十六日
![Cadence physical library lef file syntax learning [continuous update]](/img/d5/0671935b074e538a2147dbe51a5a70.jpg)
Cadence physical library lef file syntax learning [continuous update]
![[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 9](/img/ed/0edff23fbd3880bc6c9dabd31755ac.jpg)
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 9
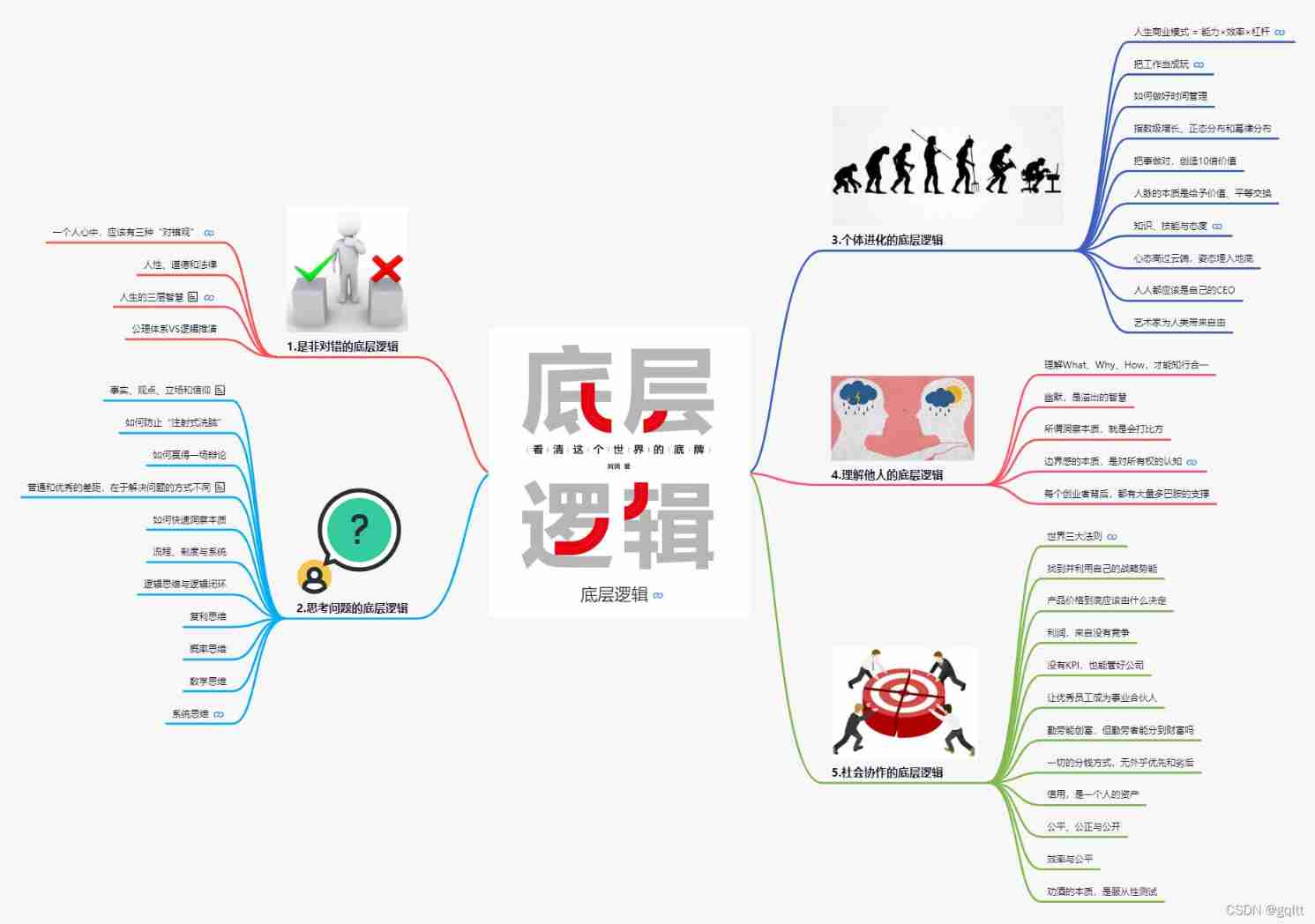
Bottom Logic -- Mind Map
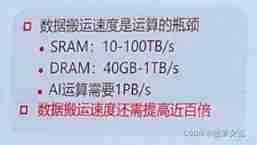
Memory computing integration: AI chip architecture in the post Moorish Era
随机推荐
How to realize the function of Sub Ledger of applet?
Map container
[ES6] template string: `string`, a new symbol in es2015
Netgear switch basic configuration command set
Entity framework calls Max on null on records - Entity Framework calling Max on null on records
13、 C window form technology and basic controls (3)
Anti clockwise rotation method of event arrangement -- PHP implementation
Hongke case study on storm impact in coastal areas of North Carolina using lidar
When synchronized encounters this thing, there is a big hole, pay attention!
Possible to restore a backup of SQL Server 2014 on SQL Server 2012?
Xshell's ssh server rejected the password, failed to skip publickey authentication, and did not register with the server
VIM, another program may be editing the same file If this is the solution of the case
17. Memory partition and paging
The detailed installation process of Ninja security penetration system (Ninjitsu OS V3). Both old and new VM versions can be installed through personal testing, with download sources
Here, the DDS tutorial you want | first experience of fastdds - source code compilation & Installation & Testing
[Yu Yue education] 233 pre school children's language education reference questions in the spring of 2019 of the National Open University
[notes] streamingassets
Googgle guava ImmutableCollections
Method of setting default items in C # ComboBox control code
How to use "bottom logic" to see the cards in the world?