当前位置:网站首页>Redis cache breakdown, cache penetration, cache avalanche
Redis cache breakdown, cache penetration, cache avalanche
2022-07-06 03:07:00 【Attacking Xiao Wang 666】
Cache penetration
a large number of key Not in cache , The request goes directly to the database , and key It's not in the database ( Finally back to null, A meaningless query ), If hackers create such a large number of request attacks , Cache penetration may occur
Solution :
1. You can verify at the front end or back end , Filter illegal requests , For example, judge whether the request has been tampered by the summary Algorithm
2. Invalid cache key, Set a shorter effective time ( Not recommended )
3. The bloon filter , A very clever data structure , The concrete realization is :
Store all possible request values in the bloom filter , When requested by the user , First, judge whether the value exists through the bloom filter , If no error message is returned directly .
The process is as follows
When stored , Through multiple hash Function calculation , Then set the corresponding position of the bit array to 1
When comparing , The use of multiple hash The algorithm calculates the request parameters , Judge whether each element at the corresponding position in the digit group is 1, If there is any inconformity, it will be judged as fasle
Of course , Different strings may be hashed out in the same position ( You can appropriately increase the size of the digit group or adjust hash function )
Cache avalanche
It is caused by memory server downtime or simultaneous failure of a large number of hotspot caches at the same time , The request landed in the database
Solution :
1. For server downtime , It can be distributed ( Master-slave ) To improve usability , Or current limiting , Prevent a large number of requests for access at the same time
2. For hotspot cache invalidation , It can be set to never expire ( Not recommended ), Or set the expiration time randomly ( Peak staggering failure )
Cache breakdown
Cache avalanche is aimed at the situation that a large number of caches for different requests are invalidated , Cache breakdown refers to the situation that a large number of requests are the same and the cache fails
Solution :
Hotspot cache does not expire
Use mutexes , Only one request thread can reload the results into the cache after the cache expires , Other threads wait , Finally, query from the cache .
边栏推荐
- Microservice registration and discovery
- C # create self host webservice
- Pat 1046 shortest distance (20 points) simulation
- NR modulation 1
- Rust language -- iterators and closures
- Custom attribute access__ getattribute__/ Settings__ setattr__/ Delete__ delattr__ method
- Single instance mode of encapsulating PDO with PHP in spare time
- Introduction to robotframework (II) app startup of appui automation
- js 正则过滤和增加富文本中图片前缀
- Who is the winner of PTA
猜你喜欢
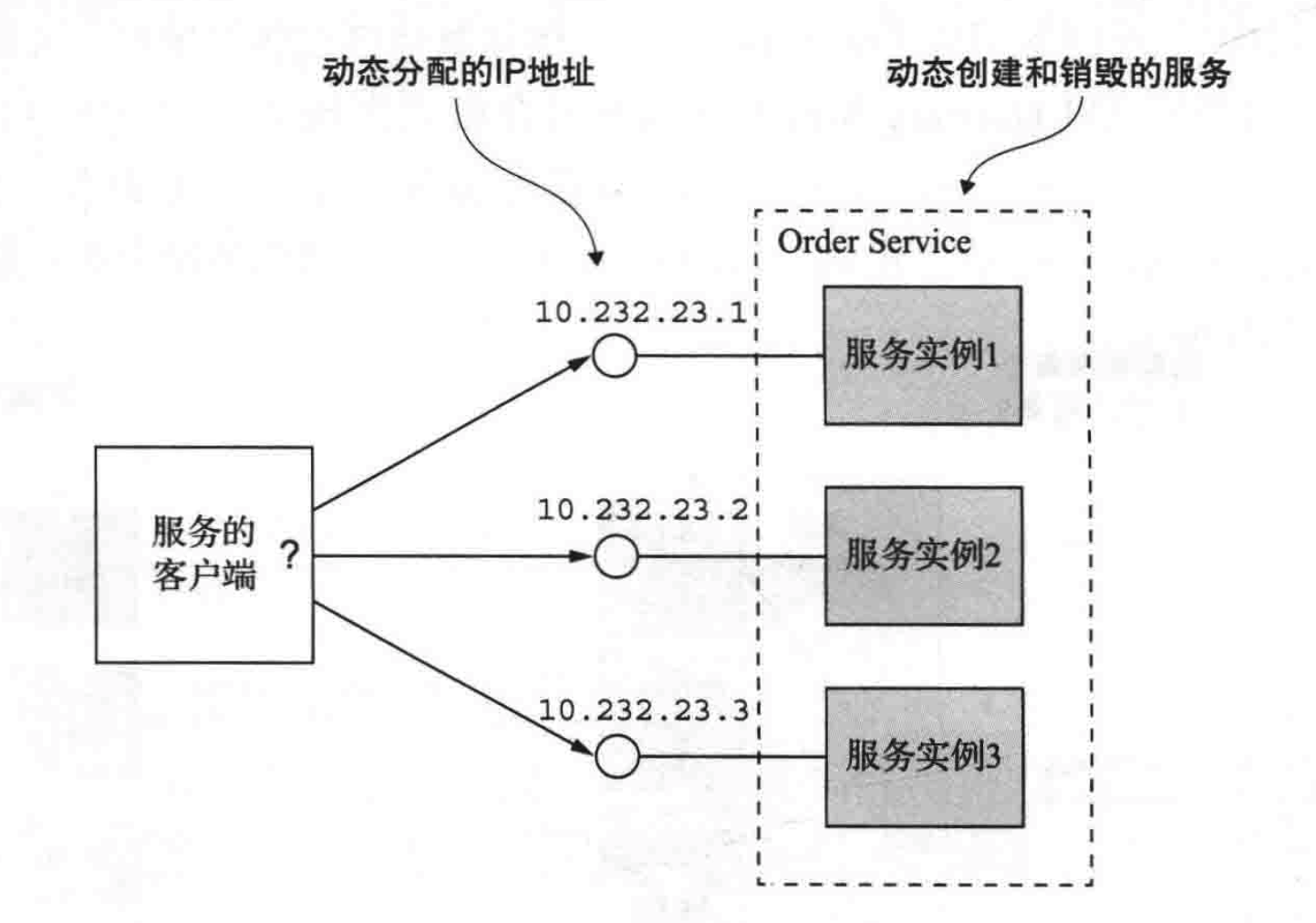
Microservice registration and discovery
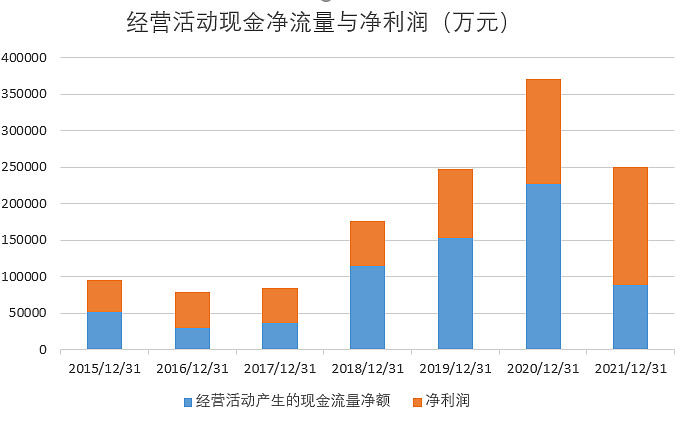
What is the investment value of iFLYTEK, which does not make money?
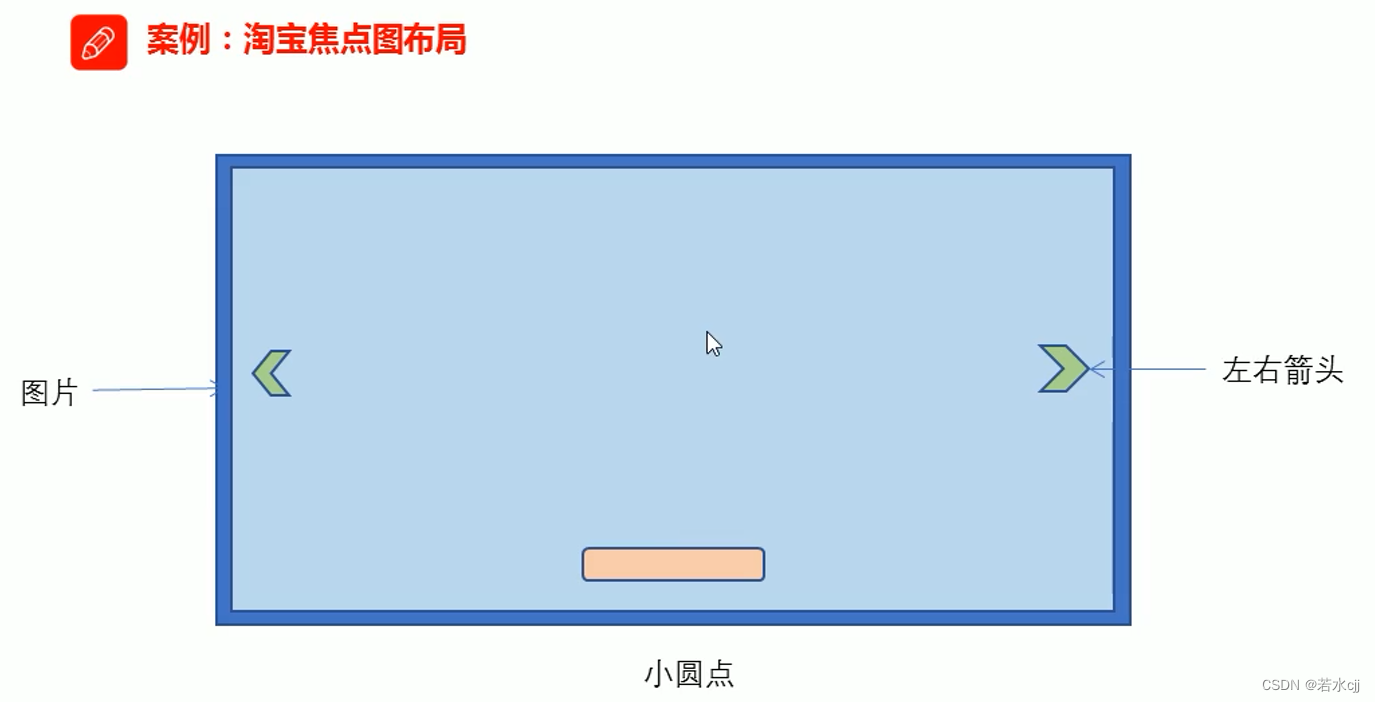
淘宝焦点图布局实战
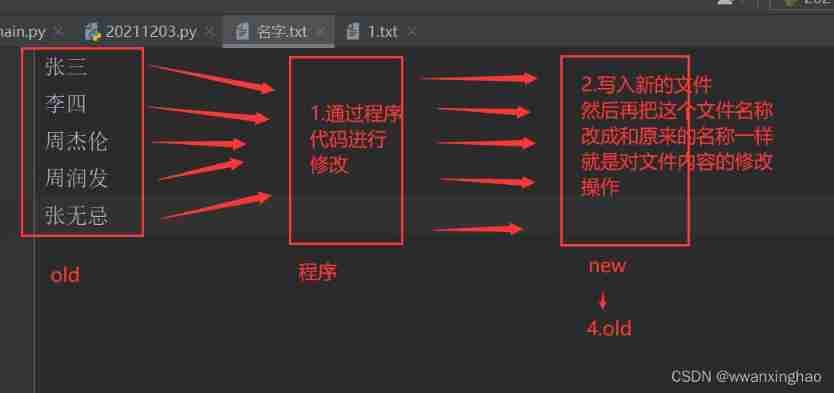
4. File modification
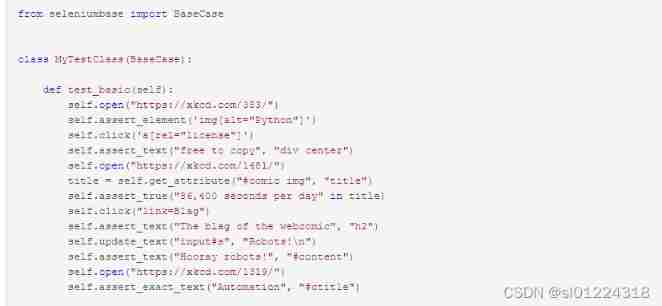
Selenium share
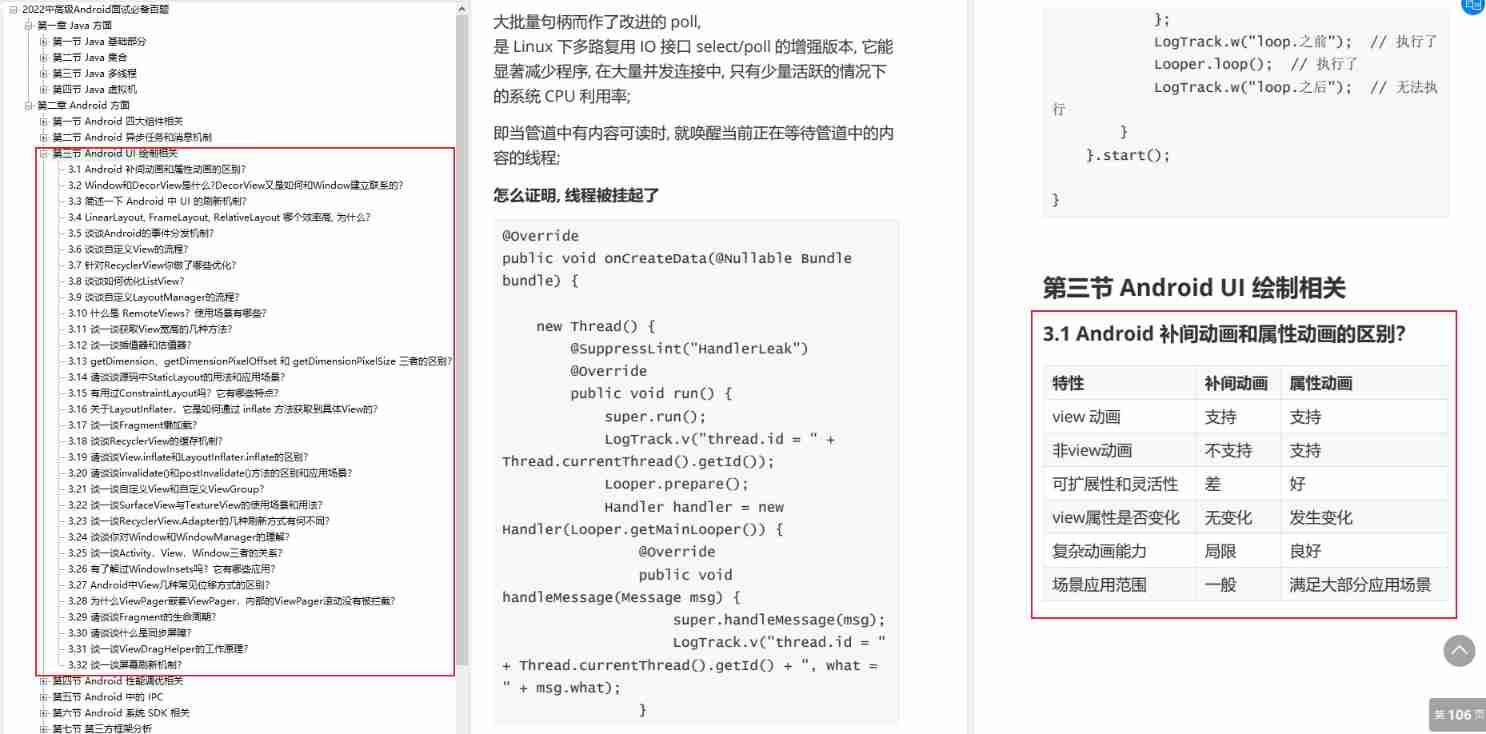
I sorted out a classic interview question for my job hopping friends
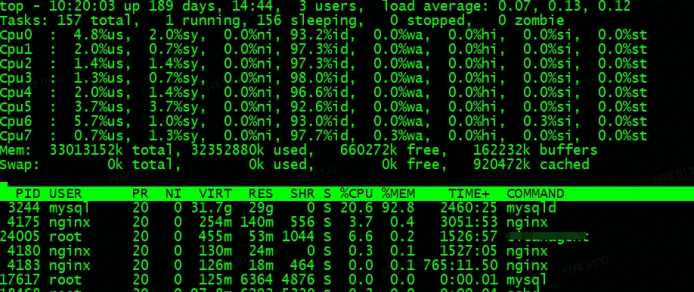
Fault analysis | analysis of an example of MySQL running out of host memory
![[concept] Web basic concept cognition](/img/27/14bcd73ca70d136436a4382a1b4bd1.jpg)
[concept] Web basic concept cognition
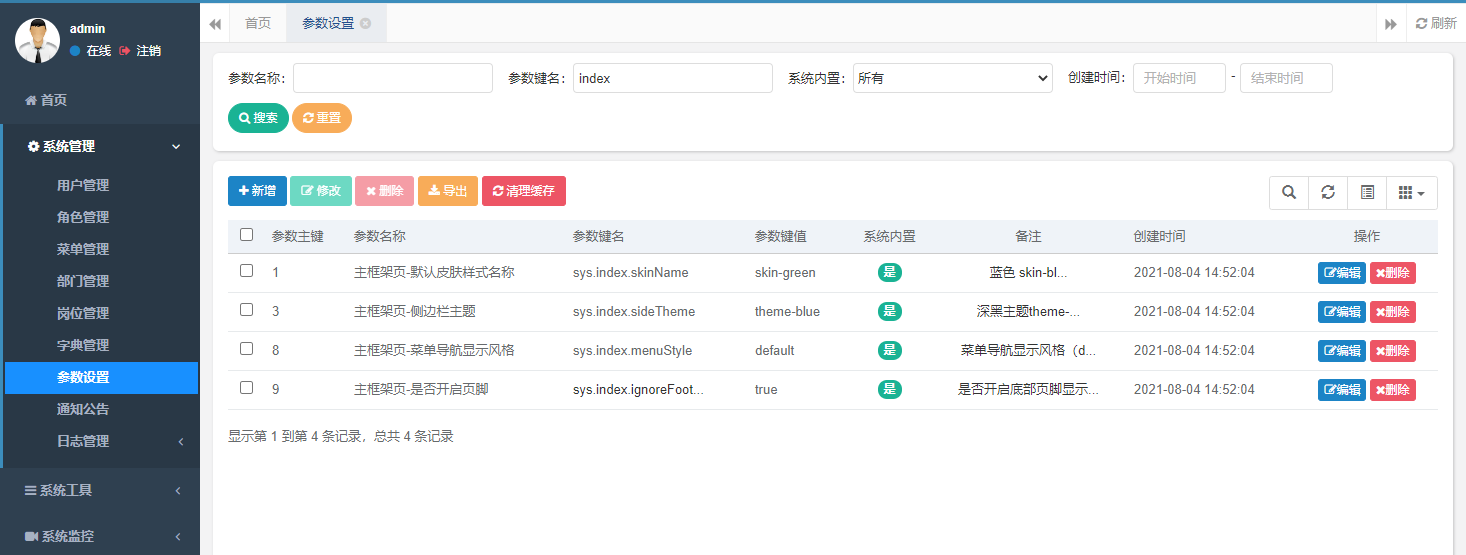
【若依(ruoyi)】设置主题样式
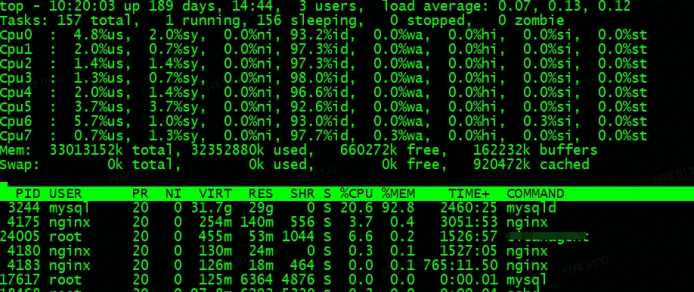
故障分析 | MySQL 耗尽主机内存一例分析
随机推荐
Microservice registration and discovery
Problems encountered in 2022 work IV
MySQL advanced notes
解决:AttributeError: ‘str‘ object has no attribute ‘decode‘
Day 50 - install vsftpd on ceontos6.8
Game theory matlab
Misc (eternal night), the preliminary competition of the innovation practice competition of the National College Students' information security competition
故障分析 | MySQL 耗尽主机内存一例分析
【paddle】加载模型权重后预测报错AttributeError: ‘Model‘ object has no attribute ‘_place‘
Linear regression and logistic regression
Technology sharing | what if Undo is too big
CSP numeric sort
Installation and use tutorial of cobaltstrike-4.4-k8 modified version
Apt installation ZABBIX
【 kubernets series】 a Literature Study on the Safe exposure Applications of kubernets Service
3857墨卡托坐标系转换为4326 (WGS84)经纬度坐标
全国大学生信息安全赛创新实践赛初赛---misc(永恒的夜)
继承day01
My C language learning record (blue bridge) -- on the pointer
适合程序员学习的国外网站推荐