当前位置:网站首页>Buuctf question brushing notes - [geek challenge 2019] easysql 1
Buuctf question brushing notes - [geek challenge 2019] easysql 1
2022-07-06 03:03:00 【Always a teenager】
Continue today BUUCTF The topic , Today's solution [ Geek challenge 2019]EasySQL 1.
One 、 Basic information of the topic
Let's go to the link , Open the web site , The results are shown below :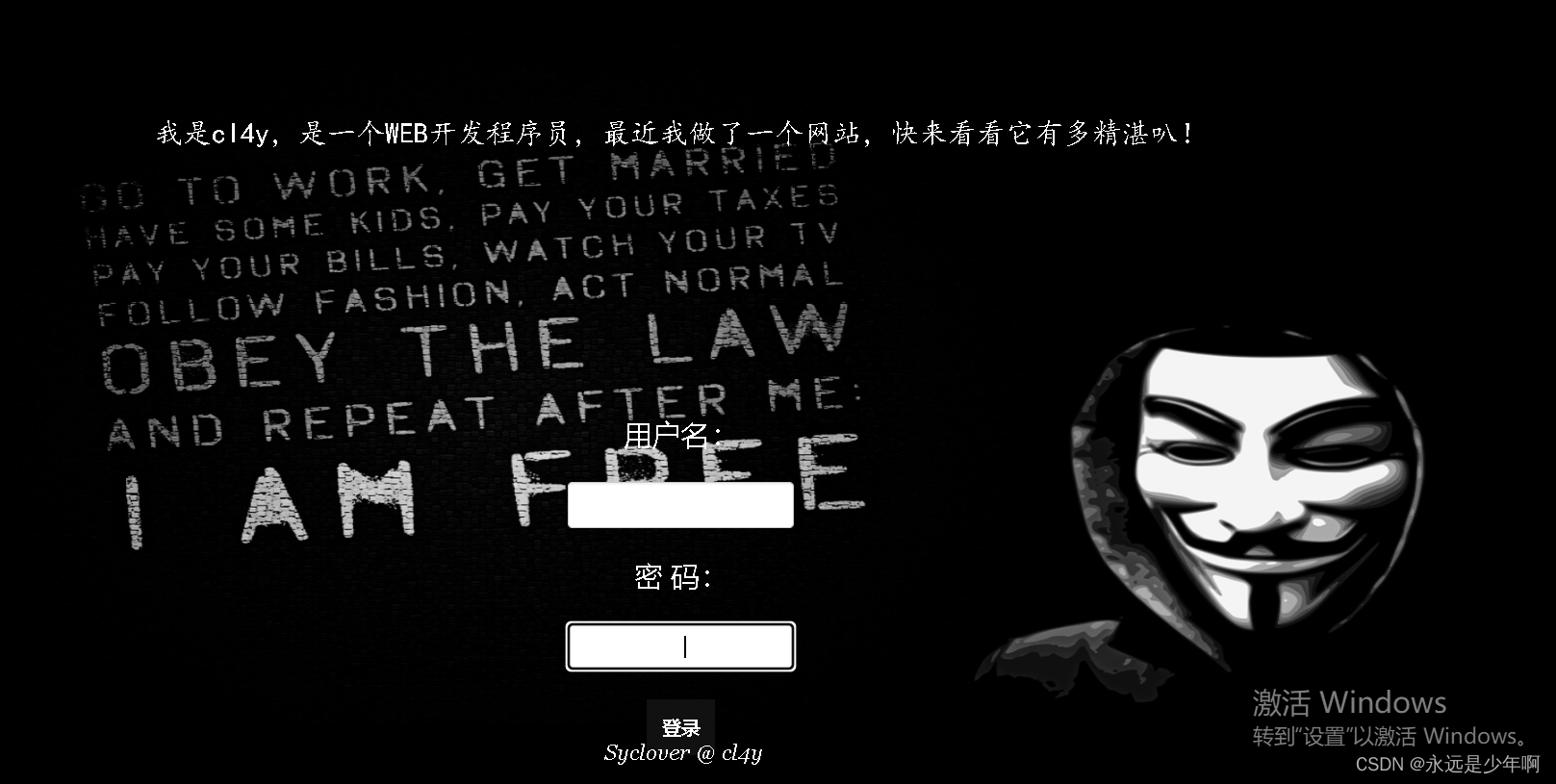
Two 、 Their thinking
As can be seen from the above figure , Our target site is a login page . Combined with the topic information , We can guess that the problem is solved as SQL Injection direction .
We simply try the user name with single quotation marks at the user name admin’, The results are shown below :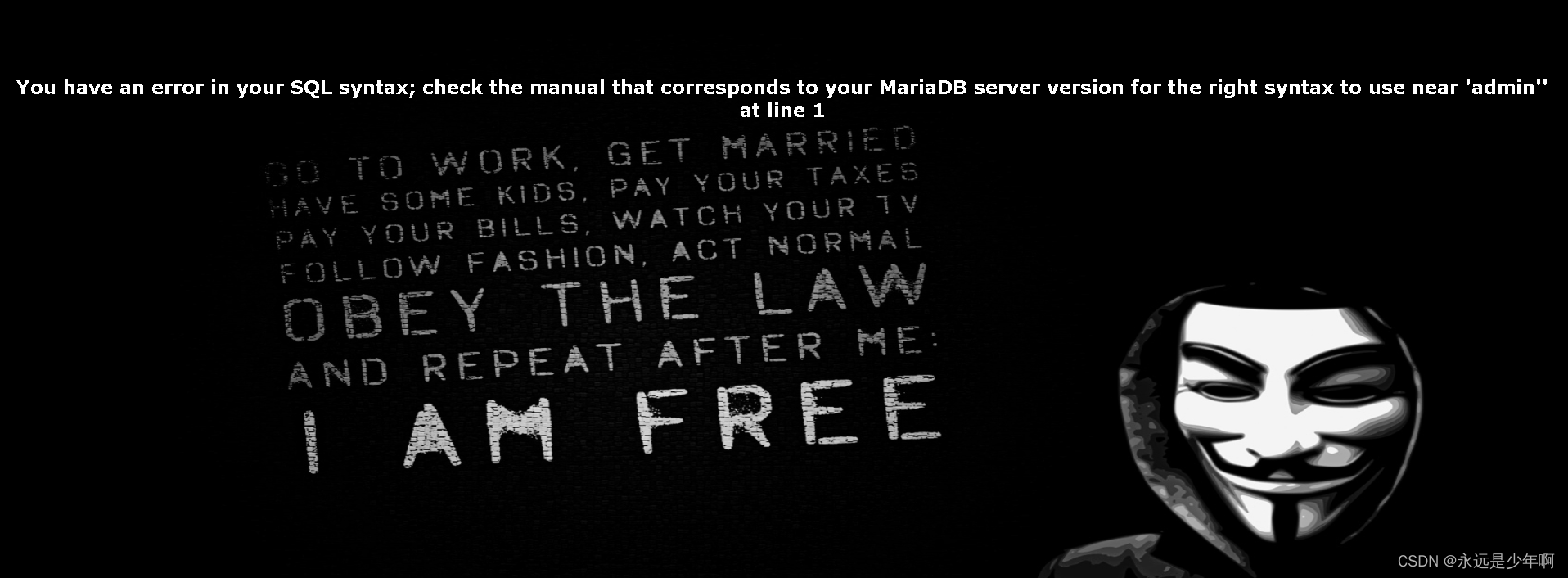
As can be seen from the above figure , This is a simple error report SQL Inject .
Next , We try to add a after the user name just now #, Try to filter the following content , The results are shown below :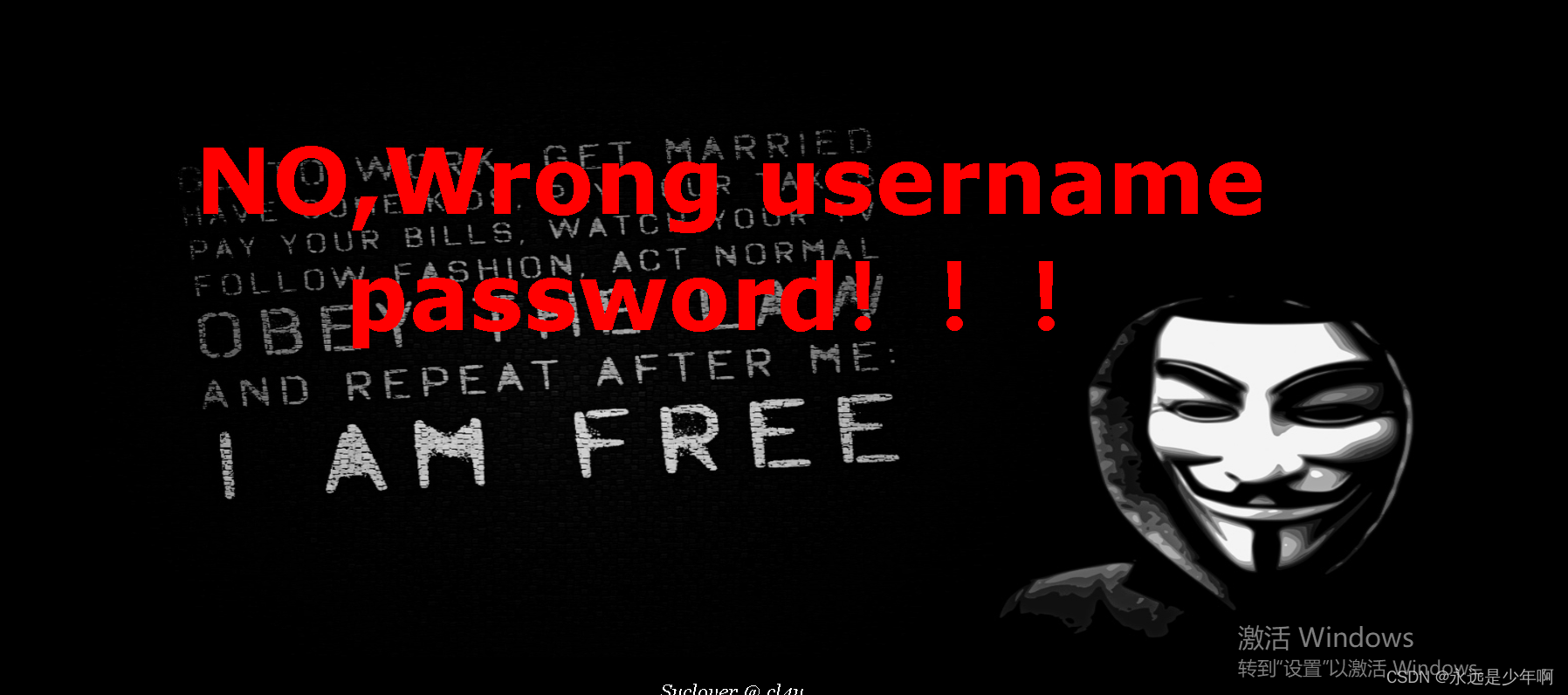
3、 ... and 、 Get flag
It is easy to analyze from the above attempts , The topic is very simple , Basically no filtering , We try to use universal password , user name admin’ or 1=1#, Password optional , Click to log in , The results are shown below :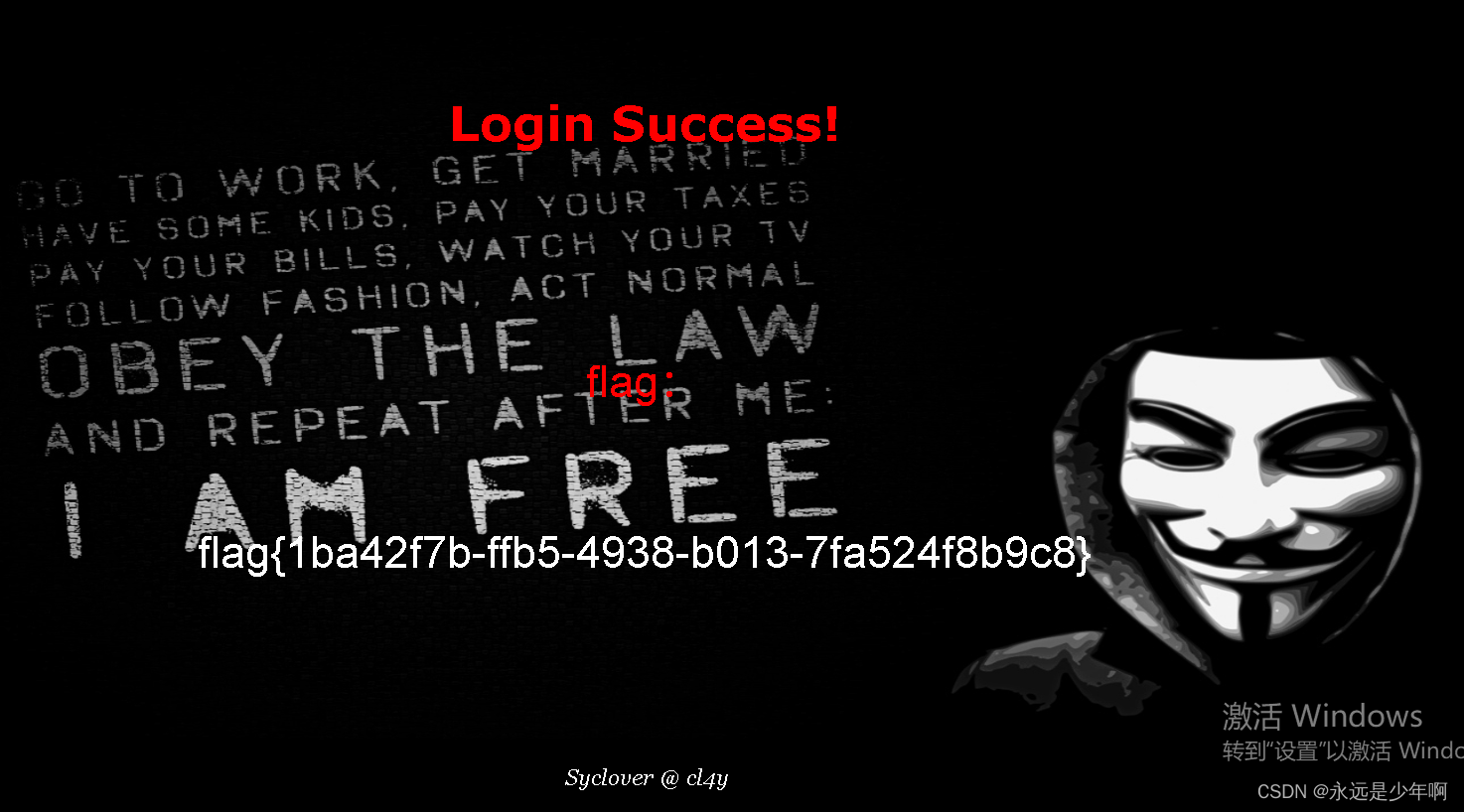
As can be seen from the above figure , We successfully got the title flag.
Originality is not easy. , Reprint please explain the source :https://blog.csdn.net/weixin_40228200
边栏推荐
- Redis SDS principle
- Microservice registration and discovery
- 2.11 simulation summary
- Introduction to robotframework (I) brief introduction and use
- PMP practice once a day | don't get lost in the exam -7.5
- Redis skip table
- Pure QT version of Chinese chess: realize two-man, man-machine and network games
- 故障分析 | MySQL 耗尽主机内存一例分析
- Apt installation ZABBIX
- Master data management theory and Practice
猜你喜欢
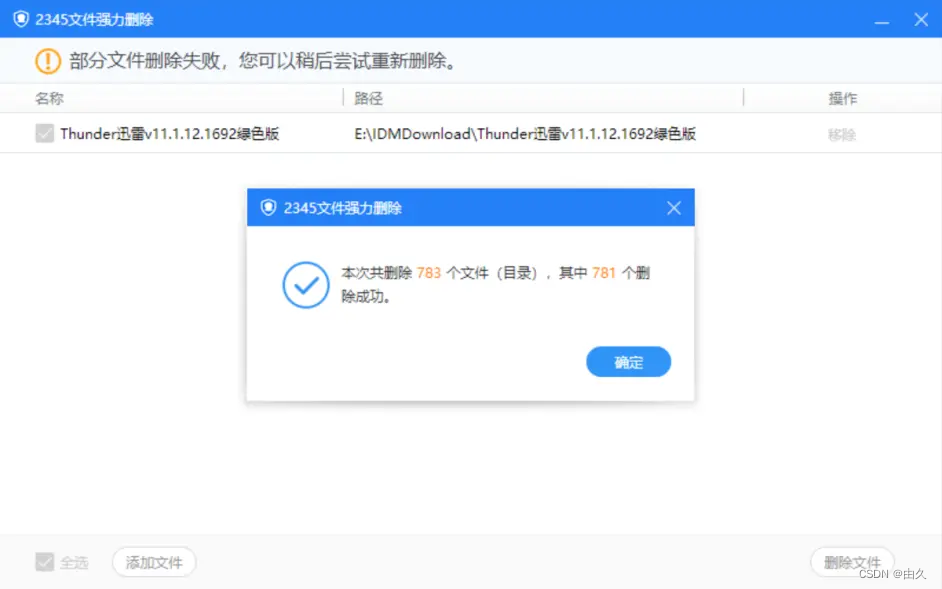
2345 file shredding, powerful file deletion tool, unbound pure extract version
![BUUCTF刷题笔记——[极客大挑战 2019]EasySQL 1](/img/37/c38a933ce7fa5d2b8fa597965ffcb2.png)
BUUCTF刷题笔记——[极客大挑战 2019]EasySQL 1
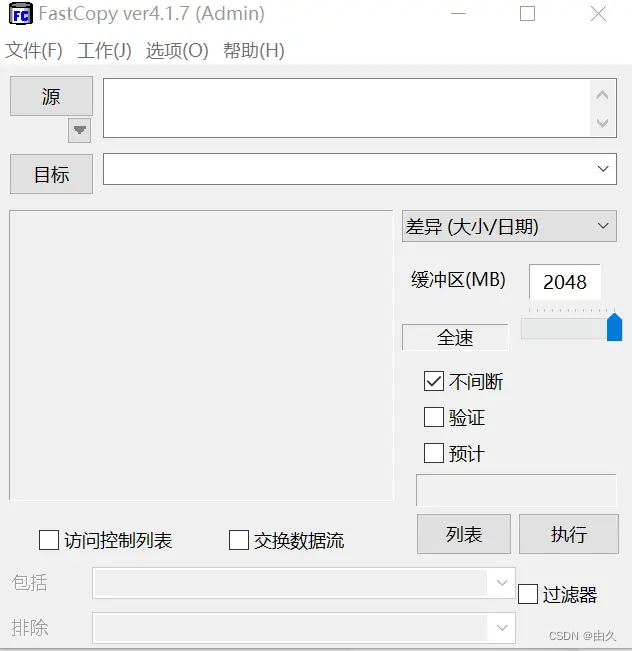
一个复制也能玩出花来
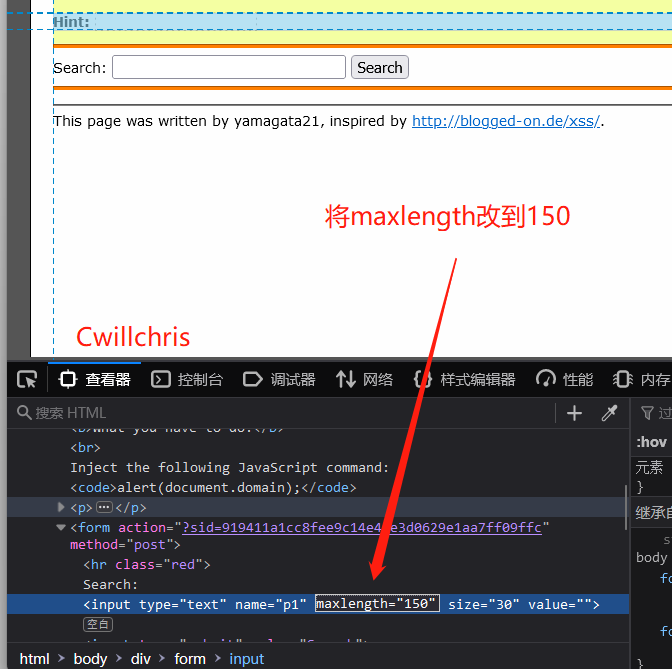
XSS challenges bypass the protection strategy for XSS injection
![[network security interview question] - how to penetrate the test file directory through](/img/48/be645442c8ff4cc5417c115963b217.jpg)
[network security interview question] - how to penetrate the test file directory through
![[matlab] access of variables and files](/img/cf/6f3cfdc4310fcf0bdcaa776d68261e.jpg)
[matlab] access of variables and files
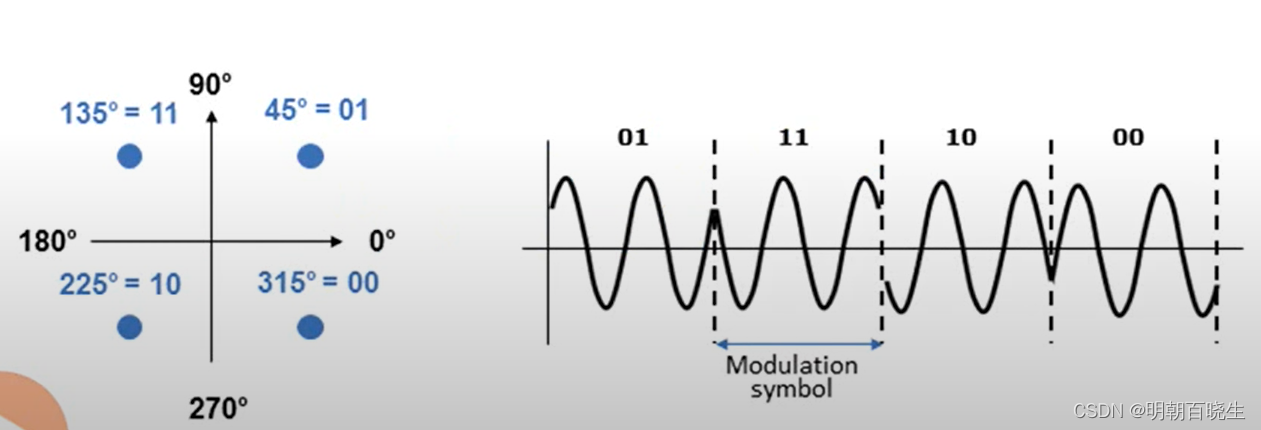
NR modulation 1
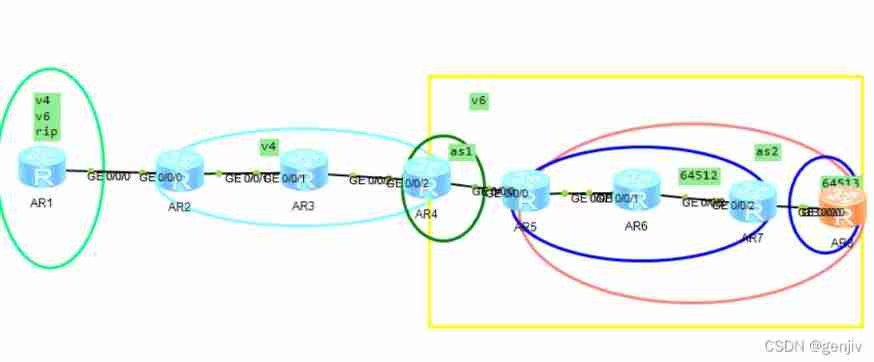
IPv6 jobs
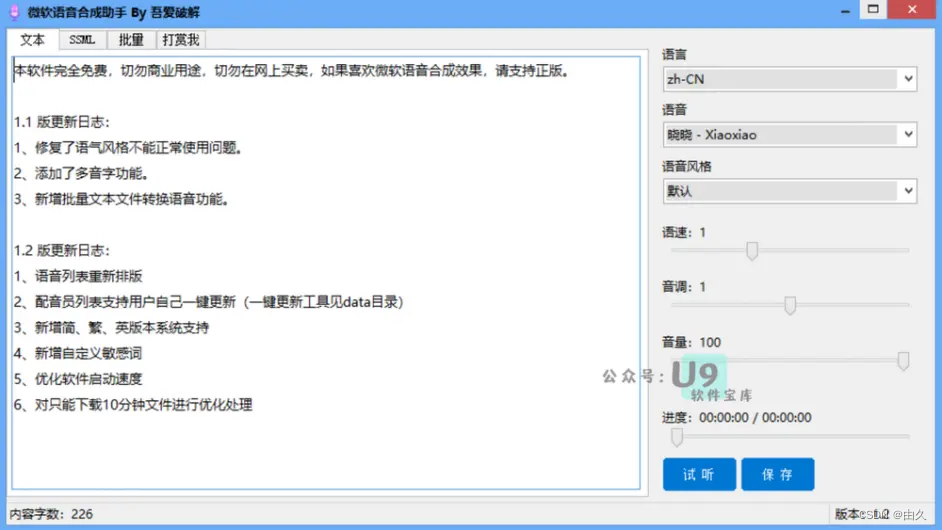
微软语音合成助手 v1.3 文本转语音工具,真实语音AI生成器

全国大学生信息安全赛创新实践赛初赛---misc(永恒的夜)
随机推荐
Introduction to robotframework (III) Baidu search of webui automation
Communication between microservices
Apt installation ZABBIX
Self made CA certificate and SSL certificate using OpenSSL
张丽俊:穿透不确定性要靠四个“不变”
Detailed use of dbutils # yyds dry goods inventory #
MySQL advanced notes
C language - Blue Bridge Cup - promised score
微软语音合成助手 v1.3 文本转语音工具,真实语音AI生成器
[pointer training - eight questions]
#PAT#day10
【概念】Web 基础概念认知
[Chongqing Guangdong education] higher mathematics I reference materials of Southwest Petroleum University
全国大学生信息安全赛创新实践赛初赛---misc(永恒的夜)
"Hands on learning in depth" Chapter 2 - preparatory knowledge_ 2.5 automatic differentiation_ Learning thinking and exercise answers
How to read excel, PDF and JSON files in R language?
JS regular filtering and adding image prefixes in rich text
DDoS attacks - are we really at war?
不赚钱的科大讯飞,投资价值该怎么看?
有没有完全自主的国产化数据库技术