当前位置:网站首页>Demonstration of using Solon auth authentication framework (simpler authentication framework)
Demonstration of using Solon auth authentication framework (simpler authentication framework)
2022-07-05 05:19:00 【Lin Xidong】
I've seen several authentication frameworks recently , what Appache Shiro La 、Sa-Token La 、Spring Security La ... In especial Spring Security, As a benchmark Spring Boot & Cloud Framework Solon What's more, we should have our own biological safety certification framework . So in the adaptation Sa-Token(satoken-solon-plugin) and sureness(sureness-solon-plugin) after , Also developed Solon My son :Solon Auth (solon.auth). The goal is to be simpler 、 More direct , At the same time, it provides users with richer and different authentication framework options .
Solon Auth (solon.auth)
Solon Auth The location is , Only do authentication control . Focus on the adaptation of validation results , And the unified control and application based on it . Less functionality , But it doesn't get dizzy .
Solon Auth Support rule control and annotation control , Each has its own advantages and disadvantages , It can also be used in combination :
- Rule control , It is suitable for the overall macro control in one place
- Annotation control , Easy to grasp in detail
One 、 Start to adapt , complete 2 Step by step
- The first 1 Step , Build an authentication adapter
@Configurationpublic class Config { @Bean public AuthAdapter init() { // // Build the adapter // return new AuthAdapter() .loginUrl("/login") // Set the login address , Jump automatically when not logged in ( If you don't set , The output 401 error ) .addRule(r -> r.include("**").verifyIp().failure((c, t) -> c.output(" Yours IP Not on the white list "))) // Add rules .addRule(b -> b.exclude("/login**").exclude("/run/**").verifyPath()) // Add rules .processor(new AuthProcessorImpl()) // Set authentication processor .failure((ctx, rst) -> { // Set the default validation failure handling ctx.render(rst); }); }}// Rule configuration description //1.include(path) The path scope of the rule package function , Can be more //2.exclude(path) The path pool of rule sort , Can be more //3.failure(..) The treatment after the rule is lost //4.verifyIp()... The verification scheme to be done by the rule ( There are many different verification schemes )- The first 2 Step , Implement an authentication processor
So let's see AuthProcessor The interface of , It connects a series of verification action results . Maybe users have to do more work themselves , But it's intuitive .
// Authentication processor public class AuthProcessorImpl implements AuthProcessor { @Override public boolean verifyIp(String ip) { // verification IP, Have access to } @Override public boolean verifyLogined() { // Verify login status , Whether the user is logged in } @Override public boolean verifyPath(String path, String method) { // Verify the path , User accessible } @Override public boolean verifyPermissions(String[] permissions, Logical logical) { // Verify specific permissions , Users have limited rights } @Override public boolean verifyRoles(String[] roles, Logical logical) { // Verify specific roles , Whether the user has a role }}Now let's do an adaptive combat , Using a production environment code :
public class GritAuthProcessor implements AuthProcessor { /** * Get the subject Id * */ protected long getSubjectId() { return SessionBase.global().getSubjectId(); } /** * Get the main display name */ protected String getSubjectDisplayName() { return SessionBase.global().getDisplayName(); } @Override public boolean verifyIp(String ip) { // The installation mode , It ignores if (Solon.cfg().isSetupMode()) { return true; } long subjectId = getSubjectId(); if (subjectId > 0) { String subjectDisplayName = getSubjectDisplayName(); Context ctx = Context.current(); if (ctx != null) { //old ctx.attrSet("user_puid", String.valueOf(subjectId)); ctx.attrSet("user_name", subjectDisplayName); //new ctx.attrSet("user_id", String.valueOf(subjectId)); ctx.attrSet("user_display_name", subjectDisplayName); } } // Non whitelist mode , It ignores if (Solon.cfg().isWhiteMode() == false) { return true; } return CloudClient.list().inListOfClientAndServerIp(ip); } @Override public boolean verifyLogined() { // The installation mode , It ignores if (Solon.cfg().isSetupMode()) { return true; } return getSubjectId() > 0; } @Override public boolean verifyPath(String path, String method) { // The installation mode , It ignores if (Solon.cfg().isSetupMode()) { return true; } try { if (GritClient.global().resource().hasResourceByUri(path) == false) { return true; } else { return GritClient.global().auth().hasUri(getSubjectId(), path); } } catch (SQLException e) { throw new GritException(e); } } @Override public boolean verifyPermissions(String[] permissions, Logical logical) { long subjectId = getSubjectId(); try { if (logical == Logical.AND) { boolean isOk = true; for (String p : permissions) { isOk = isOk && GritClient.global().auth().hasPermission(subjectId, p); } return isOk; } else { for (String p : permissions) { if (GritClient.global().auth().hasPermission(subjectId, p)) { return true; } } return false; } } catch (Exception e) { throw new RuntimeException(e); } } @Override public boolean verifyRoles(String[] roles, Logical logical) { long subjectId = getSubjectId(); try { if (logical == Logical.AND) { boolean isOk = true; for (String r : roles) { isOk = isOk && GritClient.global().auth().hasRole(subjectId, r); } return isOk; } else { for (String r : roles) { if (GritClient.global().auth().hasRole(subjectId, r)) { return true; } } return false; } } catch (Exception e) { throw new RuntimeException(e); } }}Two 、2 Applications ( It is generally used in combination )
Just now, we've adapted , Now it's time to apply .
- The first 1 Kind of , stay AuthAdapter Configure all rules directly , Or part of the rules ( Or not )
// Refer to the adapter above addRule(...)The advantage of configuration is , There is no need to hack into the business code ; At the same time, in a unified place , From the macro perspective ; But it's easy to ignore the details .
- The first 2 Kind of , Do a part based on annotations ( General specific permissions or For a specific role )
@Mapping("/rock/agroup")@Controllerpublic class AgroupController { @Mapping("") public void home() { //agroup home page } @Mapping("inner") public void inner() { // Internal list page } @AuthPermissions("agroup:edit") // Specific permissions are required @Mapping("edit/{id}") public void edit(int id) { // Edit the display page , Need edit permission } @AuthRoles("admin") // Need specific roles @Mapping("edit/{id}/ajax/save") public void save(int id) { // Edit processing interface , Administrator privileges required }}The advantage of annotation is , Micro visible , On a method, you can see what permissions or roles it needs , It's not easy to ignore .
- Combined use
commonly , use Configuration rules , Control all the addresses you need to log in to ; use annotation , Control specific permissions or roles .
3、 ... and 、 Source code of this case
https://gitee.com/noear/solon_demo/tree/master/demo16.solon_auth
Four 、 Other production project applications
https://gitee.com/noear/water/tree/master/wateradmin
https://gitee.com/noear/sponge/tree/main/spongeadmin
attach :Solon Project address
attach :Solon Other introductory examples
- Solon Getting started example :https://gitee.com/noear/solon_demo
- Solon Rpc Getting started example :https://gitee.com/noear/solon_rpc_demo
- Solon Cloud Getting started example :https://gitee.com/noear/solon_cloud_demo
- Solon Advanced tutorial examples :https://gitee.com/noear/solon_advance_demo
边栏推荐
- [to be continued] [UE4 notes] L1 create and configure items
- object serialization
- 被舆论盯上的蔚来,何时再次“起高楼”?
- 【论文笔记】Multi-Goal Reinforcement Learning: Challenging Robotics Environments and Request for Research
- Learning notes of "hands on learning in depth"
- Ue4/ue5 illusory engine, material part (III), material optimization at different distances
- 服务熔断 Hystrix
- Research on the value of background repeat of background tiling
- Lua wechat avatar URL
- [allocation problem] 135 Distribute candy
猜你喜欢
![[interval problem] 435 Non overlapping interval](/img/a3/2911ee72635b93b6430c2efd05ec9a.jpg)
[interval problem] 435 Non overlapping interval
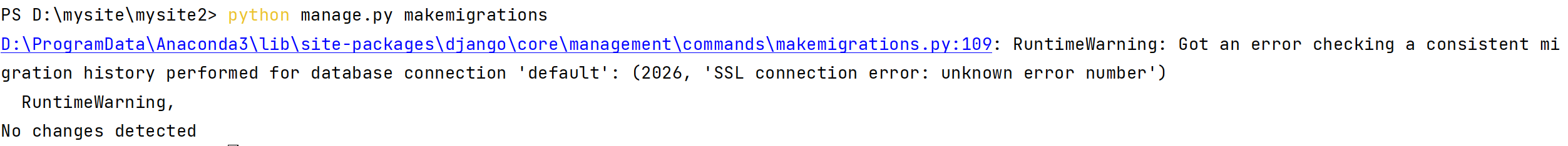
Django reports an error when connecting to the database. What is the reason
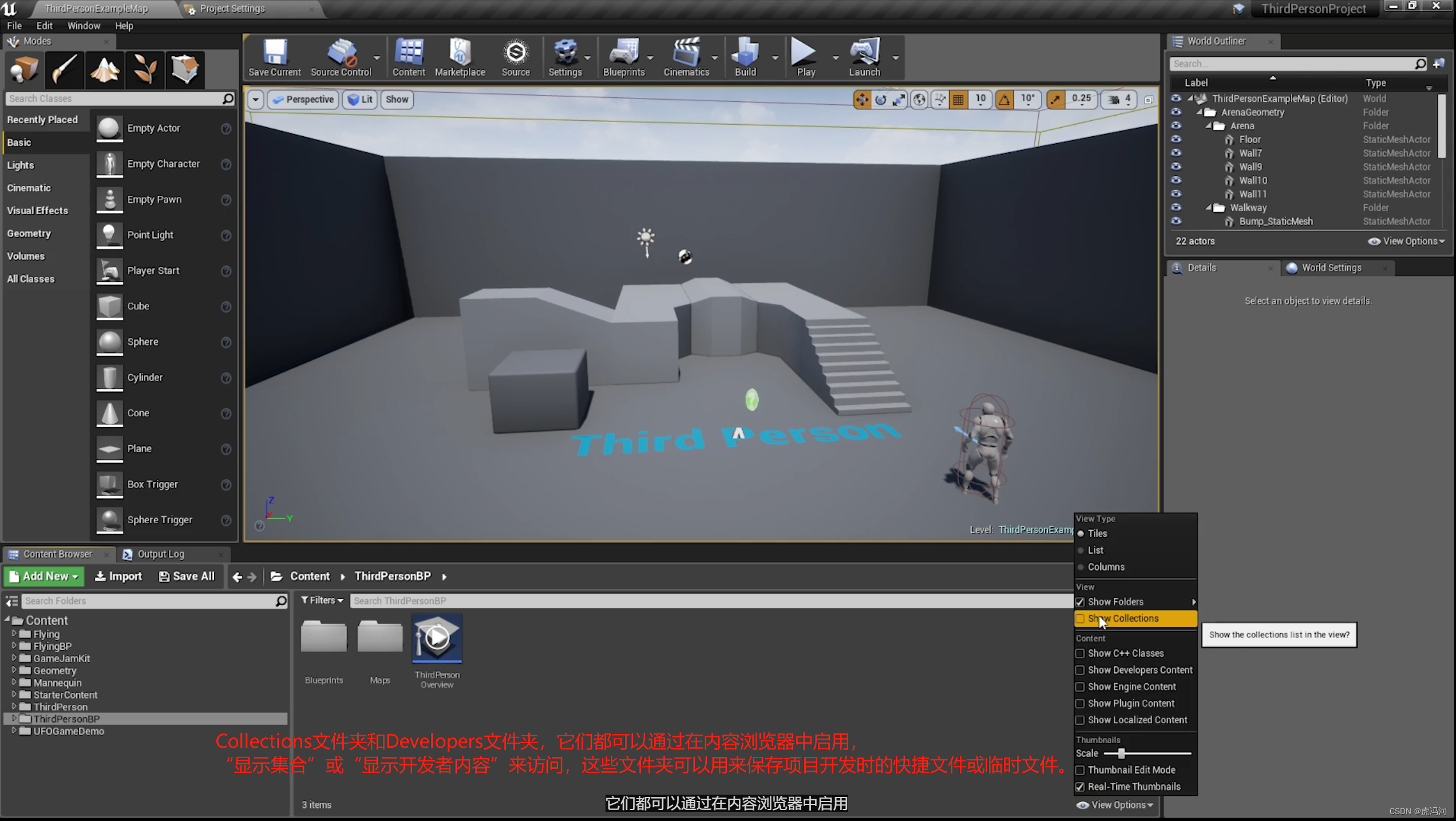
UE fantasy engine, project structure
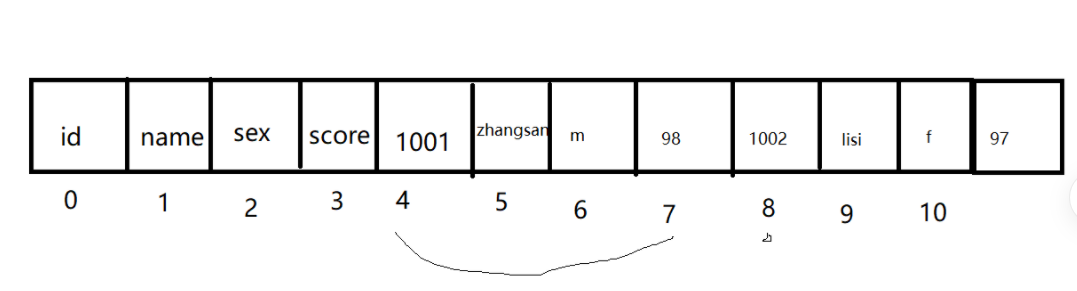
object serialization
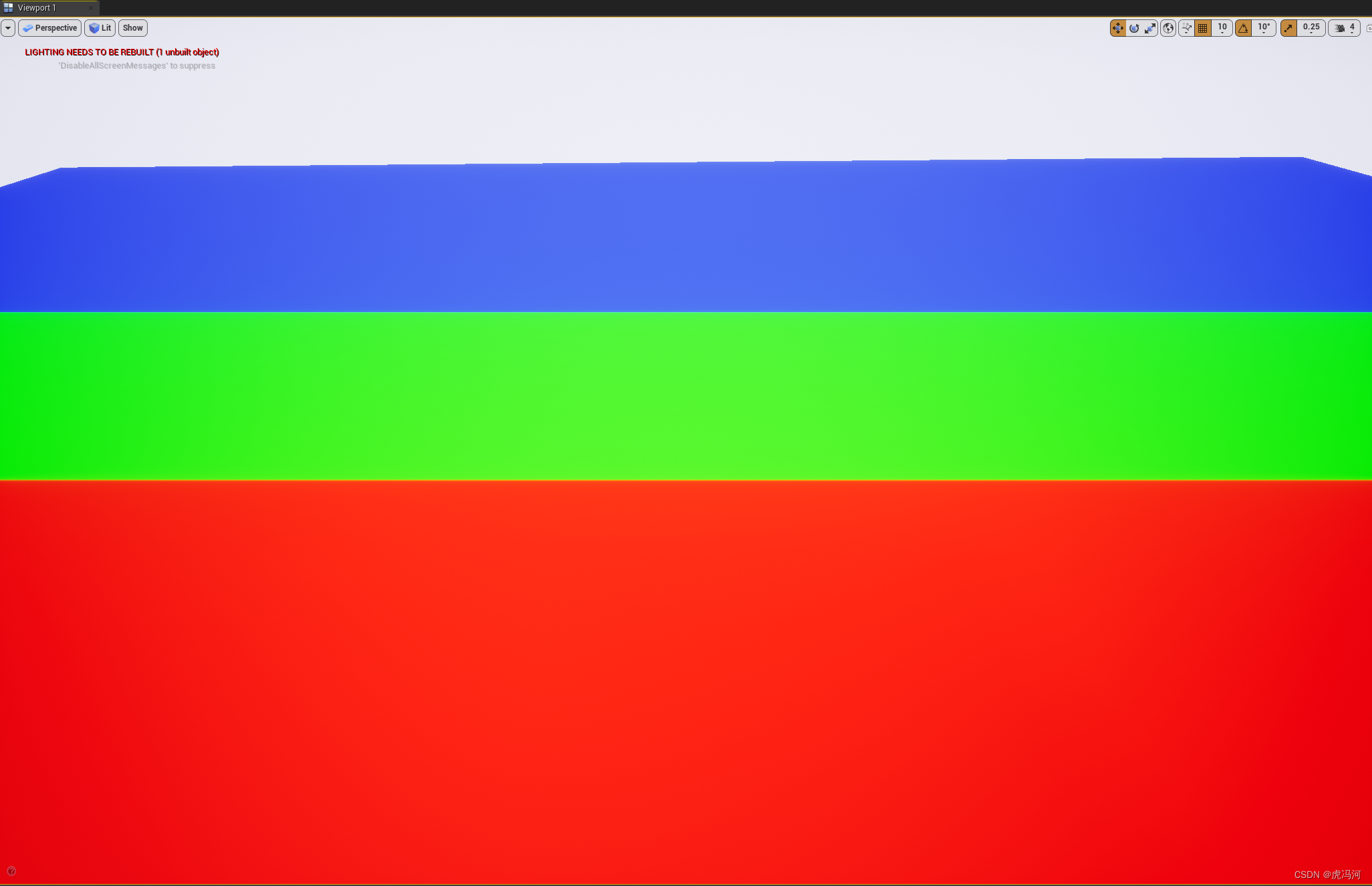
UE4/UE5 虚幻引擎,材质篇(三),不同距离的材质优化
嵌入式数据库开发编程(零)

Optimization scheme of win10 virtual machine cluster

Collapse of adjacent vertical outer margins
![[转]: OSGI规范 深入浅出](/img/54/d73a8d3e375dfe430c2eca39617b9c.png)
[转]: OSGI规范 深入浅出

Applet live + e-commerce, if you want to be a new retail e-commerce, use it!
随机推荐
cocos_ Lua listview loads too much data
FVP和Juno平台的Memory Layout介绍
Applet live + e-commerce, if you want to be a new retail e-commerce, use it!
Page countdown
[interval problem] 435 Non overlapping interval
cocos2dx_ Lua card flip
win下一键生成当日的时间戳文件
[转]MySQL操作实战(三):表联结
2022/7/1學習總結
Yolov5 adds attention mechanism
Magnifying glass effect
Haut OJ 1321: mode problem of choice sister
Binary search basis
64 horses, 8 tracks, how many times does it take to find the fastest 4 horses at least
[to be continued] [UE4 notes] L2 interface introduction
对象的序列化
小程序直播+电商,想做新零售电商就用它吧!
[depth first search] 695 Maximum area of the island
[turn to] MySQL operation practice (I): Keywords & functions
Embedded database development programming (zero)