当前位置:网站首页>Graphite document: four countermeasures to solve the problem of enterprise document information security
Graphite document: four countermeasures to solve the problem of enterprise document information security
2022-07-06 23:02:00 【Hua Weiyun】
Have you ever received such a call , The other party can say your name accurately 、 Schools attended 、 The year of enrollment and the mobile phone number you used , Then tell you that you opened campus loan when you were in College , Now we need to close the campus loan according to what he said , Otherwise, it will affect your personal credit .
Although you have never opened a campus loan , But I can't help wondering if I opened it unintentionally ? So I'm ready to operate according to the other party's words , But after hanging up, you immediately received another call :“ Hello , I'm an Internet policeman , You just received a fraud call ……”
In addition to the above personal information disclosure , Enterprise information is always exposed to the risk of disclosure , Related information leakage events are not uncommon .
 Many traditional enterprises even “ hide one 's troubles and take no remedial measures ” Choose to abandon the digital way of working . This one-sided approach is naturally undesirable , But how can we ensure that the file data assets of the enterprise organization are safe and controllable ?
Many traditional enterprises even “ hide one 's troubles and take no remedial measures ” Choose to abandon the digital way of working . This one-sided approach is naturally undesirable , But how can we ensure that the file data assets of the enterprise organization are safe and controllable ?
Graphite Of Enterprise document life cycle safety management and control system , adopt Control and control 、 early warning 、 Remedy 、 trace 4 Big Countermeasures , It can effectively reduce file security risks , Eliminate the leakage of document information , And it's very simple .
01 Control and control : Give consideration to document security and circulation
A common requirement of modern office is : In the traditional office scene , The documents are scattered and stored in the hands of the heads of each group , The boss wants to check the summarized documents , You need to ask for documents one by one , Efficiency is very low , So we need to create team space after modern office , So that the relevant person in charge can obtain the required information faster and more conveniently .
But after realizing this requirement , We have another problem : Part of the data belongs to sensitive information , If only a few people in charge can see it , And groups cannot view each other's data , How to achieve this ?
Graphite The multiple permission system of can solve the problem of file Both safety and circulation The problem of .
First , We can create one 「 Team space 」, Add boss as 「 managers 」, Add the entire department as 「 Read only collaborators 」; Then create folders for each group , For example, South China 、 North China, etc .
In South China folder , Set the upper level directory collaborator to 「 No authority 」( That is, the whole sales department can't view the South China folder except the sales head and the boss ), Again Add South China group separately as 「 Read only collaborators 」, That's it “ In addition to the department head 、 Besides the boss and the members of the South China team , Other members cannot view the South China folder .”

Space permission settings
If the enterprise wants to be in each group of folders , Only the team leader can download files , Other members can only see , Can't download ”, Can pass 「 Advanced permission settings 」 Cancel the inheritance relationship of the parent directory , Also cancel the download permission of other roles , Then add group leaders manually , In this way, the differentiated permission configuration in the same folder is realized .

Advanced permission settings
Empathy , Considering all the complexities , Enterprises can also set who can print the document just like setting the view permission 、 Who can copy 、 Who can create a copy and so on .
Finer granularity permission settings , Graphite can also support . Take the cells of a table as an example , If the enterprise wants some cells in a table , All staff can view , But only the sales department can edit , Then you can set these cells separately 「 Lock permissions 」, Add 「 View only 」 jurisdiction , Add 「 Can edit 」 Permissions can be .

Lock cell
As small as a cell , Big to team space , Fine permission configuration can be carried out in Graphite Documents . By combining , Enterprises can customize a safe and flexible management and control system according to their own business scenarios , Maximize the free flow of enterprise knowledge on the premise of ensuring safety .
02 early warning : The operation warning setting controls the file security risk to the minimum
Suppose an employee is about to leave , Downloaded some working files to take away , Because the files are only stored in the employee's computer , The enterprise does not know that the employee downloaded multiple files in a short time , I don't know. TA Which files have been downloaded , This has buried an indefinite bomb for the security of documents .
stay Graphite document , Managers can use 「 File security warning 」 Set the maximum number of exported files per person per day , If there is an employee operation that triggers this number , The system will immediately send an email notification , Managers can know the operation dynamics of employees in time , And quickly judge whether the employee's behavior needs to be stopped according to the information in the document .

File security warning
It's not just an early warning of downloading , stay 「 File security warning 」 In the settings panel , You can also print 、 Open shared file 、 Create a copy and other operations to set the alert . For enterprises with more classified businesses , The real-time early warning mechanism can help enterprises control the file security risk to the minimum .
In the future, graphite will also launch a risk control engine to monitor sensitive words and abnormal behaviors , It can automatically judge dangerous operations , Temporarily disable high-risk accounts , Nip the accident in the cradle .

03 Remedy : File recovery 、 Authority modification and other functions , Minimize potential losses
If an employee deletes all important documents when leaving , If these files are stored in Graphite document Enterprise account , Managers can use 「 Locate the operator 」 Quickly recover deleted files , Minimize the negative impact of file loss on the business .

Restore the file to the custom location
If an employee fails to properly hand over work documents when leaving , The manager can directly assign the handover person to get these documents , Avoid poor handover affecting the follow-up work of the successor , Affect the smooth transition of business .

Account number handover of resigned employees
If an employee discloses confidential internal documents of the enterprise , Managers can also uniformly manage all open link files in the background , Modify file permissions , Avoid files being viewed by unauthorized personnel .
In graphite document , The manager has the right to operate all the files of the enterprise , Like a “ Invisible hand ”, Implement a series of remedial measures , Minimize the negative impact of accidents on business and enterprises .
04 trace : The accident scene can be restored , Personnel can be located
If confidential documents have been distributed to the Internet , Enterprises should review and hold accountable for this accident , But the path of file leakage is unknown , The responsible person is unknown , I don't know where to start .
stay Graphite document , Enterprises can view 「 The operation log 」, Directional query any time period 、 Operation records of any operator or any document , Include delete 、 Copy 、 Sign in 、 export …… Even open public links and other operations , Then search and filter to restore the accident scene and the person in charge , Location problem , And then make targeted improvement measures .

Trace the operation log and editing history
As Cloud store partners , Graphite document Private deployment services are also provided —— Deploy the whole graphite office suite and overall services on the enterprise's own servers , Support for public clouds , Private cloud and its own computer room , Under the premise of independent control of enterprise data , Use graphite office kit , And support the adoption of API Connect with the existing system , Effectively link the existing system with graphite office suite , Greatly improve the file security of enterprises , It can also meet more customized business scenarios .
Product links mentioned in the article : Graphite document SaaS edition
【 Huawei cloud store —— innovation , So let's start here 】
Writing graphite 、 A big moon
Editor: a big moon
边栏推荐
- 前置机是什么意思?主要作用是什么?与堡垒机有什么区别?
- C three ways to realize socket data reception
- Dayu200 experience officer runs the intelligent drying system page based on arkui ETS on dayu200
- HDU 5077 NAND (violent tabulation)
- How to achieve text animation effect
- Aardio - integrate variable values into a string of text through variable names
- The statement that allows full table scanning does not seem to take effect set odps sql. allow. fullscan=true; I
- Designed for decision tree, the National University of Singapore and Tsinghua University jointly proposed a fast and safe federal learning system
- (flutter2) as import old project error: inheritfromwidgetofexacttype
- memcached
猜你喜欢
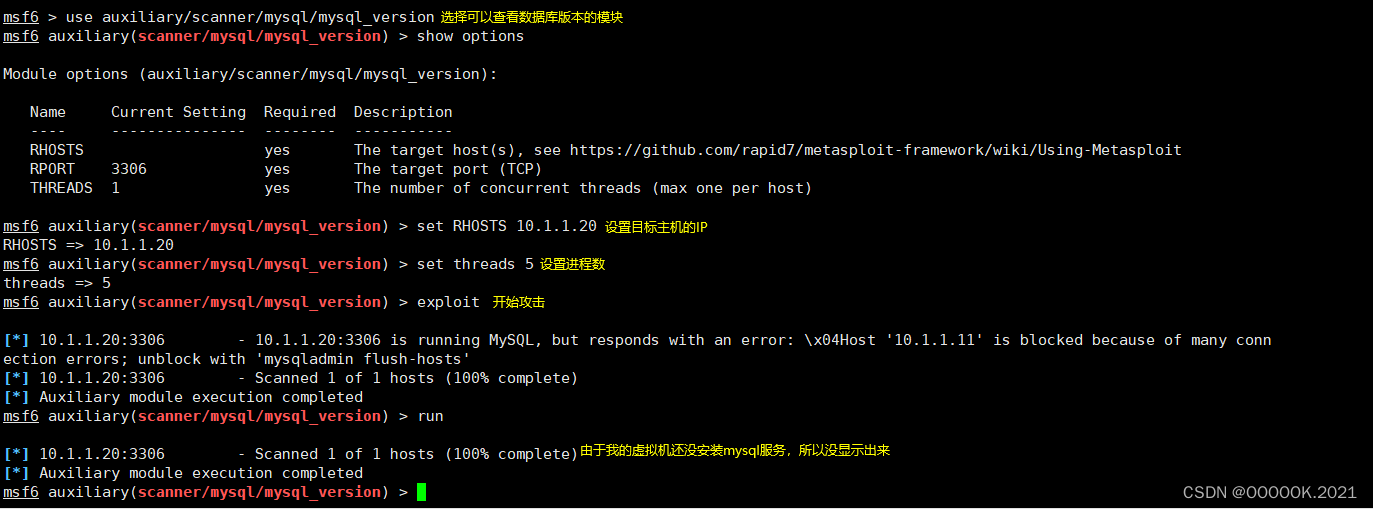
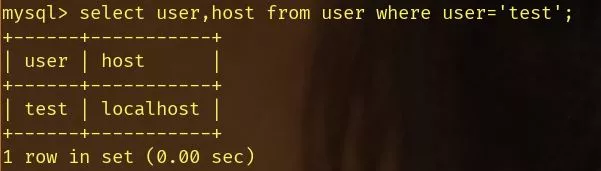
Mysql 身份认证绕过漏洞(CVE-2012-2122)
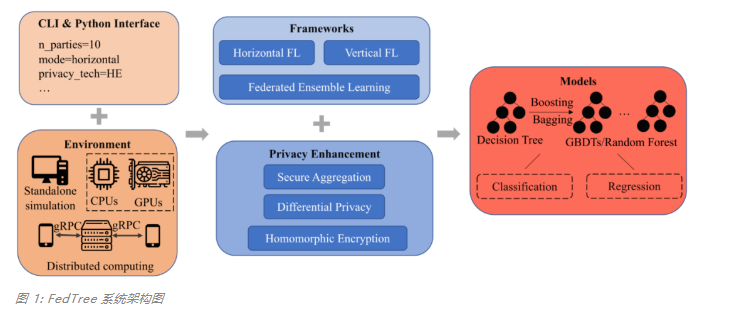
专为决策树打造,新加坡国立大学&清华大学联合提出快速安全的联邦学习新系统
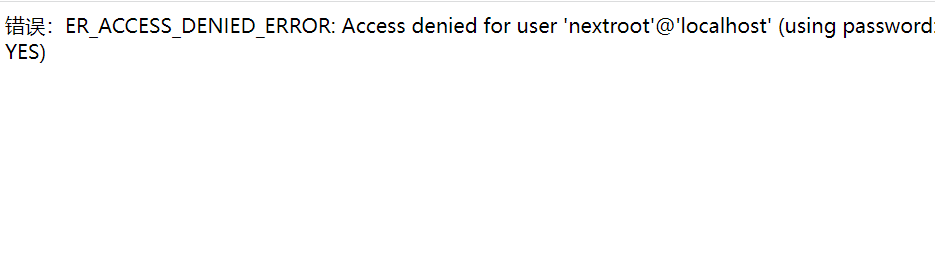
mysql连接vscode成功了,但是报这个错
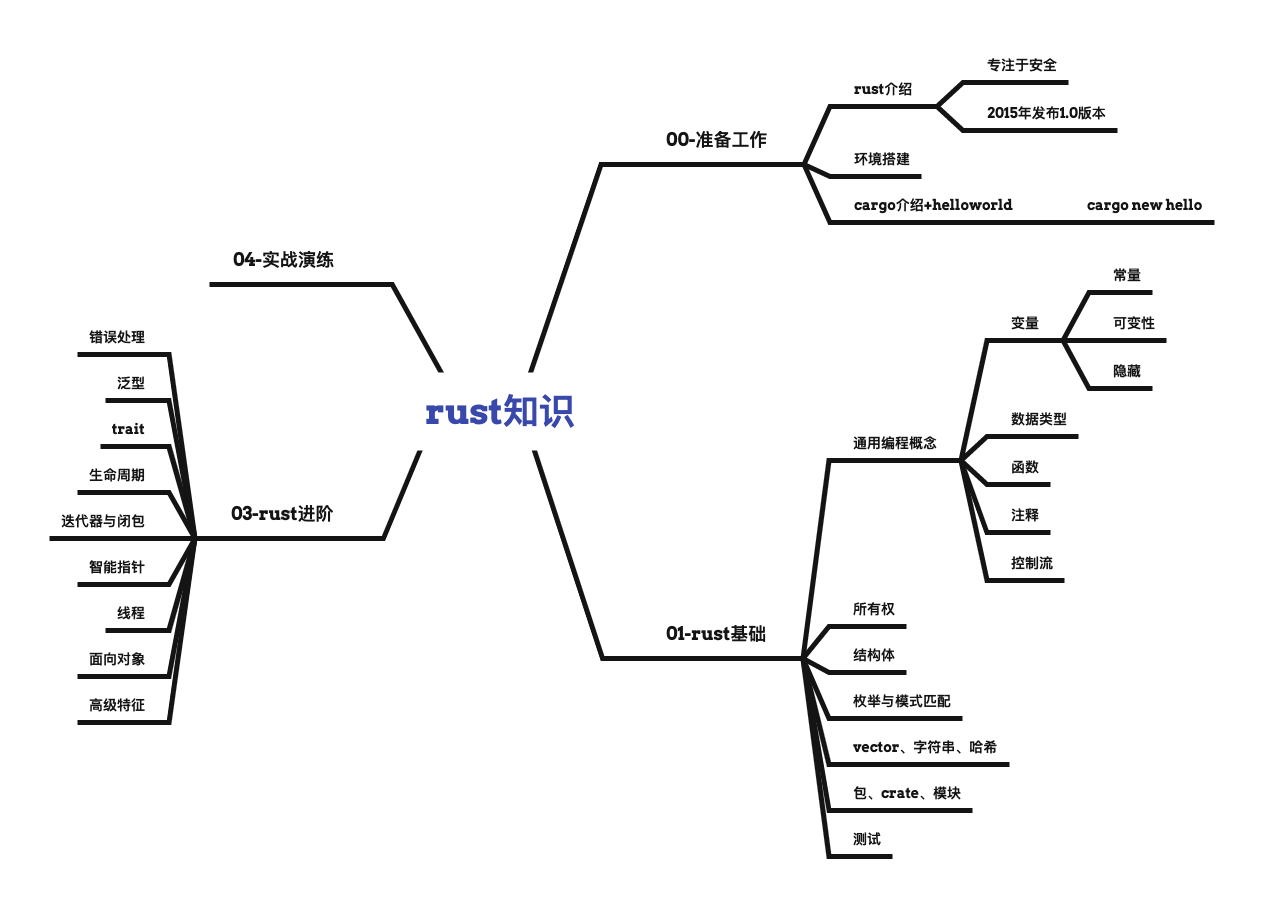
Rust knowledge mind map XMIND

室内LED显示屏应该怎么选择?这5点注意事项必须考虑在内
The problem that dockermysql cannot be accessed by the host machine is solved
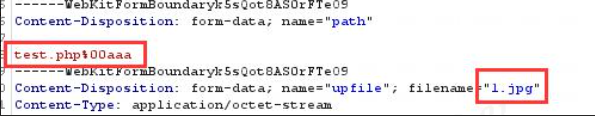
On file uploading of network security
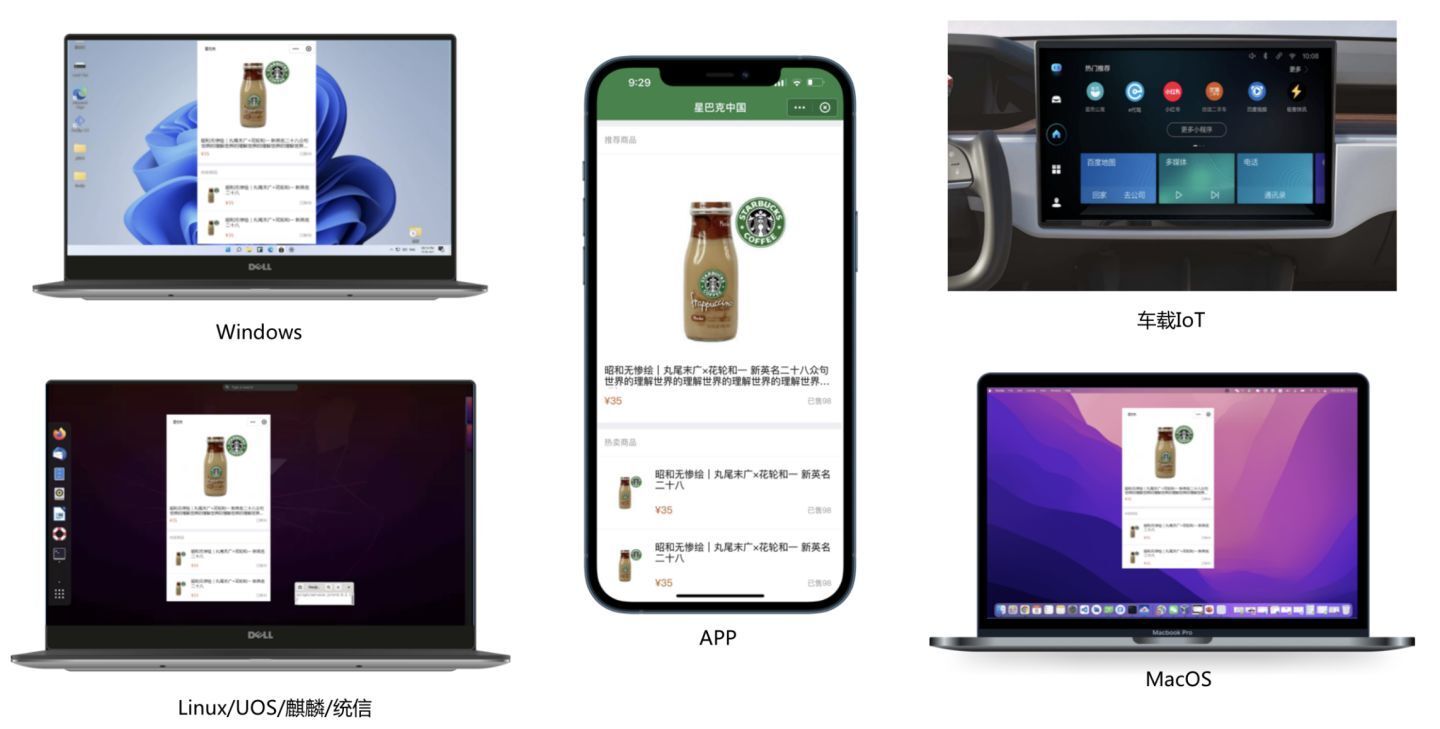
同构+跨端,懂得小程序+kbone+finclip就够了!
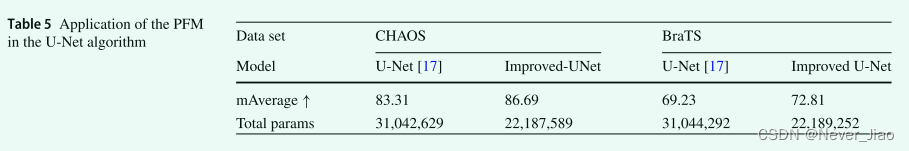
DR-Net: dual-rotation network with feature map enhancement for medical image segmentation
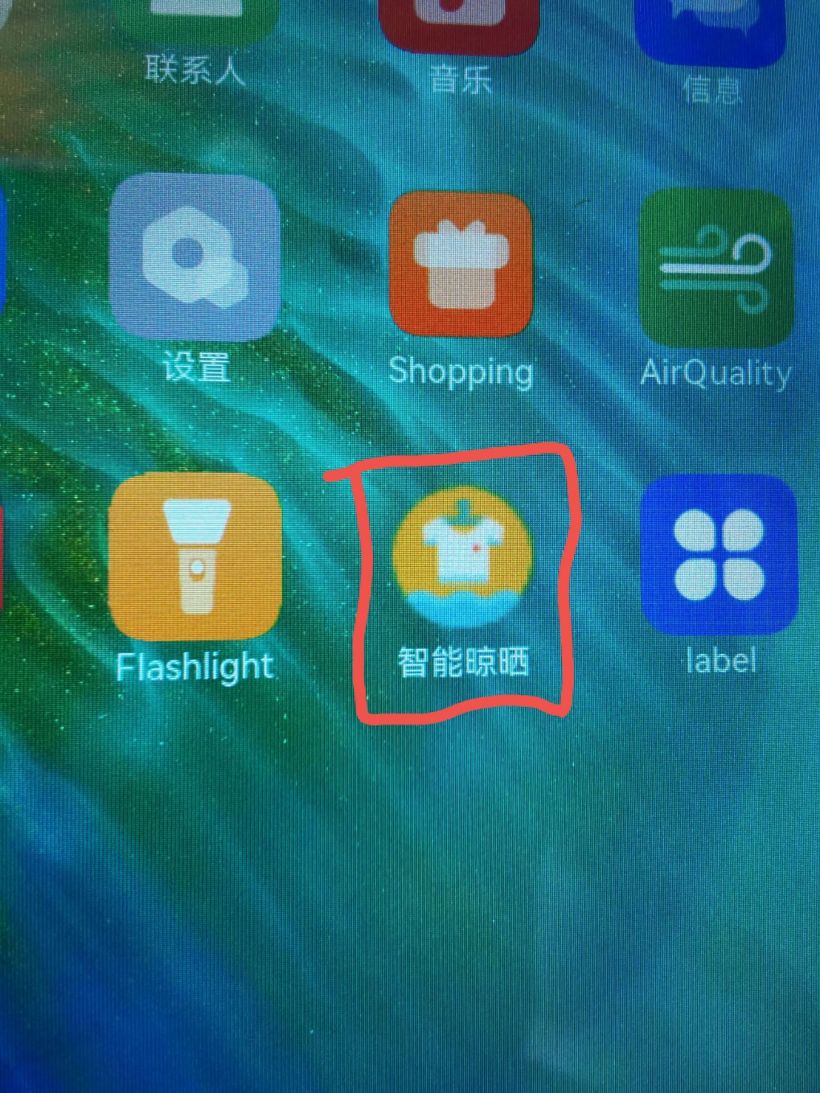
#DAYU200体验官# 在DAYU200运行基于ArkUI-eTS的智能晾晒系统页面
随机推荐
NPM cannot install sharp
uniapp滑动到一定的高度后固定某个元素到顶部效果demo(整理)
第十九章 使用工作队列管理器(二)
On file uploading of network security
Balanced Multimodal Learning via On-the-fly Gradient Modulation(CVPR2022 oral)
[IELTS speaking] Anna's oral learning record part1
【Unity】升级版·Excel数据解析,自动创建对应C#类,自动创建ScriptableObject生成类,自动序列化Asset文件
[unity] upgraded version · Excel data analysis, automatically create corresponding C classes, automatically create scriptableobject generation classes, and automatically serialize asset files
Jafka来源分析——Processor
同构+跨端,懂得小程序+kbone+finclip就够了!
How to choose the server system
(shuttle) navigation return interception: willpopscope
Const keyword
Aardio - does not declare the method of directly passing float values
Void keyword
How to use flexible arrays?
Flutter life cycle
机试刷题1
BasicVSR_ Plusplus master test videos and pictures
[step on pit collection] attempting to deserialize object on CUDA device+buff/cache occupy too much +pad_ sequence