当前位置:网站首页>Priority inversion and deadlock
Priority inversion and deadlock
2022-07-06 11:58:00 【Weiyuan escort agency】
1、 priority reverse
When resources are locked, low priority tasks preempt high priority tasks .
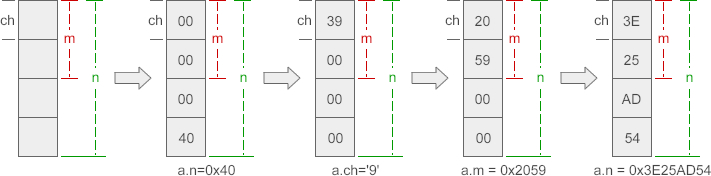
give an example : Mission A、B、C, The priority from low to high is 1、2、3, All tasks are completely preemptive , Mission A and C Shared resources R.
1. Mission A function , And for resources R Lock ;
2. Mission C Be activated to preempt tasks A, And try to resource R Lock , therefore C Get into WAITING state ,A Recover from the occupied place ;
3. Mission B Be activated and preempt the task A, Mission B Successful execution ;
4. Mission A Resume execution and release resources R, Mission A Execution completed ;
5. Mission C Recover and restore resources R Lock and complete the execution .
We observe the task B Priority is lower than task C But actually occupied the task C, This is priority reversal . In systems with high real-time requirements, it is unacceptable for such high priority tasks to be unexpectedly delayed . More serious is due to priority reversal , Mission C The delay time of is uncertain , Because anything better than the task A Tasks with high priority can preempt tasks A.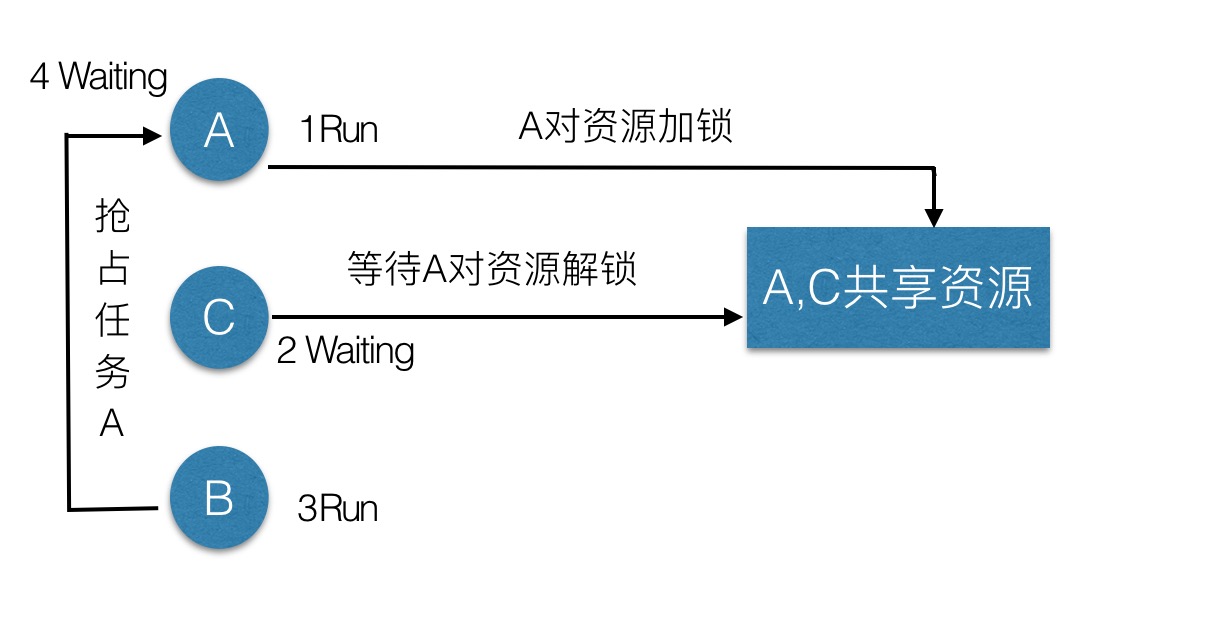
2、 Deadlock
Locking resources causes a conflict between two tasks , Each task locks the resources needed by another task , Make every task impossible .
give an example : Mission A、B, Share two resources R1、R2, Other situations are the same as those in priority inversion .
1. Mission A Yes R1 Lock ;
2. Mission B preemption A, Also on R2 Lock , Then try to R1 Lock , because R1 It's locked , So the task B Get into WAITING state ;
3. Mission A Resume execution , Try to be on R2 Lock , because R2 It's locked , So the task A Get into WAITING state ;
4. Other tasks enter the execution state , And the task A and B Can never continue .
Deadlock is likely not to be found in normal tests , After delivery to the customer, it is more difficult to be checked because the problem is difficult to recur .
There are many ways to solve priority inversion and deadlock , stay OSEK In the use of OS Priority ceiling protocol (priority ceiling protocol) It's the most effective way .
RT-thread Mutually exclusive Priority inheritance mechanism in quantity
2018-11-01 13:23:58
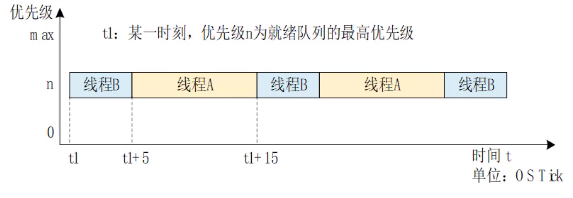
The three threads are H Threads 、M Threads 、L Threads
1. The priority order of the three threads is :H Threads > M Threads > L Threads ;
2. During normal operation H Threads can break M Threads and L Threads , M Threads can break L Threads ;
3. Suppose a resource in the system is protected , At this time, the resource is L Threads are using , At some point H The thread needs to use this resource , but L The thread is not used up ,H The thread cannot apply and enters the blocking state , At this time, priority reversal has occurred ;
When there is no priority inheritance mechanism :
If L When a thread is executing ,M The thread just woke up , because M Threads have a high priority , Will interrupt L Threads , preemption CPU Right to use , until M Thread execution complete ;
M Thread will CPU The right to use L Threads ,L The thread continues to execute ,L Release the resource after execution ;
H The thread gets the resource , Remove from the blocking state ;
This process , High priority H Waiting for the M Threads +L Thread time , If there are more threads , Then the system crashed , I can't afford to wait !
When there is a priority inheritance mechanism :
stay H When Xianchen applied for resources, he entered the blocking state because he could not apply for resources , The system will put the currently used resources L The priority of the thread is temporarily increased to H Threads have the same priority ;
here M The thread will not be interrupted when it is awakened L Threads ;
L Thread execution completed , Release resources ,H The thread obtains resources and continues to execute ,H The waiting time of the thread is only L Thread execution time .
original text :
OSEK study notes – Priority inversion and deadlock
边栏推荐
- JS array + array method reconstruction
- wangeditor富文本组件-复制可用
- error C4996: ‘strcpy‘: This function or variable may be unsafe. Consider using strcpy_ s instead
- XML文件详解:XML是什么、XML配置文件、XML数据文件、XML文件解析教程
- 【Flink】CDH/CDP Flink on Yarn 日志配置
- Machine learning -- decision tree (sklearn)
- inline详细讲解【C语言】
- 树莓派 轻触开关 按键使用
- Apprentissage automatique - - régression linéaire (sklearn)
- MySQL数据库面试题
猜你喜欢
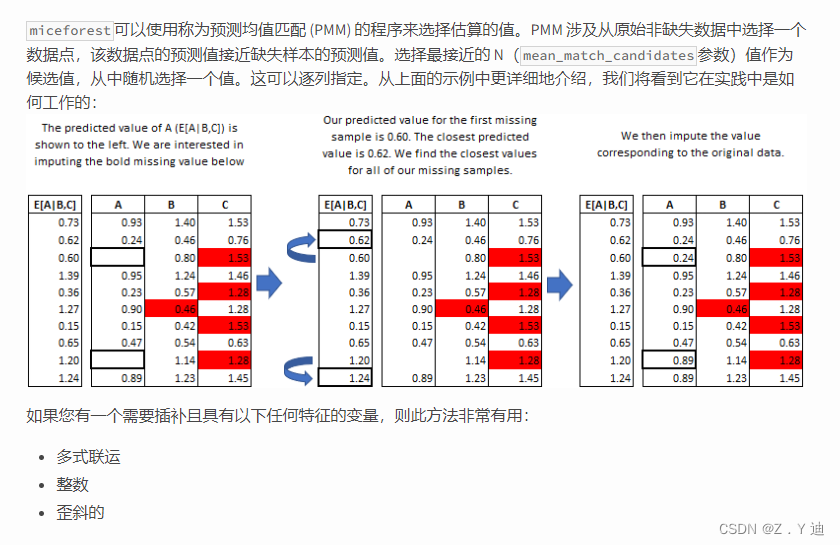
数据分析之缺失值填充(重点讲解多重插值法Miceforest)
Mysql的索引实现之B树和B+树
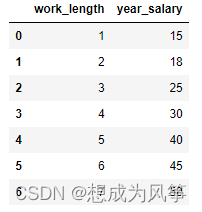
电商数据分析--薪资预测(线性回归)
JS object and event learning notes
共用体(union)详解【C语言】
RT-Thread 线程的时间片轮询调度
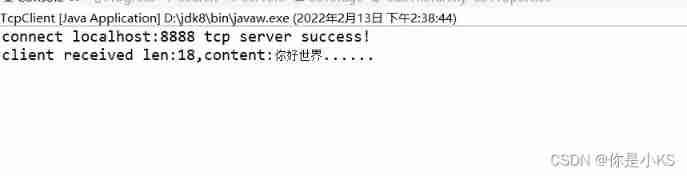
Vert. x: A simple TCP client and server demo

機器學習--線性回歸(sklearn)
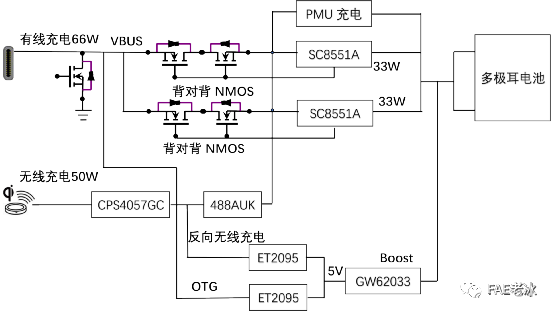
Analysis of charging architecture of glory magic 3pro

{one week summary} take you into the ocean of JS knowledge
随机推荐
E-commerce data analysis -- User Behavior Analysis
Selective sorting and bubble sorting [C language]
2019 Tencent summer intern formal written examination
RT-Thread API参考手册
arduino获取数组的长度
Reno7 60W super flash charging architecture
Stage 4 MySQL database
[Flink] Flink learning
Detailed explanation of nodejs
冒泡排序【C语言】
[BSidesCF_2020]Had_a_bad_day
Characteristics, task status and startup of UCOS III
MySQL数据库面试题
数据库面试常问的一些概念
4. Install and deploy spark (spark on Yan mode)
ESP8266通过arduino IED连接巴法云(TCP创客云)
Contiki source code + principle + function + programming + transplantation + drive + network (turn)
Raspberry pie tap switch button to use
wangeditor富文本组件-复制可用
[yarn] CDP cluster yarn configuration capacity scheduler batch allocation