当前位置:网站首页>HW notes (II)
HW notes (II)
2022-07-07 03:48:00 【H0ne】
HW Types of alarms found during
web attack : Information disclosure , Weak password ,xss,sql, Upload files , File contains ,webshell, Command execution ,xxe
Threat Intelligence : Trojan remote control , Mining Trojan , Blackmail virus , Botnet , Black market tools
sql Inject ,webshell How to determine the real attack
You can use payload Judge , Normal business requests sql The whole statement is long and no sensitive function is used ,sql Injected into the event request body payload It is usually short and there are sensitive functions in the statement such as sleep updatexml
Flow side / Main engine side How to determine false positives
The attack mainly comes from three directions , Network side , Host side and application side . The network side is traffic , Mainly check the alarm analysis of safety equipment , The host side sees what commands are executed , Or whether it is passed on , Application side view waf The firewall is good
Ideas for emergency response
First, check whether there is a false alarm , Isolate the host instead of false positives
To collect information : Collect customer information and poisoning host information , Include samples
Judgment type : Judge whether it is a security incident , What kind of security incident , blackmail , dig , Broken net ,ddos etc.
In depth analysis : Log analysis , Process analysis , Start item analysis , Sample analysis
The log was deleted : Is there a full flow device , parallel connection , see wireshake, logon server , See if there may be process log occupation , According to the process details , Find the soft connection , Then continue to view the recovery log
Clean up and disposal : Kill the process directly , Delete file , patch up , XOR is to repair files
Output report
Network seven layer protocol or model
osi Model : The physical layer , Data link layer , The network layer , Transport layer , The session layer , The presentation layer , application layer
tcp/ip(4 layer ): Network connection layer , The network layer , Transport layer , application layer
Research on Trojan horse virus , The virus broke out , How to deal with it , For example, worms
1、 Ask about the scope of the attack
2、 Attack trace mining
3、 Sample analysis
4、 Check and eradicate backdoors and Trojan files
cpu Occupancy rate and log troubleshooting
log4j Loophole
log4j With the help of JNDI Plug in vulnerability , use JNDI As a springboard to perform rebound shell
After finding the ice scorpion , Upload webshell The way of action
It mainly depends on the version of ice scorpion ,2.0 and 3.0 The encryption method of is different , Generally, ice scorpions are common 3.0, After finding the ice scorpion , see session And check whether there is md5 Encrypt data
linux Emergency and windows Emergency thinking , Mainly about the troubleshooting ideas and orders
linux Investigation thought , Mainly the source code , Log analysis , Information system analysis , Use d Whether shield scanning has webshell There is , then diff Source information , Check the modified places , Logs are divided into network logs and system logs , Network logs are mainly used find command , The system log uses last command , There is also system information analysis , Generally, when customer service uploads scripts, they run with scripts , Some customer service do not upload scripts , Then use history command , Check out the sensitive Directory , View port information
windows Mainly concentrated in accounts , journal , Port query , and linux Be the same in essentials while differing in minor points
The deployment mode of the heavenly eye
Bypass deployment , Switch traction flow
Successful log analysis cases
Common logs , Whether it is network log or system log , It's all about numbers , If a large number of 404, Or there are a lot of 4625, They all represent some meanings , Find out what the intruder is doing , How did you get in , Determine by matching some eigenvalues , stay linux of use grep and egrep To filter , stay windows of use log parse.
How to trace the attacker , The portrait of the attacker
Get access to , Stealing data , Take advantage of ,ddos etc.
agent ip, Springboard machine ,C2 The server etc.
Harpoon mail fishing ,web penetration , Puddle attack , Source penetration , Social engineering, etc
ip location id Tracking website url
HTTP Of TCP The difference between
tcp On the fourth floor ,http On the seventh floor
http It's a simple request - Response protocol tcp It's a connection oriented , reliable , Transport layer communication protocol based on byte stream ,http Running on the tcp above
eye
&& Double write , character AND Use capital letters
Field is sip dip Express original ip, Purpose ip, Followed by a colon and a specific field
eye : Based on network traffic and terminals EDR journal , Use Threat Intelligence , Rules engine , File virtual execution , Techniques like machine learning , Accurately discover the intrusion behaviors of known advanced network attacks and unknown new network attacks against hosts and servers in the network
NGSOC( Security situational awareness and security operations ): Based on big data platform , By collecting multiple , Heterogeneous massive logs , Using correlation analysis , machine learning , Threat Intelligence and other technologies , Help government and enterprise customer service to continuously monitor the network security situation , from “ Passive defense ” towards “ Active defense ” Advanced
Tianyan only analyzes the flow ,ngsoc Analysis is achieved testing Management Closed loop capability
边栏推荐
- .net中 接口可以有默认实现了
- Ubuntu20 installation redisjson record
- Not All Points Are Equal Learning Highly Efficient Point-based Detectors for 3D LiDAR Point
- pip只下载不安装
- GPT-3当一作自己研究自己,已投稿,在线蹲一个同行评议
- Graphical tools package yolov5 and generate executable files exe
- 如何替换模型的骨干网络(backbone)
- SSL certificate deployment
- Set WiFi automatic connection for raspberry pie
- 枚举通用接口&枚举使用规范
猜你喜欢
Gpt-3 is a peer review online when it has been submitted for its own research

25. (ArcGIS API for JS) ArcGIS API for JS line modification line editing (sketchviewmodel)
Create applet from 0

23. (ArcGIS API for JS) ArcGIS API for JS ellipse collection (sketchviewmodel)
API data interface of A-share index component data

小程序能运行在自有App中,且实现直播和连麦?
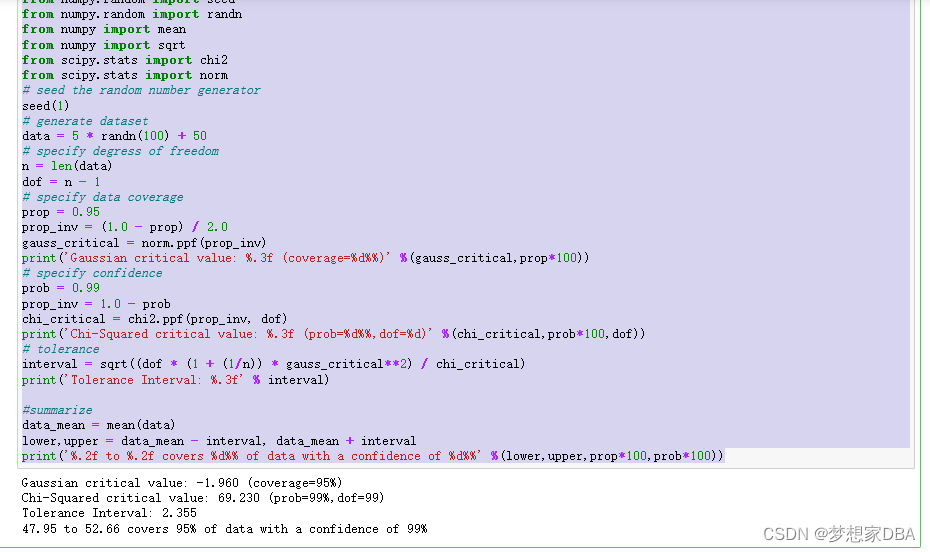
About Tolerance Intervals
GPT-3当一作自己研究自己,已投稿,在线蹲一个同行评议
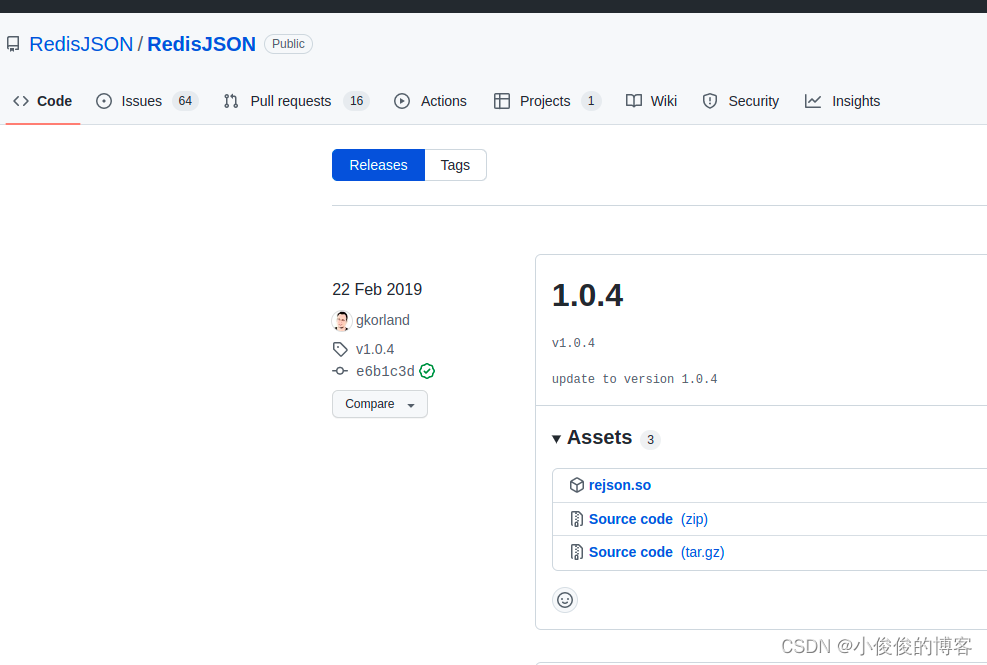
ubuntu20安裝redisjson記錄

Confirm the future development route! Digital economy, digital transformation, data This meeting is very important
随机推荐
[safe office and productivity application] Shanghai daoning provides you with onlyoffice download, trial and tutorial
如何自定义Latex停止运行的快捷键
Que savez - vous de la sérialisation et de l'anti - séquence?
U.S. Air Force Research Laboratory, "exploring the vulnerability and robustness of deep learning systems", the latest 85 page technical report in 2022
23. (ArcGIS API for JS) ArcGIS API for JS ellipse collection (sketchviewmodel)
密码学系列之:在线证书状态协议OCSP详解
HW-小记(二)
Probability formula
C# Task拓展方法
The latest 2022 review of "small sample deep learning image recognition"
Can the applet run in its own app and realize live broadcast and connection?
[C language] question set of IX
Introduction to opensea platform developed by NFT trading platform (I)
Free PHP online decryption tool source code v1.2
Machine learning notes - bird species classification using machine learning
GPT-3当一作自己研究自己,已投稿,在线蹲一个同行评议
19.(arcgis api for js篇)arcgis api for js线采集(SketchViewModel)
Vernacular high concurrency (2)
[colmap] 3D reconstruction with known camera pose
Top 50 hit industry in the first half of 2022