当前位置:网站首页>Simple process of penetration test
Simple process of penetration test
2022-07-05 13:54:00 【Cwxh0125】
Simple process
One . information gathering
nslookup whois
Two . Scan for leaks
namp=IP Range port 80 (iss,apache, What website )
Advanced scanning : Such as iss Loophole Scanning for website vulnerabilities
3、 ... and . Exploit
Four . Raise the right (shell Environmental Science , Desktop Environment , Highest authority ))
Manually test port number open : talent IP Address Test port
5、 ... and . Destroy the bodies
6、 ... and . leave oneself a way out
7、 ... and . Penetration test report
Practice
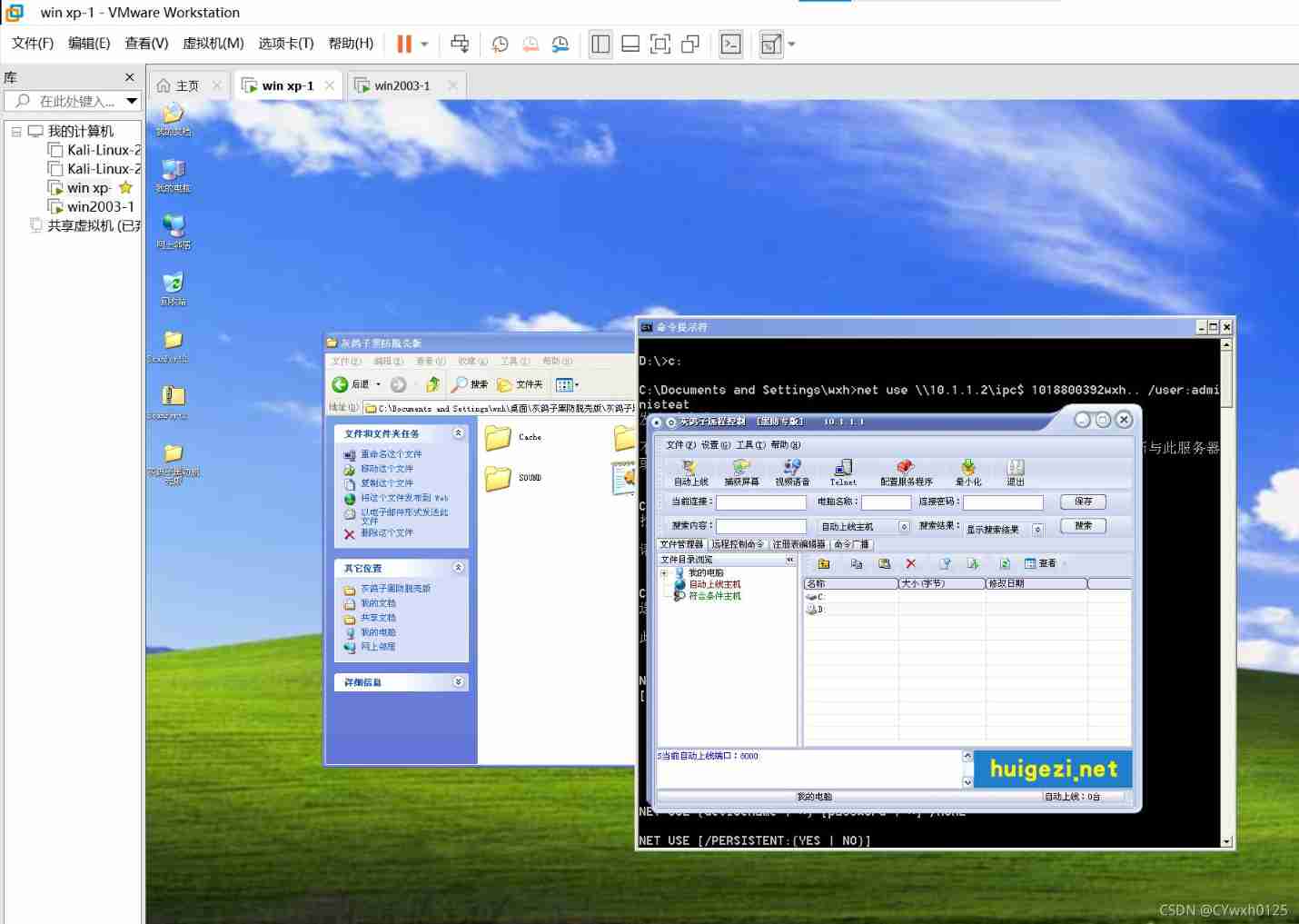
Open two virtual machines
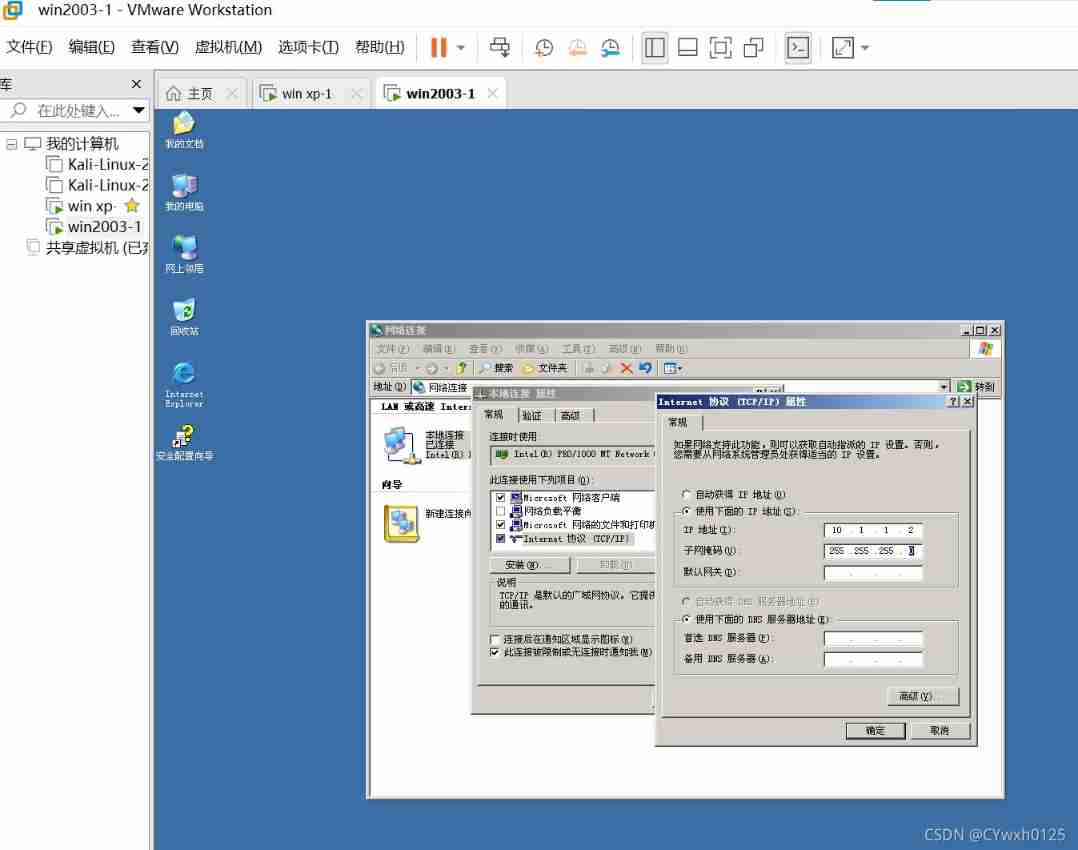
win2003 The server 10.1.1.2
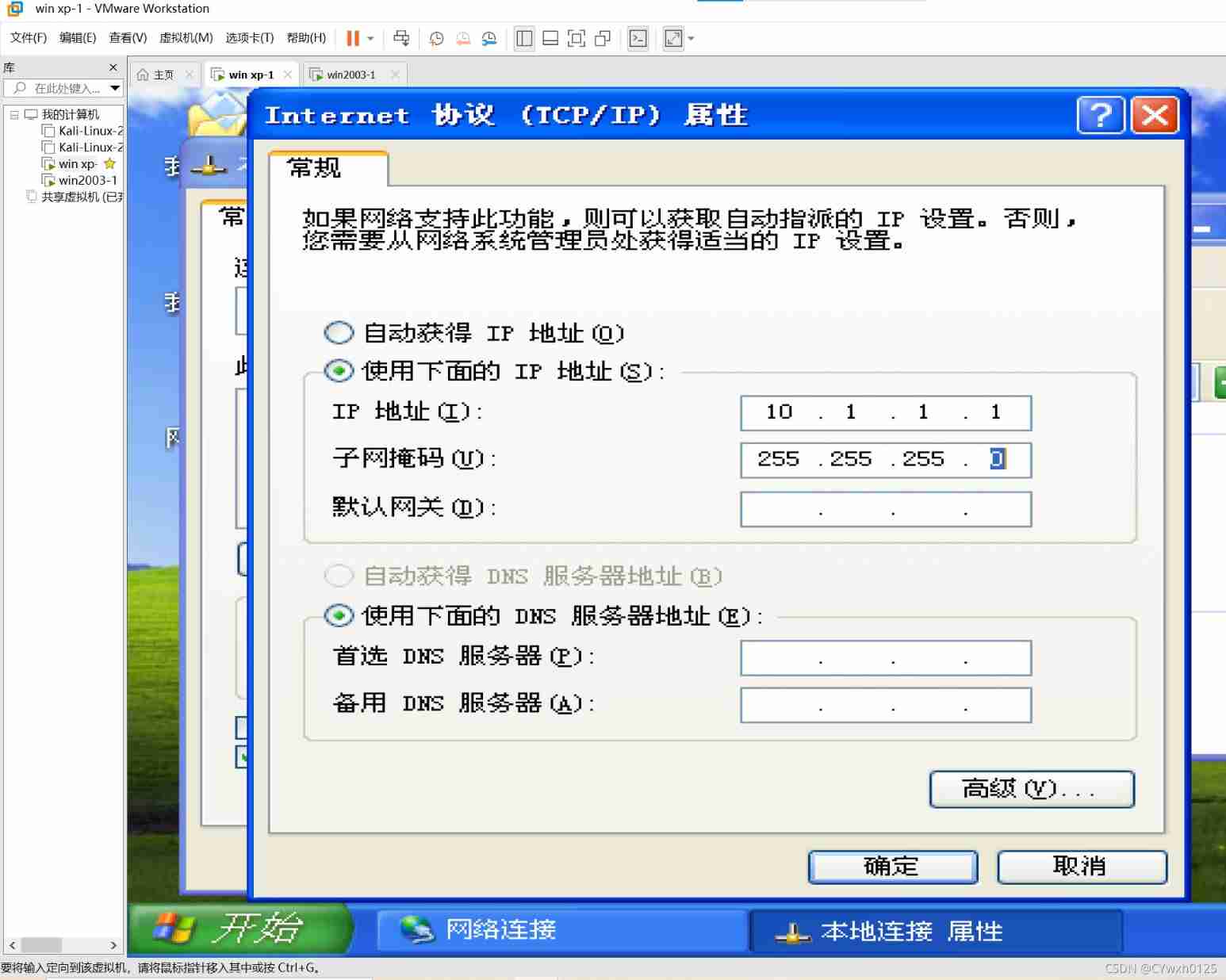
winxp staff 10.1.1.1
use xp attack 2003
First, two virtual machines should be able to communicate To configure IP In the same LAN
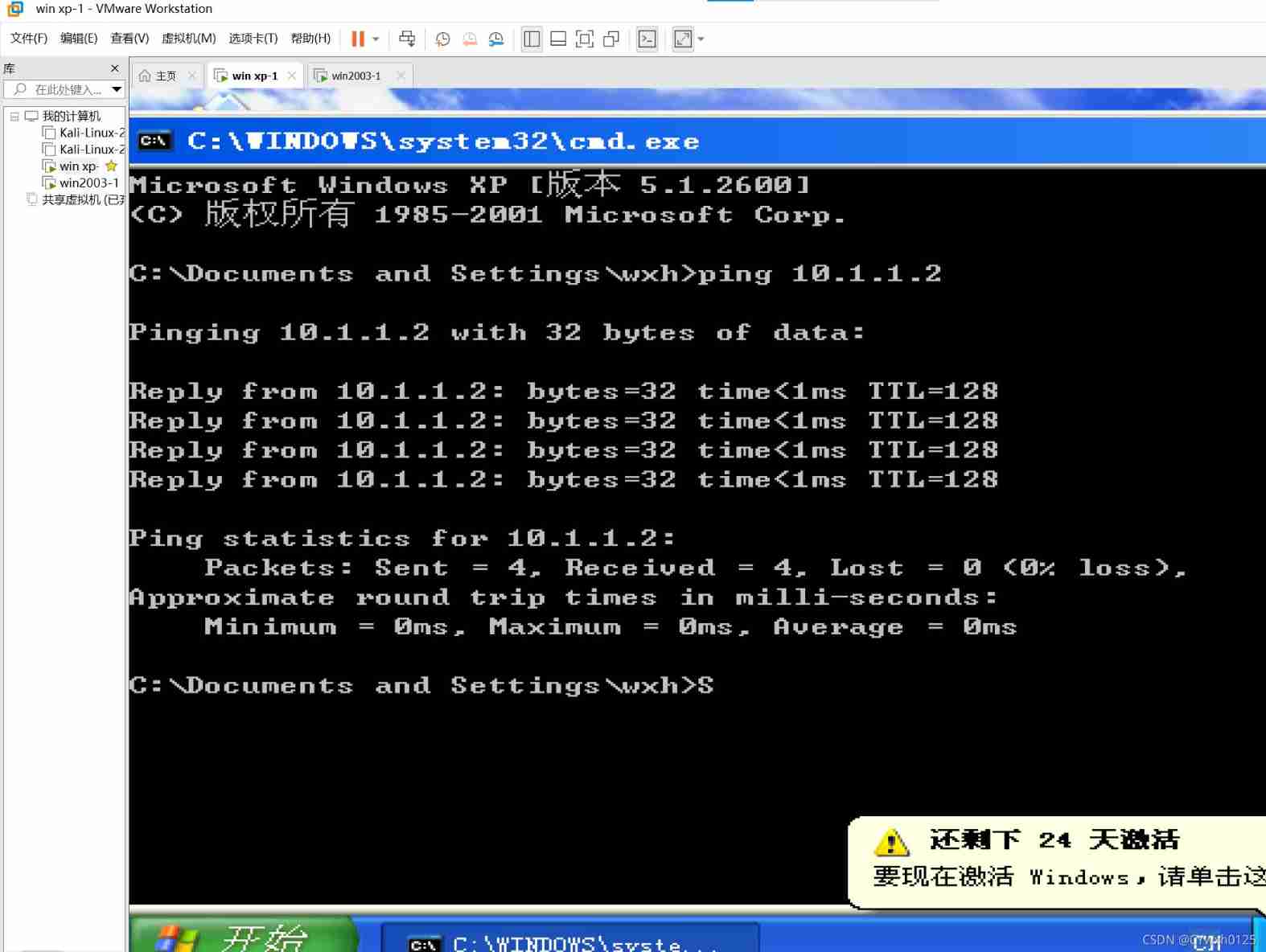
After the configuration is completed, try xp On ping once 2003 ping success
Next The attack
attack 445 attack ( Shared port )
First step : Port scanning
Manual scanning
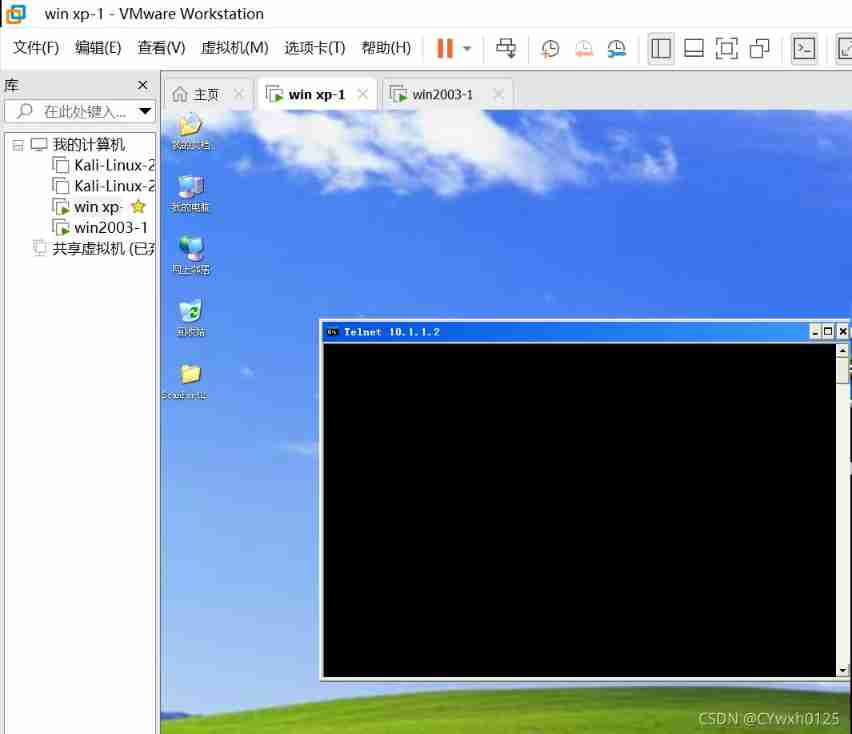
telnet IP port The following situations represent that the corresponding port is open 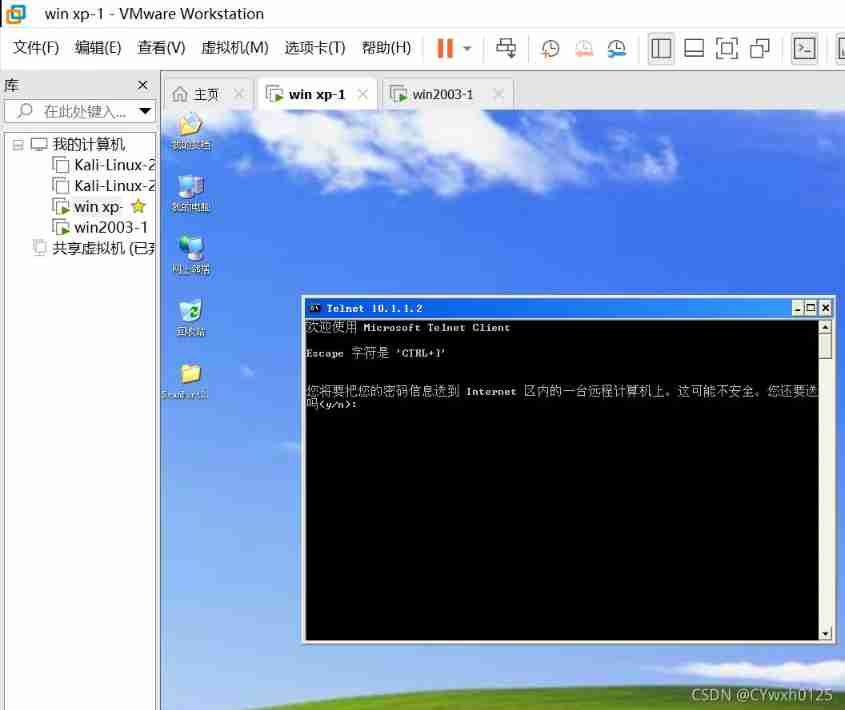
Automatic scanning Use scanport
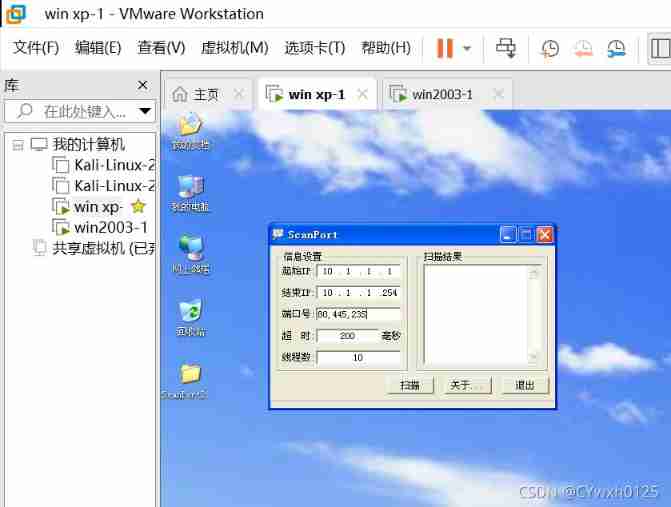
You can see xp and 2003 Both virtual machines are turned on 445 port

445 One of the exploits ipc$:
net use Used to connect your computer to shared resources ( Establish disk mapping ), Or disconnect the computer from shared resources ( Delete disk mapping ), When using this command without options , It lists the computer connections .
1) Make an empty connection :
net use \\IP\ipc$ "" /user:"" ( Be sure to pay attention to : This line of command contains 3 A space )
2) Establish a non empty connection :
net use \\IP\ipc$ " password " /user:" user name " ( There are also 3 A space )
3) Map default share :
net use z: \\IP\c$ " password " /user:" user name " ( You can put the other party's c The disk maps to its own z disc , And so on )
If you've established a goal ipc$, You can use IP+ Disk character +$ visit , Specific commands net use z: \\IP\c$
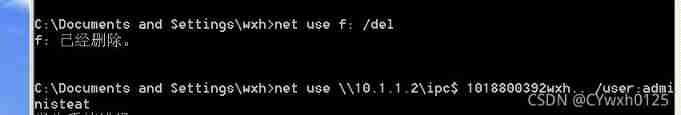
4) Delete one ipc$ Connect
net use \\IP\ipc$ /del
5) Delete shared mapping
net use c: /del Delete mapped c disc , And so on
net use * /del Delete all , There will be a prompt to press y confirm
3 View the shared resources of the remote host ( But you don't see the default share )
net view \\IP
Brutally crack the system password 445
Using tools ntscan
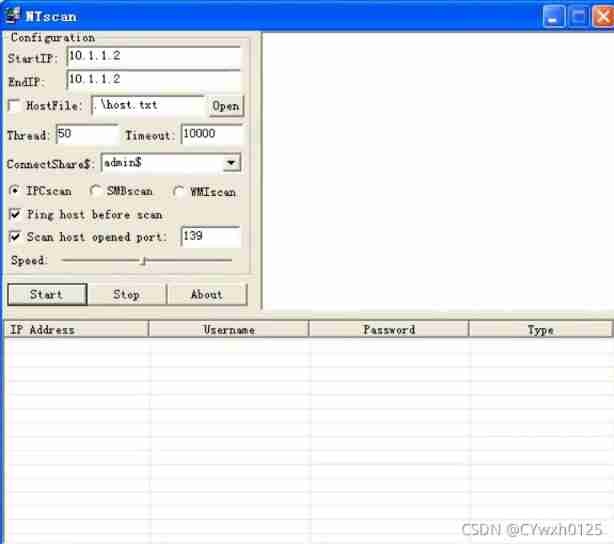
take user And the password burst out You can go through net use \\IP\ipc$ " password " /user:" user name " To make a connection
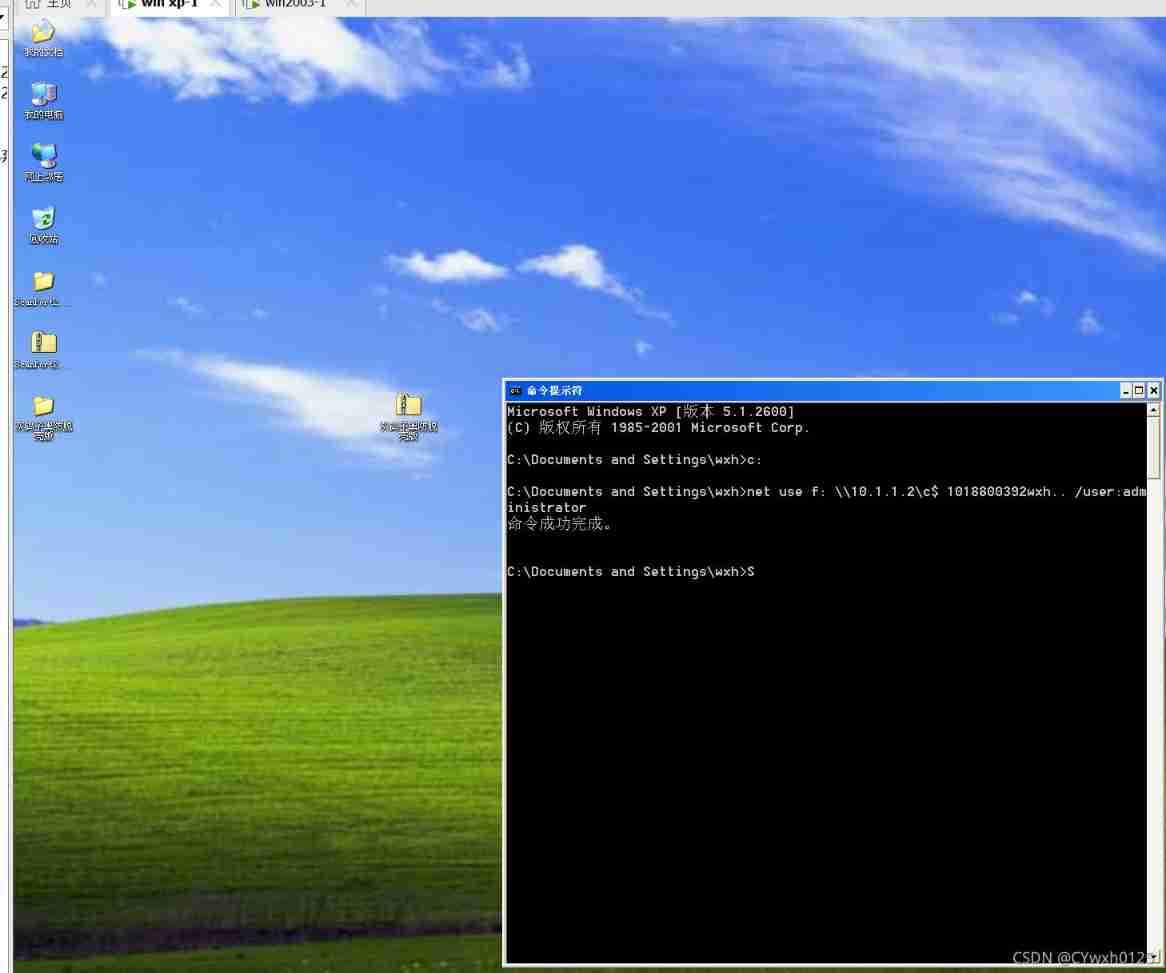
After successful connection, the back door can be left
Make a Trojan
copy Implant Trojans
边栏推荐
- Requests + BS4 crawl Douban top250 movie information
- These 18 websites can make your page background cool
- About the problem and solution of 403 error in wampserver
- Programmer growth Chapter 8: do a good job of testing
- NFT value and white paper acquisition
- 清大科越冲刺科创板:年营收2亿 拟募资7.5亿
- Recommendation number | what are interesting people looking at?
- js 从一个数组对象中取key 和value组成一个新的对象
- 荐号 | 有趣的人都在看什么?
- Interviewer soul torture: why does the code specification require SQL statements not to have too many joins?
猜你喜欢
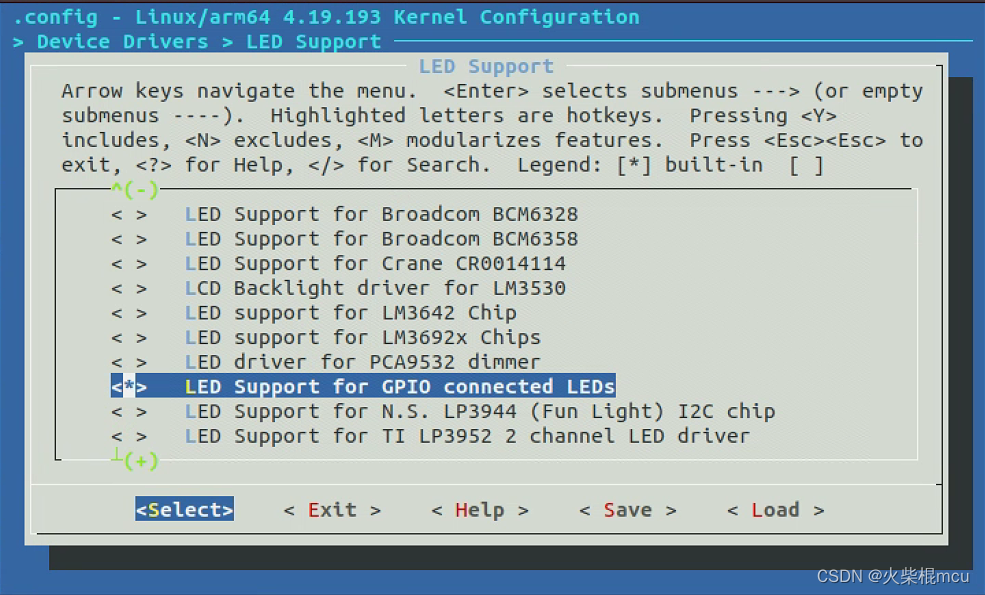
Rk3566 add LED

常见问题之PHP——Fatal error: Allowed memory size of 314572800 bytes exhausted...
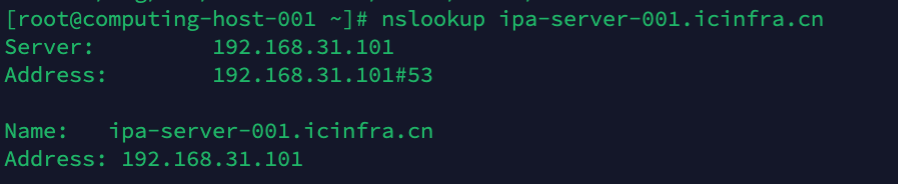
:: ffff:192.168.31.101 what address is it?
Data Lake (VII): Iceberg concept and review what is a data Lake

那些考研后才知道的事

Kotlin协程利用CoroutineContext实现网络请求失败后重试逻辑
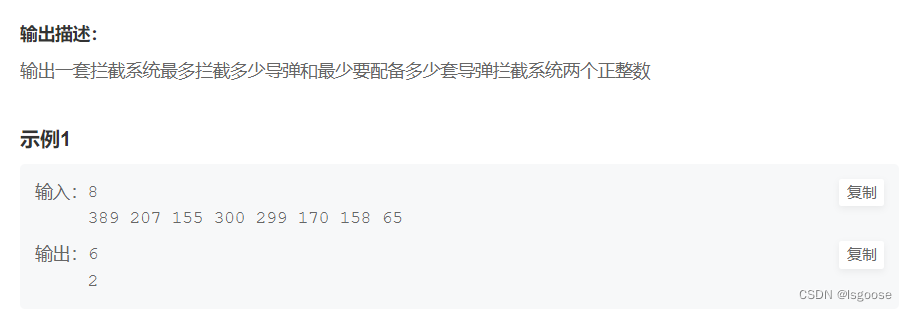
牛客网:拦截导弹

Can graduate students not learn English? As long as the score of postgraduate entrance examination English or CET-6 is high!
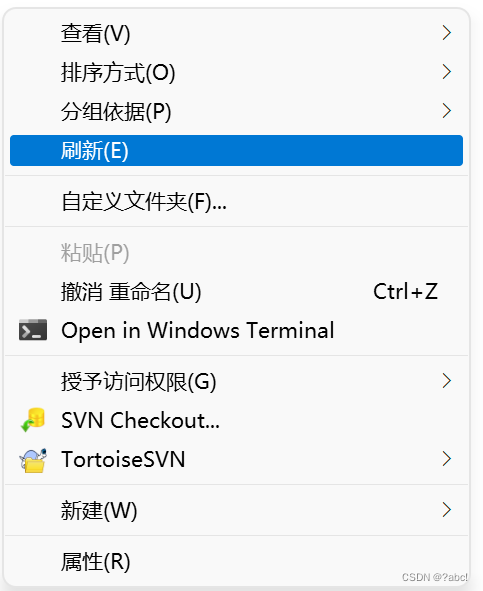
Usage, installation and use of TortoiseSVN

Catch all asynchronous artifact completable future
随机推荐
PHP character capture notes 2020-09-14
内网穿透工具 netapp
Summit review | baowanda - an integrated data security protection system driven by compliance and security
Kotlin协程利用CoroutineContext实现网络请求失败后重试逻辑
Solution to the prompt of could not close zip file during phpword use
Nantong online communication group
In addition to the root directory, other routes of laravel + xampp are 404 solutions
Hide Chinese name
aspx 简单的用户登录
Set up a website with a sense of ceremony, and post it to the public 2/2 through the intranet
LeetCode_67(二进制求和)
laravel-dompdf导出pdf,中文乱码问题解决
Embedded software architecture design - message interaction
昆仑太科冲刺科创板:年营收1.3亿拟募资5亿 电科太极持股40%
[js] basic syntax - for loop
What is information security? What is included? What is the difference with network security?
Jetpack compose introduction to mastery
Redis6 transaction and locking mechanism
Laravel框架运行报错:No application encryption key has been specified
asp. Net read TXT file