当前位置:网站首页>Sword finger offer II 019 Delete at most one character to get a palindrome
Sword finger offer II 019 Delete at most one character to get a palindrome
2022-07-06 16:08:00 【mrbone9】
Address :
Power button  https://leetcode-cn.com/problems/RQku0D/
https://leetcode-cn.com/problems/RQku0D/
This question is related to 680. Verify palindrome string Ⅱ identical
subject :
Given a non empty string s, Please judge if most If you delete a character from the string, you can get a palindrome string .
Example 1:
| Input : s = "aba" Output : true |
Example 2:
| Input : s = "abca" Output : true explain : You can delete "c" character perhaps "b" character |
Example 3:
| Input : s = "abc" Output : false |
Tips :
| 1 <= s.length <= 105 s It's made up of lowercase letters |
source : Power button (LeetCode)
link :https://leetcode-cn.com/problems/RQku0D
Copyright belongs to the network . For commercial reprint, please contact the official authority , Non-commercial reprint please indicate the source .
Ideas :
Here are some examples :
Palindrome :abba,abcba
It can be seen that as long as palindromes are deleted 1 Times are still palindromes
Non palindrome :abcb,bcba,cbbcc
The left pointer points to [0], The right pointer points to [len-1], Adjust the left or right pointer once , If the rest is palindromes, then you can
Let's take a longer example :ebcbbececabbacecbbcbe
The left pointer can be adjusted [5] ->[6], The right pointer cannot be adjusted [15]->[14], The total number of adjustments is also one
So the conclusion is , Scan the entire string with double pointers , If it's palindrome perhaps After one adjustment, the substring is also a palindrome , Then the result is ok , Otherwise, you can't
bool checksub(char *s, int i, int j)
{
bool ret = true;
while(i < j)
{
if(s[i] != s[j])
{
ret = false;
break;
}
i++;
j--;
}
return ret;
}
bool validPalindrome(char * s){
int slen = strlen(s);
int i,j;
int maxjudge = 0;
bool ret = true;
i = 0;
j = slen - 1;
while(i < j)
{
if(s[i] != s[j])
{
if( checksub(s, i, j-1) || checksub(s, i+1, j) )
{
ret = true;
break;
}
else
{
ret = false;
break;
}
}
i++;
j--;
}
return ret;
}边栏推荐
- frida hook so层、protobuf 数据解析
- 渗透测试 2 --- XSS、CSRF、文件上传、文件包含、反序列化漏洞
- Web based photo digital printing website
- If you want to apply for a programmer, your resume should be written like this [essence summary]
- Hdu-6025-prime sequence (girls' competition)
- 滲透測試 ( 1 ) --- 必備 工具、導航
- 双向链表—全部操作
- [teacher Gao UML software modeling foundation] collection of exercises and answers for level 20 cloud class
- 2027. Minimum number of operations to convert strings
- 信息安全-安全编排自动化与响应 (SOAR) 技术解析
猜你喜欢
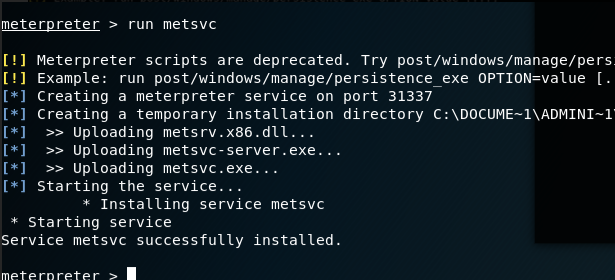
渗透测试 ( 3 ) --- Metasploit Framework ( MSF )
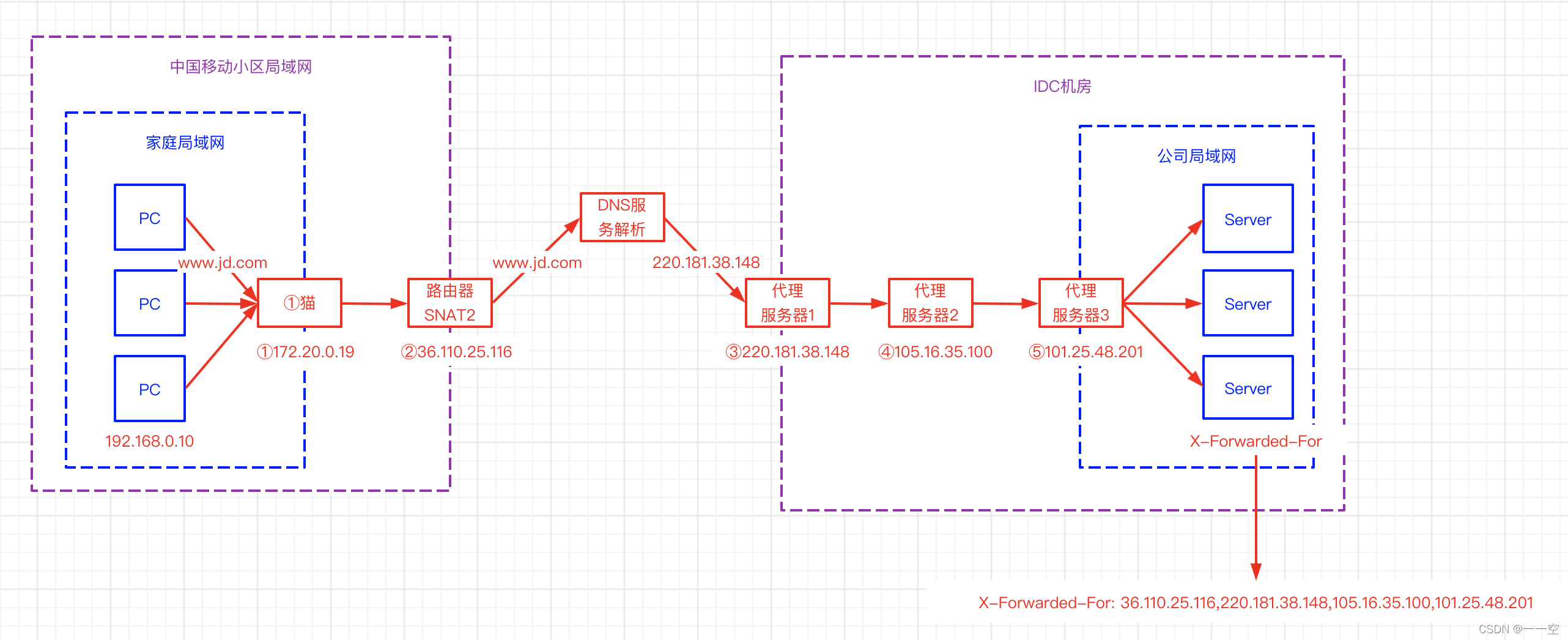
X-forwarded-for details, how to get the client IP
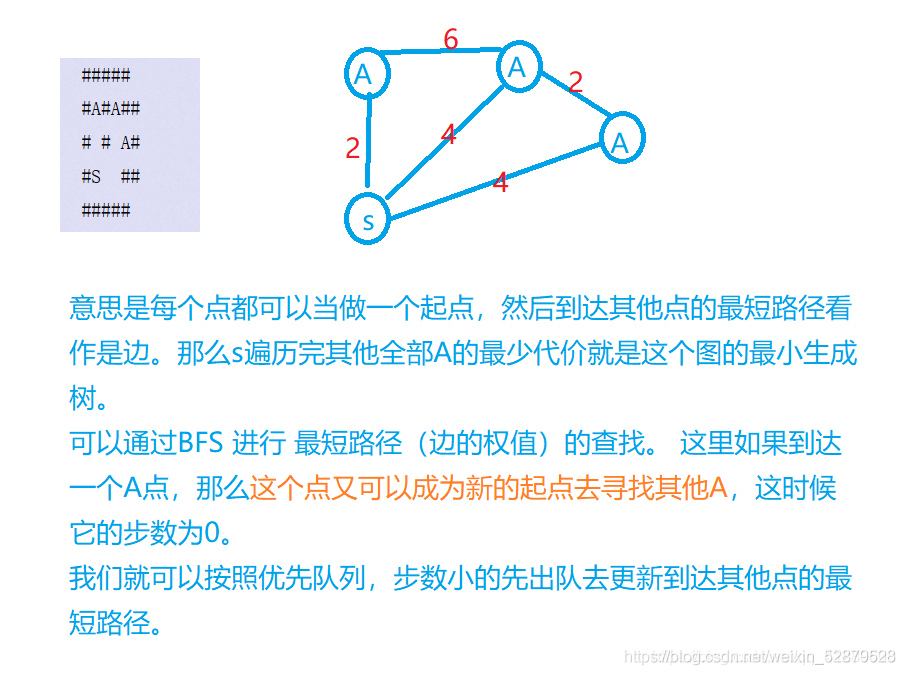
Borg Maze (BFS+最小生成树)(解题报告)
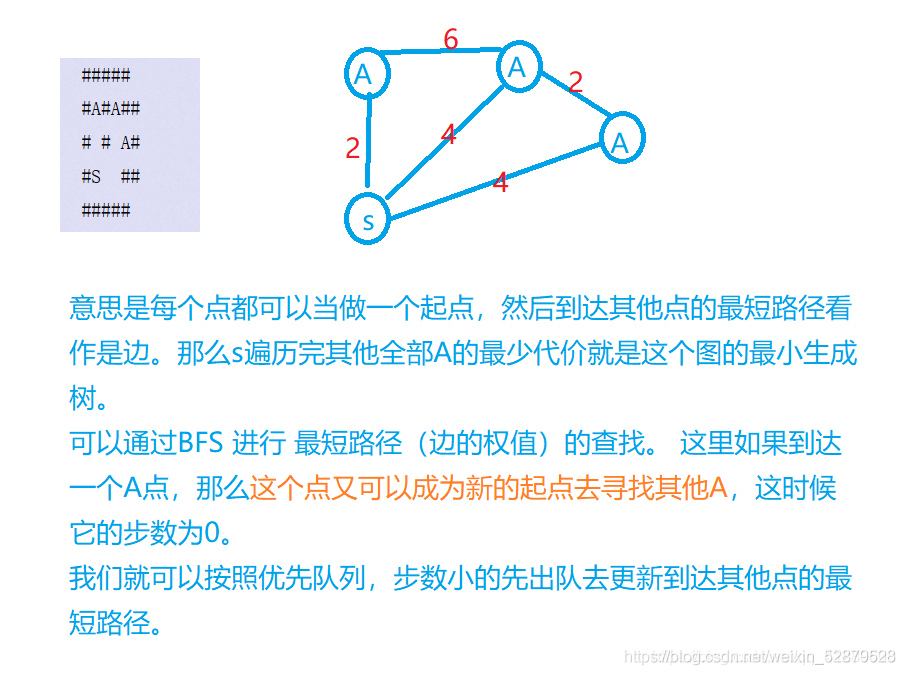
Borg maze (bfs+ minimum spanning tree) (problem solving report)
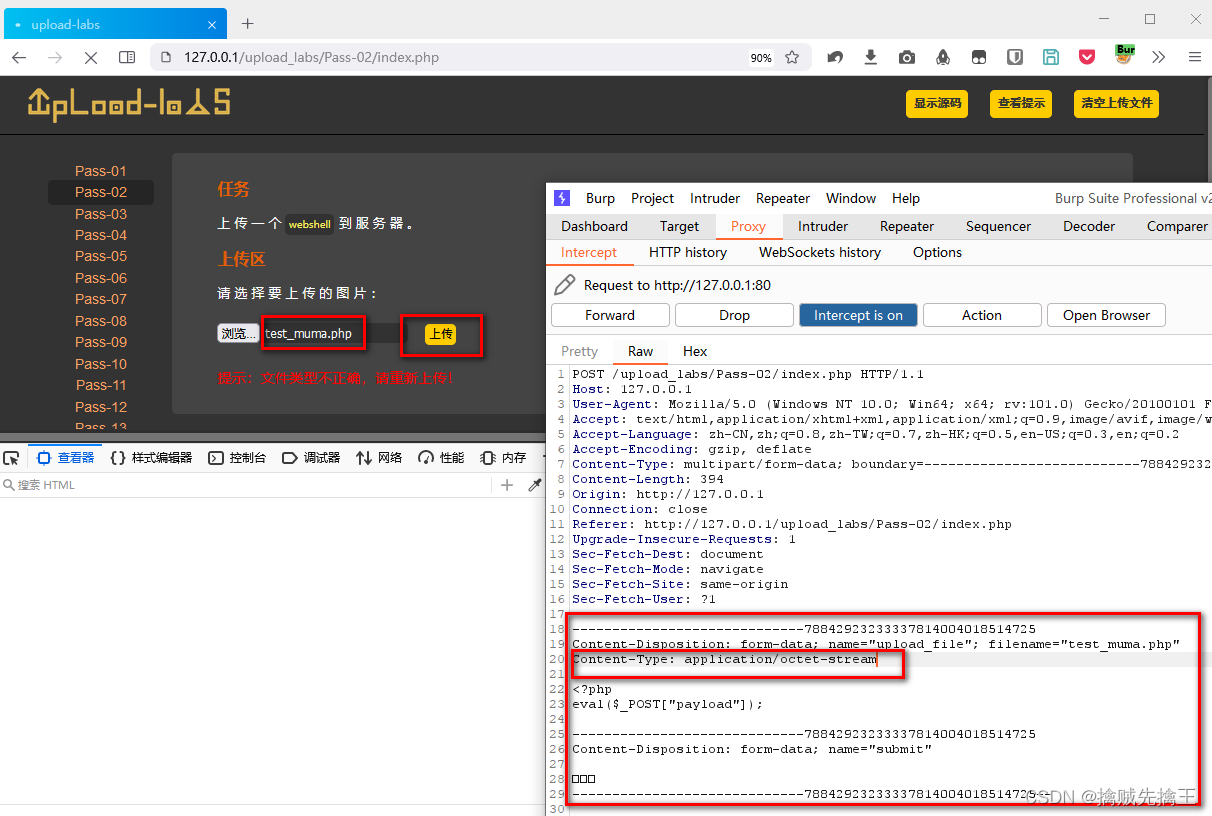
Penetration test 2 --- XSS, CSRF, file upload, file inclusion, deserialization vulnerability
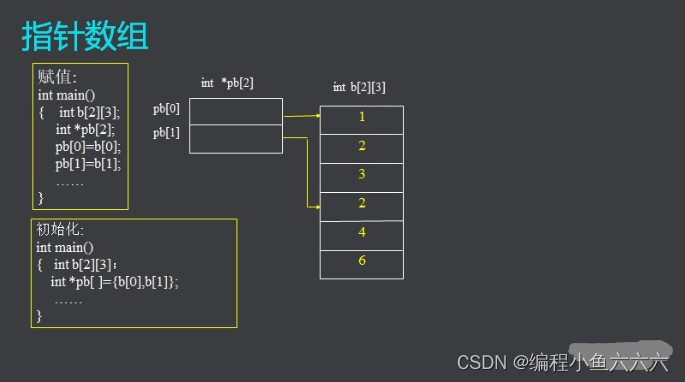
C language learning notes
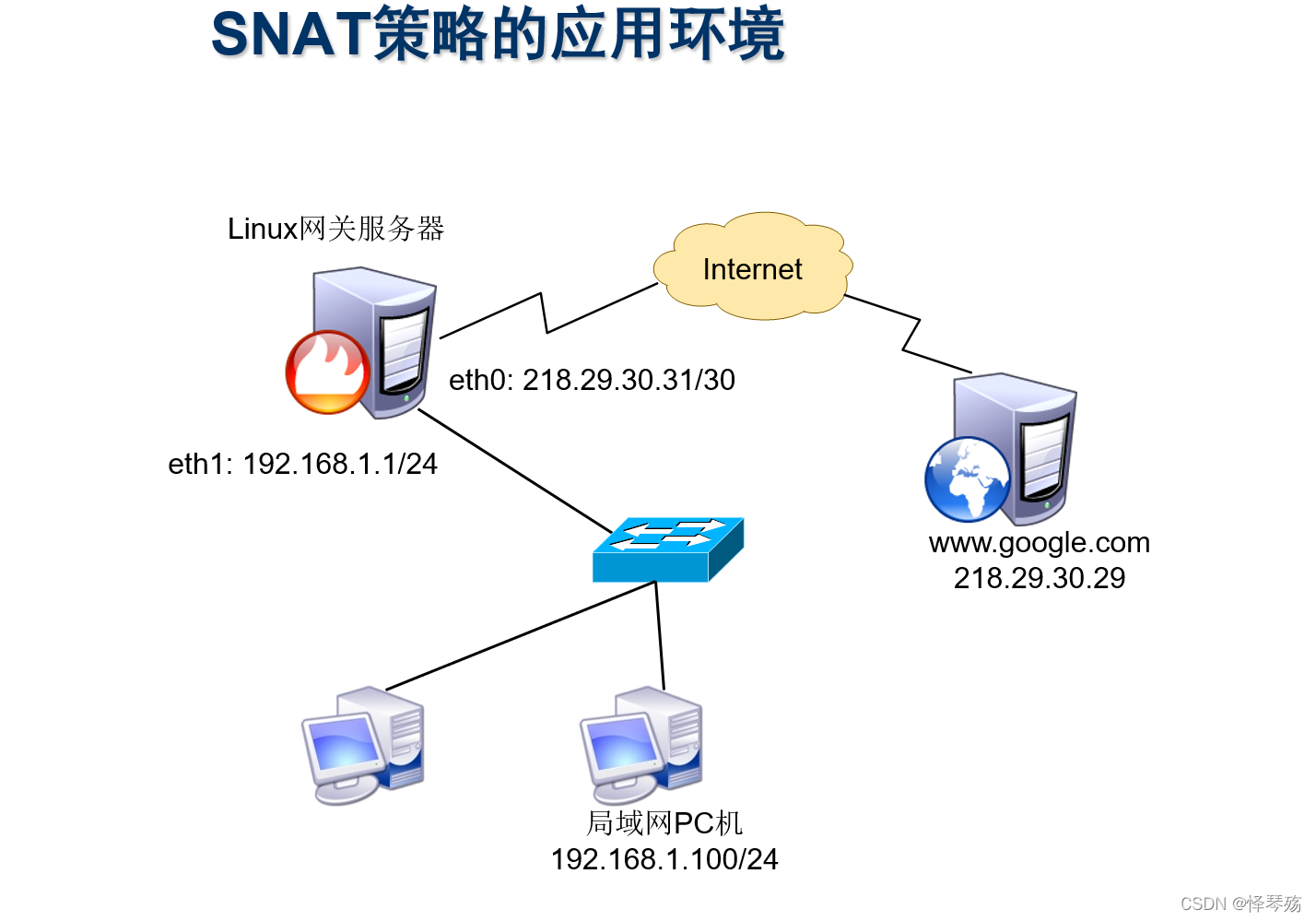
Information security - threat detection - detailed design of NAT log access threat detection platform

C language must memorize code Encyclopedia
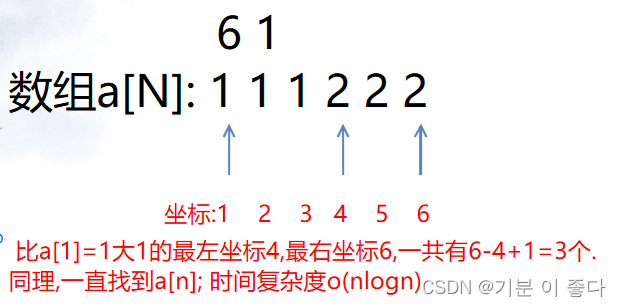
Luogu P1102 A-B number pair (dichotomy, map, double pointer)
Information security - threat detection engine - common rule engine base performance comparison
随机推荐
[exercise-1] (UVA 673) parentheses balance/ balanced brackets (stack)
D - function (HDU - 6546) girls' competition
【练习-3】(Uva 442)Matrix Chain Multiplication(矩阵链乘)
【练习-11】4 Values whose Sum is 0(和为0的4个值)
HDU - 6024 building shops (girls' competition)
Programmers, what are your skills in code writing?
【高老师软件需求分析】20级云班课习题答案合集
渗透测试 ( 3 ) --- Metasploit Framework ( MSF )
信息安全-安全编排自动化与响应 (SOAR) 技术解析
Penetration test 2 --- XSS, CSRF, file upload, file inclusion, deserialization vulnerability
China potato slicer market trend report, technical dynamic innovation and market forecast
1323. Maximum number of 6 and 9
Data storage in memory & loading into memory to make the program run
B - 代码派对(女生赛)
frida hook so层、protobuf 数据解析
CEP used by Flink
JS调用摄像头
信息安全-威胁检测引擎-常见规则引擎底座性能比较
【练习-5】(Uva 839)Not so Mobile(天平)
What is the difficulty of programming?