当前位置:网站首页>Openwrt source code generation image
Openwrt source code generation image
2022-07-06 16:07:00 【mrbone9】
The code download :
![]()
Update the latest package definition :
![]()
Install all packages :
![]()
Generate default profile :
![]()
![]()
Configure the system :
![]()
1. Target platform x86
![]()
2. install LuCI Tools
![]()

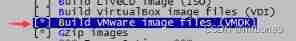
3. Compile the generated VM Usable .vmdk Image file
![]()
Compile code :
![]()
V=s Show the compilation process ,-j2 Compile with two threads , Speed up
Here I have changed it into Ubuntu20, Because of other projects
The final stage of compilation generates image An error occurred when , As before , To generate VM Finally, you need to use tools to convert the image of
The default time used here qemu-img To complete , But Ubuntu 20 It's a little different , Different from an earlier version
sudo apt-get install qemu Can be installed qemu All the relevant software , Cut into several packages for installation (mips For example ):
1. System level virtual machine ,sudo apt-get install qemu-system-mips
2. Process level virtual machine ,sudo apt-get install qemu-user
3. Tools , such as qemu-img,sudo apt-get install qemu-utils
Current error reporting :

therefore , We need to install :
![]()
![]()
Finally, generate the image file you need :
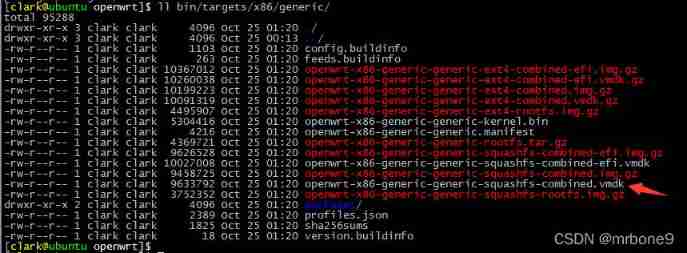
Subsequent operation in VM See Openwrt Image mount
边栏推荐
- Nodejs+vue网上鲜花店销售信息系统express+mysql
- [exercise -11] 4 values why sum is 0 (and 4 values of 0)
- Understand what is a programming language in a popular way
- Research Report on surgical fluid treatment industry - market status analysis and development prospect prediction
- Web based photo digital printing website
- Opencv learning log 14 - count the number of coins in the picture (regardless of overlap)
- CEP used by Flink
- 渗透测试 ( 8 ) --- Burp Suite Pro 官方文档
- 【高老师软件需求分析】20级云班课习题答案合集
- Essai de pénétration (1) - - outils nécessaires, navigation
猜你喜欢
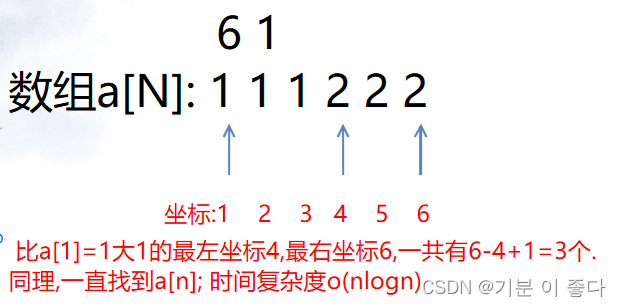
Luogu P1102 A-B number pair (dichotomy, map, double pointer)

Optimization method of path problem before dynamic planning
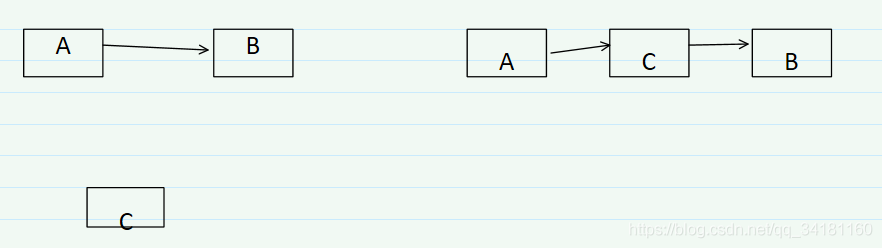
【练习-4】(Uva 11988)Broken Keyboard(破损的键盘) ==(链表)

Vs2019 initial use
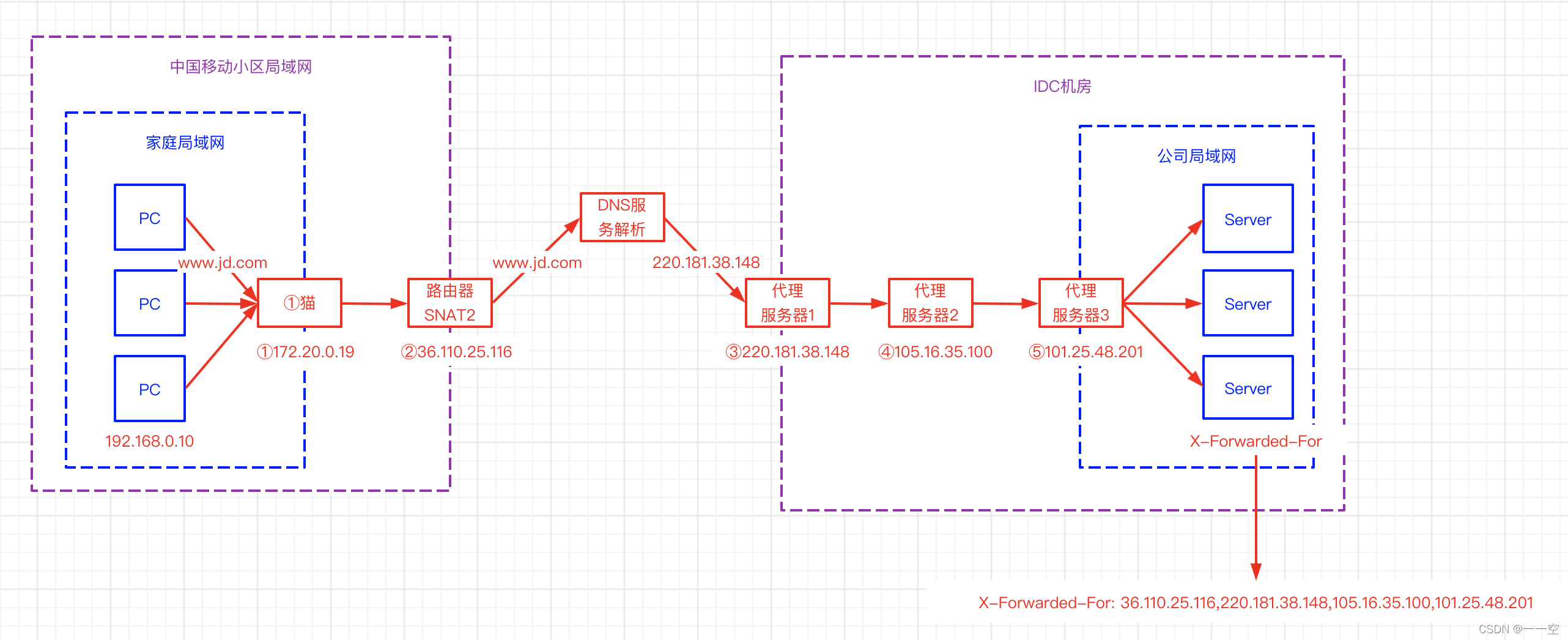
X-Forwarded-For详解、如何获取到客户端IP
Frida hook so layer, protobuf data analysis
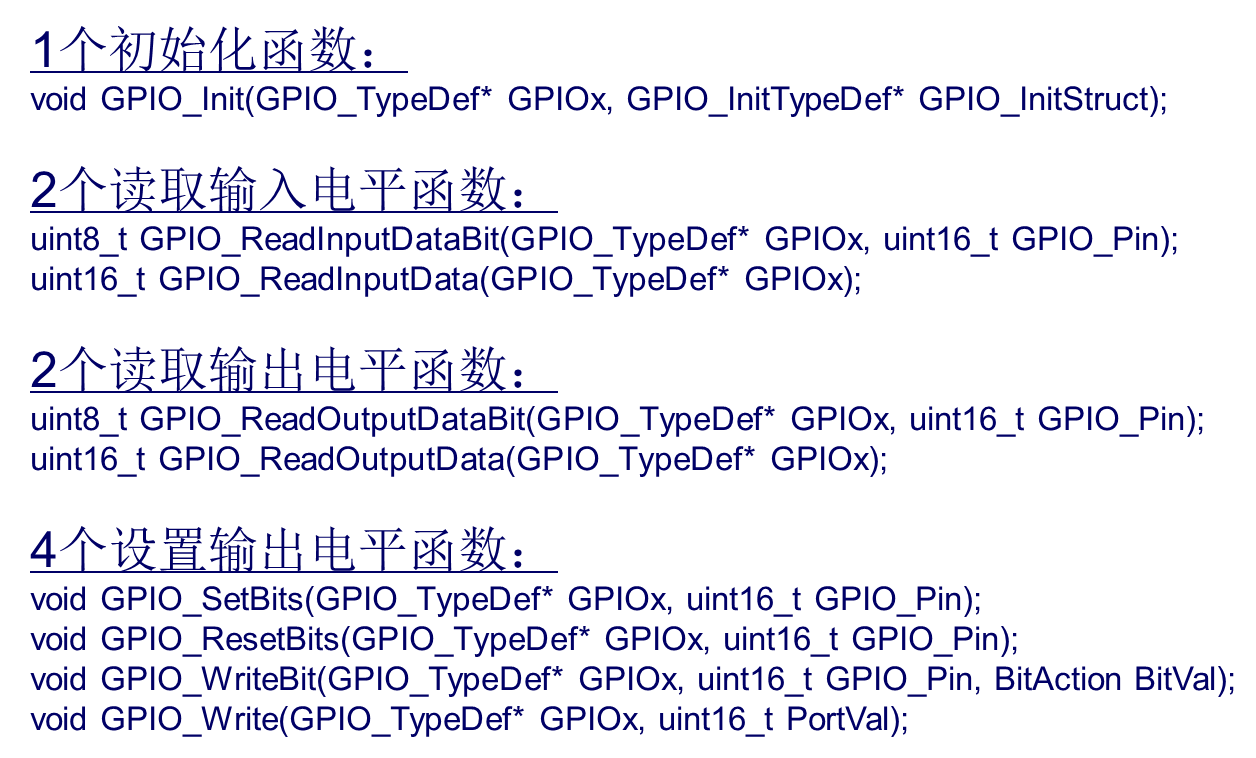
STM32 how to use stlink download program: light LED running light (Library version)

Web based photo digital printing website
渗透测试 ( 8 ) --- Burp Suite Pro 官方文档
7-1 懂的都懂 (20 分)
随机推荐
CEP used by Flink
【练习-11】4 Values whose Sum is 0(和为0的4个值)
[teacher Gao UML software modeling foundation] collection of exercises and answers for level 20 cloud class
C language learning notes
[exercise-3] (UVA 442) matrix chain multiplication
Record of brushing questions with force deduction -- complete knapsack problem (I)
【高老师软件需求分析】20级云班课习题答案合集
渗透测试 ( 5 ) --- 扫描之王 nmap、渗透测试工具实战技巧合集
Luogu P1102 A-B number pair (dichotomy, map, double pointer)
信息安全-安全编排自动化与响应 (SOAR) 技术解析
E. Breaking the Wall
PySide6 信号、槽
Gartner:关于零信任网络访问最佳实践的五个建议
【练习-7】(Uva 10976)Fractions Again?!(分数拆分)
Programmers, what are your skills in code writing?
Raspberry pie csi/usb camera uses mjpg to realize web camera monitoring
Penetration test (3) -- Metasploit framework (MSF)
【练习-4】(Uva 11988)Broken Keyboard(破损的键盘) ==(链表)
[exercise-7] crossover answers
[exercise -10] unread messages