边栏推荐
- Pat 1046 shortest distance (20 points) simulation
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 12
- JS regular filtering and adding image prefixes in rich text
- Classic interview question [gem pirate]
- 微服务间通信
- Installation and use tutorial of cobaltstrike-4.4-k8 modified version
- Solution: attributeerror: 'STR' object has no attribute 'decode‘
- Linear programming matlab
- 07 singleton mode
- Detailed use of dbutils # yyds dry goods inventory #
猜你喜欢
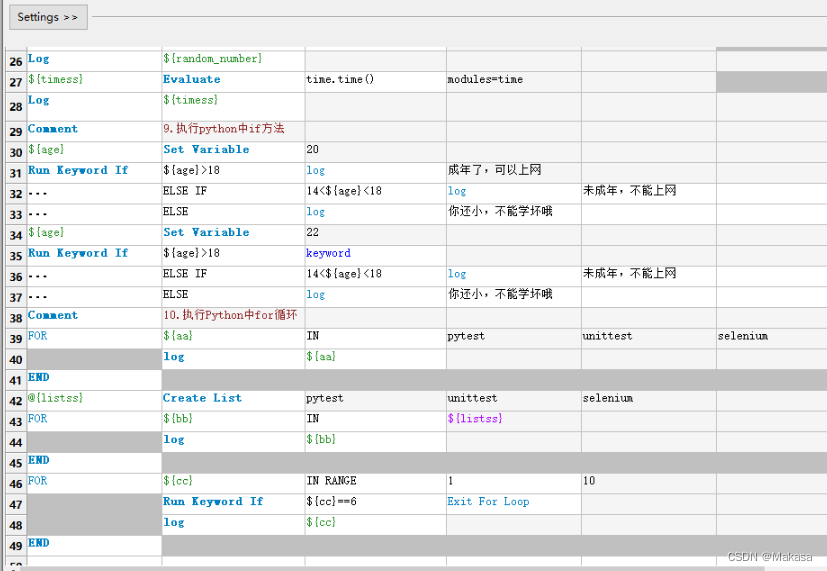
Introduction to robotframework (I) brief introduction and use
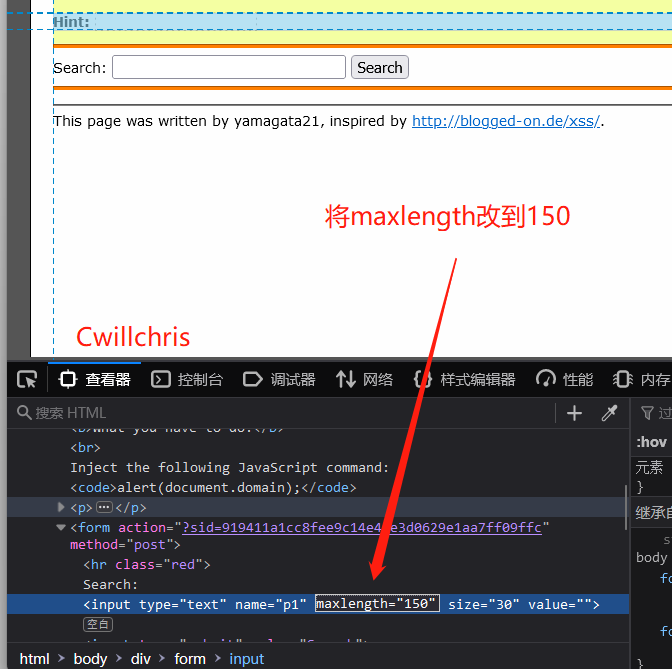
XSS challenges bypass the protection strategy for XSS injection
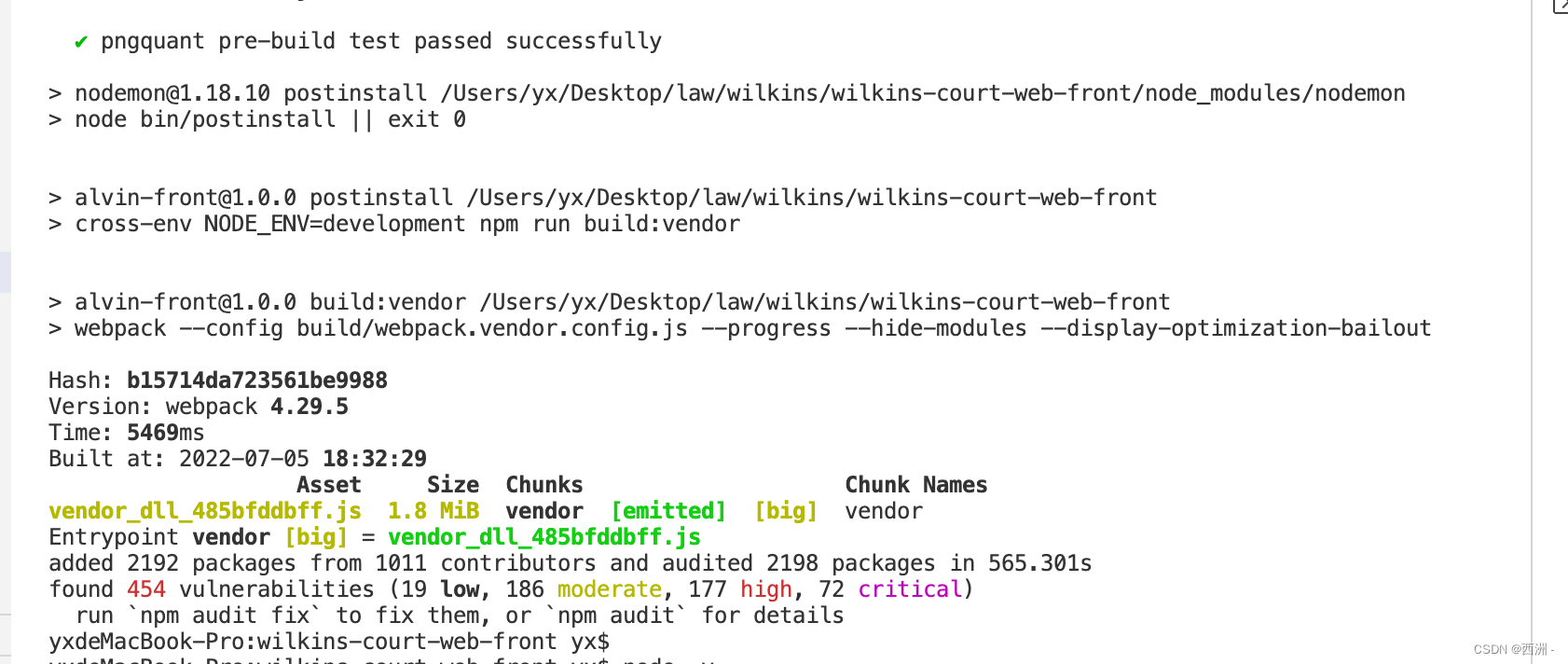
Referenceerror: primordials is not defined error resolution
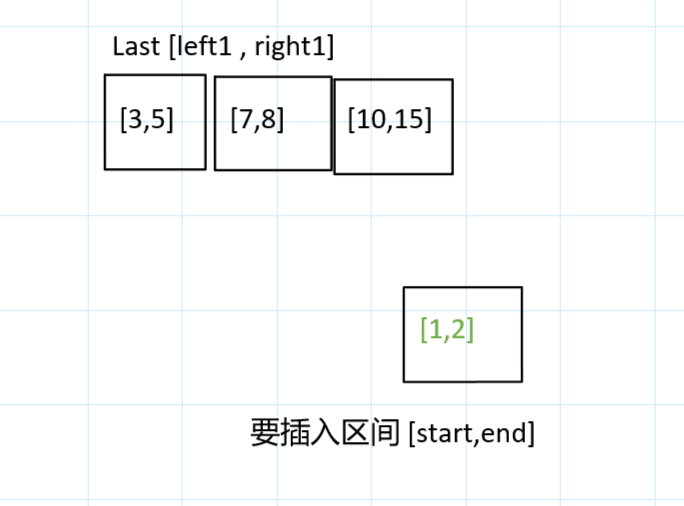
Déduisez la question d'aujourd'hui - 729. Mon emploi du temps I
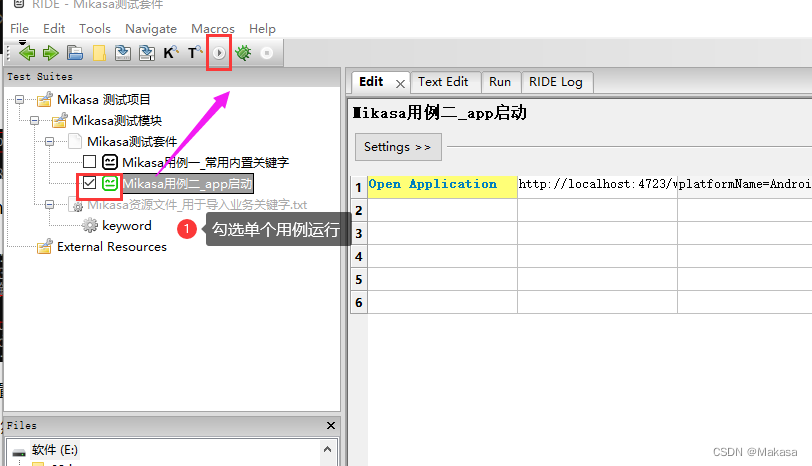
Introduction to robotframework (II) app startup of appui automation
![[kubernetes series] learn the exposed application of kubernetes service security](/img/61/4564230feeb988886fe595e3125ef4.png)
[kubernetes series] learn the exposed application of kubernetes service security

PMP每日一练 | 考试不迷路-7.5
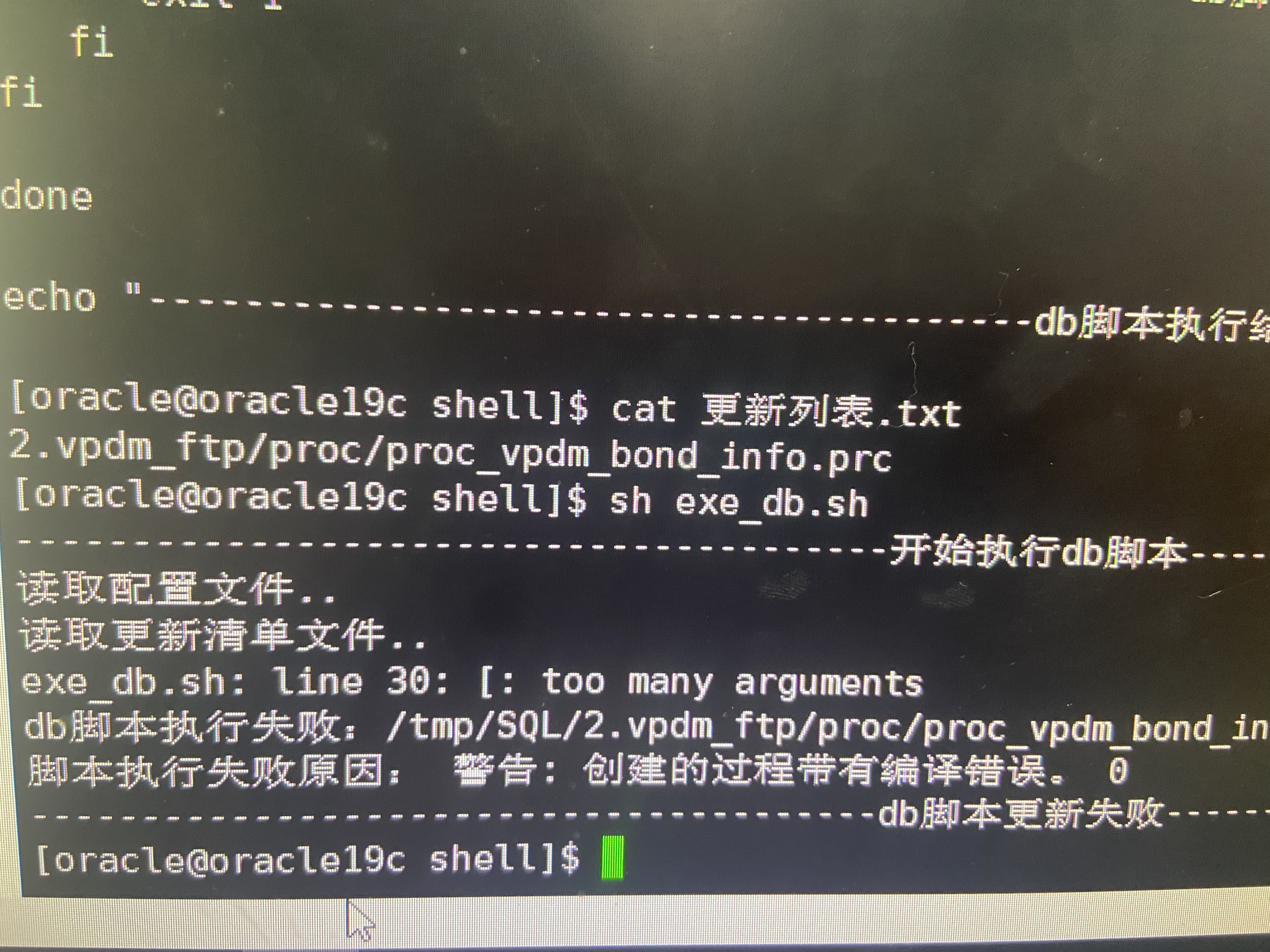
Shell script updates stored procedure to database
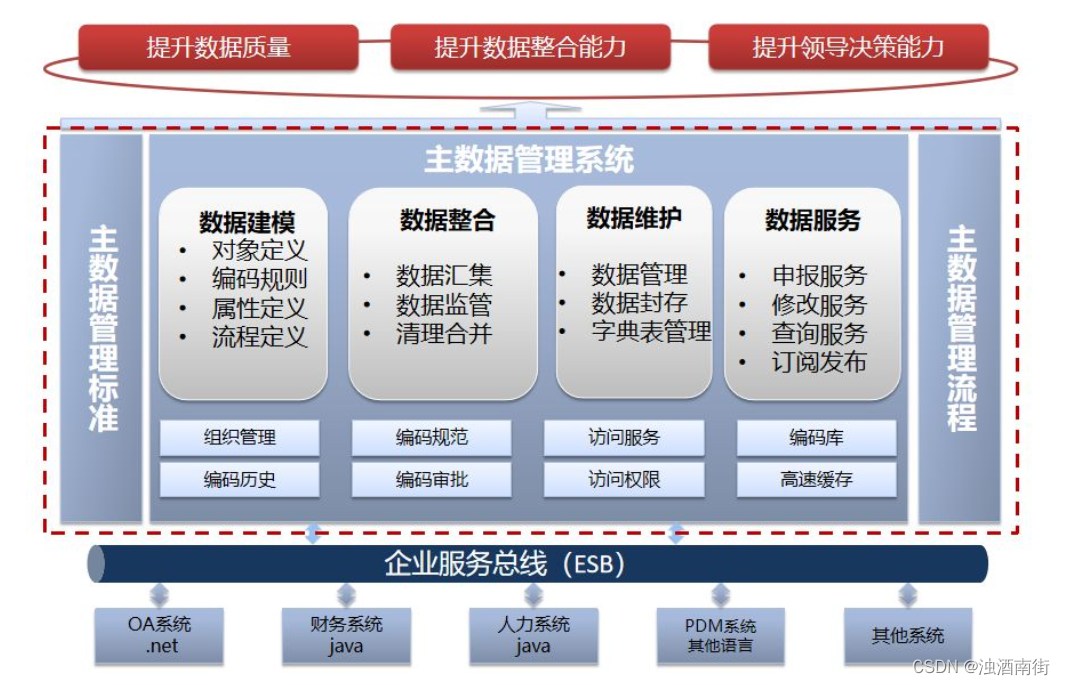
Master data management theory and Practice
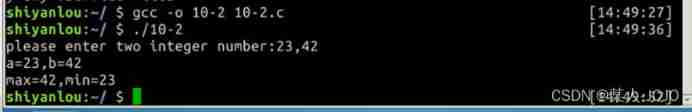
My C language learning record (blue bridge) -- on the pointer
随机推荐
"Hands on learning in depth" Chapter 2 - preparatory knowledge_ 2.3 linear algebra_ Learning thinking and exercise answers
Fault analysis | analysis of an example of MySQL running out of host memory
Jenkins basic knowledge ----- detailed explanation of 03pipeline code
MySQL learning notes-10-tablespace recycling
Shell script updates stored procedure to database
Technology sharing | what if Undo is too big
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 12
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 15
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 9
Yyds dry inventory comparison of several database storage engines
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 23
Qt发布exe软件及修改exe应用程序图标
Referenceerror: primordials is not defined error resolution
Apt installation ZABBIX
Redis cluster deployment based on redis5
Briefly describe the implementation principle of redis cluster
A copy can also produce flowers
Modeling specifications: naming conventions
[Chongqing Guangdong education] higher mathematics I reference materials of Southwest Petroleum University
解决:AttributeError: ‘str‘ object has no attribute ‘decode‘