当前位置:网站首页>South China x99 platform chicken blood tutorial
South China x99 platform chicken blood tutorial
2022-07-07 21:27:00 【Ape growth】
Chicken blood drive only supports E5-26xxV3 E5-26xxV4 E5-46xxV3 E5-46xxV4 The official version of the processor !
Don't use beta (ES) It may not light normally !
Go to Taobao customer service in South China to get the chicken blood of your own model motherboard bios And the original bios
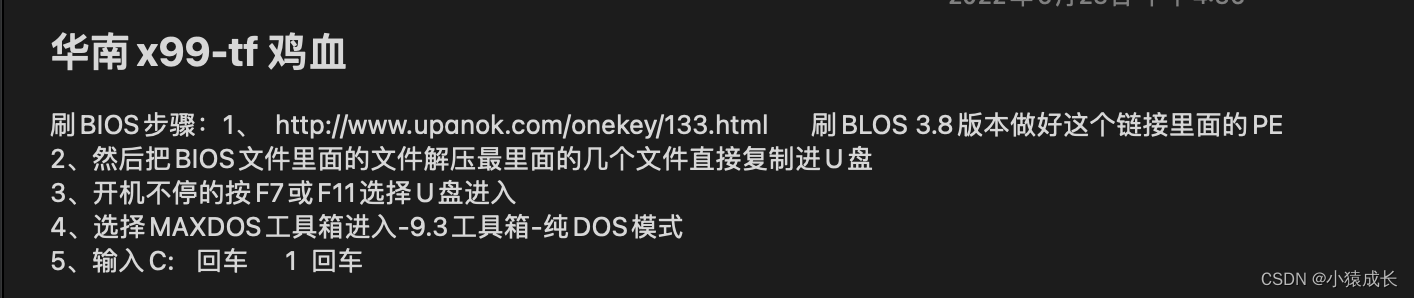
My model is X99-TF
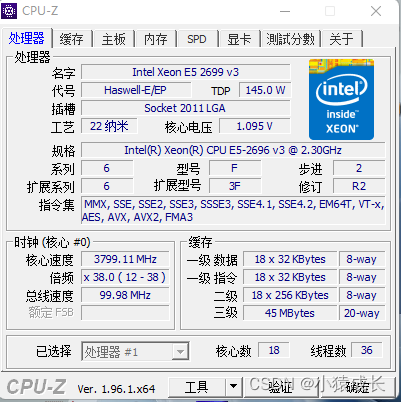
Details of computer hardware are as follows :

The chicken blood process can be referred to as follows :
After chicken blood cpu-z:
边栏推荐
- UVA 11080 – place the guards
- Validutil, "Rethinking the setting of semi supervised learning on graphs"
- What are the official stock trading apps in the country? Is it safe to use
- Implementation of mahout Pearson correlation
- 反诈困境,国有大行如何破局?
- JNI primary contact
- Devil daddy A0 English zero foundation self-improvement Road
- [UVALive 6663 Count the Regions] (dfs + 离散化)[通俗易懂]
- Deployment, recall and deletion solutions - stsadm and PowerShell "suggestions collection"
- 部署、收回和删除解决方式—-STSADM和PowerShell「建议收藏」
猜你喜欢
The new version of onespin 360 DV has been released, refreshing the experience of FPGA formal verification function
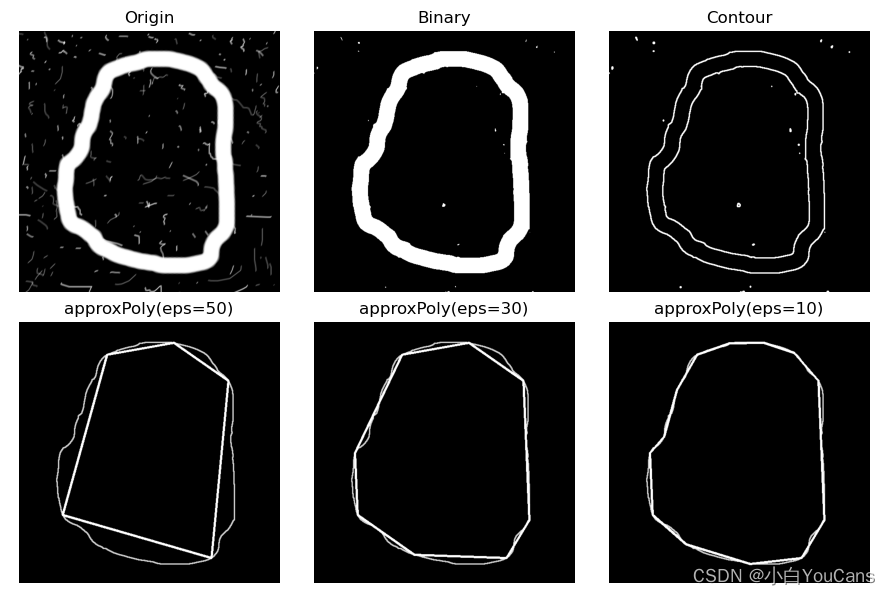
【OpenCV 例程200篇】223. 特征提取之多边形拟合(cv.approxPolyDP)
Codesonar Webinar
SQL注入报错注入函数图文详解
![Is embedded system really safe? [how does onespin comprehensively solve the IC integrity problem for the development team]](/img/af/61b384b1b6ba46aa1a6011f8a30085.png)
Is embedded system really safe? [how does onespin comprehensively solve the IC integrity problem for the development team]
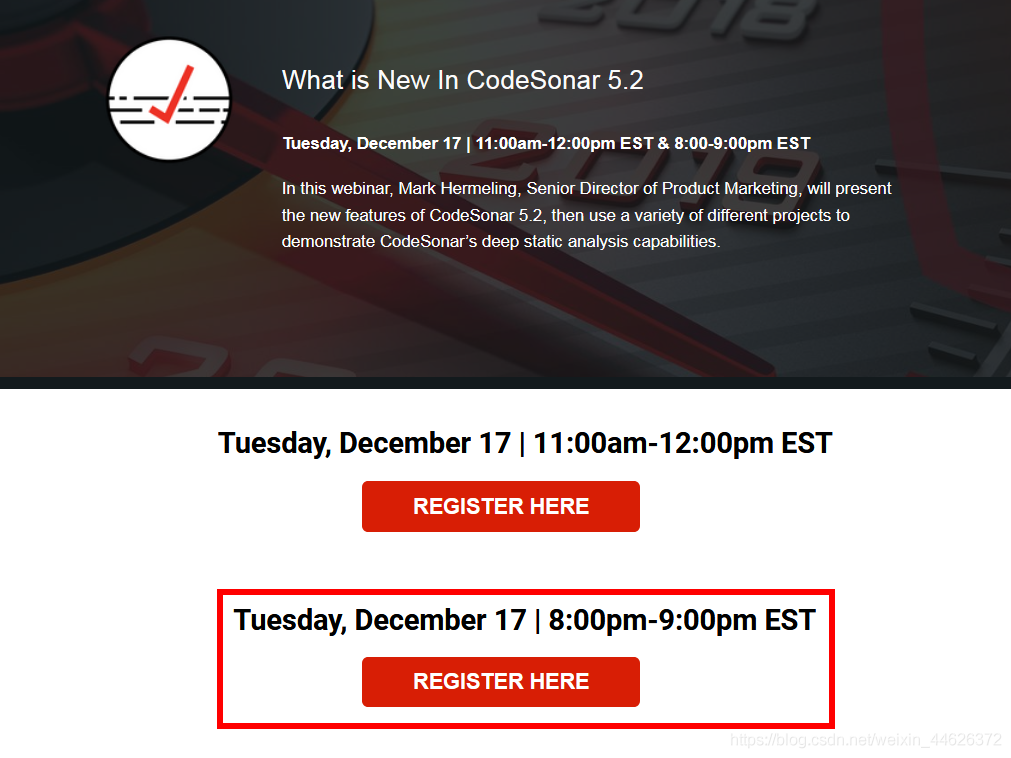
Static analysis of software defects codesonar 5.2 release

Helix QAC 2020.2 new static test tool maximizes the coverage of standard compliance

Magic weapon - sensitive file discovery tool
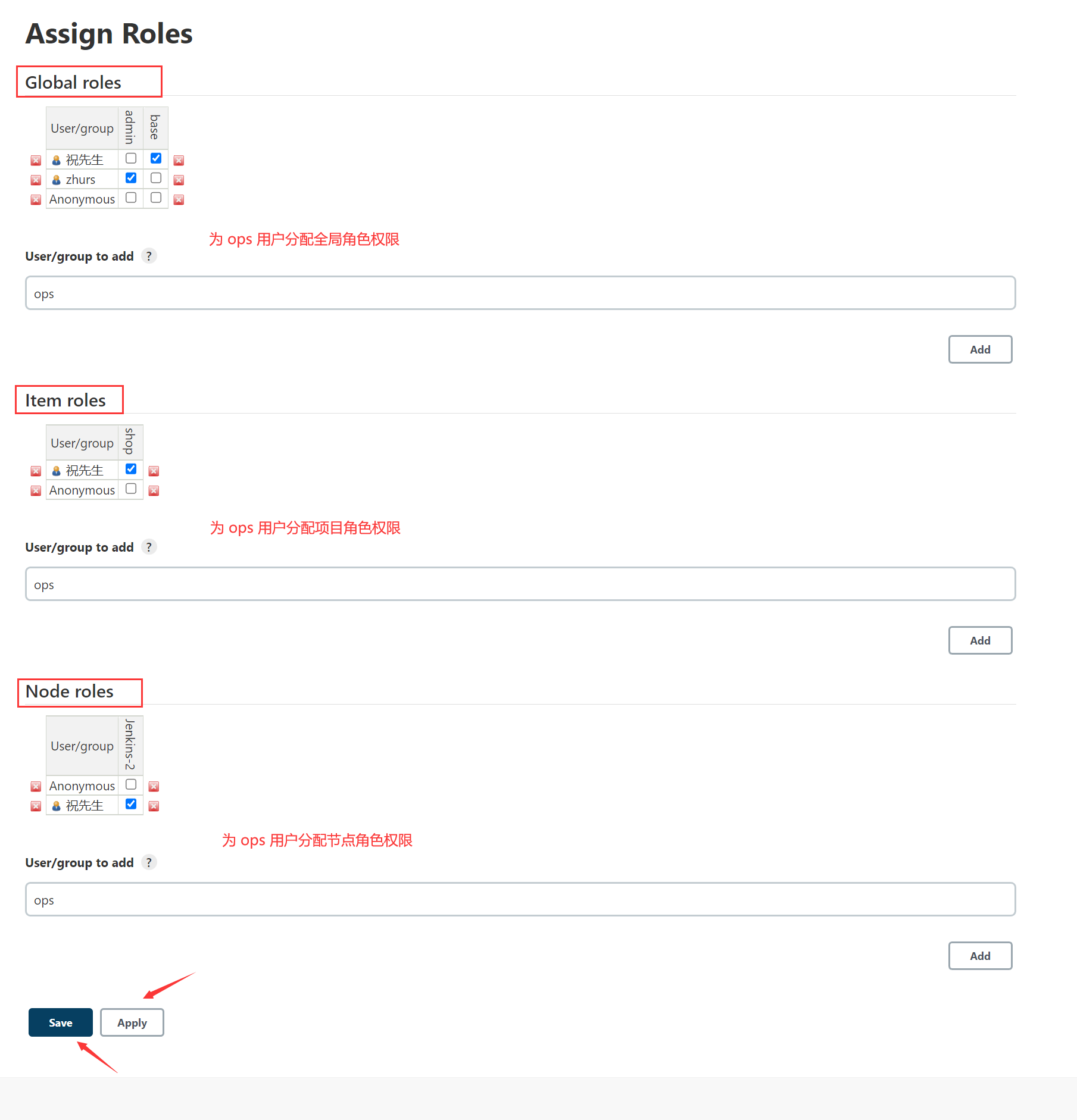
Jenkins user rights management
Demon daddy B3 read extensively in a small amount, and completed 20000 vocabulary+
随机推荐
POJ 3140 Contestants Division「建议收藏」
Details of C language integer and floating-point data storage in memory (including details of original code, inverse code, complement, size end storage, etc.)
Take the intersection of two sets
私募基金在中國合法嗎?安全嗎?
openGl超级宝典学习笔记 (1)第一个三角形「建议收藏」
Klocwork code static analysis tool
Actual combat: sqlserver 2008 Extended event XML is converted to standard table format [easy to understand]
死锁的产生条件和预防处理[通俗易懂]
Mysql子查询关键字的使用方式(exists)
Develop those things: go plus c.free to free memory, and what are the reasons for compilation errors?
Unity3d 4.3.4f1执行项目
Codeforces Round #275 (Div. 2) C – Diverse Permutation (构造)[通俗易懂]
[function recursion] do you know all five classic examples of simple recursion?
Jetty: configure connector [easy to understand]
恶魔奶爸 A1 语音听力初挑战
MySQL storage expression error
SQL injection error report injection function graphic explanation
MySQL约束之默认约束default与零填充约束zerofill
Virtual machine network configuration in VMWare
How much does it cost to develop a small program mall?