当前位置:网站首页>Network Security Learning - Information Collection
Network Security Learning - Information Collection
2022-07-07 04:23:00 【haoaaao】
/**cdn Bypass 7. information gathering ——CDN Bypass technology · Language sparrow
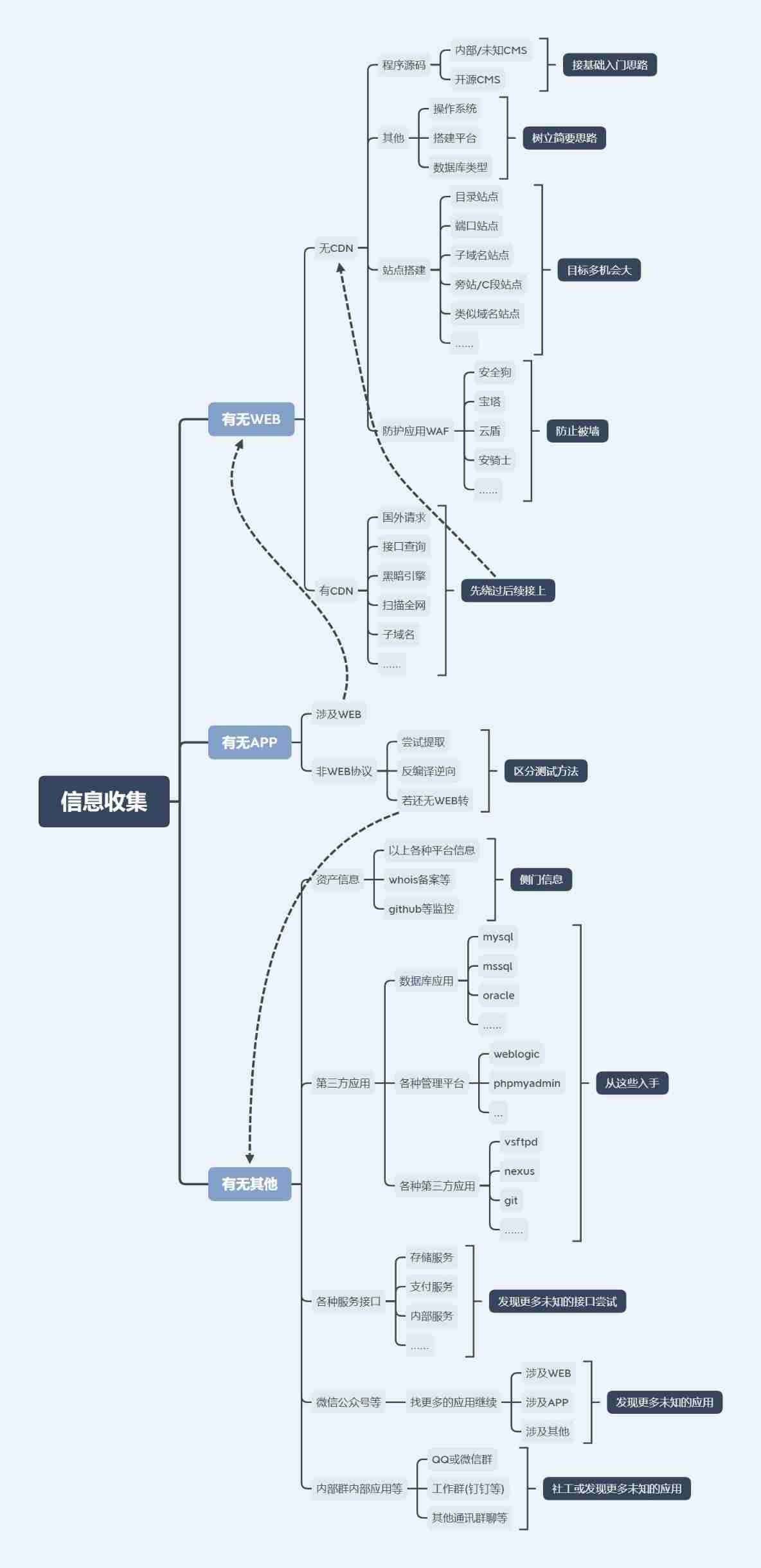
One 、 framework 、 build 、waf
1、 Site construction type :
(1) Directory site construction :
Same website , But in different directories , Building source code is also different , But a problem with one website will affect the other website .
Such as

Probe : Yujian and other directory scanning tools can find
(2) Port class site
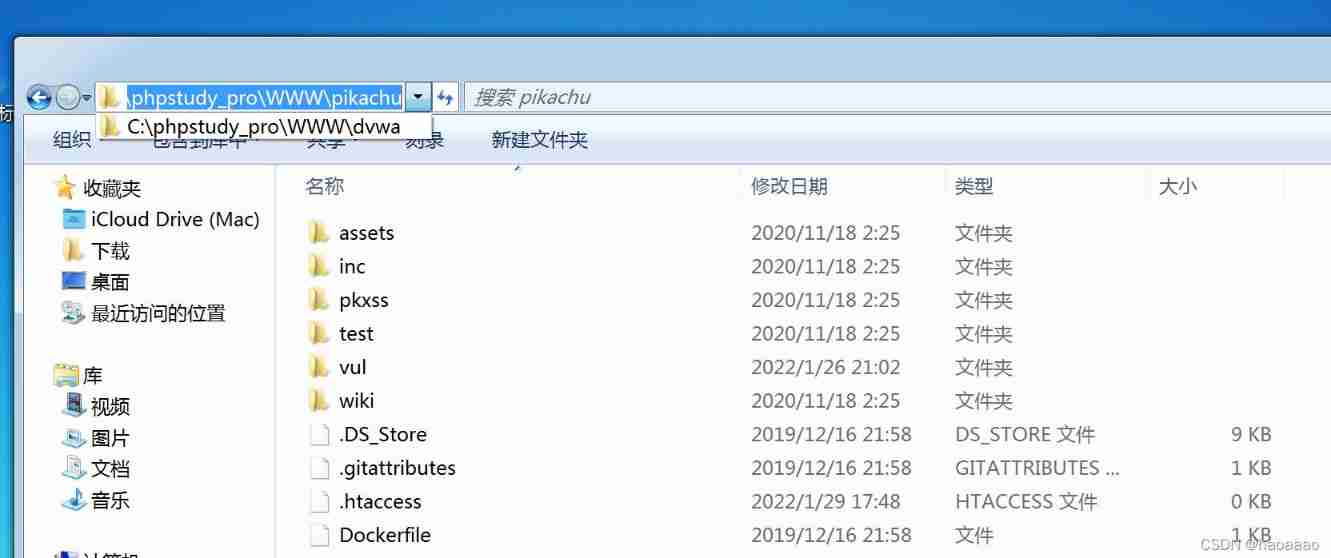
The website is located on the same server , But ports are different , For example, those target aircrafts built in practice ,dvwa yes 8023 port ,pikachu yes 8022 port
nmap Port scanning 、 Surf the Internet query
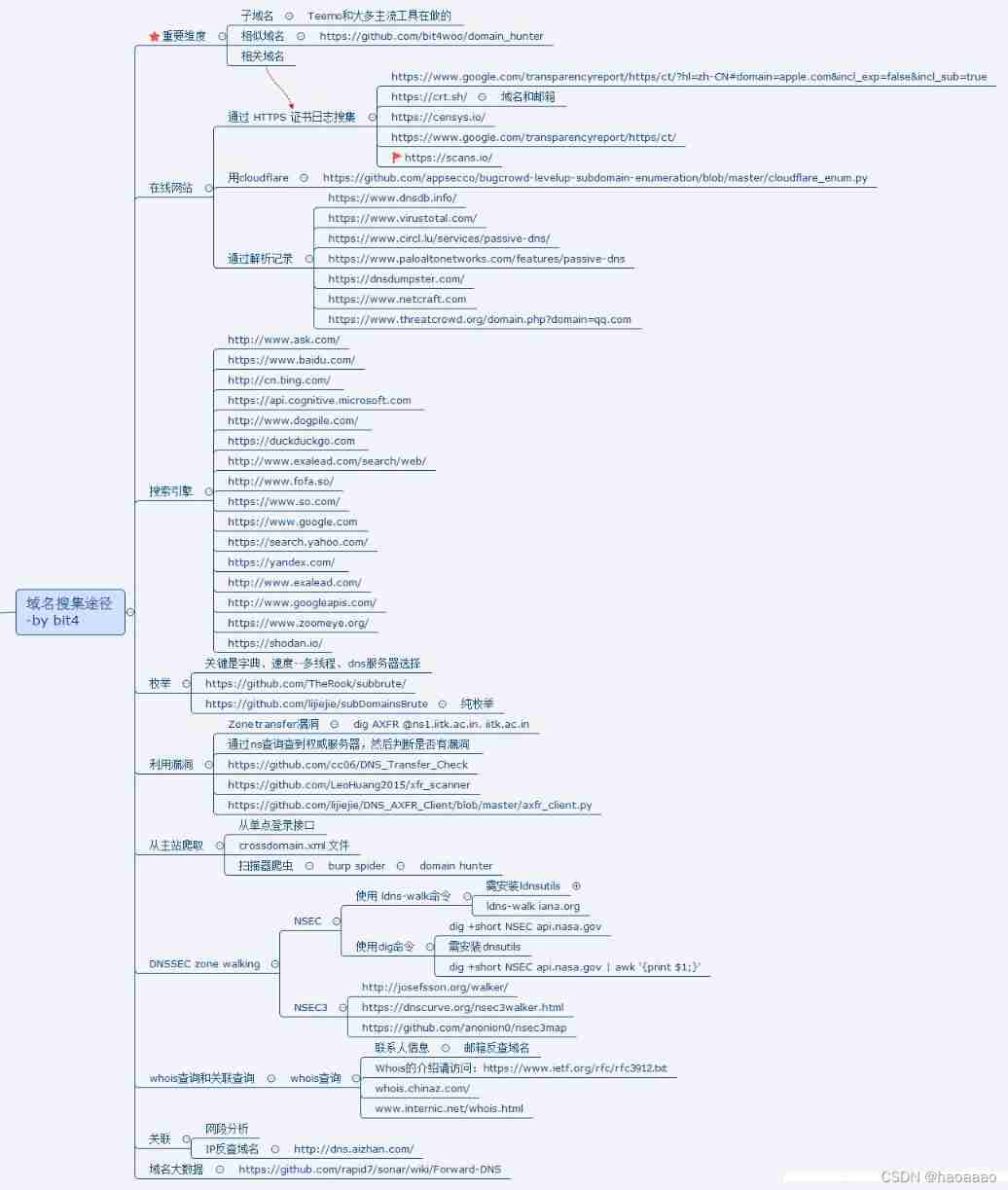
(3) Sub domain name class site
Search the subdomain name online ip,ip Different does not belong to the same server .
(4) Similar domain name sites
The domain name suffix is different , Such as .com and .cn, But from the same server or company .


(5) sidenote 、c Segment site
/** Excerpt from : 8. information gathering —— Site construction and WAF · Language sparrow **/
1) sidenote
Marginal note is an intrusion method , Literally, it means -" Inject... From the side ", Exploit the vulnerabilities of different websites on the same host to get webshell, Thus, the physical path of the user exposed by the program or service on the host can be used for intrusion . Different sites on the same server . Two or more websites are placed on the same server , One of the websites is the target .
Implementable premise :
There are multiple site servers ;
www.a.com( The goal is )
www.b.com
........
Stand alone site server
2)c paragraph
Different servers and different sites in the same network segment . The website has one or more sites , Through the server IP Address of the network segment to test .
192.168.1.1
www.a.com( The goal is )
www.b.com
........
192.168.1.101
www.a.com
www.b.com
........
By querying the network segment 1-254, To get 101 Network segment server permissions , The test method of implementing intranet security through the target host of the same network segment of the server , To obtain the permission of the specified web server .
(6) Build software
Such as phpstudy、 Pagoda and other building software ; f12 View site information , Generally, software with complete information is built , Such as : Apache/2.4.41(win32)OpenSSL/1.1.1c mod_fcgid/2.3.9a;
Similar building software usually has a default account password or security settings , Such as :/phpmyadmin Catalog
2、WAF
(1) brief introduction ( Baidu Encyclopedia )
Web Application protection system ( Also known as : Website Application level intrusion prevention system . english :Web Application Firewall, abbreviation : WAF). utilize The international A generally accepted saying :Web application A firewall It's through the execution of a series of HTTP/HTTPS Of The security policy Come for Web An application that provides protection ;
Web Application protection system (Web Application Firewall, abbreviation :WAF) It represents a new kind of information security technology , To solve the problem that traditional devices such as firewalls are helpless Web Application security issues . Unlike traditional firewalls ,WAF Working in the application layer , So right. Web Application protection has inherent technical advantages . Based on the Web Apply a deep understanding of business and logic ,WAF from Web All kinds of requests from application clients are used for content detection and verification , Ensure its security and legitimacy , Block illegal requests in real time , So as to effectively protect all kinds of websites .
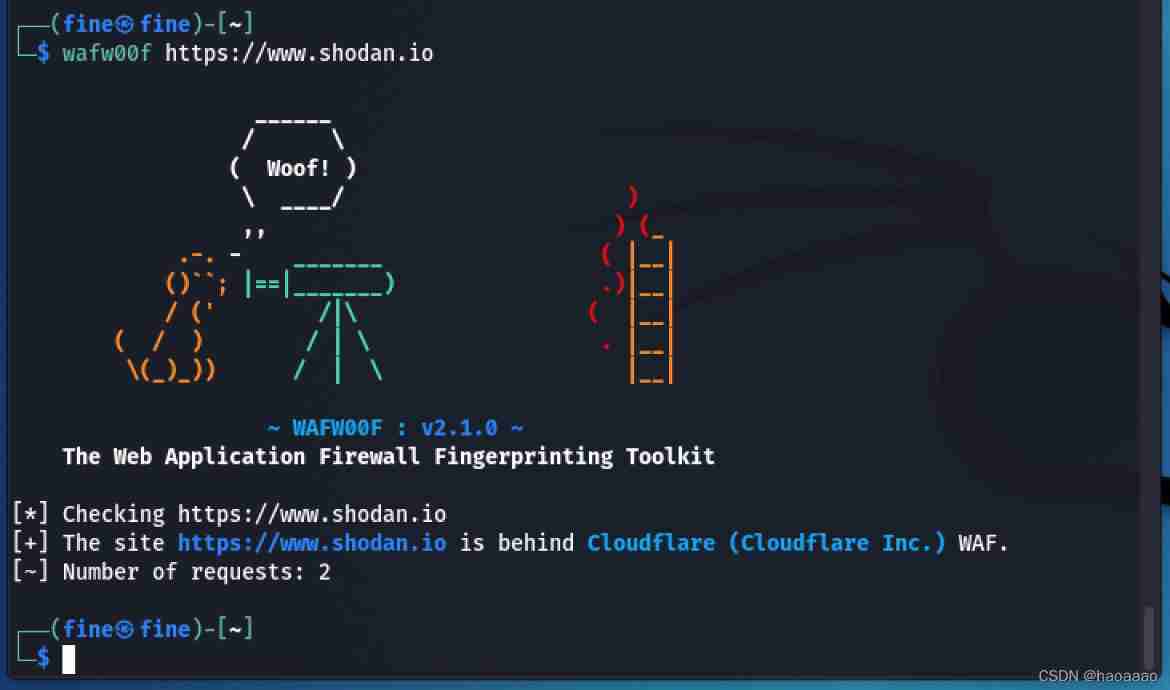
(2) How to quickly identify waf:wafw00f
1)wafw00f Download and install :
github Address :https://github.com/EnableSecurity/wafw00f
kali Bring their own wafw00f:
a、 Start command :wafw00f -l
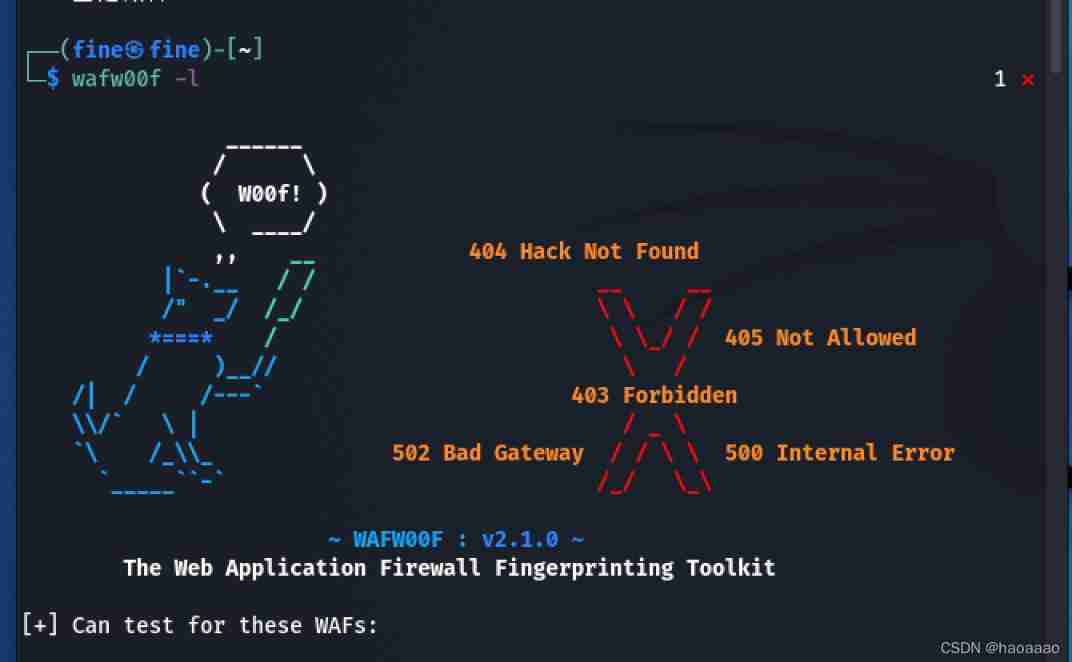
b、 Use command :wafw00f domain name /ip
2)sqlmap:
command :python sqlmap.py -u “url” --identify-waf
Two 、app And other assets
1、app Extraction, bag capturing and subsequent cooperation
(1) some apk One click extraction decompilation
A big hole is missing for installation and use :
(2) Use burp History catches more url
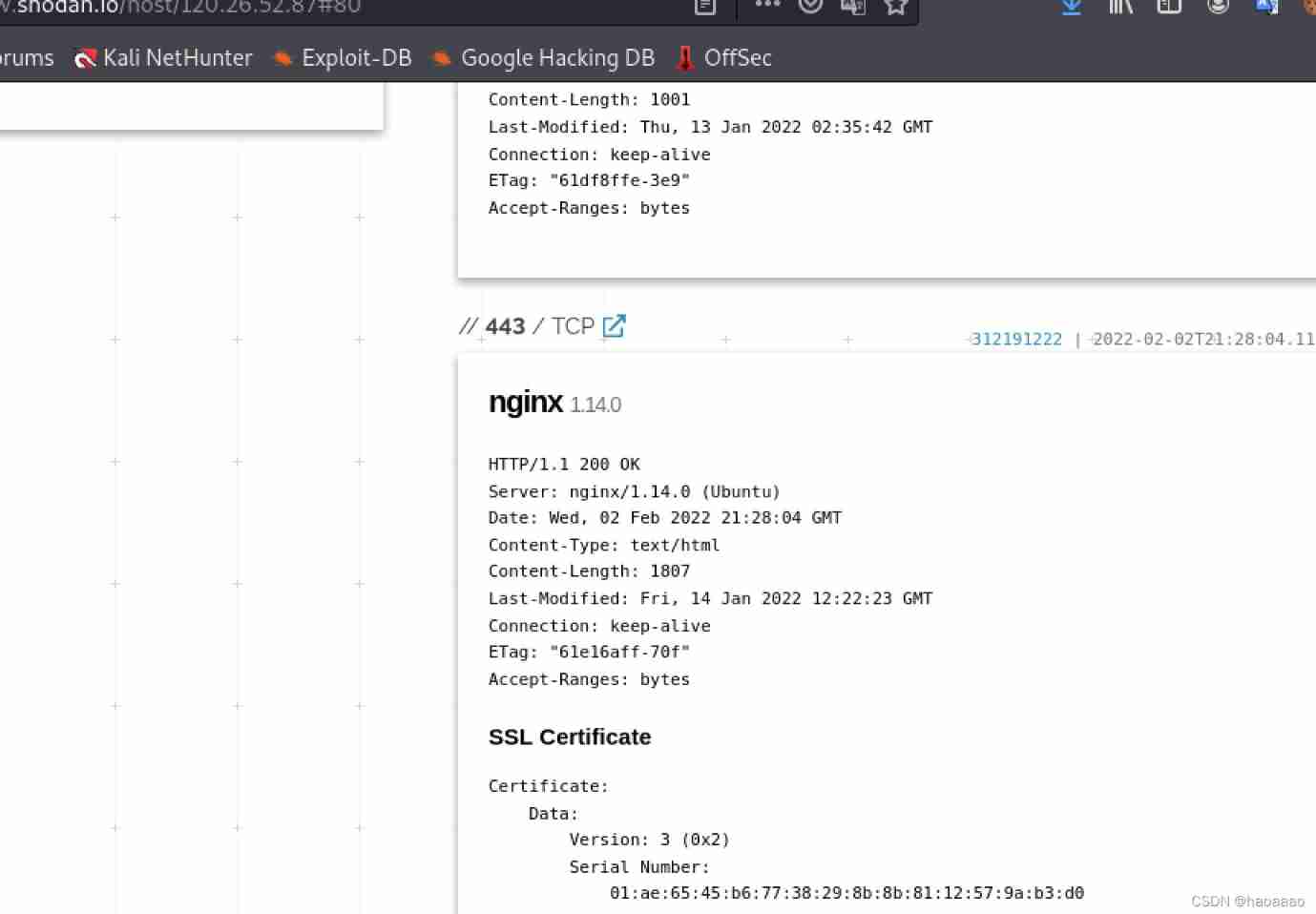
2、 some ip nothing web Third party testing ideas under the framework
(1) Random scanning of various ports
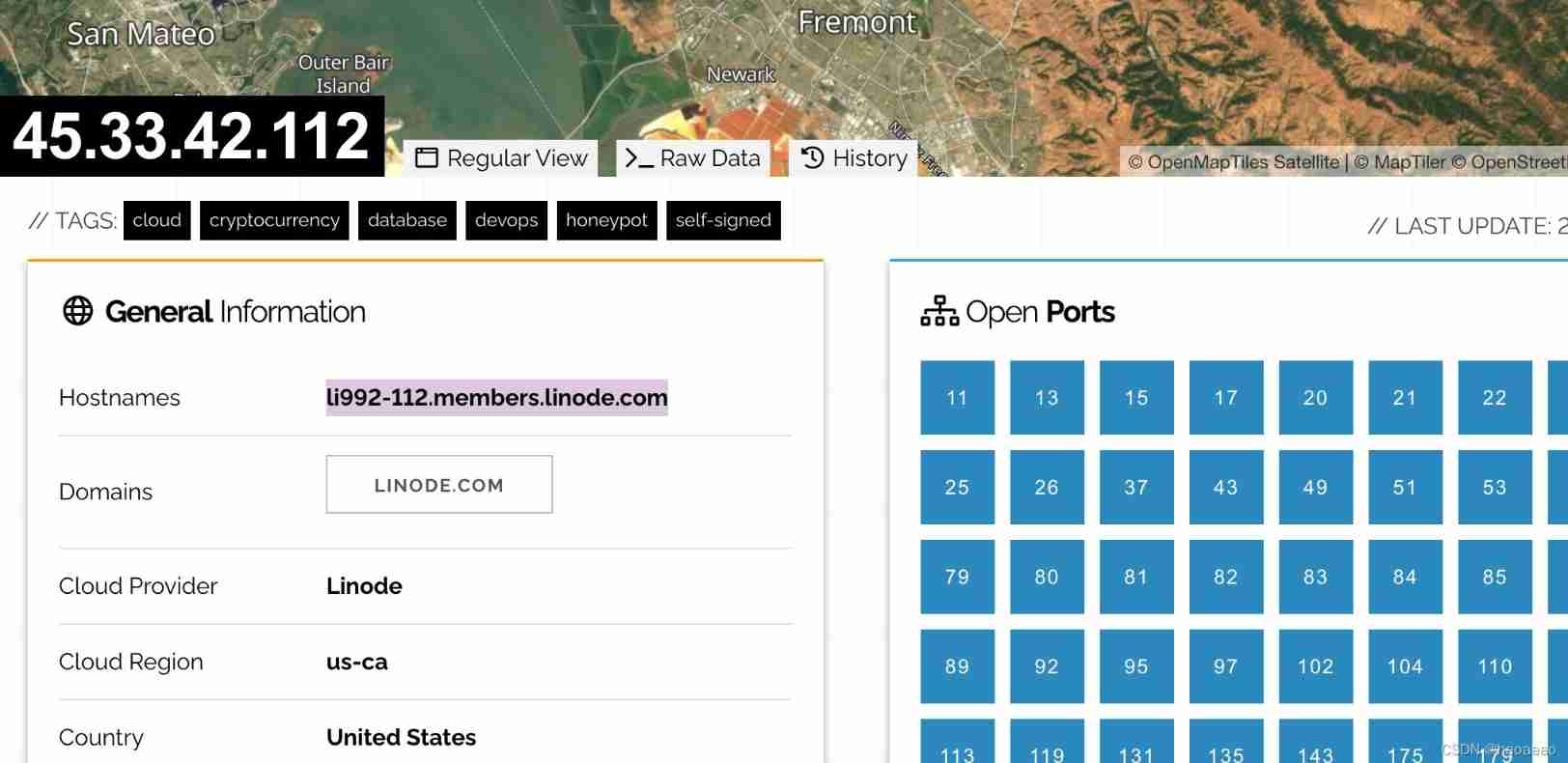
nmap、 Search engine (shodan、 Zhong Kui's eyes 、fofa.info etc. )
/** Friends, yuan fofa By b Station a live broadcast to * standing , Leading to fofa It was hacked by the Ministry of industry and information technology and can't be used ***/
eg:
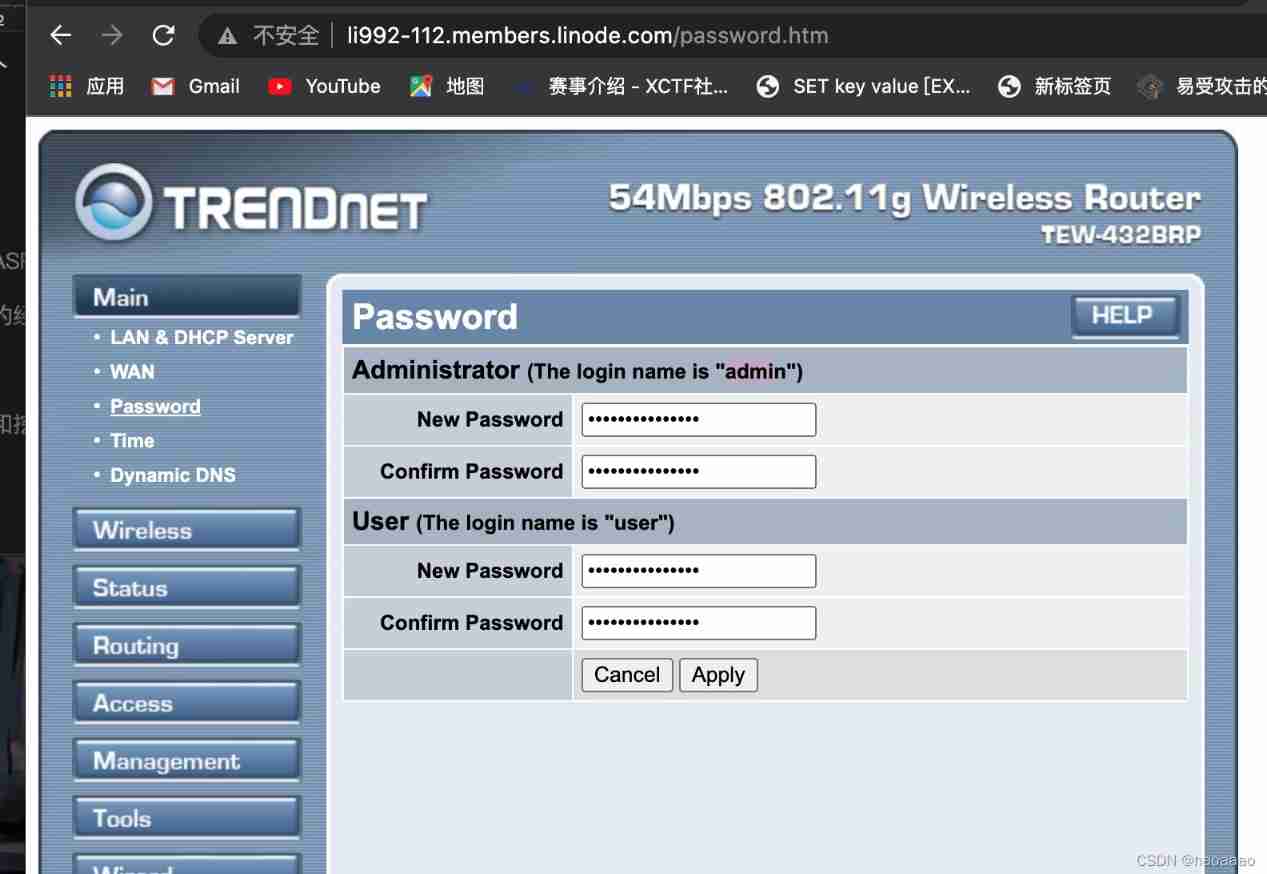
(2) Various interfaces are scanned randomly
(3) Various interface tests
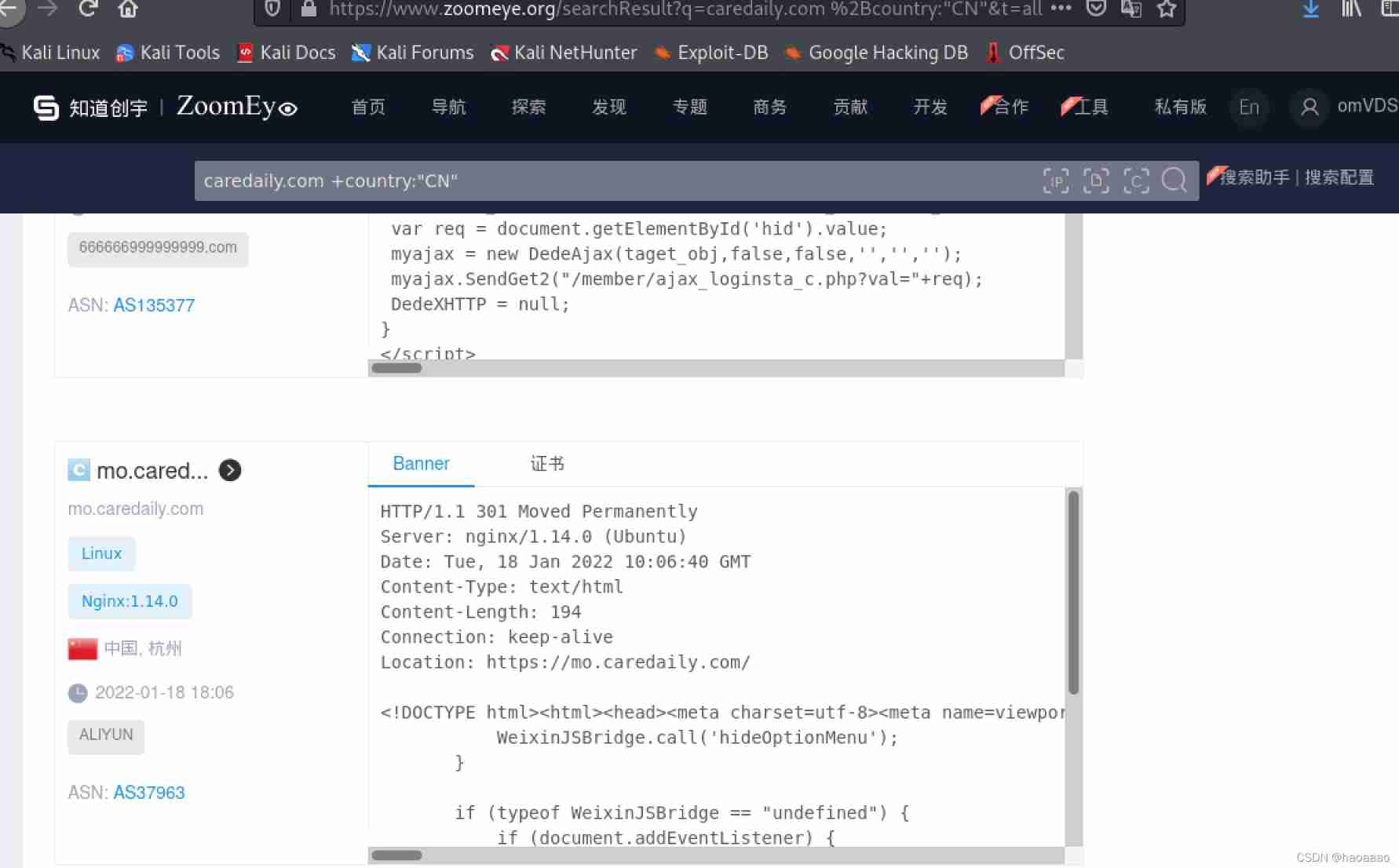
3、 example ( A pyramid selling website )
(1) Check out the website
(2) Collect all kinds of information :
1) Search domain name , Check various ports
Find login port

2)ping The website finds the truth ip
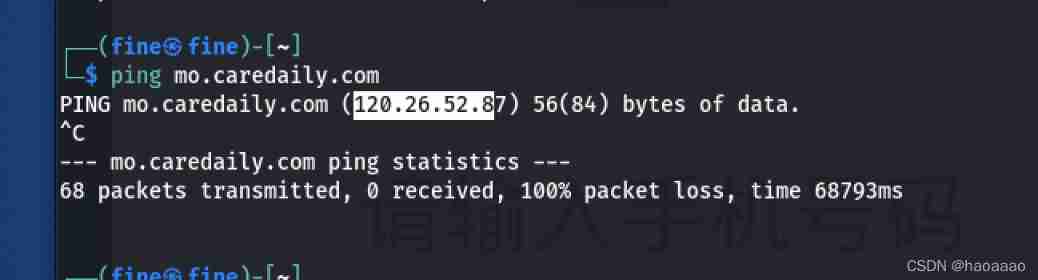
Subdomain query

Marginal query
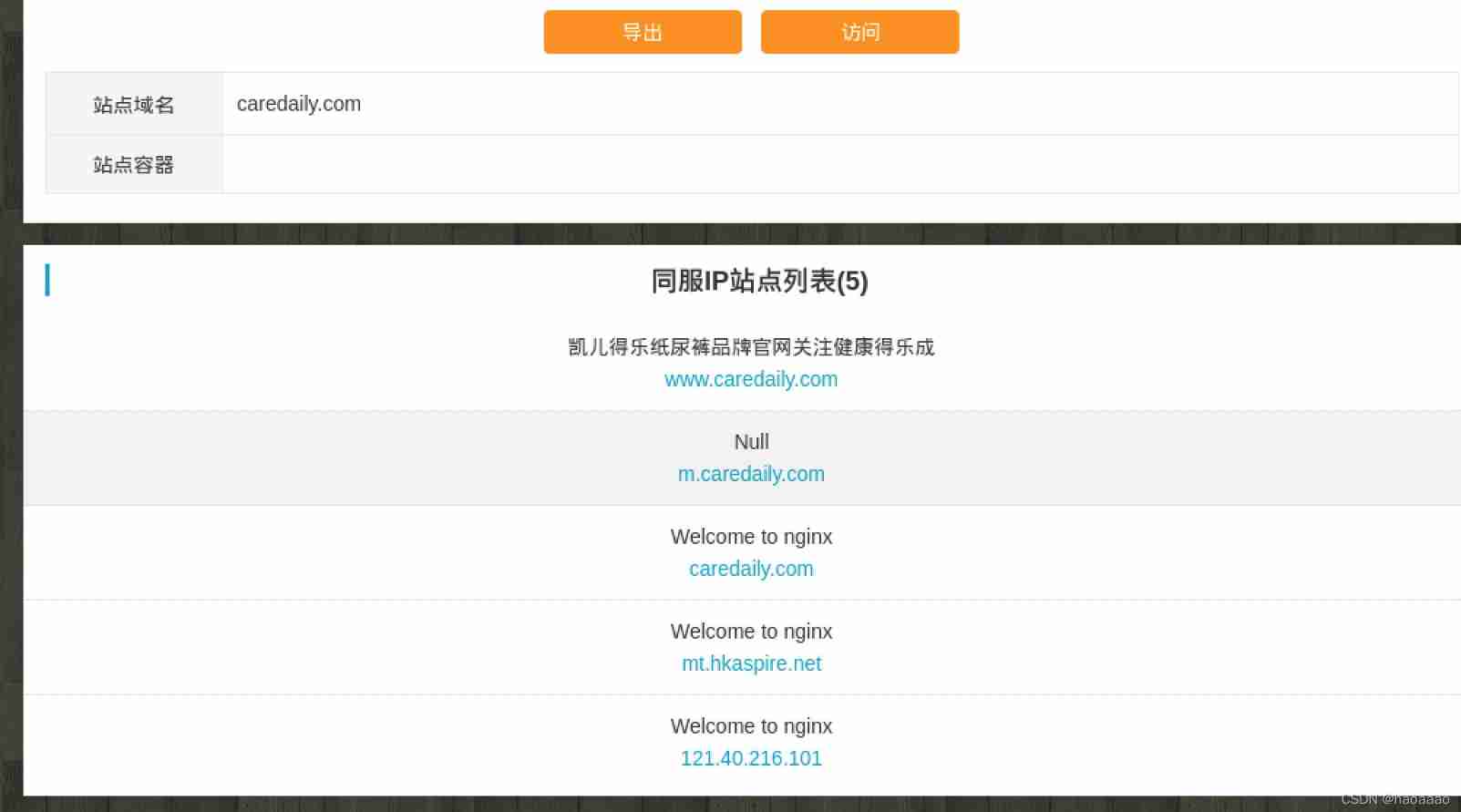
3) Record query



3、 ... and 、 Asset monitoring expansion
1、POC、EXP、Payload And Shellcode
(1) POC: Full name ' Proof of Concept ', chinese ' Proof of concept ' , It often refers to a piece of code that proves a vulnerability .
EXP: Full name ' Exploit ', chinese ' utilize ', It refers to the action of using system vulnerability to attack .
Payload: chinese ' Payload ', Success exploit after , Code or instruction actually executed in the target system .
Shellcode: Simple translation ' shell Code ', yes Payload A kind of , Because of its positive establishment / reverse shell And get the name .
(2)POC Is used to prove the existence of vulnerabilities ,EXP Is used to exploit vulnerabilities , The two are usually not in the same category , Or say ,PoC It's usually harmless ,Exp Usually harmful , With POC, Only then EXP.
Payload There are many kinds of , It can be Shellcode, It can also be a system command directly . The same Payload Can be used for multiple vulnerabilities , But each vulnerability has its own EXP, In other words, there is no universal EXP.
Shellcode There are many kinds , Including positive , In reverse , even to the extent that meterpreter.
Shellcode And Shellshcok Is not a ,Shellshock especially 14 Discovered in 2003 Shellshock Loophole .
2、github monitor
3、 Various collections
4、 demonstration : Monitor the latest EXP Release and others
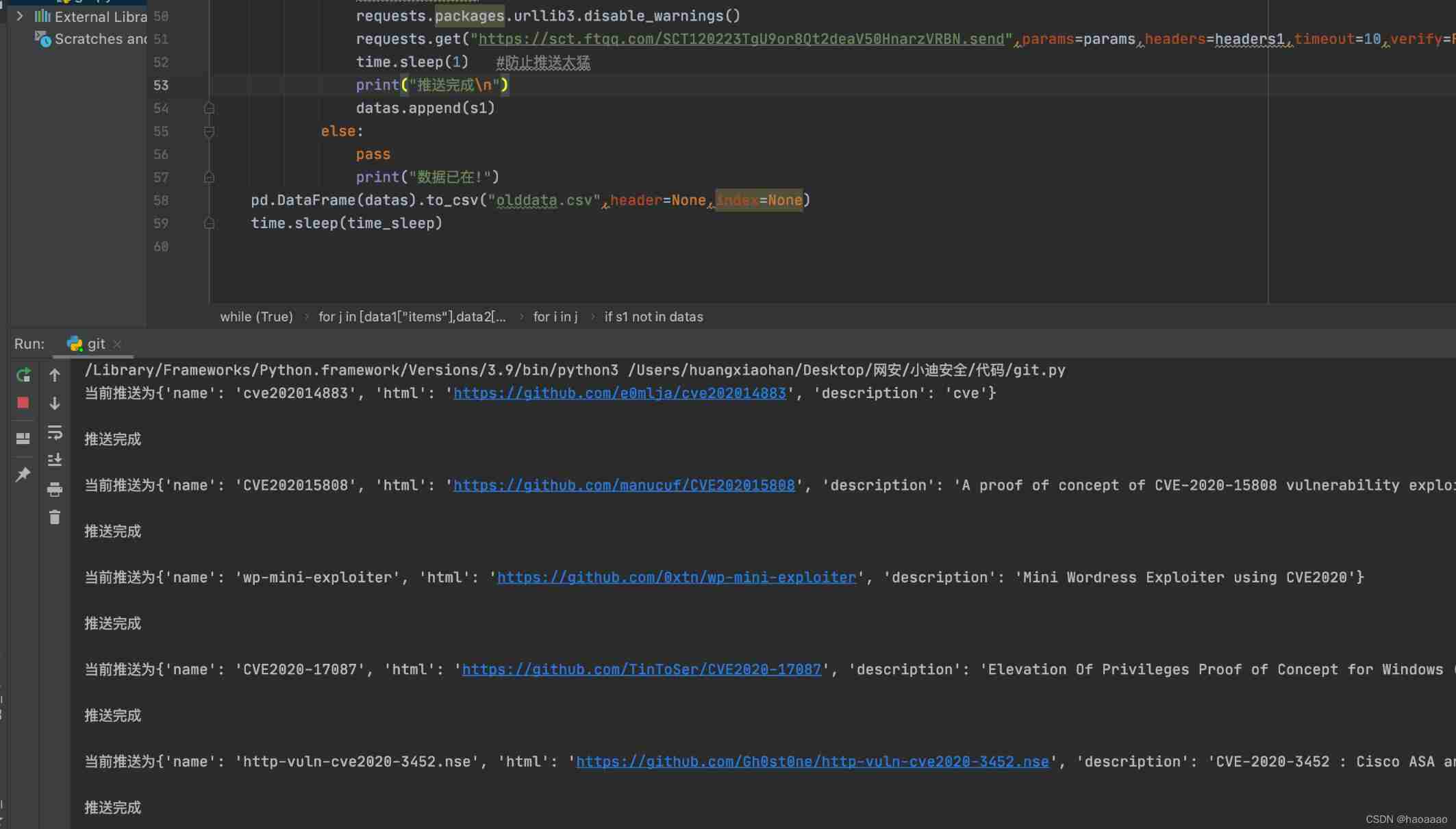
(1) The code is as follows :
#Title: wechat push CVE-2020
#Date: 2020-5-9
#Exploit Author: weixiao9188
#Version: 4.0
#Tested on: Linux,windows
#cd /root/sh/git/ && nohup python3 /root/sh/git/git.py &
#coding:UTF-8
import requests
import json
import time
import os
import pandas as pd
time_sleep = 60 # every other 20 Climb once a second
while(True):
headers1 = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko)Chrome/70.0.3538.25 Safari/537.36 Core/1.70.3741.400 QQBrowser/10.5.3863.400"}
# Judge whether the file exists
datas = []
response1=None
response2=None
if os.path.exists("olddata.csv"):
# If the file exists, each crawl 10 individual
df = pd.read_csv("olddata.csv", header=None)
datas = df.where(df.notnull(),None).values.tolist()# In the extracted data nan Turn into None
requests.packages.urllib3.disable_warnings()
response1 = requests.get(url="https://api.github.com/search/repositories?q=CVE2020&sort=updated&per_page=10",headers=headers1,verify=False)
response2 = requests.get(url="https://api.github.com/search/repositories?q=RCE&ssort=updated&per_page=10",headers=headers1,verify=False)
else:
# There is no crawling all
datas = []
requests.packages.urllib3.disable_warnings()
response1 = requests.get(url="https://api.github.com/search/repositories?q=CVE2020&sort=updated&order=desc",headers=headers1,verify=False)
response2 = requests.get(url="https://api.github.com/search/repositories?q=RCE&ssort=updated&order=desc",headers=headers1,verify=False)
data1 = json.loads(response1.text)
data2 = json.loads(response2.text)
for j in [data1["items"],data2["items"]]:
for i in j:
s = {"name":i['name'],"html":i['html_url'],"description":i['description']}
s1 =[i['name'],i['html_url'],i['description']]
if s1 not in datas:
#print(s1)
#print(datas)
params = {
"text":s["name"],
"desp":" link :"+str(s["html"])+"\n brief introduction "+str(s["description"])
}
print(" The current push is "+str(s)+"\n")
#print(params)
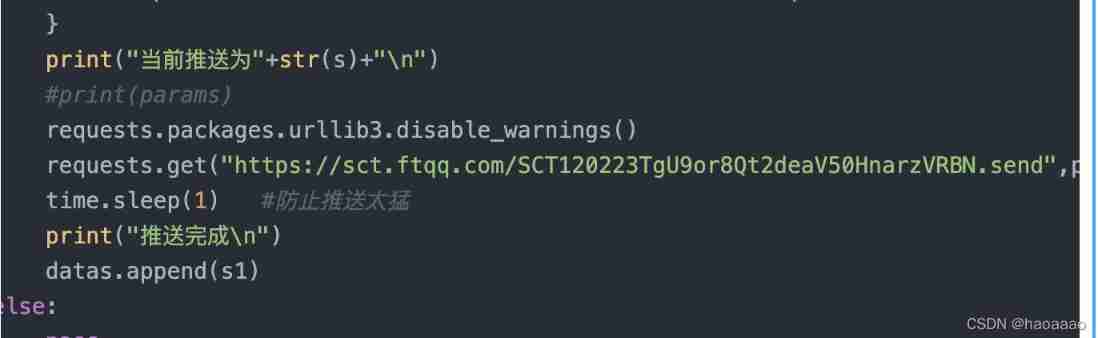
requests.packages.urllib3.disable_warnings()
requests.get("https://sct.ftqq.com/SCT120223TgU9or8Qt2deaV50HnarzVRBN.send",params=params,headers=headers1,timeout=10,verify=False)
time.sleep(1) # Prevent pushing too hard
print(" Push complete \n")
datas.append(s1)
else:
pass
print(" Data already in !")
pd.DataFrame(datas).to_csv("olddata.csv",header=None,index=None)
time.sleep(time_sleep)
(2) step :
1) stay sct.ftqq.com Scan wechat account , obtain sendkey:
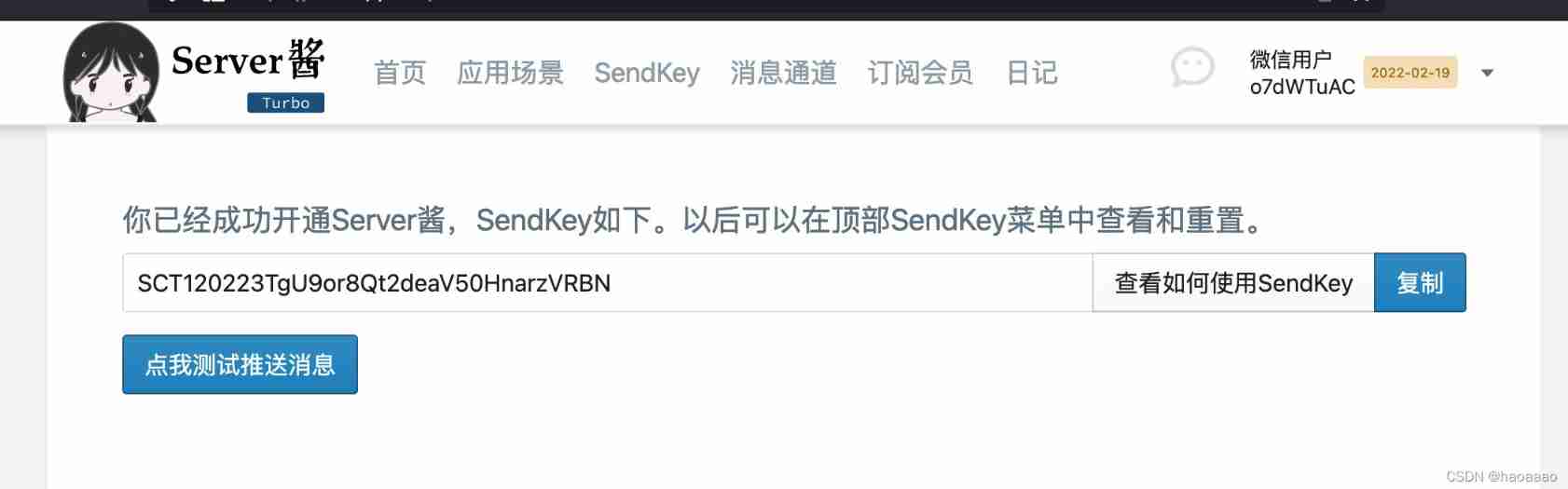
2) take sendkey Copy value to requests.get here :
3) Execution results :
边栏推荐
- Pyqt5 out of focus monitoring no operation timer
- Using thread class and runnable interface to realize the difference between multithreading
- Win11图片打不开怎么办?Win11无法打开图片的修复方法
- How do test / development programmers get promoted? From nothing, from thin to thick
- Do you choose pandas or SQL for the top 1 of data analysis in your mind?
- 科兴与香港大学临床试验中心研究团队和香港港怡医院合作,在中国香港启动奥密克戎特异性灭活疫苗加强剂临床试验
- 機器人(自動化)課程的持續學習-2022-
- Some thoughts on cross end development of kbone and applet
- Redis configuration and optimization of NoSQL
- Win11远程桌面连接怎么打开?Win11远程桌面连接的五种方法
猜你喜欢
ABAP 動態內錶分組循環
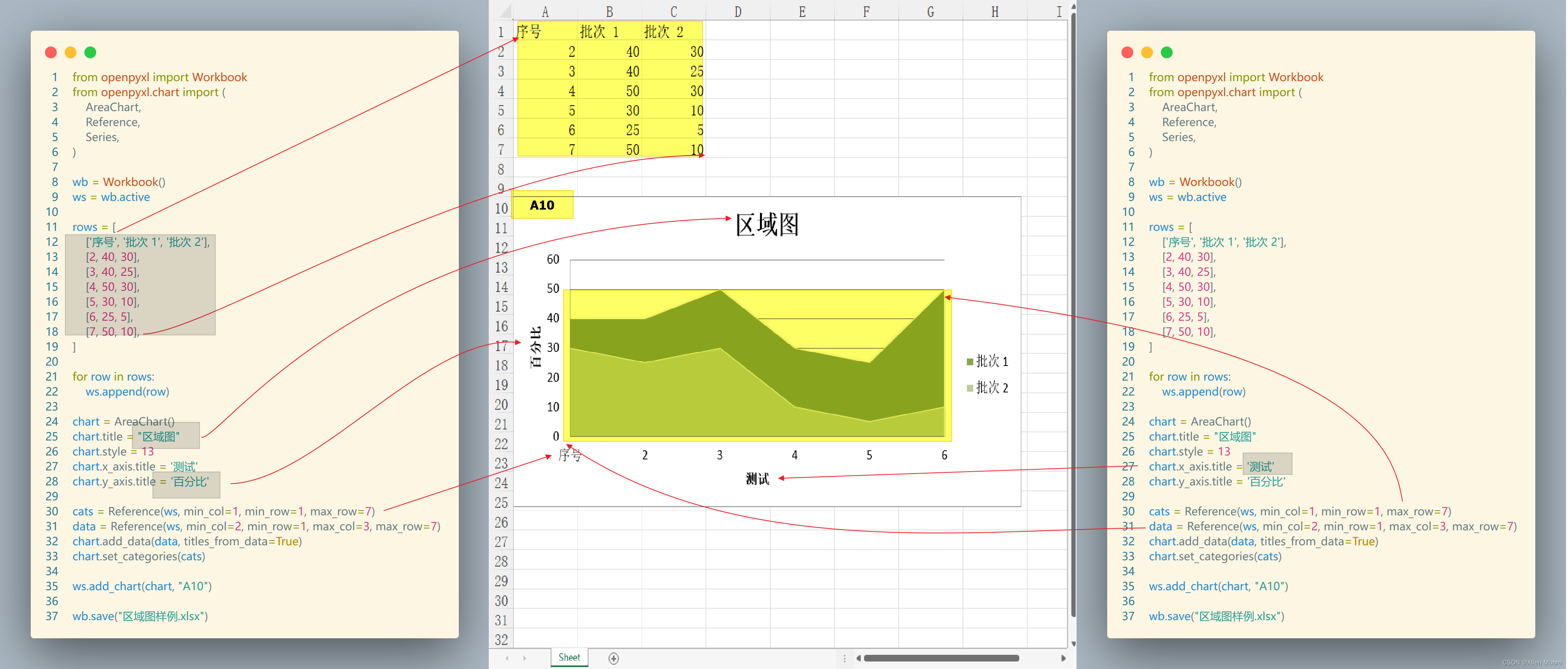
【OA】Excel 文档生成器: Openpyxl 模块
![[multi threading exercise] write a multi threading example of the producer consumer model.](/img/8a/4a2836f905968f42e0ef339d900b19.jpg)
[multi threading exercise] write a multi threading example of the producer consumer model.
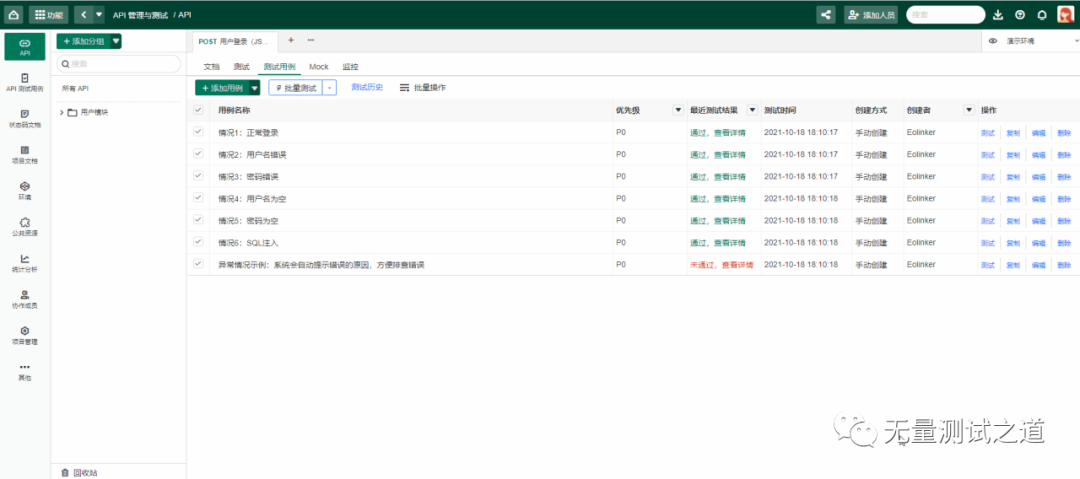
接口自动化测试实践指导(中):接口测试场景有哪些
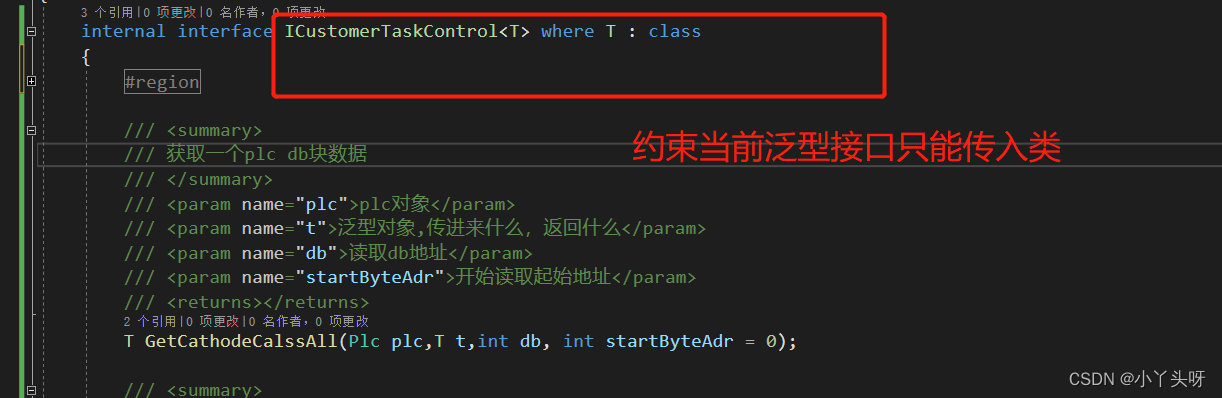
C # use Siemens S7 protocol to read and write PLC DB block

案例大赏:英特尔携众多合作伙伴推动多领域AI产业创新发展
NFT meta universe chain diversified ecosystem development case
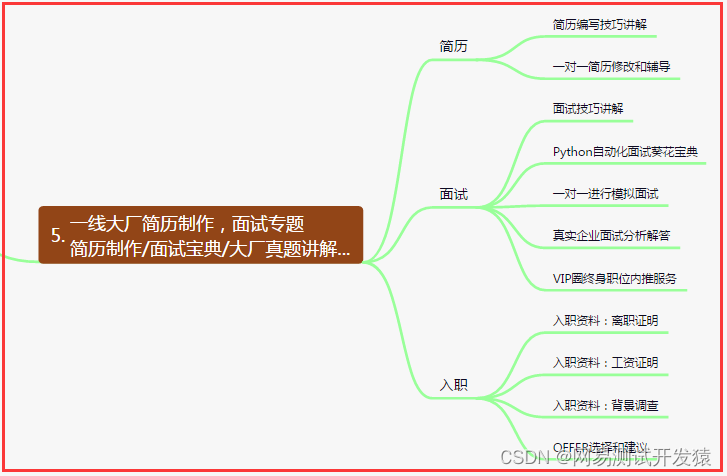
How do test / development programmers get promoted? From nothing, from thin to thick
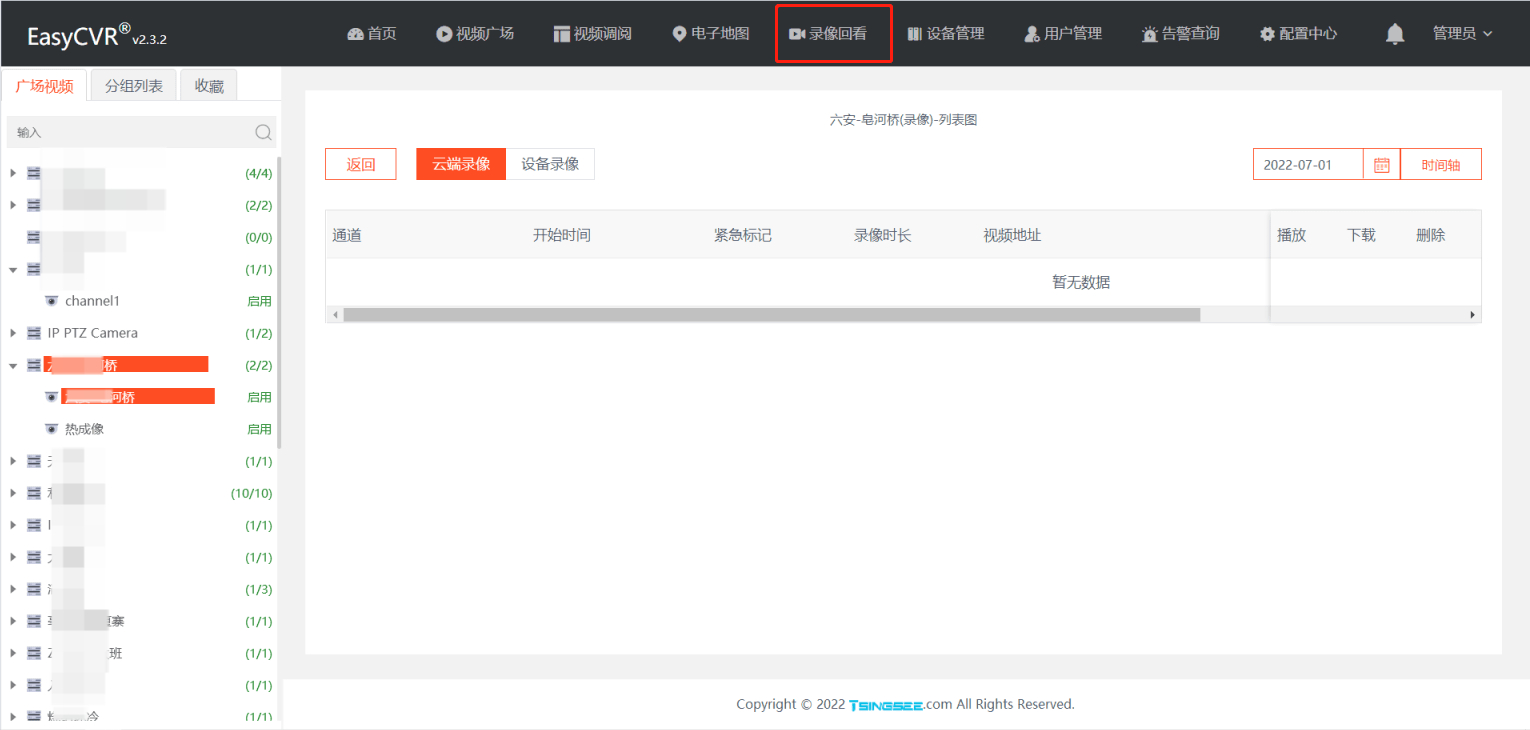
EasyCVR视频广场点击播放时,主菜单高亮效果消失问题的修复
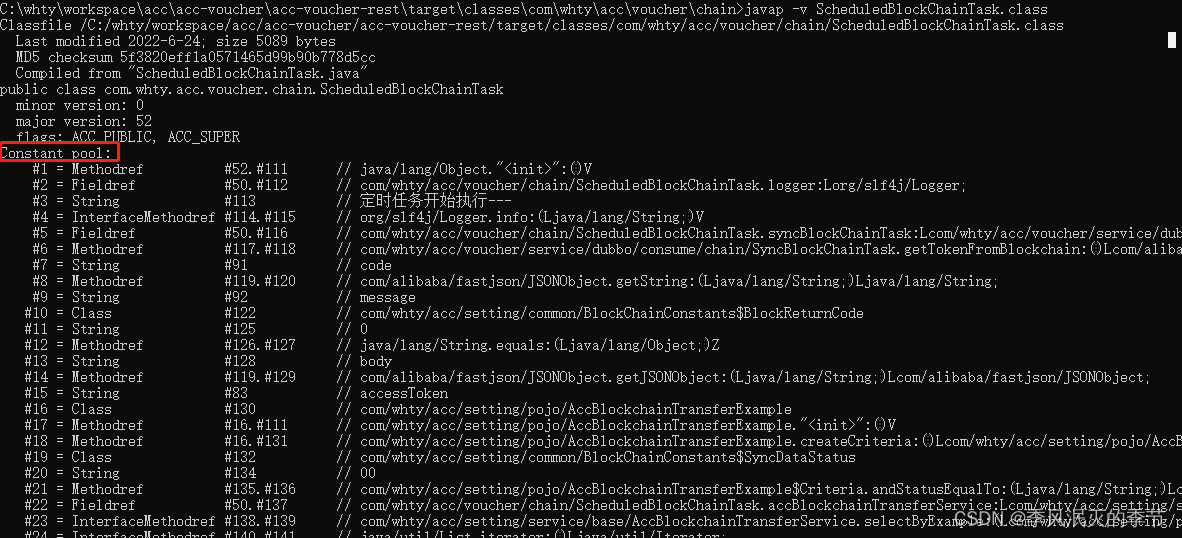
Class constant pool and runtime constant pool
随机推荐
Restore backup data on GCS with tidb lightning
[team learning] [phase 34] Baidu PaddlePaddle AI talent Creation Camp
Fix the problem that the highlight effect of the main menu disappears when the easycvr Video Square is clicked and played
See Gardenia minor
Highly paid programmers & interview questions. Are you familiar with the redis cluster principle of series 120? How to ensure the high availability of redis (Part 1)?
高薪程序员&面试题精讲系列120之Redis集群原理你熟悉吗?如何保证Redis的高可用(上)?
Operational amplifier application summary 1
Food Chem | in depth learning accurately predicts food categories and nutritional components based on ingredient statements
[ArcGIS tutorial] thematic map production - population density distribution map - population density analysis
[on automation experience] the growth path of automated testing
ABAP Dynamic Inner table Group cycle
Use dumping to back up tidb cluster data to GCS
Why does WordPress open so slowly?
[system management] clear the icon cache of deleted programs in the taskbar
EasyCVR集群重启导致其他服务器设备通道状态离线情况的优化
Implementation of JSTL custom function library
EasyCVR无法使用WebRTC进行播放,该如何解决?
機器人(自動化)課程的持續學習-2022-
The JSON format of the international area code of the mobile phone number is obtained with PHP
Triple half circle progress bar, you can use it directly