当前位置:网站首页>史上最全MongoDB之安全认证
史上最全MongoDB之安全认证
2022-07-06 21:33:00 【janyxe】
MongoDB系列文章目录
如果本文对你们的开发之路有所帮助,请帮忙点个赞,您的支持是我坚持写博客的动力
扫描文章底部二维码获取电子书和最新面试资料
前言
本系列课程将带着大家以面试题的方式 深入分布式专题之MongoDB。这篇文章带着大家深入MongoDB安全认证
MongoDB 的用户权限介绍
- MongoDB 2.4支持RABC模型,使用的是基于角色的访问控制(Role-Based Access Control,RBAC)来管理用户对实例的访问
RBAC(基于角色的访问控制):英文名称Role-Based Access Control
MongoDB 角色
| 角色 | 权限名称 |
|---|---|
| 数据库用户角色 | read、readWrite |
| 数据库管理角色 | dbAdmin、dbOwner、userAdmin |
| 集群管理角色 | clusterAdmin、clusterManager、clusterMonitor、hostManager |
| 备份恢复角色 | backup、restore |
| 所有数据库角色 | readAnyDatabase、readWriteAnyDatabase、userAdminAnyDatabase、dbAdminAnyDatabase |
| 超级用户角色 | root |
| 内部角色 | __system |
MongoDB 权限
| 权限名 | 描述 |
|---|---|
| read | 允许用户读取指定数据库 |
| readWrite | 允许用户读写指定数据库 |
| dbAdmin | 允许用户在指定数据库中执行管理函数,如索引创建、删除,查看统计或访问system.profile |
| dbOwner | 允许用户在指定数据库中执行任意操作,增、删、改、查等 |
| userAdmin | 允许用户向system.users集合写入,可以在指定数据库里创建、删 除和管理用户 |
| clusterAdmin | 只在admin数据库中可用,赋予用户所有分片和复制集相关函数的管理权限 |
| readAnyDatabase | 只在admin数据库中可用,赋予用户所有数据库的读权限 |
| readWriteAnyDatabase | 只在admin数据库中可用,赋予用户所有数据库的读写权限 |
| userAdminAnyDatabase | 只在admin数据库中可用,赋予用户所有数据库的userAdmin权限 |
| dbAdminAnyDatabase | 只在admin数据库中可用,赋予用户所有数据库的dbAdmin权限 |
| root | 只在admin数据库中可用。超级账号,超级权限 |
MongoDB 的用户权限建议
- 默认情况,MongoDB 服务端启动没有启动用户
访问权限, 客户端连接MongoDB 服务端不需要安全认证,可以随意操作存在很大风险 - 生产环境 开启安全认证,通过命令行方式启动加上
--auth,或配置文件(mongod.conf)加上auth=true - 生产环境建议修改默认端口(27017)
- MongoDB应部署在内网环境,bind_ip参数(默认为localhost),根据客户端ip修改,格式:
bind_ip=1.1.1.1,2.2.2.2,禁止bind_ip使用0.0.0.0或bind_ip_all设置为true - 客户端操作数据库,应该用dbOwner(数据库管理角色)的账号操作,禁止使用管理员角色(/权限高账号)操作数据库
操作用户角色命令
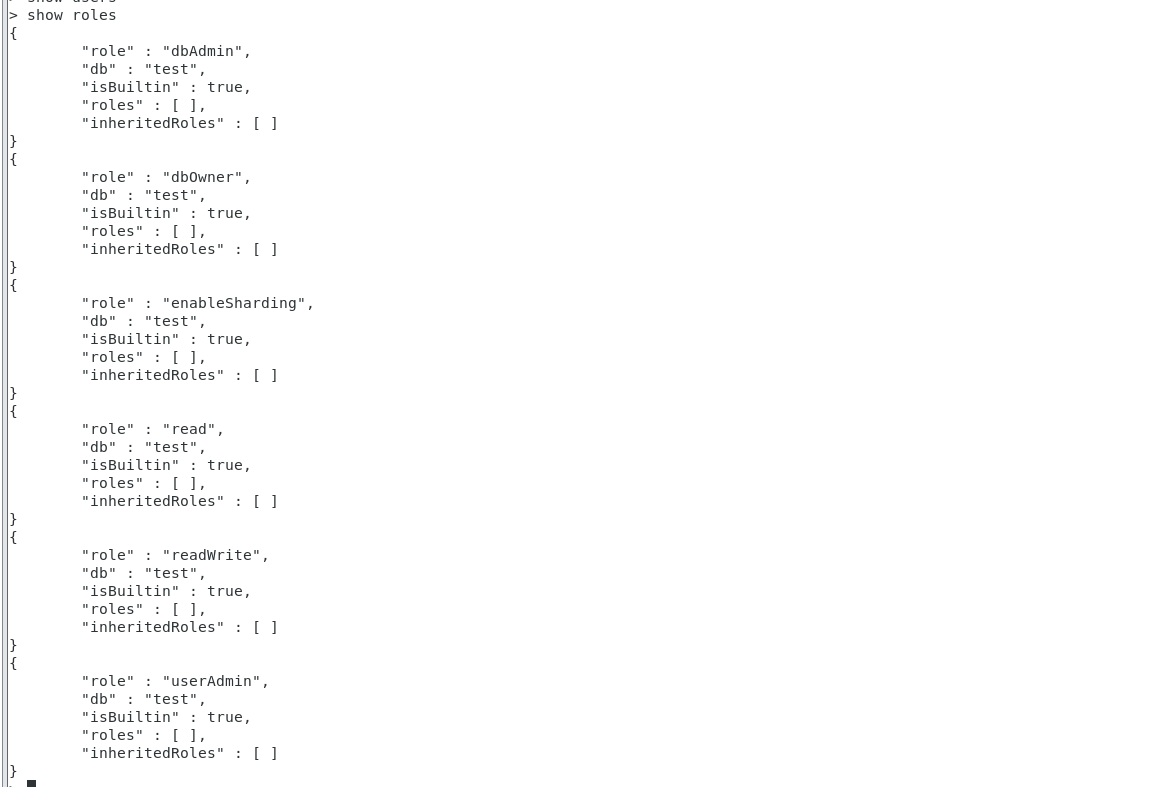
show roles 查看角色列表命令
概念
查看角色列表
命令应用
> show roles
{
"role" : "dbAdmin",
"db" : "test",
"isBuiltin" : true,
"roles" : [ ],
"inheritedRoles" : [ ]
}
{
"role" : "dbOwner",
"db" : "test",
"isBuiltin" : true,
"roles" : [ ],
"inheritedRoles" : [ ]
}
{
"role" : "enableSharding",
"db" : "test",
"isBuiltin" : true,
"roles" : [ ],
"inheritedRoles" : [ ]
}
{
"role" : "read",
"db" : "test",
"isBuiltin" : true,
"roles" : [ ],
"inheritedRoles" : [ ]
}
{
"role" : "readWrite",
"db" : "test",
"isBuiltin" : true,
"roles" : [ ],
"inheritedRoles" : [ ]
}
{
"role" : "userAdmin",
"db" : "test",
"isBuiltin" : true,
"roles" : [ ],
"inheritedRoles" : [ ]
}
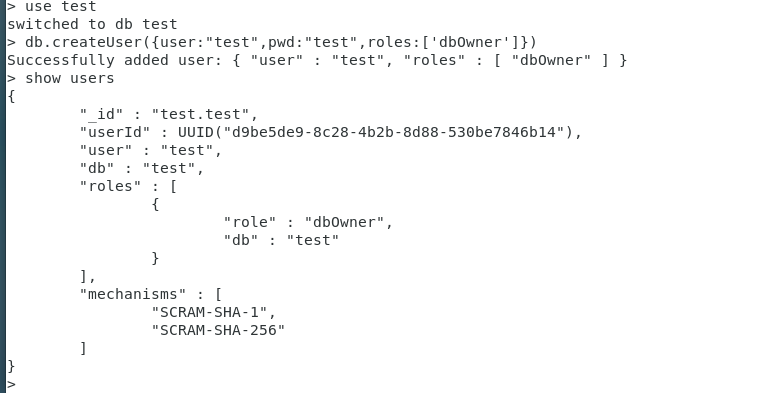
db.createUser(用户信息) 创建用户 命令
概念
创建用户
命令格式
db.createUser({user:“用户名”,pwd:“名称”,roles:[“角色”]})
| 命令参数 | 含义 |
|---|---|
| user | 用户名称 |
| pwd | 密码 |
| roles | 角色列表 |
命令应用
创建test库,并指定test库的管理员
> use test
switched to db test
> db.createUser({
user:"test",pwd:"test",roles:['dbOwner']})
uncaught exception: ReferenceError: dn is not defined :
@(shell):1:1
> use test
switched to db test
> db.createUser({
user:"test",pwd:"test",roles:['dbOwner']})
Successfully added user: {
"user" : "test", "roles" : [ "dbOwner" ] }
> show users
{
"_id" : "test.test",
"userId" : UUID("d9be5de9-8c28-4b2b-8d88-530be7846b14"),
"user" : "test",
"db" : "test",
"roles" : [
{
"role" : "dbOwner",
"db" : "test"
}
],
"mechanisms" : [
"SCRAM-SHA-1",
"SCRAM-SHA-256"
]
}
>
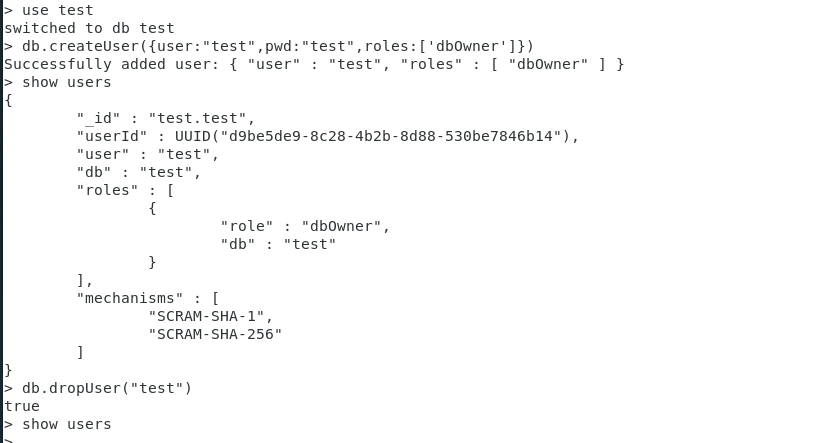
db.dropUser(用户名称) 删除用户 命令
概念
创建用户
命令格式
db.dropUser(“用户名”)
命令应用
db.dropUser(“test”)
> use test
switched to db test
> dn.createUser({
user:"test",pwd:"test",roles:['dbOwner']})
uncaught exception: ReferenceError: dn is not defined :
@(shell):1:1
> use test
switched to db test
> db.createUser({
user:"test",pwd:"test",roles:['dbOwner']})
Successfully added user: {
"user" : "test", "roles" : [ "dbOwner" ] }
> show users
{
"_id" : "test.test",
"userId" : UUID("d9be5de9-8c28-4b2b-8d88-530be7846b14"),
"user" : "test",
"db" : "test",
"roles" : [
{
"role" : "dbOwner",
"db" : "test"
}
],
"mechanisms" : [
"SCRAM-SHA-1",
"SCRAM-SHA-256"
]
}
>
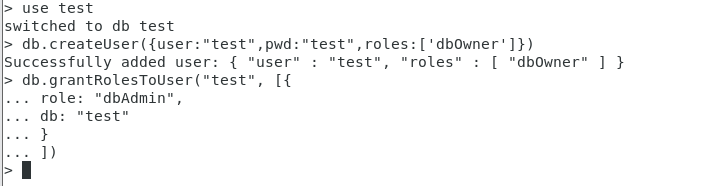
db.grantRolesToUser(用户名称,[]) 授权用户权限 命令
概念
授权用户权限
命令格式
db.grantRolesToUser(“用户名”, [{
role: “角色code”,
db: “数据库名称”
},…
])
命令应用
db.grantRolesToUser(“test”, [{
role: “dbAdmin”,
db: “test”
}
])
> use test
switched to db test
> db.createUser({
user:"test",pwd:"test",roles:['dbOwner']})
Successfully added user: {
"user" : "test", "roles" : [ "dbOwner" ] }
> db.grantRolesToUser("test", [{
... role: "dbAdmin",
... db: "test"
... }
... ])
>
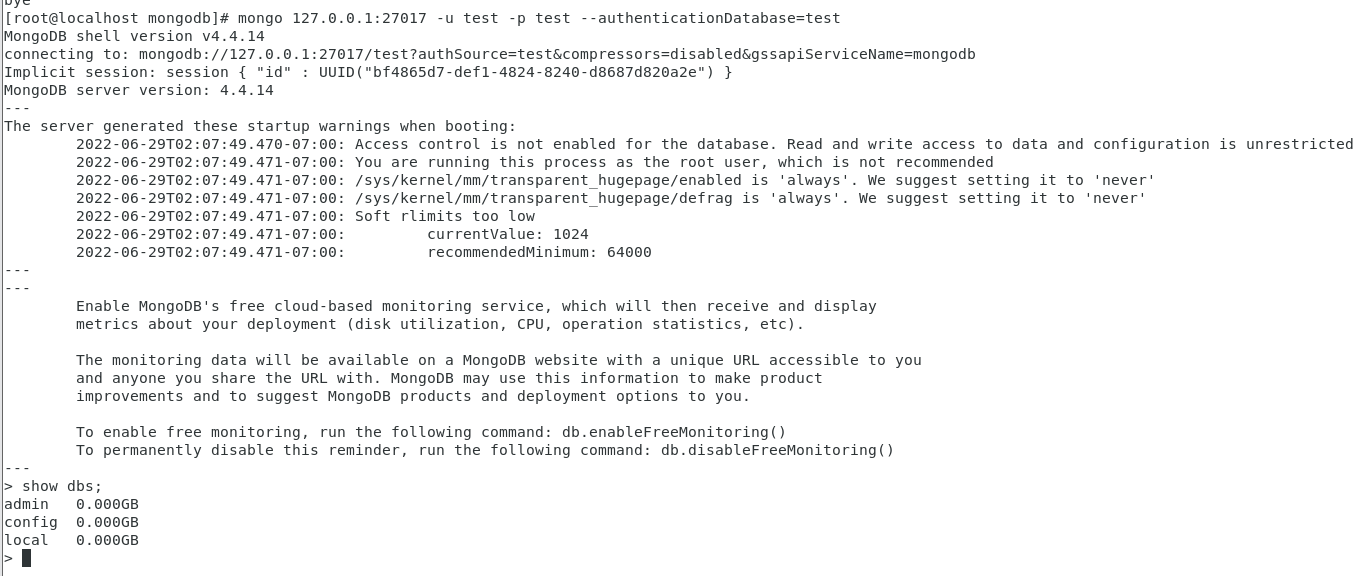
授权账号登录 命令
概念
授权账号登录
命令格式
mongo MONGO_HOST:PORT -u USER -p PWD --authenticationDatabase=DB
| 命令参数 | 含义 |
|---|---|
| MONGO_HOST | Mongo服务端 ip |
| PORT | Mongo服务端 端口 |
| -u | 用户名 |
| -p | 密码 |
| –authenticationDatabase | 授权数据库 |
命令应用
mongo 127.0.0.1:27017 -u test -p test --authenticationDatabase=test
[[email protected] mongodb]# mongo 127.0.0.1:27017 -u test -p test --authenticationDatabase=test
MongoDB shell version v4.4.14
connecting to: mongodb://127.0.0.1:27017/test?authSource=test&compressors=disabled&gssapiServiceName=mongodb
Implicit session: session {
"id" : UUID("bf4865d7-def1-4824-8240-d8687d820a2e") }
MongoDB server version: 4.4.14
---
The server generated these startup warnings when booting:
2022-06-29T02:07:49.470-07:00: Access control is not enabled for the database. Read and write access to data and configuration is unrestricted
2022-06-29T02:07:49.471-07:00: You are running this process as the root user, which is not recommended
2022-06-29T02:07:49.471-07:00: /sys/kernel/mm/transparent_hugepage/enabled is 'always'. We suggest setting it to 'never'
2022-06-29T02:07:49.471-07:00: /sys/kernel/mm/transparent_hugepage/defrag is 'always'. We suggest setting it to 'never'
2022-06-29T02:07:49.471-07:00: Soft rlimits too low
2022-06-29T02:07:49.471-07:00: currentValue: 1024
2022-06-29T02:07:49.471-07:00: recommendedMinimum: 64000
---
---
Enable MongoDB's free cloud-based monitoring service, which will then receive and display
metrics about your deployment (disk utilization, CPU, operation statistics, etc).
The monitoring data will be available on a MongoDB website with a unique URL accessible to you
and anyone you share the URL with. MongoDB may use this information to make product
improvements and to suggest MongoDB products and deployment options to you.
To enable free monitoring, run the following command: db.enableFreeMonitoring()
To permanently disable this reminder, run the following command: db.disableFreeMonitoring()
---
> show dbs;
admin 0.000GB
config 0.000GB
local 0.000GB
>
初次见面,也不知道送你们啥。干脆就送几百本电子书和最新面试资料,祝你们找到更好的工作,扫描下面二维码获取
边栏推荐
- [hcie TAC] question 3
- On file uploading of network security
- termux设置电脑连接手机。(敲打命令贼快),手机termux端口8022
- Create commonly used shortcut icons at the top of the ad interface (menu bar)
- Simple implementation of AVL tree insertion and verification operations
- 杭州电 3711 Binary Number
- Enter the rough outline of the URL question (continuously updated)
- 史上最全学习率调整策略lr_scheduler
- QT item table new column name setting requirement exercise (find the number and maximum value of the array disappear)
- 如何检测mysql代码运行是否出现死锁+binlog查看
猜你喜欢
Baidu map JS development, open a blank, bmapgl is not defined, err_ FILE_ NOT_ FOUND
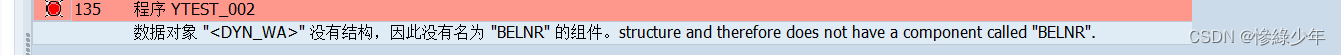
ABAP dynamic inner table grouping cycle

21. (article ArcGIS API for JS) ArcGIS API for JS rectangular acquisition (sketchviewmodel)
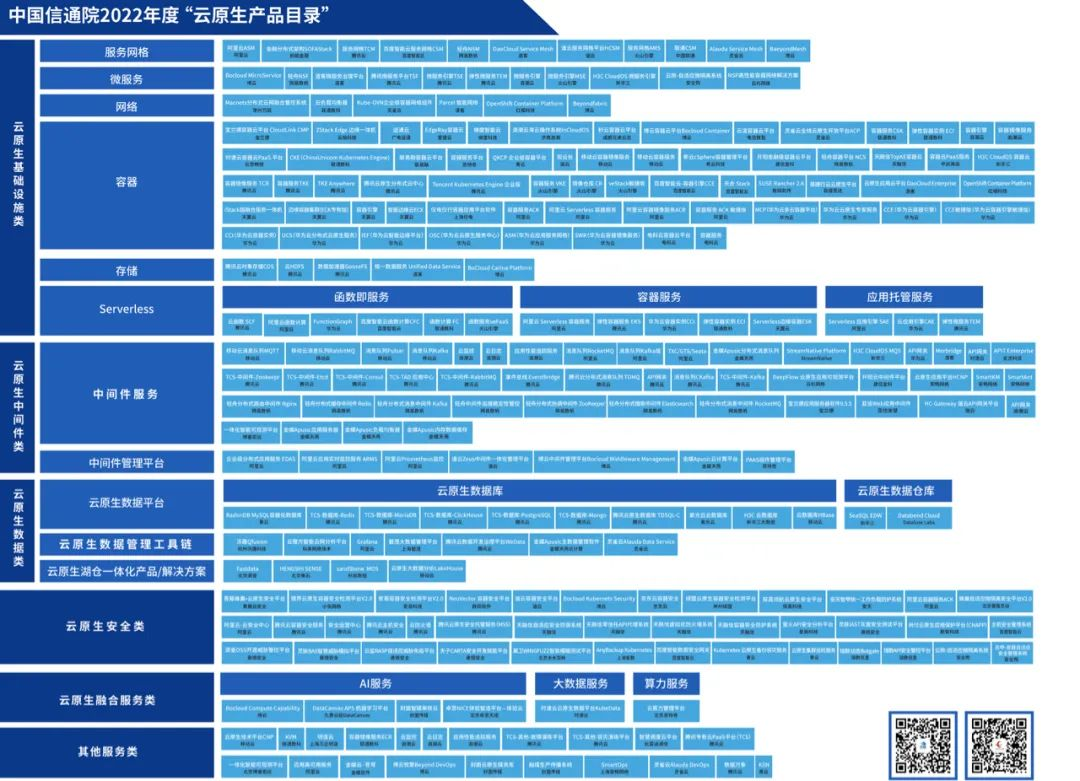
Tencent cloud native database tdsql-c was selected into the cloud native product catalog of the Academy of communications and communications
![[hcie TAC] question 3](/img/d2/38a7286be7780a60f5311b2fcfaf0b.jpg)
[hcie TAC] question 3
Leetcode: interview question 17.24 Maximum cumulative sum of submatrix (to be studied)
QT opens a file and uses QFileDialog to obtain the file name, content, etc
![[MySQL] row sorting in MySQL](/img/97/8a451fa62796838e11242c86eecd8d.png)
[MySQL] row sorting in MySQL
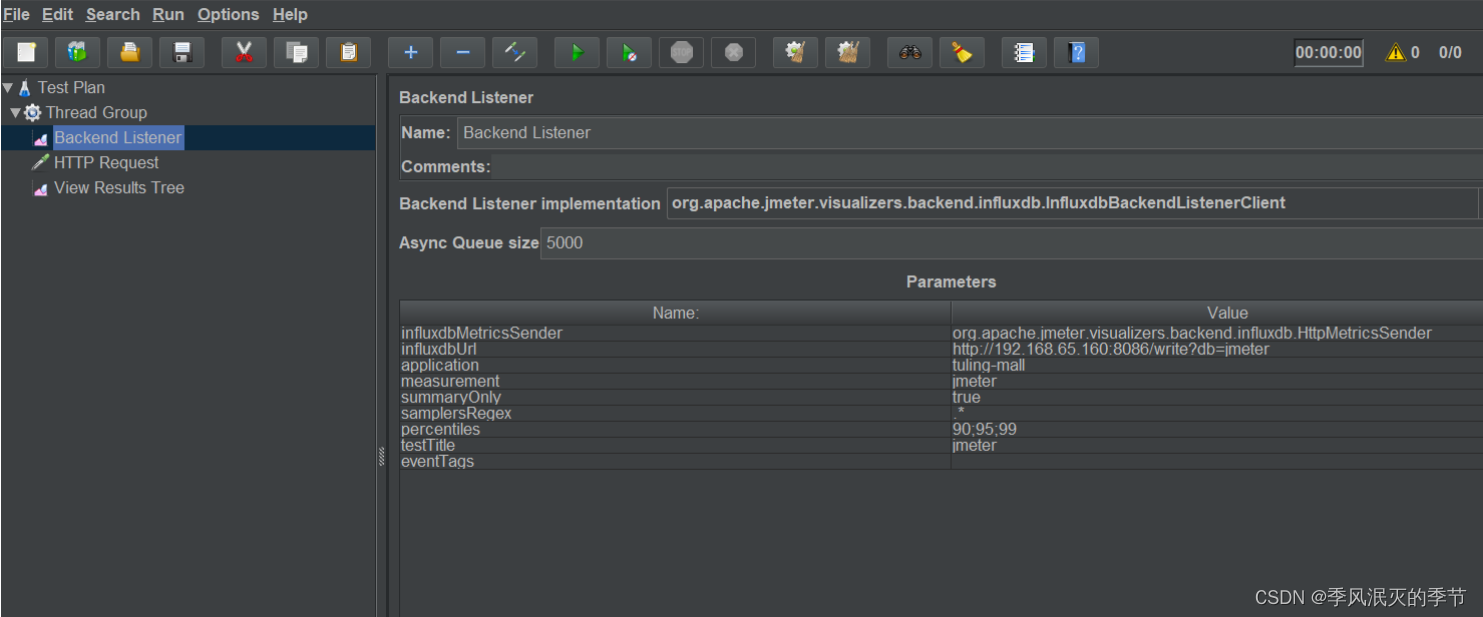
Web service performance monitoring scheme
![[security attack and Defense] how much do you know about serialization and deserialization?](/img/1c/e5ae74e65bacf688d7f61cc1b71d3e.png)
[security attack and Defense] how much do you know about serialization and deserialization?
随机推荐
Delete data in SQL
【安全攻防】序列化與反序列,你了解多少?
再AD 的 界面顶部(菜单栏)创建常用的快捷图标
QT item table new column name setting requirement exercise (find the number and maximum value of the array disappear)
Arduino droplet detection
What is the experience of maintaining Wanxing open source vector database
One of oscp tools: dirsearch usage Encyclopedia
接口数据安全保证的10种方式
Redis configuration and optimization of NoSQL
When QT uses qtooltip mouse to display text, the picture of the button will also be displayed and the prompt text style will be modified
Storage of data
Enter the rough outline of the URL question (continuously updated)
C# Task拓展方法
API data interface of A-share index component data
Probability formula
. Net interface can be implemented by default
复杂因子计算优化案例:深度不平衡、买卖压力指标、波动率计算
MySQL的存储引擎
Docker部署Mysql8的实现步骤
Antd Comment 递归循环评论