当前位置:网站首页>【Try to Hack】主动侦查隐藏技术
【Try to Hack】主动侦查隐藏技术
2022-07-03 16:53:00 【开心星人】
https://www.bilibili.com/video/BV1bt4y1874s?p=79
博客主页:开心星人的博客主页
系列专栏:Try to Hack
欢迎关注点赞收藏️留言
首发时间:2022年7月3日
作者水平很有限,如果发现错误,还望告知,感谢!
主动侦察建立在OSNT开源的被动侦察基础上,获取目标更多信息,为了找到更多可能存在安全问题的地方。但是主动侦察会与目标进行大量交互,被目标检测到的可能性会更大。
技术
1、伪装工具签名
2、将流量隐藏与合法流量中
3、修改来源与类型
调整源IP栈和工具识别设置
常见是更改User-Agent
这里用msf来进行演示msfconsoleuse auxiliary/fuzzers/http/http_form_field 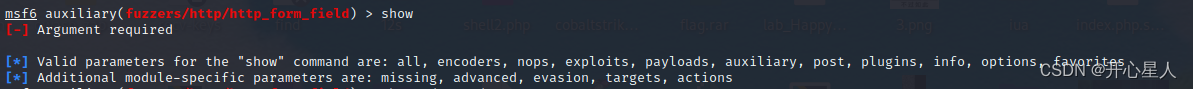
有一个advancedshow advanced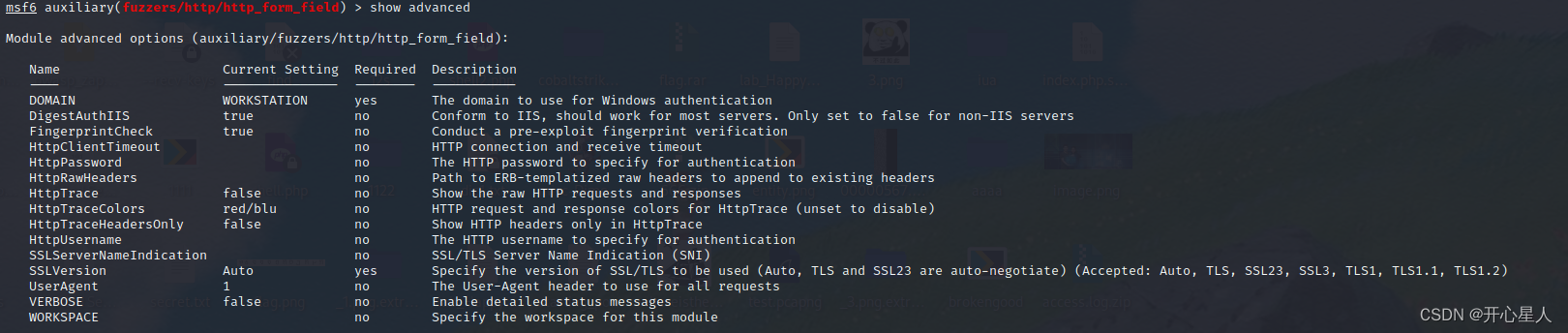
有useragentset useragent BaiduSpider //搜索引擎的爬虫一般都不会被过滤set rhost 192.168.0.1 设置为路由,向路由发送http数据包run
wireshark抓包看看
过滤规则http&&ip.dst==192.168.0.1&&ip.src==192.168.0.106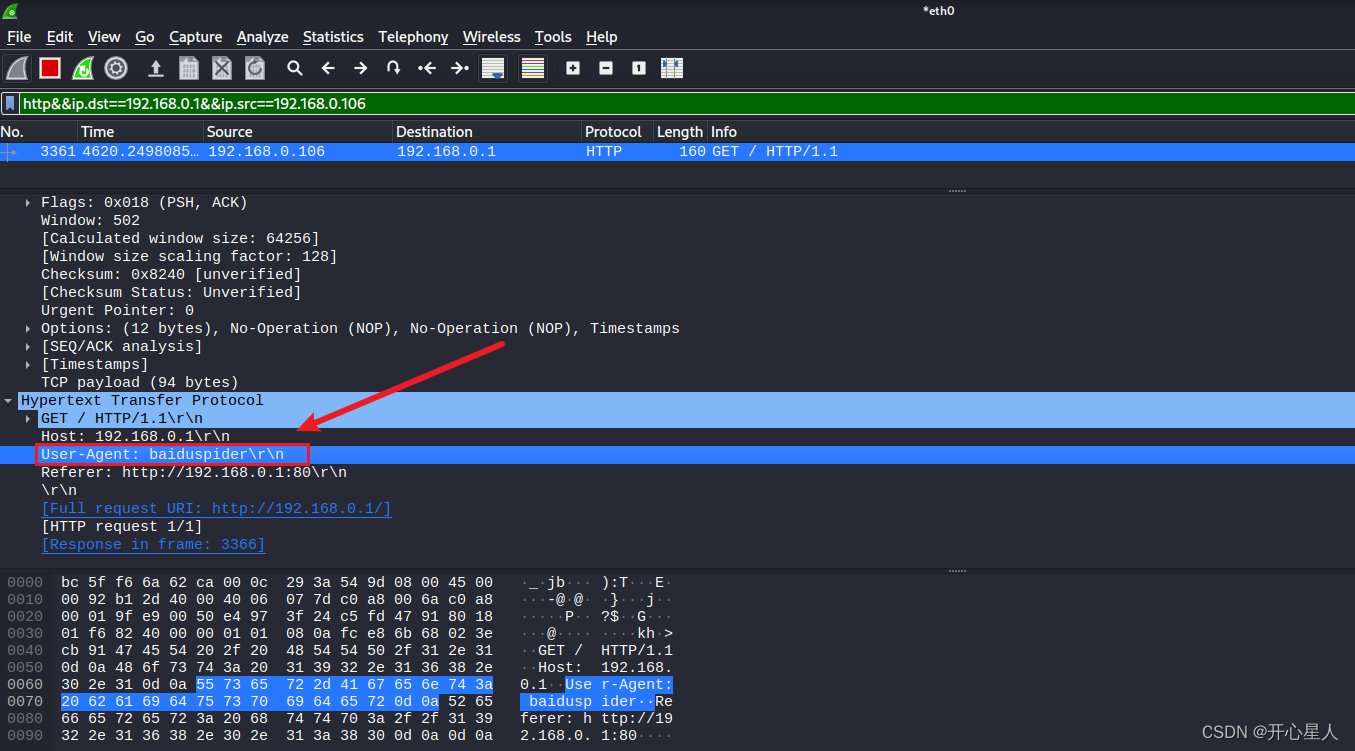
修改数据包参数
Nmap修改原始参数nmap --spoof-mac 11:11:11:11:11:11 26 -sS -Pn -p80 192.168.0.1
确实伪装了mac地址,但是为什么Destination是0.0.0.26,我也不太清楚
很多其他工具也都有类似的可以修改数据包参数
如masscan的–adapter-mac、–adapter-ip
使用代理匿名网络tor
当使用Tor客户端时,您的Internet通信将通过Tor的网络进行路由。 在离开Tor网络到达目的地之前,流量会经过几个随机选择的中继站(由志愿者运行)。 这样可以防止Internet服务提供商和监视您的本地网络的人员查看您访问的网站。 它还会阻止网站本身知道您的实际位置或IP地址-他们会看到出口节点的IP地址和位置。 甚至中继站也不知道谁请求了他们所经过的流量。 Tor网络中的所有流量均已加密。
apt install torservice tor start 启动torservice tor status 查看tor是否启动
通过安装配置proxychains4,是将任何程序和代理工具的proxy建立连接,原理和浏览器的代理相似。apt install proxychains4gedit /etc/proxychains4.conf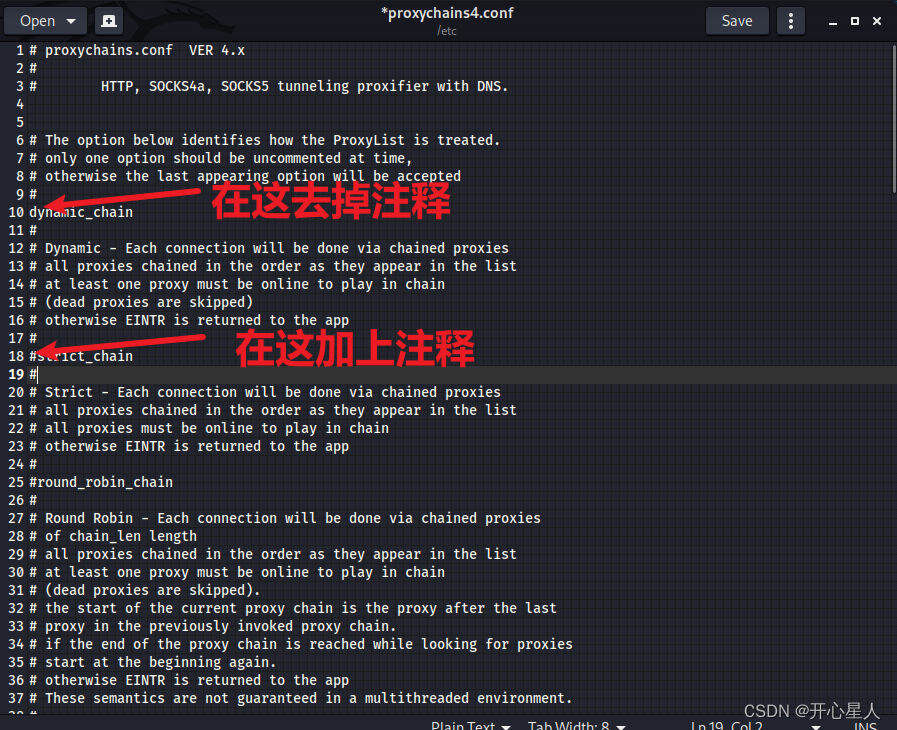

firefox www.whatismyip.com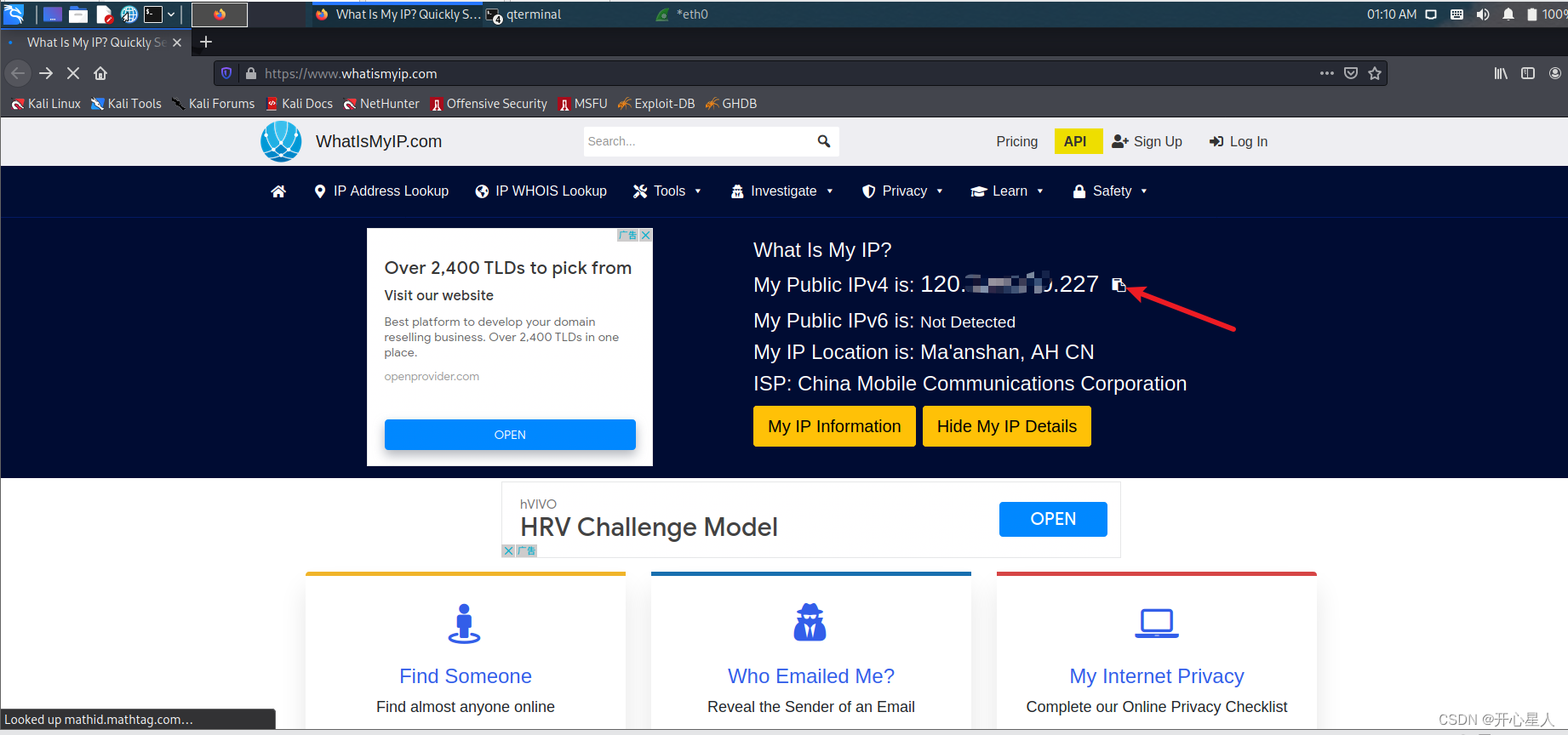
看到了,这是没有使用代理的真实ip,确实就是我的公网ip
proxychains firefox www.whatismyip.com 修改代理
边栏推荐
- 于文文、胡夏等明星带你玩转派对 皮皮APP点燃你的夏日
- Mysql 单表字段重复数据取最新一条sql语句
- CC2530 common registers for port interrupts
- To resist 7-Zip, list "three sins"? Netizen: "is the third key?"
- What material is sa537cl1? Sa537cl1 corresponds to the national standard material
- 香港理工大学|数据高效的强化学习和网络流量动态的自适应最优周界控制
- [combinatorics] recursive equation (constant coefficient linear homogeneous recursive equation | constant coefficient, linear, homogeneous concept description | constant coefficient linear homogeneous
- 消息队列消息丢失和消息重复发送的处理策略
- Visual SLAM algorithms: a survey from 2010 to 2016
- arduino-esp32:LVGL项目(一)整体框架
猜你喜欢

Simulink oscilloscope data is imported into Matlab and drawn

线程池执行定时任务

网络安全web渗透技术
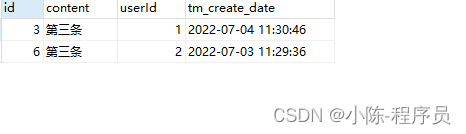
MySQL single table field duplicate data takes the latest SQL statement

What is the pledge pool and how to pledge?

Idea configuration plug-in
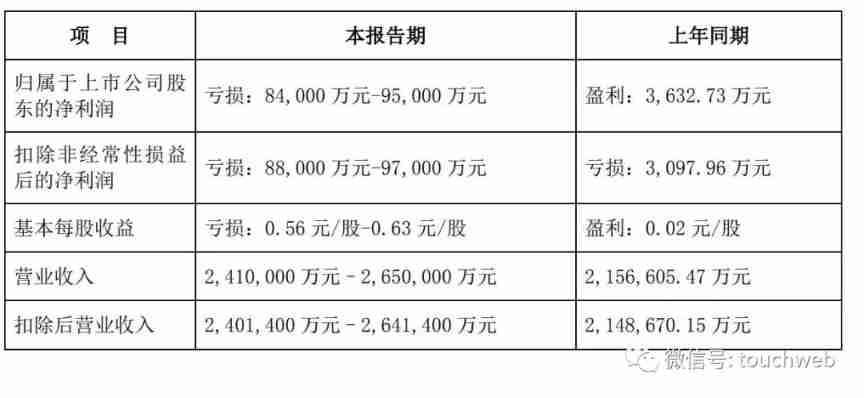
Shentong express expects an annual loss of nearly 1billion

8 cool visual charts to quickly write the visual analysis report that the boss likes to see
CC2530 common registers for port initialization

NLP four paradigms: paradigm 1: fully supervised learning in the era of non neural networks (Feature Engineering); Paradigm 2: fully supervised learning based on neural network (Architecture Engineeri
随机推荐
How to delete a specific line from a text file using the SED command?
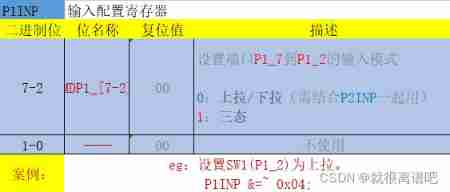
CC2530 common registers for port interrupts
[JDBC] API parsing
New features of C 10
Characteristic polynomial and constant coefficient homogeneous linear recurrence
[combinatorics] polynomial theorem (polynomial coefficients | full arrangement of multiple sets | number of schemes corresponding to the ball sub model | polynomial coefficient correlation identity)
To resist 7-Zip, list "three sins"? Netizen: "is the third key?"
CC2530 common registers
LeetCode 1658. Minimum operand to reduce x to 0
Atom QT 16_ audiorecorder
There are several APIs of airtest and poco that are easy to use wrong in "super". See if you have encountered them
AcWing 第58 场周赛
MySQL user management
How to set up SVN server on this machine
[sword finger offer] 58 - I. flip the word order
香港理工大学|数据高效的强化学习和网络流量动态的自适应最优周界控制
Google Earth engine (GEE) - daymet v4: daily surface weather data set (1000m resolution) including data acquisition methods for each day
[combinatorial mathematics] counting model, common combinatorial numbers and combinatorial identities**
LeetCode 1657. Determine whether the two strings are close
Informatics Olympiad all in one YBT 1175: divide by 13 | openjudge noi 1.13 27: divide by 13