边栏推荐
- Simple configuration of single arm routing and layer 3 switching
- 小试牛刀之NunJucks模板引擎
- “解密”华为机器视觉军团:华为向上,产业向前
- PIP related commands
- Skills of embedded C language program debugging and macro use
- Redis的发布与订阅
- Ten thousand words nanny level long article -- offline installation guide for datahub of LinkedIn metadata management platform
- [paddleseg source code reading] add boundary IOU calculation in paddleseg validation (1) -- val.py file details tips
- GSAP animation library
- String type, constant type and container type of go language
猜你喜欢
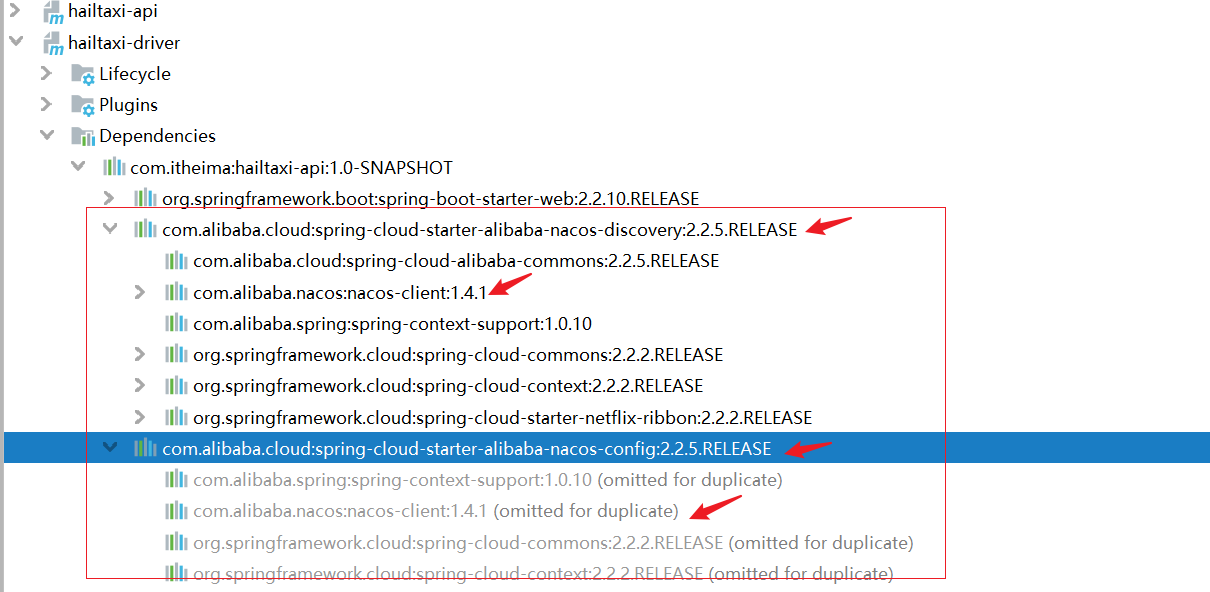
Tear the Nacos source code by hand (tear the client source code first)
RISCV64
![[Tawang methodology] Tawang 3W consumption strategy - U & a research method](/img/63/a8c08ac6ec7d654159e5fc8b4423e4.png)
[Tawang methodology] Tawang 3W consumption strategy - U & a research method
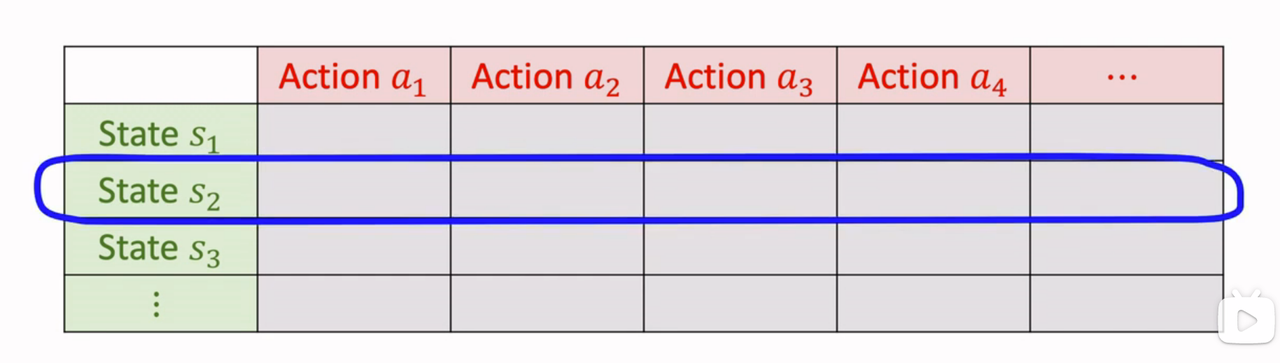
强化学习-学习笔记8 | Q-learning
Datasimba launched wechat applet, and datanuza accepted the test of the whole scene| StartDT Hackathon
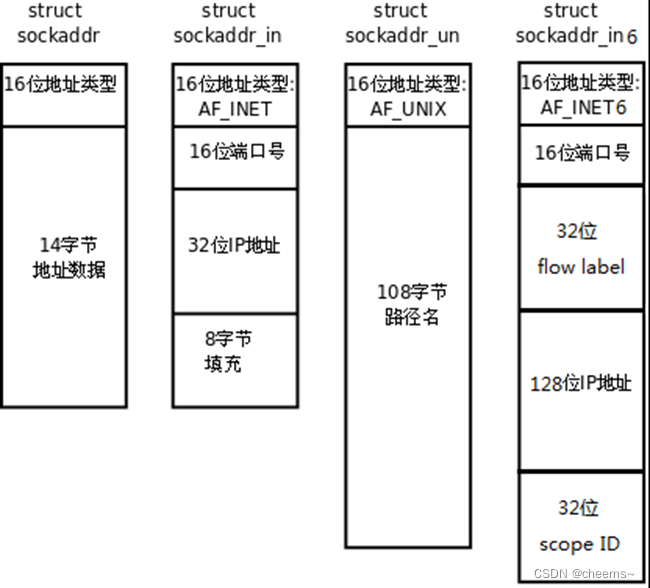
socket編程之常用api介紹與socket、select、poll、epoll高並發服務器模型代碼實現

直播预约通道开启!解锁音视频应用快速上线的秘诀
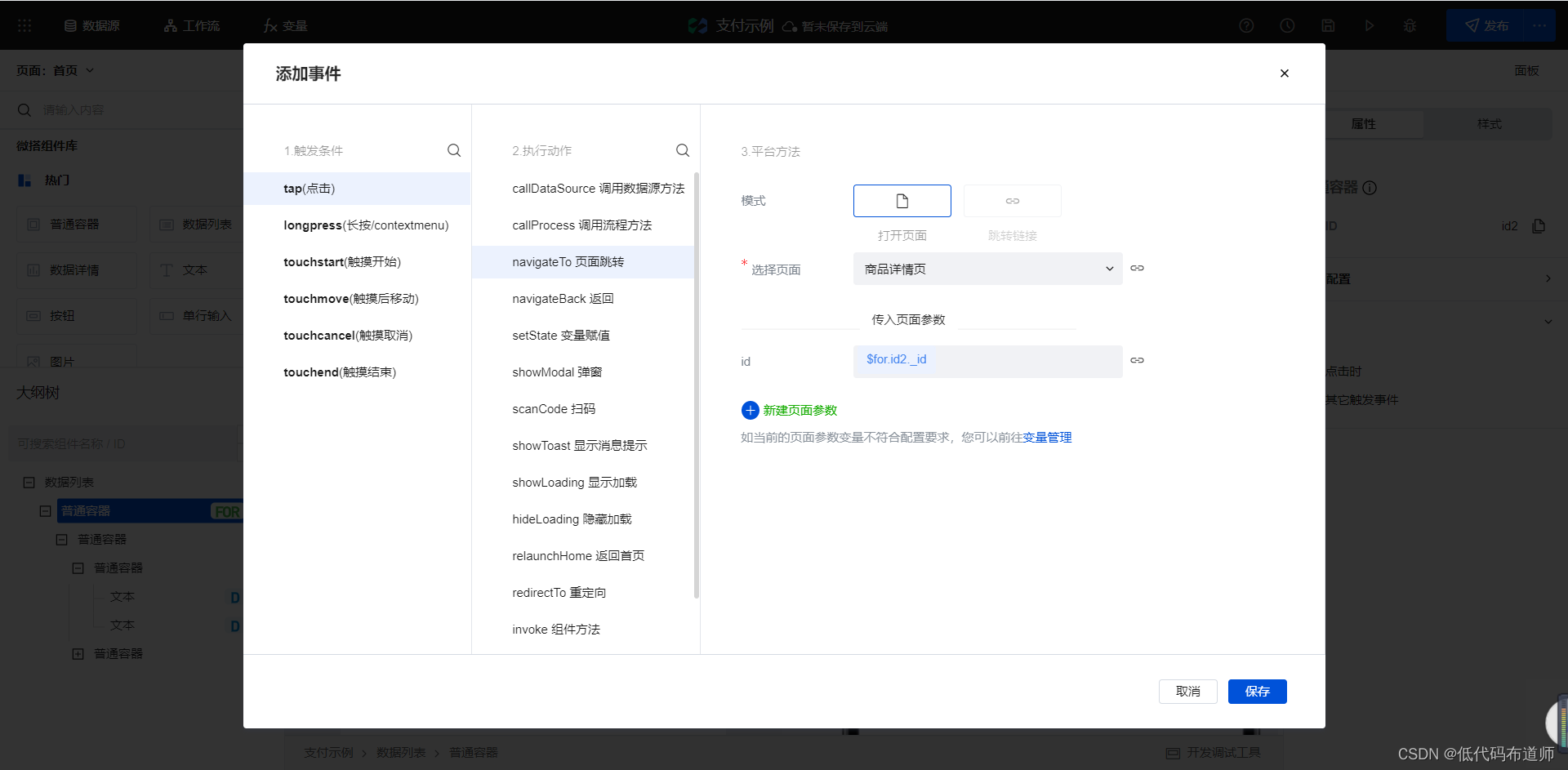
小程序中实现付款功能
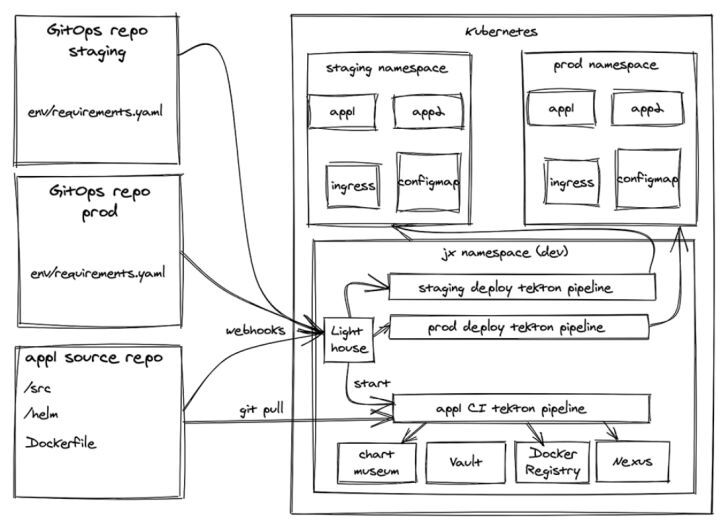
Comparison and selection of kubernetes Devops CD Tools

上市十天就下线过万台,欧尚Z6产品实力备受点赞
随机推荐
五种网络IO模型
财富证券证券怎么开户?通过链接办理股票开户安全吗
nest. Database for getting started with JS
PHP面试题 foreach($arr as &$value)与foreach($arr as $value)的用法
Download, installation and development environment construction of "harmonyos" deveco
Idea completely uninstalls installation and configuration notes
清华、剑桥、UIC联合推出首个中文事实核查数据集:基于证据、涵盖医疗社会等多个领域
【demo】循环队列及条件锁实现goroutine间的通信
Ten thousand words nanny level long article -- offline installation guide for datahub of LinkedIn metadata management platform
Antisamy: a solution against XSS attack tutorial
简单几步教你如何看k线图图解
强化学习-学习笔记8 | Q-learning
万字保姆级长文——Linkedin元数据管理平台Datahub离线安装指南
6.关于jwt
云景网络科技面试题【杭州多测师】【杭州多测师_王sir】
Save the memory of the model! Meta & UC Berkeley proposed memvit. The modeling time support is 30 times longer than the existing model, and the calculation amount is only increased by 4.5%
“解密”华为机器视觉军团:华为向上,产业向前
Afghan interim government security forces launched military operations against a hideout of the extremist organization "Islamic state"
单臂路由和三层交换的简单配置
Reinforcement learning - learning notes 8 | Q-learning