当前位置:网站首页>清华、剑桥、UIC联合推出首个中文事实核查数据集:基于证据、涵盖医疗社会等多个领域
清华、剑桥、UIC联合推出首个中文事实核查数据集:基于证据、涵盖医疗社会等多个领域
2022-07-07 16:26:00 【智源社区】

论文地址: https://arxiv.org/pdf/2206.11863.pdf 数据集CHEF Dataset链接: https://github.com/THU-BPM/CHEF
边栏推荐
- Tips for short-term operation of spot silver that cannot be ignored
- 讨论| 坦白局,工业 AR 应用为什么难落地?
- 回归问题的评价指标和重要知识点总结
- 三仙归洞js小游戏源码
- 『HarmonyOS』DevEco的下载安装与开发环境搭建
- js拉下帷幕js特效显示层
- Learn to make dynamic line chart in 3 minutes!
- How to implement safety practice in software development stage
- [4500 word summary] a complete set of skills that a software testing engineer needs to master
- Chapter 2 build CRM project development environment (database design)
猜你喜欢
![[论文分享] Where’s Crypto?](/img/27/9b47bfcdff8307e63f2699d6a4e1b4.png)
[论文分享] Where’s Crypto?

上市十天就下线过万台,欧尚Z6产品实力备受点赞
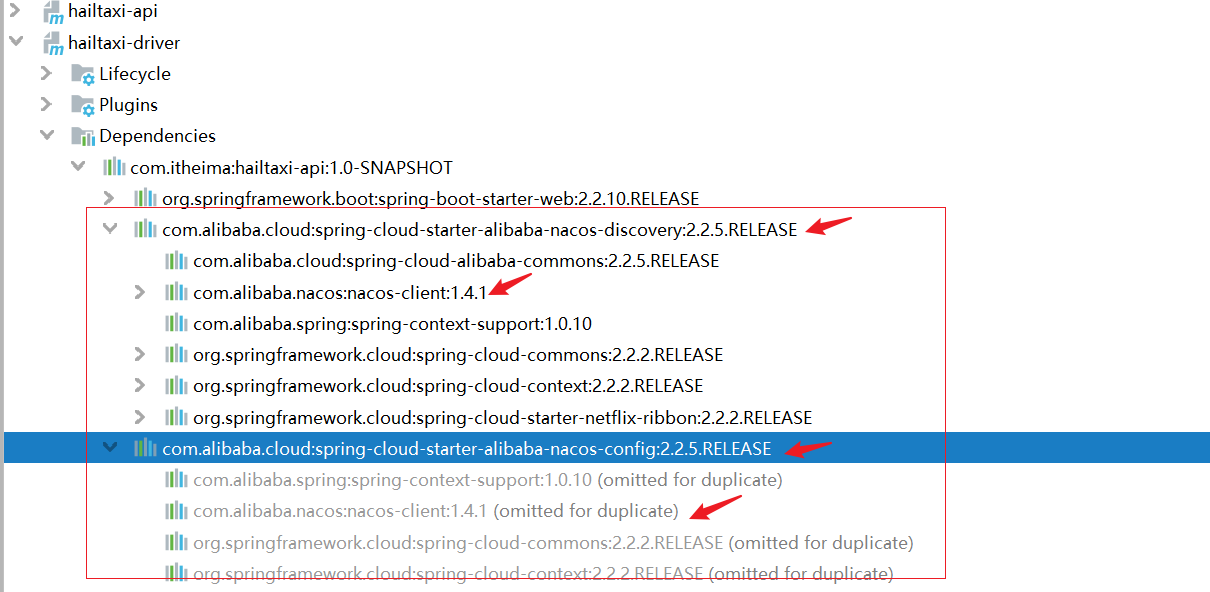
手撕Nacos源码(先撕客户端源码)

Mobile pixel bird game JS play code

通过 Play Integrity API 的 nonce 字段提高应用安全性

元宇宙带来的创意性改变
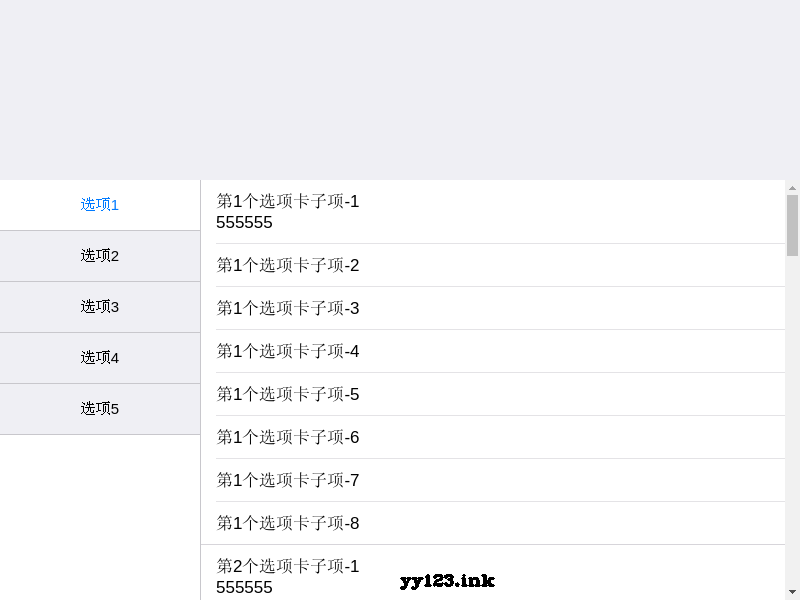
Mui side navigation anchor positioning JS special effect
![[principle and technology of network attack and Defense] Chapter 6: Trojan horse](/img/2f/bd35ca141fad5c85f78fd6340ada1d.png)
[principle and technology of network attack and Defense] Chapter 6: Trojan horse

现货白银分析中的一些要点
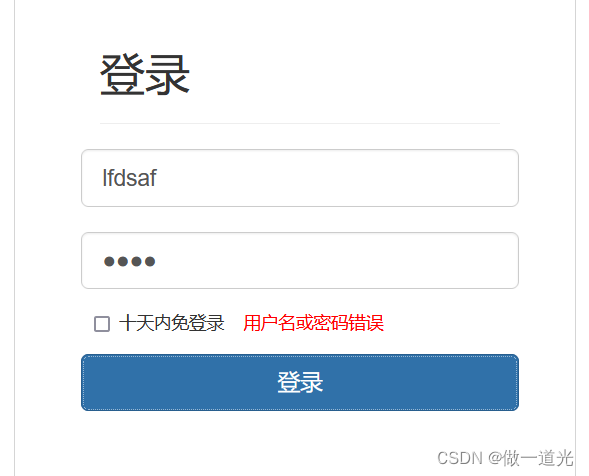
Chapter 3 business function development (user login)
随机推荐
Hash, bitmap and bloom filter for mass data De duplication
讨论 | AR 应用落地前,要做好哪些准备?
The report of the state of world food security and nutrition was released: the number of hungry people in the world increased to 828million in 2021
Target detection 1 -- actual operation of Yolo data annotation and script for converting XML to TXT file
Performance test process and plan
[deep learning] 3 minutes introduction
Tear the Nacos source code by hand (tear the client source code first)
go语言的字符串类型、常量类型和容器类型
Click on the top of today's headline app to navigate in the middle
SD_DATA_SEND_SHIFT_REGISTER
[principle and technology of network attack and Defense] Chapter 7: password attack technology Chapter 8: network monitoring technology
Introduction to OTA technology of Internet of things
C语言中匿名的最高境界
Using stored procedures, timers, triggers to solve data analysis problems
Explain it in simple terms. CNN convolutional neural network
Self made dataset in pytoch for dataset rewriting
Mobile pixel bird game JS play code
[principles and technologies of network attack and Defense] Chapter 5: denial of service attack
上市十天就下线过万台,欧尚Z6产品实力备受点赞
Hutool - 轻量级 DB 操作解决方案