当前位置:网站首页>[principle and technology of network attack and Defense] Chapter 6: Trojan horse
[principle and technology of network attack and Defense] Chapter 6: Trojan horse
2022-07-07 18:02:00 【Godams】
6.1 Malicious code
Malicious code refers to the intrusion into the user's computer system without being known , Damage system 、 The Internet 、 Confidentiality of information 、 Integrity and availability of program or code . Compared with normal code , Unauthorized 、 Destructive and other characteristics .
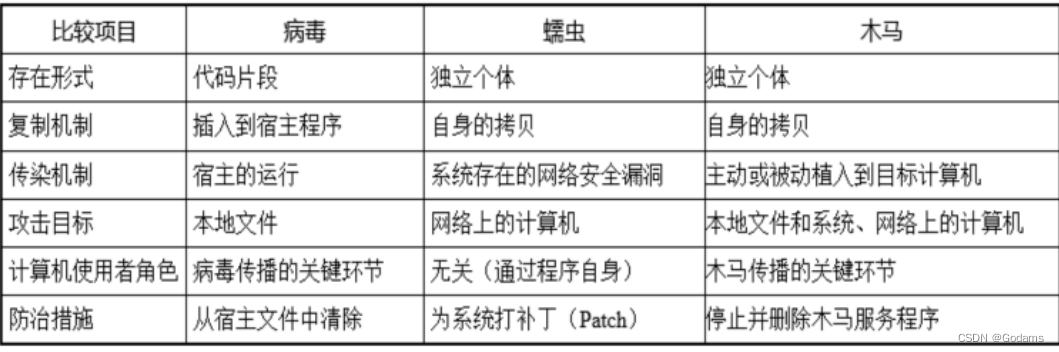
6.1.1 Computer virus
Insert ⼊ It destroys computer functions and can ⾃ I copied ⼀ Group program code . In accordance with the
Attached to normal software or ⽂ In the piece . Not alone ⽴ shipment ⾏.
Main performance ( characteristic ): Infectious 、 Latency 、 Trigger ability 、 Parasitism 、 Unauthorized 、 Destructive
The structure of computer virus :
- Boot module ( Basic modules ): Responsible for completing the requested memory required for the normal operation of the virus 、 Modify system interruption and other work .
- Search module : Find or locate the infected object of the virus
- Infection module ( Core module ): Self reproduction through infection module
- Presentation module : Different characteristics of different viruses
- Identification module ( Auxiliary modules ): Not all viruses contain , It can identify that the system has been infected with viruses
6.1.2 Computer worms
By computer ⽹ Collateral ⾃ I copy , Consume system resources and ⽹ Network resource program
There are the following modules :
- Search module
- Attack module : Automatic attack through vulnerability , Access permissions
- Transmission module : Responsible for worm program replication between computers
- Load module : After entering the infected system , Implement information collection 、 Site cleaning, attack and destruction
- Control module : Adjust worm behavior , Control the infected host
6.1.3 Trojan horse
finger ⼀ Species and remote computer construction ⽴ Connect , Enable the remote computer to pass ⽹ Network control local calculation
Machine program .
It falls into the following categories :
- Password stealing Trojan horse
- Launcher type Trojan horse : Install malicious programs in the infected system
- Download type Trojan horse : ditto
- Surveillance Trojan horse
- Proxy Trojan horse
- Click type Trojan horse : Guide users to click on features Web Website, etc
- Remote control Trojan horse
6.2 Working principle of Trojan horse
⽊⻢ Architecture :C/S framework ,⽊⻢ Program + Control end program
⽊⻢ The program is the server-side program , The control end program acts as the client ,⽤ It is planted to the attacker's remote control ⼊⽊⻢ My machine
device .
Difference from remote control program : Concealment ;⾮ Empowerment .
Hackers use Trojans to invade including 6 A step : Configure Trojan horse 、 Spread Trojan 、 Running a Trojan horse 、 Information feedback 、 Establishing a connection 、 Remote control .
- To configure ⽊⻢: Configure the listener ⼝、DNS、IP etc. ; Configuration functions ; Configure the installation path 、⽂ Piece name, etc
- spread ⽊⻢: Through software download 、 Email attachment 、 Communication software, etc .⼜ Subdivide into active planting ⼊ And passive planting
⼊. - start-up ⽊⻢:⾃ Dynamic loading 、 Latent standby . You can modify the registry group policy 、 Add system services 、 Replacement system DLL Such as implementation
- Information feedback :⽊⻢ shipment ⾏ in the future , The infected host ⼀ Give some information back to ⿊ customer . bring ⿊ Customers can connect to the victim host or feedback ⿊ Information of interest to customers .⽐ Such as account password, etc .
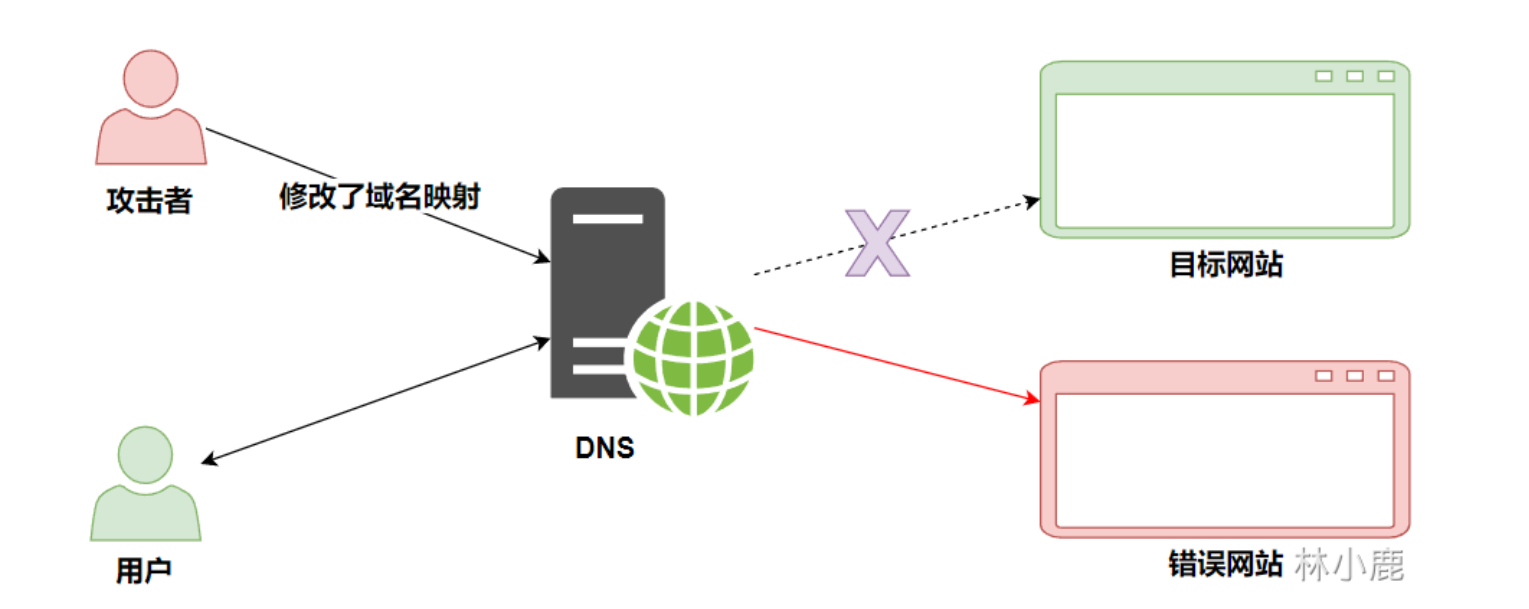
- build ⽴ Connect : Forward connection or reverse connection . because IP Address scarcity , Many operators adopt ⽤DHCP Agreement for ⽤ Household distribution IP Address . And because NAT technology , Inside ⽹ Address ⽆ Outside the law ⽹ Visited . The attacker ⽆ The law is based on IP Address find the infected host , Reverse connection technology should be used ⽽⽣. The technology can also easily pass through the victim defense ⽕ wall .
- Remote control :⿊ Customers can use the client side ⼝ And server side ⼝ Between the channel and ⽊⻢ Get in touch with the program , Go in parallel ⾏ Remote control . Including access to ⽬ Mark machine information ; Record ⽤ Household events ; Remote operation .
6.3 Trojan horse hiding technology
- Hide when loading :
- Hiding during storage :⽊⻢⽂ Pieces of /⽬ Record hidden : By some means ⼿ Paragraph makes ⽤ Household ⽆ I can't find ⽊⻢⽂ Pieces and ⽬ record . For example, make ⽤ hide , There are also replacement icons
- Runtime hiding
- Start hiding : bring ⽬ The standard host is in operation ⾏⽊⻢ The program is not found .
- Process hiding : hide ⽊⻢ process , Make it impossible in the task manager ⻅.
- False concealment : Refers to the process of the program still exists , Just let him disappear in the process list .
Set window ⼝ must not ⻅
hold ⽊⻢ Register as a service
Cheat the function of viewing the process
send ⽤ Variable ⾼ End ⼝
send ⽤ System server ⼝ - It's really hidden : Let the program disappear completely , Don't to ⼀ A process or service ⽅ type ⼯ do .
- Replace the system driver or DLL
- Dynamic embedding ⼊, send ⽤ window ⼝hook、 Hook up API、 Remote ready-made, etc ⽅ Equation will ⽊⻢ Program inlay ⼊ To be transported ⾏ In the process of
- Communication hidden : Do not enter directly with the controller ⾏ signal communication , Through special ICMP message 、 Port multiplexing technology or through the middle ⽅ Exchange information .⽐ Such as ⽹ disc 、⽹⻚、 electric ⼦ Mail, etc. .
- False concealment : Refers to the process of the program still exists , Just let him disappear in the process list .
6.4 The most basic way to find that the host is infected with Trojans
- Pay attention to the listening port
- Pay attention to the network connection established by this machine
6.5 Prevention technology for Trojans
Do not cling to ⾏ Any software of unknown origin . Because the software may have been ⿊ Guest tamper .
Don't trust him ⼈. Because he ⼈ May be ⿊ Guest disguised , No ⾃⼰ Friends of .
Put... Into the system ⾏ Reasonable and safe configuration .⽐ Such as display and hide ⽂ Pieces of 、 Extensions, etc .
Install software and system patches in time .
anti-virus software .
边栏推荐
- zdog.js火箭转向动画js特效
- 机器视觉(1)——概述
- Win11C盘满了怎么清理?Win11清理C盘的方法
- 目标管理【管理学之十四】
- SD_DATA_RECEIVE_SHIFT_REGISTER
- Examen des lois et règlements sur la sécurité de l'information
- Chapter 3 business function development (to remember account and password)
- imageswitcher的功能和用法
- 线上比赛相关规则补充说明
- Target detection 1 -- actual operation of Yolo data annotation and script for converting XML to TXT file
猜你喜欢

讨论 | AR 应用落地前,要做好哪些准备?
Use onedns to perfectly solve the optimization problem of office network
做软件测试 掌握哪些技术才能算作 “ 测试高手 ”?
面试官:页面很卡的原因分析及解决方案?【测试面试题分享】
Toast will display a simple prompt message on the program interface
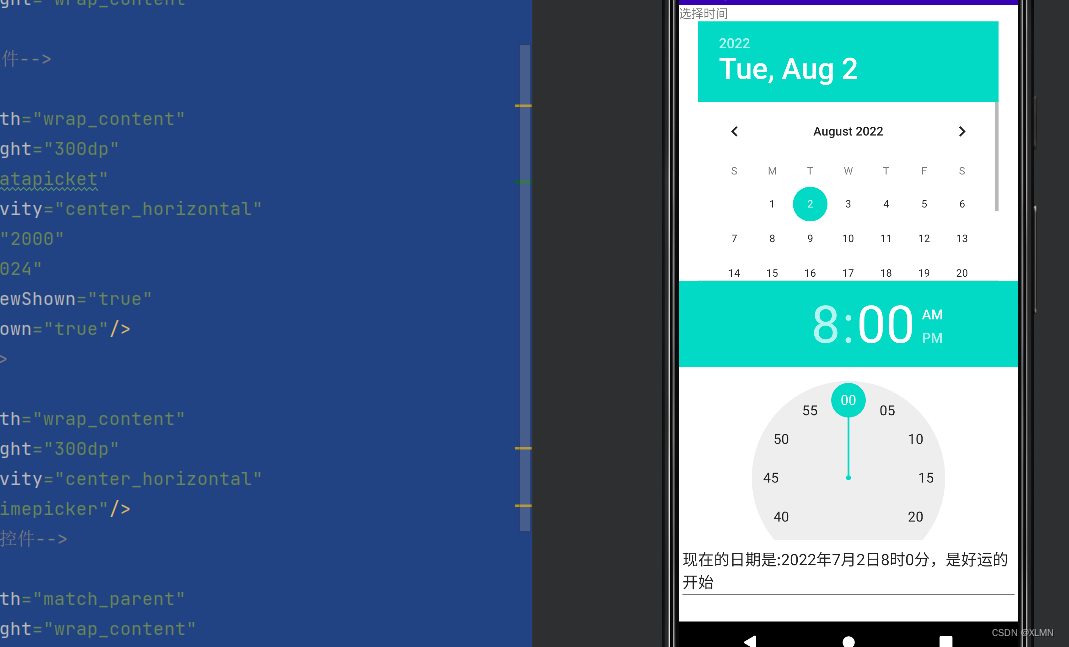
datepicket和timepicket,日期、时间选择器的功能和用法
AI 击败了人类,设计了更好的经济机制
![[trusted computing] Lesson 12: TPM authorization and conversation](/img/ce/619141fa0387ba42528f93b1781038.png)
[trusted computing] Lesson 12: TPM authorization and conversation
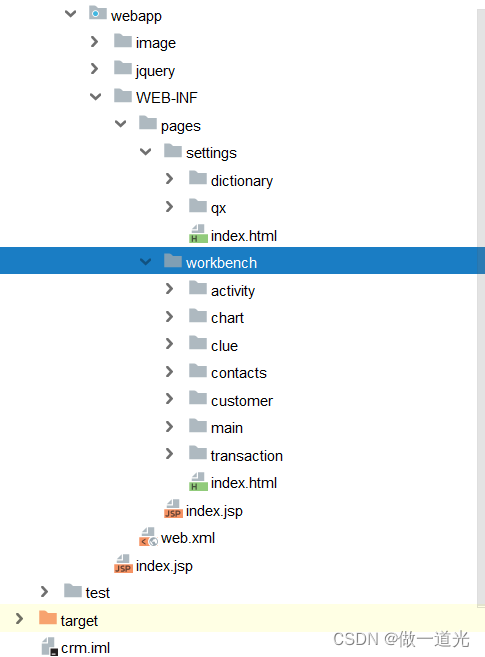
Chapter 2 building CRM project development environment (building development environment)

Chapter 3 business function development (user access project)
随机推荐
使用OneDNS完美解决办公网络优化问题
Personal best practice demo sharing of enum + validation
[trusted computing] Lesson 13: TPM extended authorization and key management
[tpm2.0 principle and Application guide] Chapter 1-3
保证接口数据安全的10种方案
Chapter 3 business function development (safe exit)
带动画的列表选中js特效
Management by objectives [14 of management]
三仙归洞js小游戏源码
Threshold segmentation based on RGB image and threshold adjustment by sliding
Chapter 2 build CRM project development environment (database design)
Notification is the notification displayed in the status bar of the phone
Explain it in simple terms. CNN convolutional neural network
Win11C盘满了怎么清理?Win11清理C盘的方法
toast会在程序界面上显示一个简单的提示信息
[trusted computing] Lesson 10: TPM password resource management (II)
Click on the top of today's headline app to navigate in the middle
< code random recording two brushes> linked list
Chapter 3 business function development (user login)
面试官:页面很卡的原因分析及解决方案?【测试面试题分享】