当前位置:网站首页>Leetcode-1. Sum of two numbers (Application of hash table)
Leetcode-1. Sum of two numbers (Application of hash table)
2022-07-05 12:20:00 【A finger leaf next to the giant】
Preface :
stay Leetcode First simple question - The sum of two numbers algorithm problem , I directly took violence to solve two levels for Cycle to solve the problem , Next, I'm in the discussion area , See a new solution , Take advantage of Map Containers , And in further understanding Map Container found , original Map Containers -hash_map The bottom of the set is the hash table , Hash table , This enables us to learn hash tables with java Medium hasMap Gather and associate to understand .
Let's look at the original question :
Given an array of integers nums And an integer target value target, Please find... In the array And is the target value the Two Integers , And return their array subscripts . You can assume that each input corresponds to only one answer . however , The same element in an array cannot be used twice .
You can return the answers in any order .
source : Power button (LeetCode)
First of all, mine
Violence solution :
The idea is easy to understand , It is through for The loop first determines a number , And then again for Whether the number after loop traversal is equal to the difference between its target value and the determined number .
class Solution {
public int[] twoSum(int[] nums, int target) {
int []a=new int[2];
int middle;
for(int i=0;i<nums.length;i++){
middle=target-nums[i];
for(int j=i+1;j<nums.length;j++){
if(nums[j]==middle){
a[0]=i;
a[1]=j;
return a;
}
}
}
return a;
}
}
Complexity analysis
Time complexity :O(N^2) among N Is the number of elements in the array . In the worst case, any two numbers in the array must be matched once .
Spatial complexity :O(1).
then , In the discussion area , It was proposed , Its comparison obviously has many repetitive results , In order to make every time for Cycles are more meaningful . We store the compared value and the corresponding subscript into hasMap Collection , And in the hasMap The efficiency of searching in the set is very high . Therefore, it introduces Map Concept of container .
about Map If the container has something you don't understand , Take a look at this article : Map Interpretation of container
Hash solution
It mainly uses hasMap aggregate , stay hasMap The query time complexity in the set is constant , Although it consumes a lot of memory space , But it has a good performance in terms of time efficiency .
class Solution {
public int[] twoSum(int[] nums, int target) {
Map<Integer,Integer> map = new HashMap<>();
int[] result = new int[2];
for (int i = 0; i < nums.length; i++) {
if(map.containsKey(target - nums[i])){
result[0] = i;
result[1] = map.get(target - nums[i]);
return result;
}
map.put(nums[i],i);
}
return result;
}
}
Complexity analysis
Time complexity :O(N), among N Is the number of elements in the array . because hasMap The query time complexity in the set is constant , For each element x, We can O(1) Looking for target - x.
Spatial complexity :O(N), among N Is the number of elements in the array . Mainly for the cost of hash table .
边栏推荐
- Check the debug port information in rancher and do idea remote JVM debug
- [pytorch pre training model modification, addition and deletion of specific layers]
- Understand redis persistence mechanism in one article
- Tabbar configuration at the bottom of wechat applet
- [untitled]
- The evolution of mobile cross platform technology
- MySQL log module of InnoDB engine
- Correct opening method of redis distributed lock
- 2022年国内云管平台厂商哪家好?为什么?
- 只是巧合?苹果 iOS16 的神秘技术竟然与中国企业 5 年前产品一致!
猜你喜欢
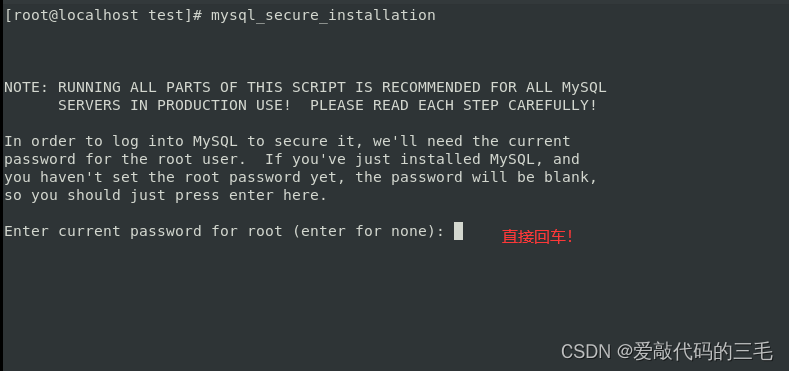
Linux Installation and deployment lamp (apache+mysql+php)
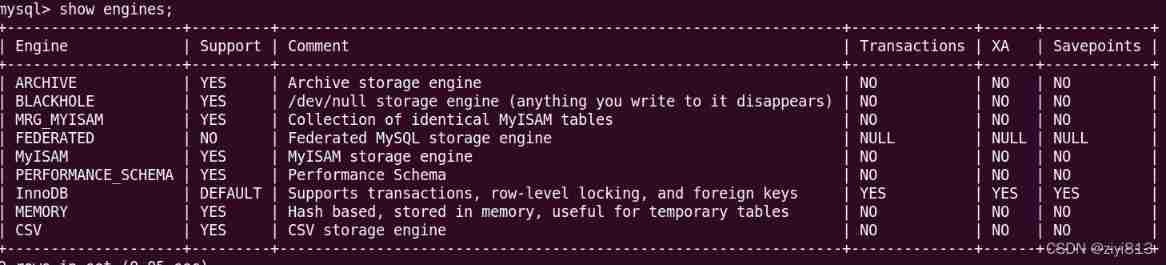
MySQL storage engine
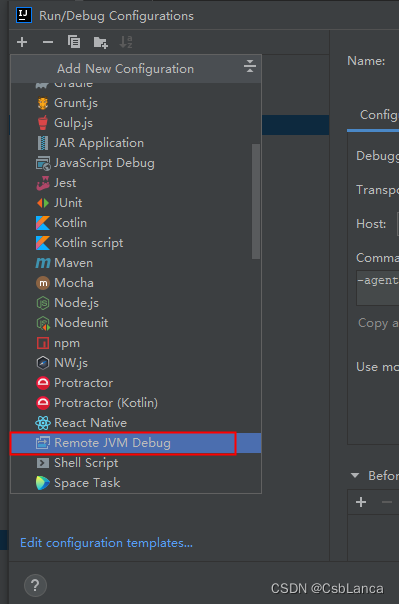
查看rancher中debug端口信息,并做IDEA Remote Jvm Debug
调查显示传统数据安全工具在60%情况下无法抵御勒索软件攻击
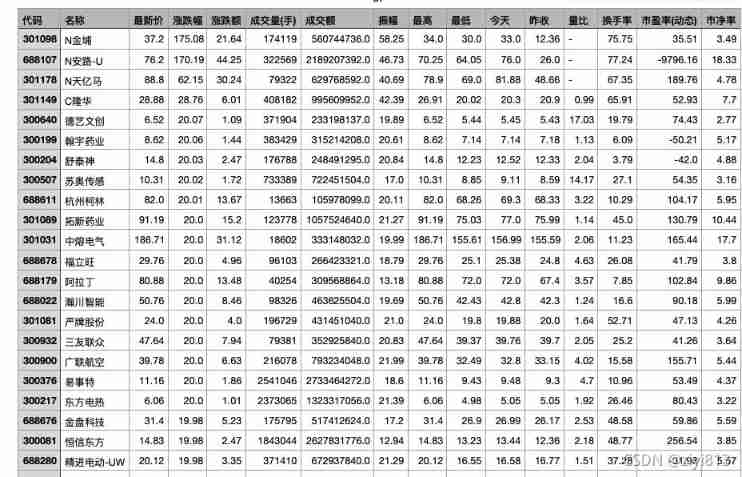
Get all stock data of big a
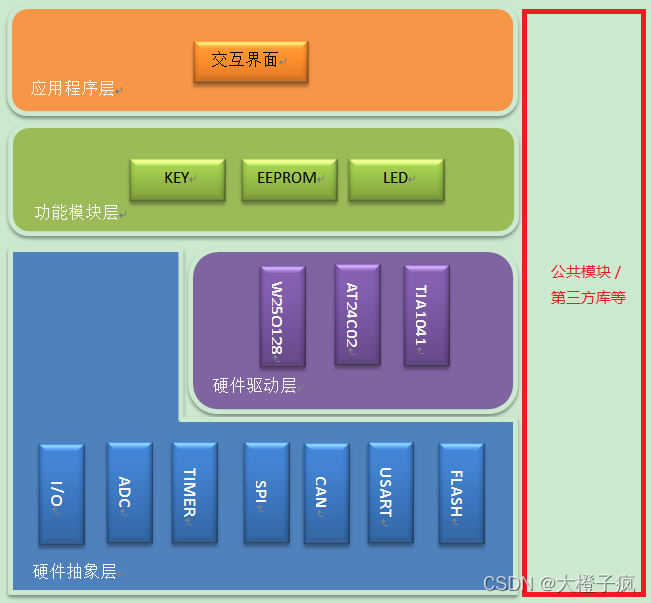
嵌入式软件架构设计-消息交互
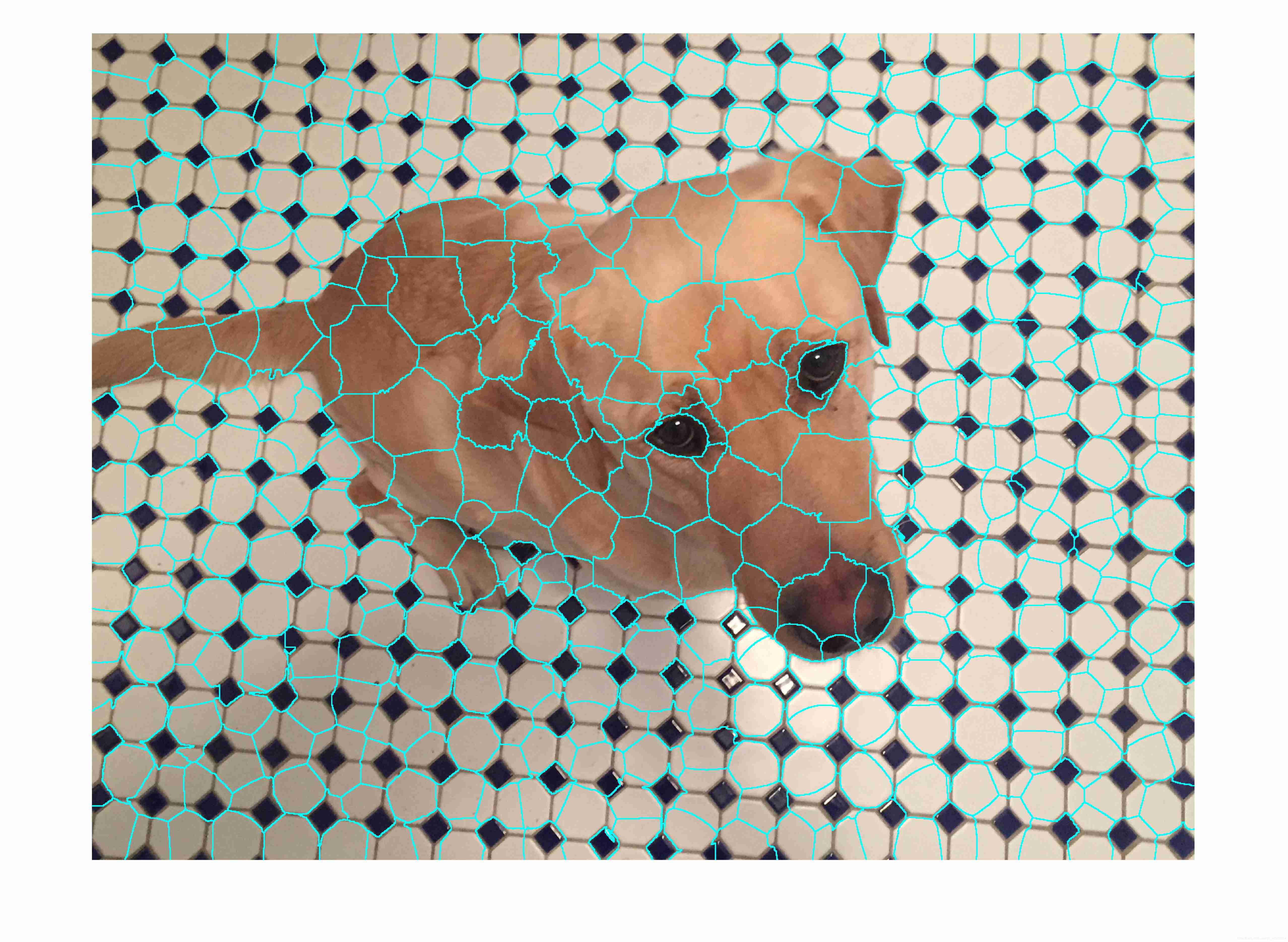
Matlab superpixels function (2D super pixel over segmentation of image)
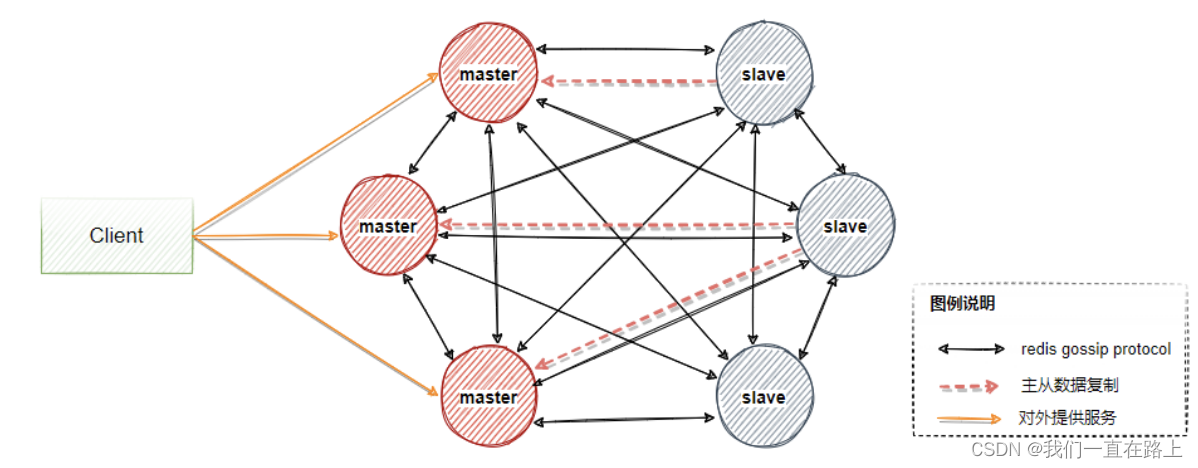
Principle of redis cluster mode
![[pytorch modifies the pre training model: there is little difference between the measured loading pre training model and the random initialization of the model]](/img/ad/b96e9319212cf2724e0a640109665d.png)
[pytorch modifies the pre training model: there is little difference between the measured loading pre training model and the random initialization of the model]
![[untitled]](/img/56/6a9a4bcab6503872942fff7a365def.jpg)
[untitled]
随机推荐
Solve the problem of cache and database double write data consistency
Hash tag usage in redis cluster
Take you hand in hand to develop a service monitoring component
Sentinel sentinel mechanism of master automatic election in redis master-slave
MySQL trigger
Read and understand the rendering mechanism and principle of flutter's three trees
ACID事务理论
Xi IO flow
Just a coincidence? The mysterious technology of apple ios16 is actually the same as that of Chinese enterprises five years ago!
Redis highly available sentinel cluster
MySQL basic operation -dql
Simply solve the problem that the node in the redis cluster cannot read data (error) moved
Matlab struct function (structure array)
POJ-2499 Binary Tree
Automated test lifecycle
Learn garbage collection 01 of JVM -- garbage collection for the first time and life and death judgment
POJ-2499 Binary Tree
[cloud native | kubernetes] actual battle of ingress case (13)
JS for loop number exception
[pytorch pre training model modification, addition and deletion of specific layers]