当前位置:网站首页>"2022" is a must know web security interview question for job hopping
"2022" is a must know web security interview question for job hopping
2022-07-05 01:28:00 【Web frontend】
1、 You are right about WEB The understanding of safety ?
The Internet is developing rapidly , current web It is no longer a simple web page , In addition to the common e-commerce shopping platform 、 Mobile transfer 、 Outside the banking system , The development of Internet of things technology , Not only let smart home into life , It also promotes medical 、 The development of logistics and other industries , Security has gradually become a matter of concern .
As a front-end programmer, I am most concerned about web It's safe , The more common and harmful ones are XSS Cross site scripts gongji、SQL Inject 、CSFR Cross Site Request Forgery, etc gongji The way . We need to better understand their malice gongji principle , In order to better defense gongji.

2、XSS Cross site scripts gongji
XSS yes Cross Site Scripting Abbreviation , In order to CSS Make a distinction , So it's called XSS .
XSS gongji Mainly web The page is implanted with malicious script Code , When a user visits a page , Embedded malicious code automatically executes , So as to achieve gongji The effect of .XSS There are three types :
- reflective XSS
- Storage type XSS
- Document type XSS
reflective XSS When making a network request , malice gongji The code appears in url in , Submit as input to the server , The server returns to the browser , Browser execution XSS Code , This process is like a reflection , So it's called reflective XSS gongji.
http://www.xxx.com?q=<script>alert(" Malicious script ")</script>
or
http://www.xxx.com?n=<img sec="1 onerror=alert(' Malicious code ')">
- 1.
- 2.
- 3.
Storage type XSS It's submitted XSS The code is stored in the server's database 、 In memory or file system , Don't submit again the next time you request the target page XSS Code . Common in user input .
Document type XSS It doesn't go through the server , As a middleman , Hijacking network packets during data transmission , Then modify the html file .
XSS More harm , It is common to steal accounts 、 Steal business value information, etc . So we need to take some defensive measures to protect the rights and interests of users , For the above three gongji The way , There are three corresponding defensive measures , Respectively :
- Escape coding between client and server
<script>alert(' Malicious code ')</script>
- 1.
After escaping the code, the editor will reprocess it for you , Students who don't know can try it by themselves !
- Filter out dangerous nodes , Such as script、style、link、iframe .
- utilize CSP
Content Security Policy Content security policy , You can specify the whitelist of resources that can be loaded on the current web page , So as to reduce the impact of web pages XSS gongji The risk of .
3、CSRF How to defend, you know ?
CSFR yes cross site request forgery , The Chinese name is cross site request forgery . Also known as :one click attack/session riding, Abbreviation for :CSRF / XSRF.
CSRF Mainly gongji The identity of the user is stolen , Malicious operation in the name of the user , It is easy to cause personal privacy disclosure and property security problems , therefore CSRF Our defense measures cannot be less , You can start from both server and client , Its defense methods are as follows :
- Check http The head of the referer Information
- Use a one-time token
- Key operations use POST request
- Use verification code
The specific defensive measures are :
1>、 Check http The head of the referer Information
referer Included in http Request header , Indicates the page source of the request interface , The server passes the check referer Information , Intercept the request when it is found that it comes from a foreign domain , Block unknown requests , To some extent, it can reduce gongji.
2>、 Use a one-time token
Use a one-time token for identification ,heike You cannot get a one-time token across domains , Therefore, the server can judge whether to carry a one-time token , Some illegal operators can be excluded .
3>、 Key operations use POST request
Sensitive operations use POST request , It is mainly to prevent user sensitive information from appearing in url in , Easy to reveal important information .
4>、 Use verification code
CSRF gongji Basically, it occurs when users don't know , Secretly send network requests when users are not aware , If verification code is used , It needs to be verified every time important operations are carried out , Thus, the defense is simple and effective CSRF gongji.

4、SQL What is injection ?
So-called SQL To inject is to put SQL Insert the statement command into web Query string for form submission or page request , Finally, the malicious execution of the server is achieved SQL command . It is a common WEB Security loudong,gongji People will take advantage of this loudong, You can access or modify data , Leverage potential databases loudong Conduct gongji.
SQL Injection can be divided into the following examples :
- Digital injection
- Character injection
- Other types
SQL Precautions against injection :
- Add regular validation and filtering . Where the user enters , Don't trust user input , Regular expression validation is required for user input .
- Sensitive fields should be encrypted . Confidential and sensitive information cannot be stored directly , Need encryption or hash Drop sensitive information .
- Do not use administrator privileges to connect to the database . Use separate permissions for each application to control limited database connections , Never connect to a database with administrator privileges .
- Dynamic splicing is not allowed SQL sentence . You can use parameterized SQL Or directly use stored procedures for data query access , But don't dynamically splice .
5、DDOS
DDOS yes Distributed Denial of Service Abbreviation , Distributed denial of service .DDOS gongji It refers to the use of customers / Server technology , Combine multiple computers as gongji platform , Launch on one or more targets DDOS gongji, So as to double the denial of service gongji The power of . The gongji The method mainly uses the defect of the network service function of the target system or directly consumes its system resources , Make the target system unable to provide normal services .
DDOS gongji Use a lot of resources through a large number of legitimate requests , In order to achieve the purpose of paralyzing the network , There are several specific forms of expression :
- By overloading the network to interfere with or even block the normal network communication ;
- By submitting a large number of requests to the server , Overload the server ;
- Block a user from accessing the server ;
- Block the communication between a service and a specific system or individual .
6、DNS hijacked
DNS It is to map the network domain name to the one that can be recognized by the real computer IP Address , For further communication .DNS Hijacking is when a user visits a site through a domain name , Tampered with DNS The server returns the of a phishing website IP, Users are hijacked to phishing sites , And reveal privacy .
7、HTTP hijacked
HTTP Hijacking is when a user visits a website , Will pass through the operator , Operators can intercept the content requested to be returned by colluding with black factories , And tamper with the returned content and then return it to the user . Generally, some advertisements will be inserted after the website is hijacked , Seriously, it may be directly modified into phishing websites to steal user information .
Defensive measures :
The identity of the other party and data integrity are not verified in the communication process , So prevent HTTP The only way to hijack is to encrypt the content , So that the hijacker cannot pojie Tampering , This will prevent HTTP Hijacked .
边栏推荐
- 资深测试/开发程序员写下无bug?资历(枷锁)不要惧怕错误......
- Main window in QT application
- 【纯音听力测试】基于MATLAB的纯音听力测试系统
- Research Report on the overall scale, major producers, major regions, products and application segmentation of agricultural automatic steering system in the global market in 2022
- Call Huawei order service to verify the purchase token interface and return connection reset
- 潘多拉 IOT 开发板学习(RT-Thread)—— 实验4 蜂鸣器+马达实验【按键外部中断】(学习笔记)
- Basic operation of database and table ----- the concept of index
- La jeunesse sans rancune de Xi Murong
- 小程序直播 + 电商,想做新零售电商就用它吧!
- Game 280 of leetcode week
猜你喜欢
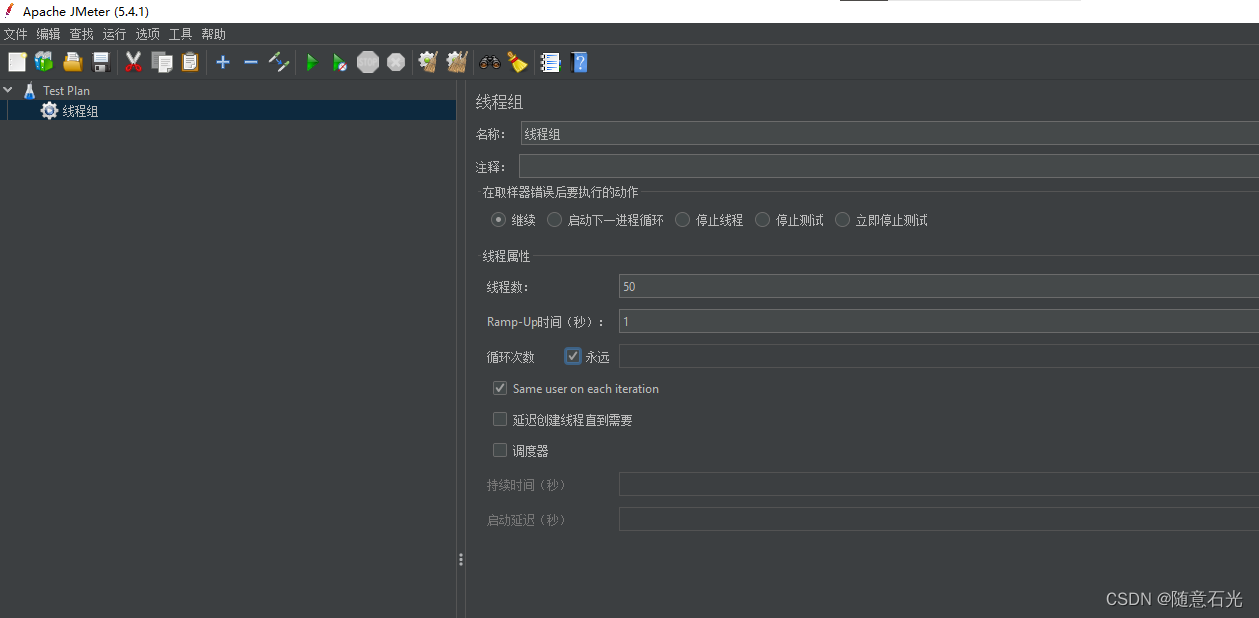
【大型电商项目开发】性能压测-优化-中间件对性能的影响-40
![[flutter topic] 64 illustration basic textfield text input box (I) # yyds dry goods inventory #](/img/1c/deaf20d46e172af4d5e11c28c254cf.jpg)
[flutter topic] 64 illustration basic textfield text input box (I) # yyds dry goods inventory #

Game 280 of leetcode week
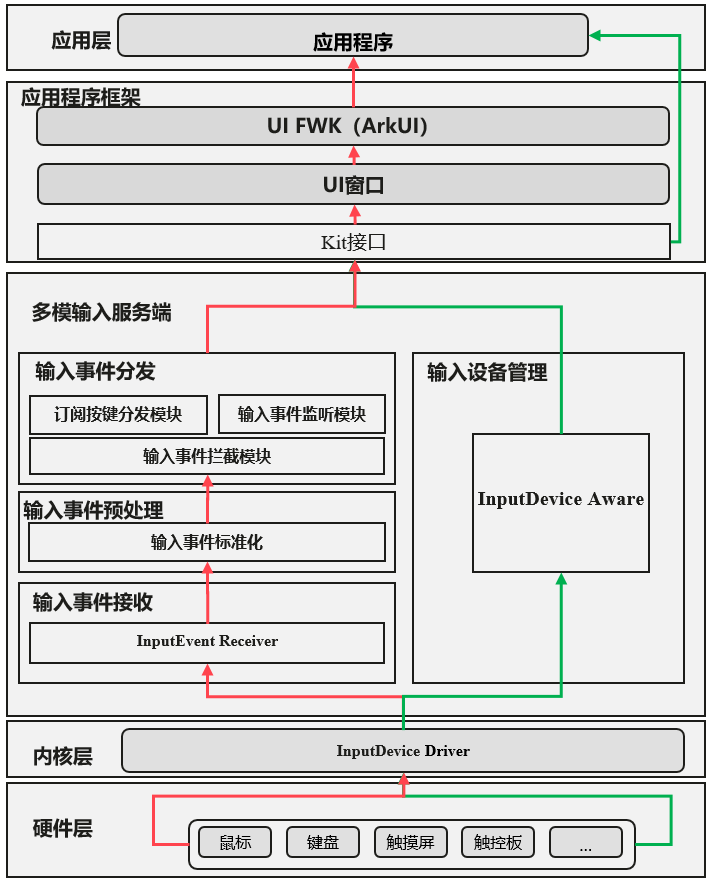
Detailed explanation of multi-mode input event distribution mechanism
![抓包整理外篇——————状态栏[ 四]](/img/88/8267ab92177788ac17ab665a90b781.png)
抓包整理外篇——————状态栏[ 四]
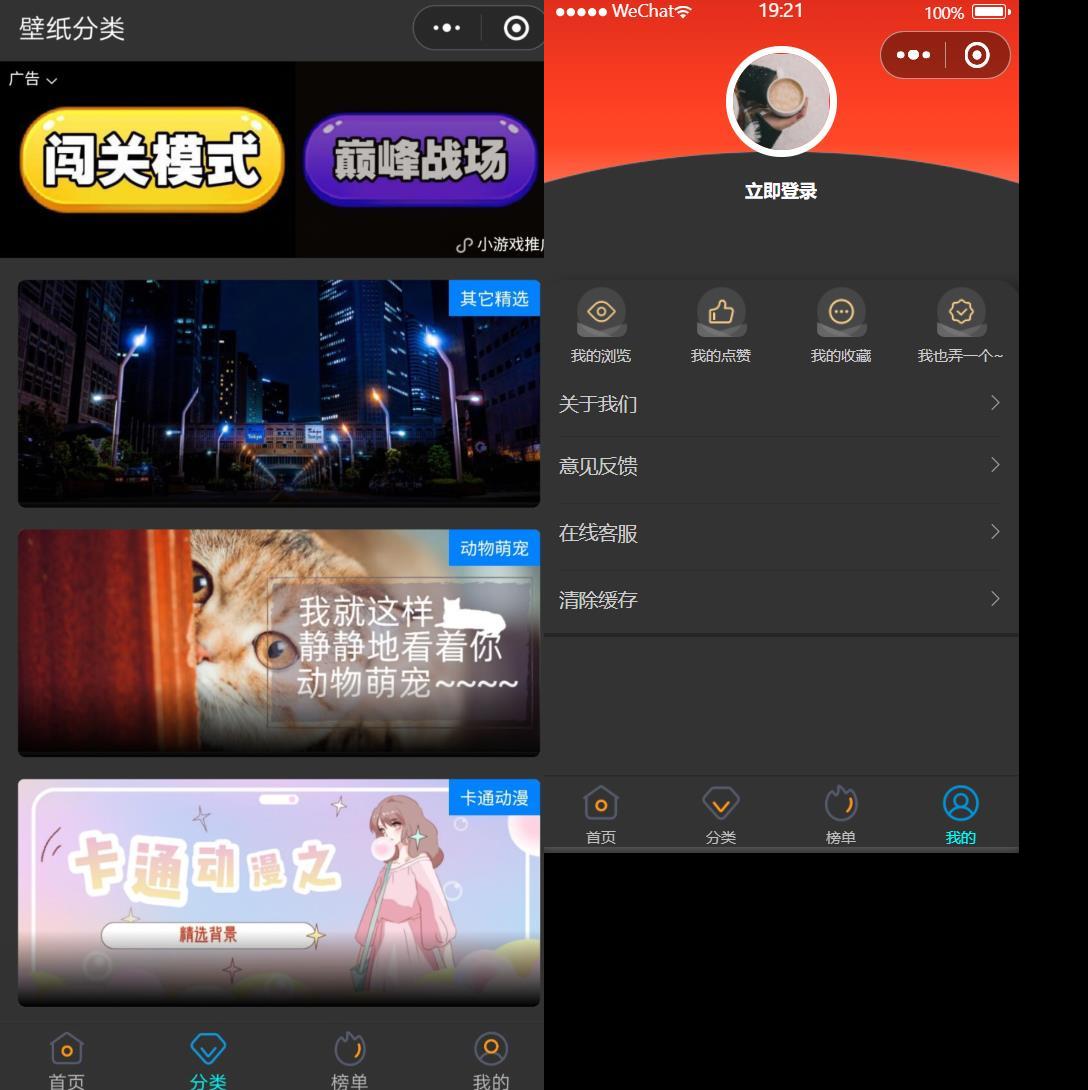
微信小程序:最新wordpress黑金壁纸微信小程序 二开修复版源码下载支持流量主收益
Arbitrum:二维费用
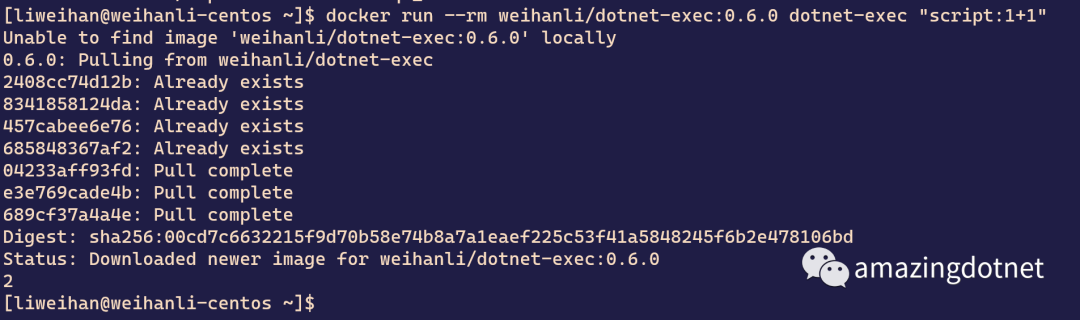
dotnet-exec 0.6.0 released
![[swagger]-swagger learning](/img/60/1dbe074b3c66687867192b0817b553.jpg)
[swagger]-swagger learning
![Grabbing and sorting out external articles -- status bar [4]](/img/88/8267ab92177788ac17ab665a90b781.png)
Grabbing and sorting out external articles -- status bar [4]
随机推荐
[development of large e-commerce projects] performance pressure test - Performance Monitoring - heap memory and garbage collection -39
Database postragesql client connection default
Grabbing and sorting out external articles -- status bar [4]
Arbitrum: two-dimensional cost
[wave modeling 1] theoretical analysis and MATLAB simulation of wave modeling
Poap: the adoption entrance of NFT?
To sort out messy header files, I use include what you use
【FPGA教程案例9】基于vivado核的时钟管理器设计与实现
Basic operations of database and table ----- delete index
19. Delete the penultimate node of the linked list
phpstrom设置函数注释说明
Game 280 of leetcode week
Implementation steps of master detail detail layout mode of SAP ui5 application
Innovation leads the direction. Huawei Smart Life launches new products in the whole scene
Discrete mathematics: reasoning rules
Wechat applet: exclusive applet version of the whole network, independent wechat community contacts
Introduction to redis (1)
Global and Chinese market of veterinary thermometers 2022-2028: Research Report on technology, participants, trends, market size and share
Expansion operator: the family is so separated
How to safely eat apples on the edge of a cliff? Deepmind & openai gives the answer of 3D security reinforcement learning