当前位置:网站首页>Prometheus remote_ write InfluxDB,unable to parse authentication credentials,authorization failed
Prometheus remote_ write InfluxDB,unable to parse authentication credentials,authorization failed
2022-07-07 21:19:00 【leboop-L】
here Prometheus It is started in the following way :
systemctl start prometheus.service
Execute the following command , see Prometheus journal :
journalctl -u prometheus -f
error :unable to parse authentication credentials,authorization failed
see Prometheus The configuration file prometheus.yml, as follows :
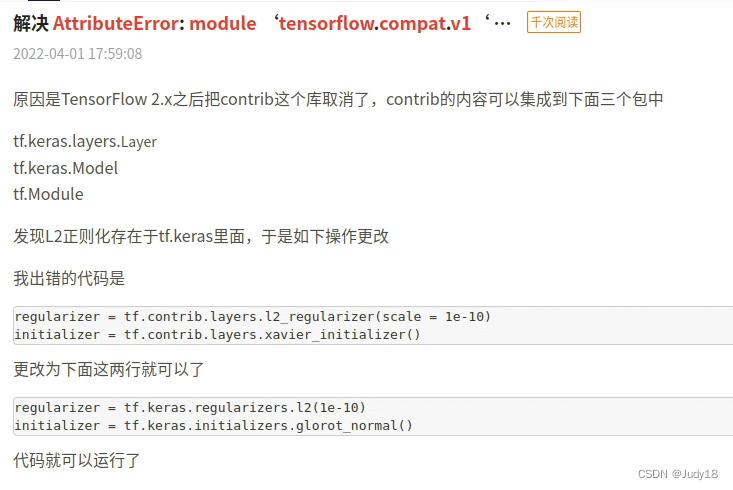
remote_write:
- url: "http://bigdata111:8086/api/v1/prom/write?db=combeye&u=combeye&p=#Wtt2&Me"If you don't study it carefully , Unable to see the problem , It turned out , Because the password contains url Special characters for , For example, here # and &, You need to use code instead of ,# Corresponding code %23,$ Corresponding code %26, It is amended as follows :
remote_write:
- url: "http://bigdata111:8086/api/v1/prom/write?db=combeye&u=combeye&p=%23Wtt2%26Me"success !
边栏推荐
- Validutil, "Rethinking the setting of semi supervised learning on graphs"
- Write a jump table
- AADL inspector fault tree safety analysis module
- Implement secondary index with Gaussian redis
- Using enumeration to realize English to braille
- 【函数递归】简单递归的5个经典例子,你都会吗?
- Can Huatai Securities achieve Commission in case of any accident? Is it safe to open an account
- UVA 12230 – crossing rivers (probability) "suggested collection"
- 私募基金在中国合法吗?安全吗?
- Alibaba cloud award winning experience: how to mount NAS file system through ECS
猜你喜欢
![[paper reading] maps: Multi-Agent Reinforcement Learning Based Portfolio Management System](/img/76/b725788272ba2dcdf866b28cbcc897.jpg)
[paper reading] maps: Multi-Agent Reinforcement Learning Based Portfolio Management System

Small guide for rapid formation of manipulator (12): inverse kinematics analysis

解决使用uni-app MediaError MediaError ErrorCode -5
Tensorflow2.x下如何运行1.x的代码
How to meet the dual needs of security and confidentiality of medical devices?
Static analysis of software defects codesonar 5.2 release
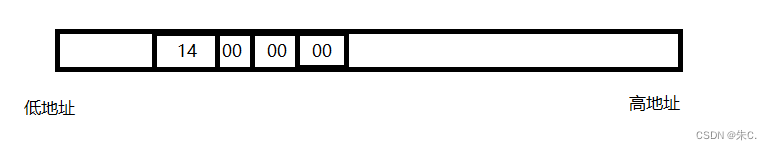
C语言 整型 和 浮点型 数据在内存中存储详解(内含原码反码补码,大小端存储等详解)
![Is embedded system really safe? [how does onespin comprehensively solve the IC integrity problem for the development team]](/img/af/61b384b1b6ba46aa1a6011f8a30085.png)
Is embedded system really safe? [how does onespin comprehensively solve the IC integrity problem for the development team]
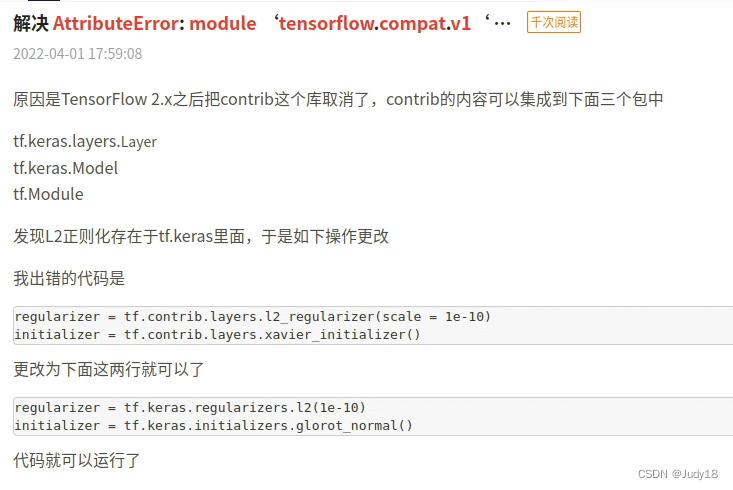
Tensorflow2. How to run under x 1 Code of X
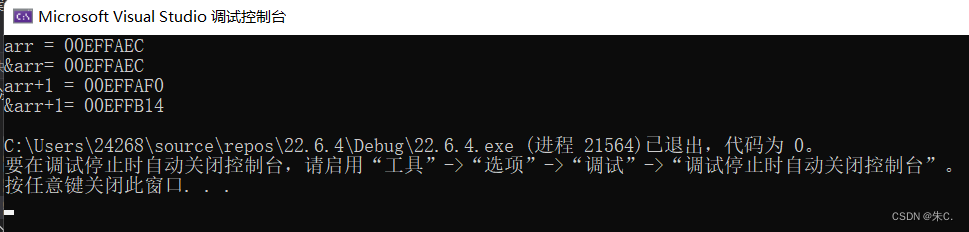
C语言多角度帮助你深入理解指针(1. 字符指针2. 数组指针和 指针数组 、数组传参和指针传参3. 函数指针4. 函数指针数组5. 指向函数指针数组的指针6. 回调函数)
随机推荐
Default constraint and zero fill constraint of MySQL constraint
寫一下跳錶
私募基金在中國合法嗎?安全嗎?
神兵利器——敏感文件发现工具
How can big state-owned banks break the anti fraud dilemma?
Onespin | solve the problems of hardware Trojan horse and security trust in IC Design
95年专注安全这一件事 沃尔沃未来聚焦智能驾驶与电气化领域安全
写一下跳表
The little money made by the program ape is a P!
The difference between NPM uninstall and RM direct deletion
使用高斯Redis实现二级索引
awk处理JSON处理
FatMouse' Trade(杭电1009)
UVA 11080 – place the guards
MinGW MinGW-w64 TDM-GCC等工具链之间的差别与联系「建议收藏」
Is it safe to open an account online now? I want to know where I can open an account in Nanning now?
UVA 12230 – crossing rivers (probability) "suggested collection"
死锁的产生条件和预防处理[通俗易懂]
Flask1.1.4 werkzeug1.0.1 source code analysis: Routing
刚开户的能买什么股票呢?炒股账户安全吗