当前位置:网站首页>Onespin | solve the problems of hardware Trojan horse and security trust in IC Design
Onespin | solve the problems of hardware Trojan horse and security trust in IC Design
2022-07-07 20:27:00 【Maihexong】
stride across 5G, Artificial intelligence , The Internet of things and the automotive sector 40 Several organizations have expressed the importance of trust and security dilemmas .
Electronic systems have increasingly become the core of products and services . From power plants to cars , Medical equipment to the plane , From smart phones to home appliances , Complex electronic systems have achieved unprecedented Automation , performance , Safety and security level . The integrated circuit (IC) It is the foundation of electronic system , And the most important thing is , Need to ensure that they operate in full compliance with specifications and Certification , In this regard, it is trustworthy . but IC The design of the , Production and distribution are vulnerable to attacks by malicious agents , These malicious agents may penetrate devices with poor performance and reliability , Even infiltrate into the hardware Trojan horse , Other hidden functions designed for malicious purposes .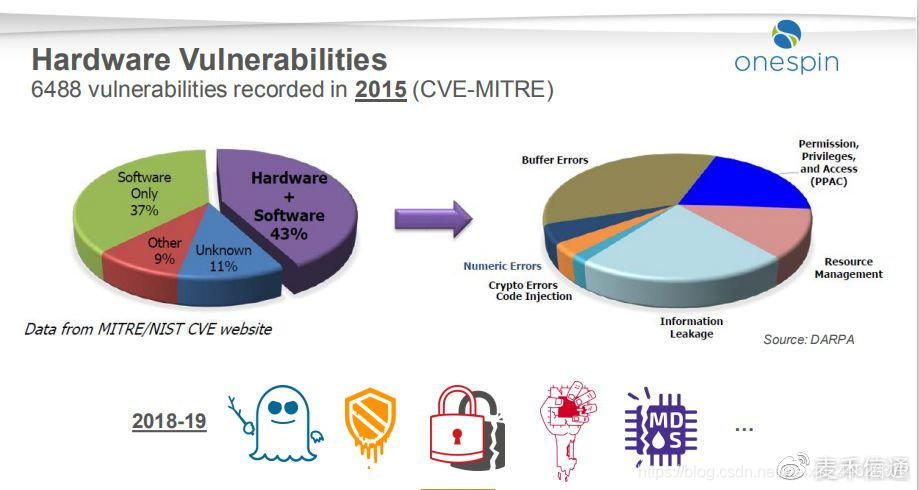
A well-designed hardware Trojan horse , Can respond to triggers known to the attacker , Thus causing significant damage . It may expose “ Security ” data , Cause serious product failure , Even damage the chip . In modern times , Highly configurable hardware is a backdoor 、 Time bomb 、 Provide a good hiding place for the switch to stop or degrade . Like a Trojan horse program being inserted into a third party IP And threats in the design and implementation steps before production , It is increasingly attracting extensive attention in the hardware industry . Networked driverless cars , Medical equipment , A smart phone , Defense and aerospace systems , nuclear power plant ,5G The Internet , Internet of things devices and cloud computing , Everything is at risk here .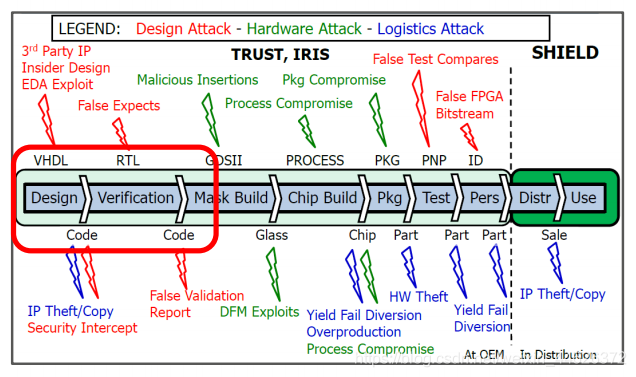
The company is obliged to ensure that electronic equipment is protected from security attacks that may cause great harm .OneSpin Hardware trust and security challenges illustrate , Face hidden in the whole IC Trojans in the development phase , How fragile the design is , meanwhile , It also tells us how to fight it .
 About OneSpin Solutions for
About OneSpin Solutions for
OneSpin President and CEO Raik Brinkmann mention : Now more and more companies realize that , The importance of protecting hardware design from trust and security risks . The loopholes left in the design , Whether unintentional or malicious , Can have disastrous consequences . Be able to fully detect these in the design “ Loophole ”, For delivering security to the market , Reliable and trustworthy equipment is essential . As IC Part of integrity , In terms of ensuring trust and security at the hardware level ,OneSpin The technical services provided have always been at the forefront of the industry .”
More details and white papers :http://www.softtest.cn
边栏推荐
- Optimization cases of complex factor calculation: deep imbalance, buying and selling pressure index, volatility calculation
- rk3128投影仪lcd显示四周显示不完整解决
- [philosophy and practice] the way of program design
- One click deployment of any version of redis
- Nebula importer data import practice
- Oracle 存储过程之遍历
- Update iteration summary of target detection based on deep learning (continuous update ing)
- How C language determines whether it is a 32-bit system or a 64 bit system
- How does codesonar help UAVs find software defects?
- I wrote a markdown command line gadget, hoping to improve the efficiency of sending documents by garden friends!
猜你喜欢
【mysql篇-基础篇】事务

Measure the height of the building
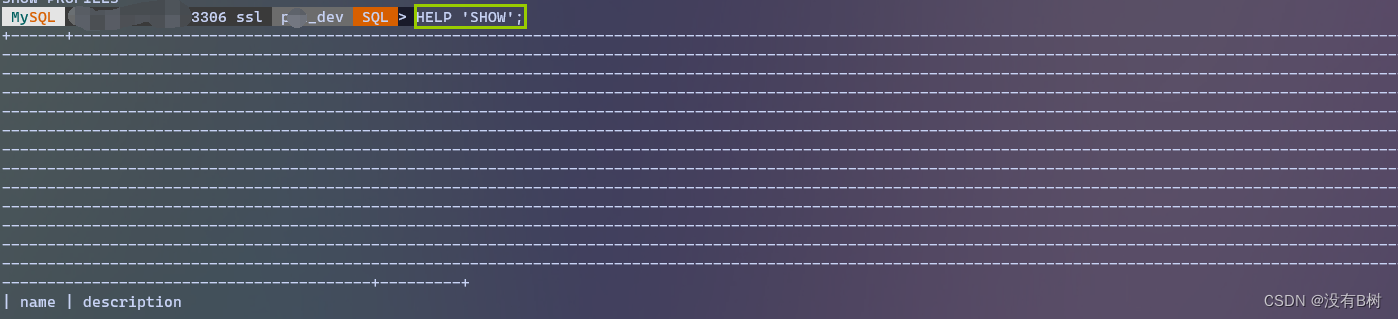
ERROR: 1064 (42000): You have an error in your SQL syntax; check the manual that corresponds to your
Klocwork code static analysis tool
Klocwork 代码静态分析工具
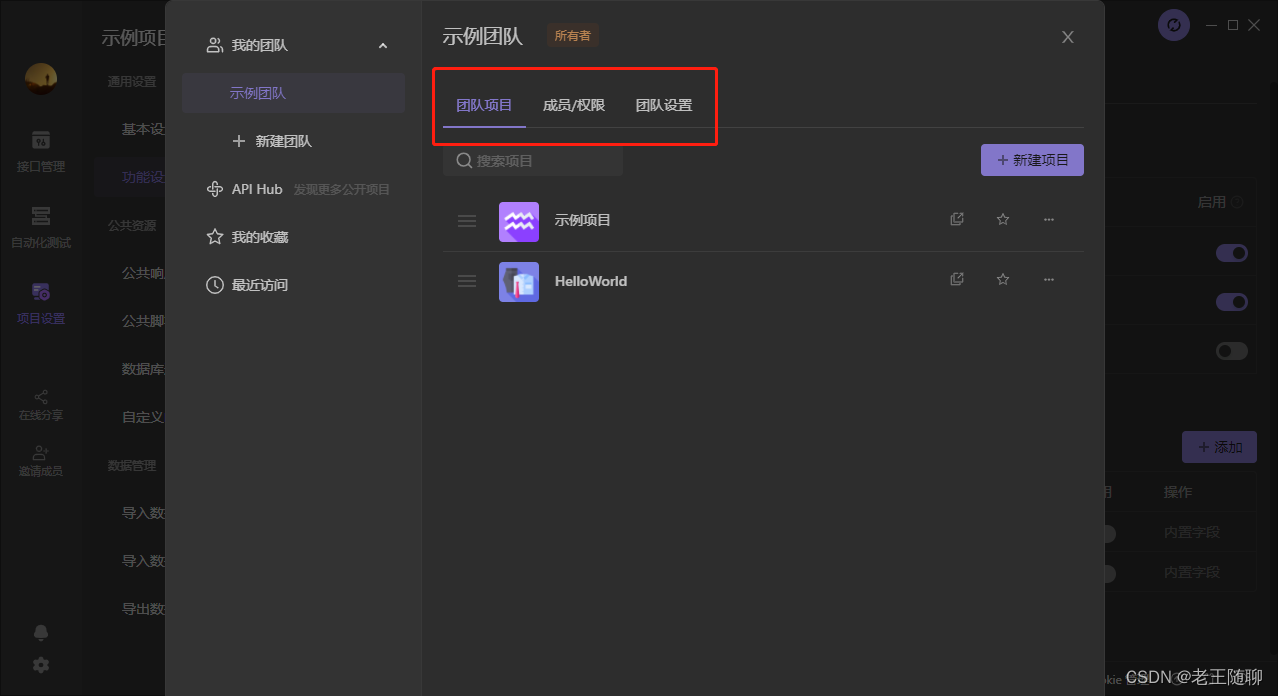
Apifox interface integrated management new artifact
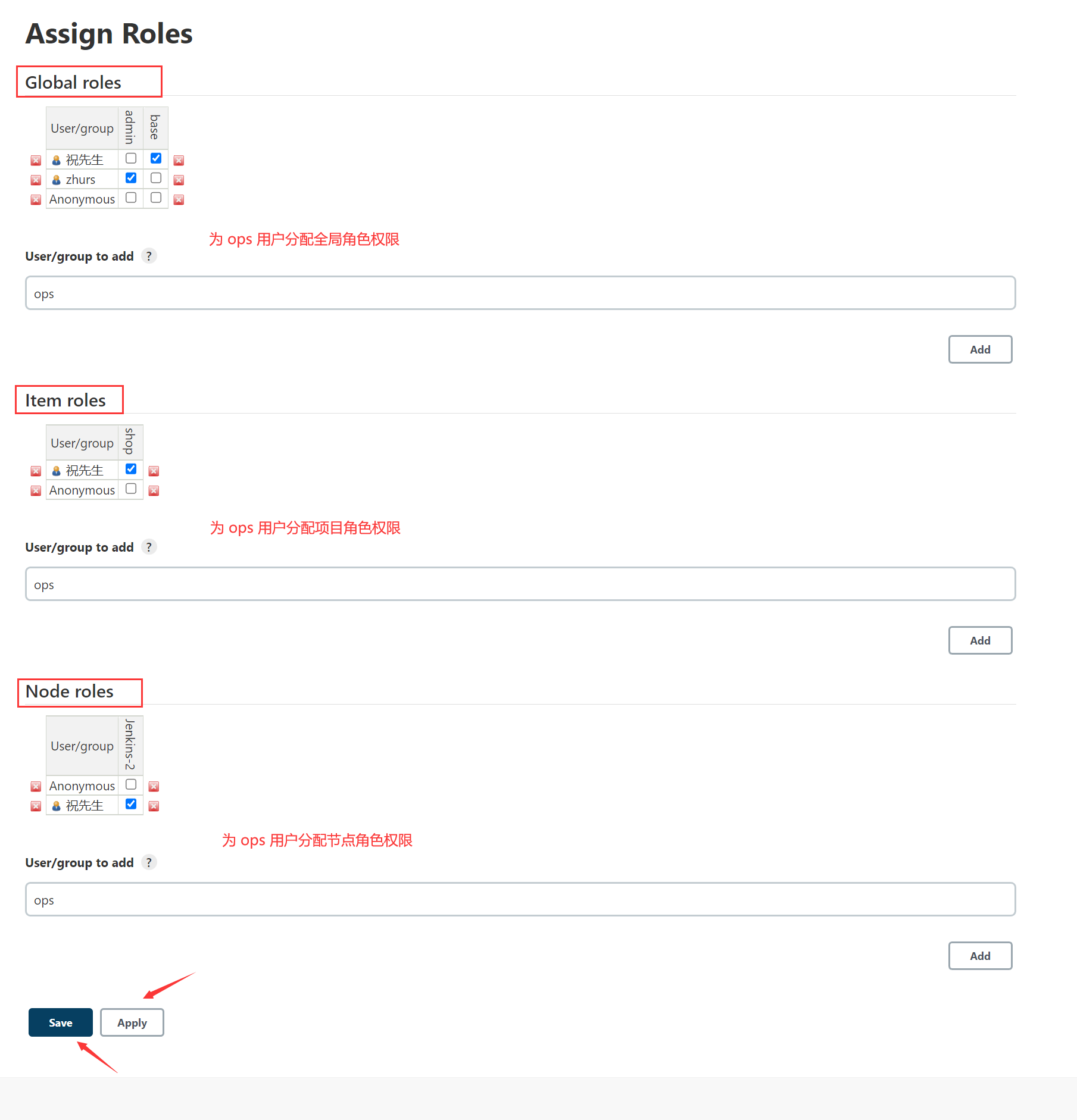
Jenkins 用户权限管理
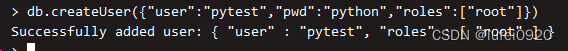
Mongodb learn from simple to deep
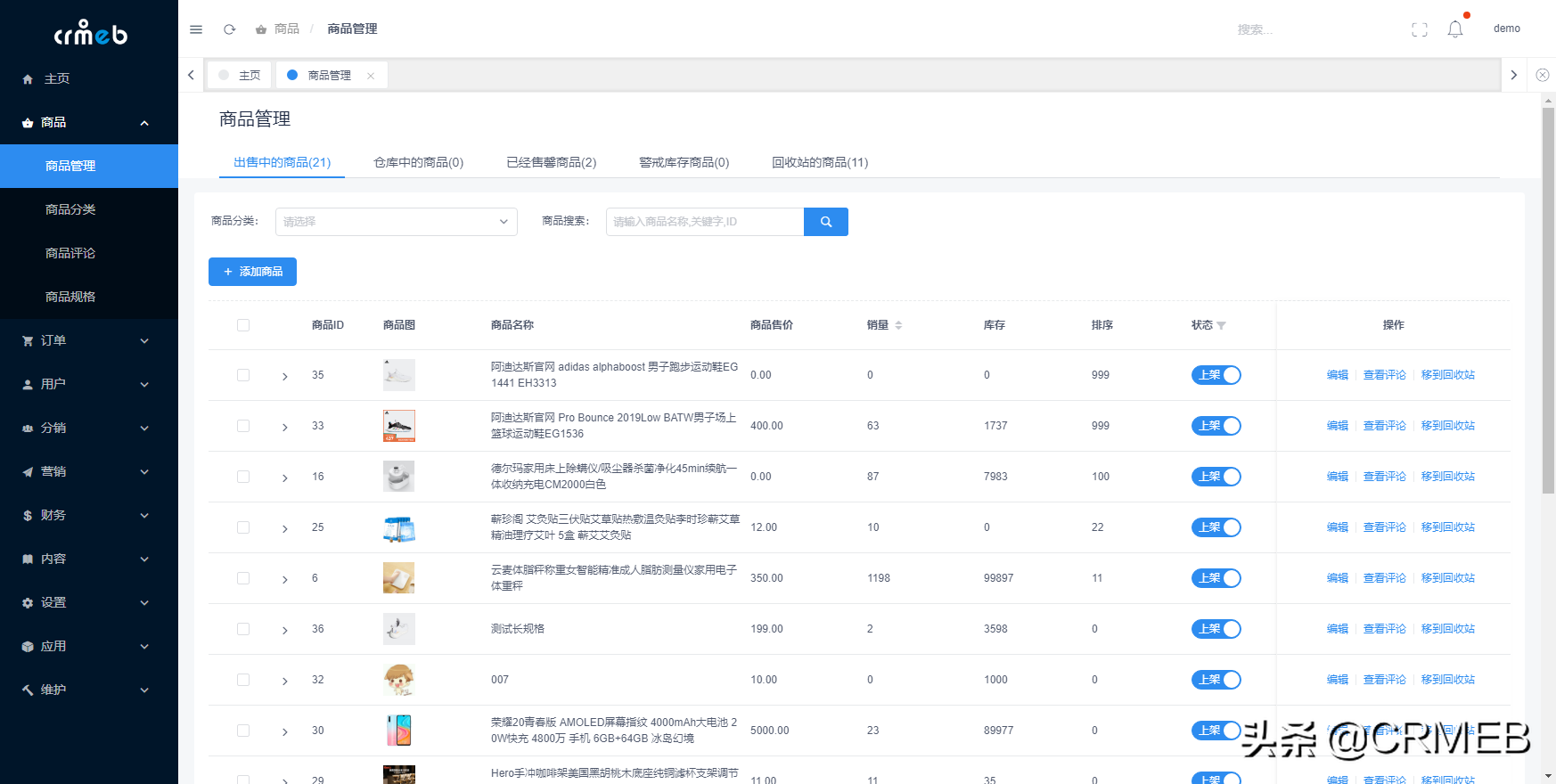
Make this crmeb single merchant wechat mall system popular, so easy to use!
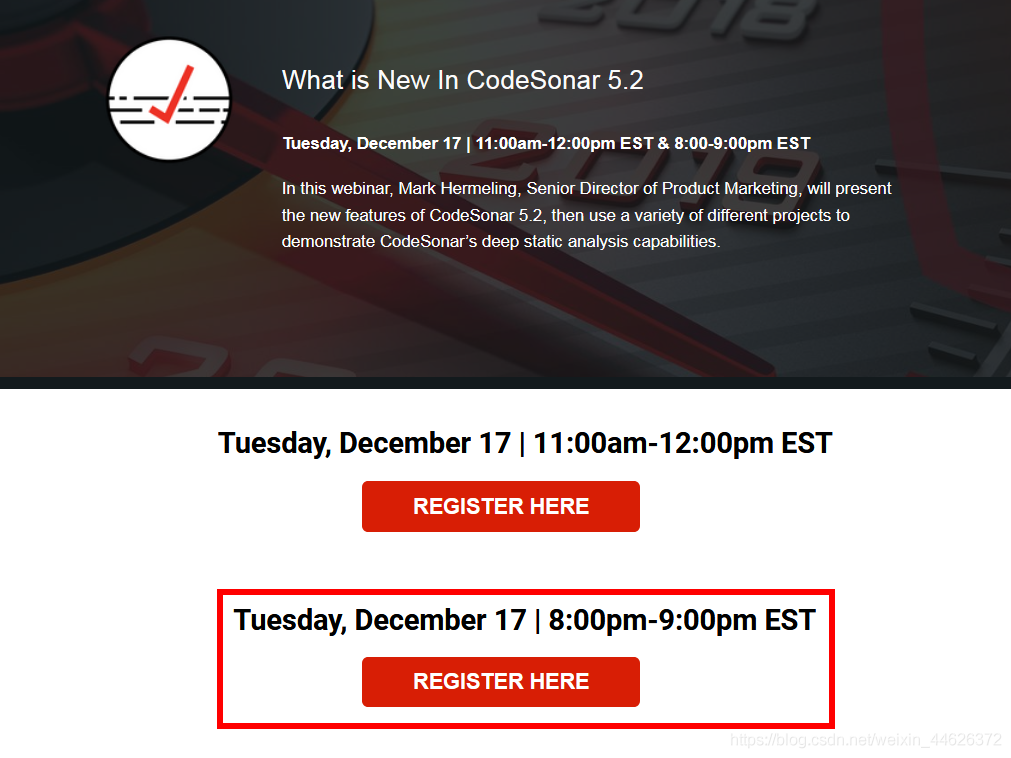
软件缺陷静态分析 CodeSonar 5.2 新版发布
随机推荐
阿里云有奖体验:如何通过ECS挂载NAS文件系统
Try the tuiroom of Tencent cloud (there is an appointment in the evening, which will be continued...)
【解决】package ‘xxxx‘ is not in GOROOT
Don't fall behind! Simple and easy-to-use low code development to quickly build an intelligent management information system
School 1 of vulnhub
使用camunda做工作流设计,驳回操作
VMWare中虚拟机网络配置
软件缺陷静态分析 CodeSonar 5.2 新版发布
九度 1201 -二叉排序数遍历- 二叉排序树「建议收藏」
Mrs offline data analysis: process OBS data through Flink job
理财产品要怎么选?新手还什么都不懂
Update iteration summary of target detection based on deep learning (continuous update ing)
I Basic concepts
[paper reading] maps: Multi-Agent Reinforcement Learning Based Portfolio Management System
Opencv learning notes high dynamic range (HDR) imaging
字符串中数据排序
微服务远程Debug,Nocalhost + Rainbond微服务开发第二弹
图扑数字孪生煤矿开采系统,打造采煤“硬实力”
AIRIOT助力城市管廊工程,智慧物联守护城市生命线
Airiot helps the urban pipe gallery project, and smart IOT guards the lifeline of the city