当前位置:网站首页>DCL statement of MySQL Foundation
DCL statement of MySQL Foundation
2022-07-04 10:21:00 【Java full stack preacher】
DCL(Data Control Language) sentence : Data control statement .
purpose : Control database 、 surface 、 Field 、 User Access and security levels .
Common keywords :grant、revoke etc.
It is generally used to manage the permissions of databases and users , Learn from practical examples grant( Assign permissions ) and revoke( Take back authority )
Take a common example , This example will be useful in the future
Example : Assign permissions to a user for a database
The database server in a company may run databases of many projects at the same time . therefore , We should be able to Create different users according to different projects , Assign different permissions To manage and maintain the database .
create user 'usertest'@'%' indentified by '123456';
grant all privileges on mydb.* to 'usertest'@'%';
-- View the user's permissions
show grants for 'usertest'@'%';
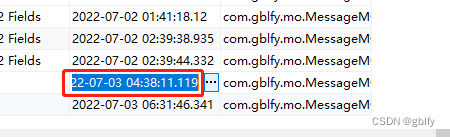
user usertest Yes mydb The database has all permissions (ALL PRIVILEGES)
Revoke delete permission
revoke delete on mydb.* from 'usertest'@'%'Switch back to the root, Re execution revoke command

-- View the user's permissions
show grants for 'usertest'@'%';
In addition to deleting permissions , Other permissions are . You can also see here , A user has many operation permissions , And these permissions can be assigned independently .
Pay attention to the official account, learn more about the knowledge of the database and get the database free e-book. .

边栏推荐
- Safety reinforcement learning based on linear function approximation safe RL with linear function approximation translation 2
- Button wizard business running learning - commodity quantity, price reminder, judgment Backpack
- A little feeling
- Latex arranges single column table pictures in double column format articles
- View CSDN personal resource download details
- Kotlin 集合操作汇总
- How to teach yourself to learn programming
- Reprint: summation formula of proportional series and its derivation process
- 2021-08-10 character pointer
- Container cloud notes
猜你喜欢
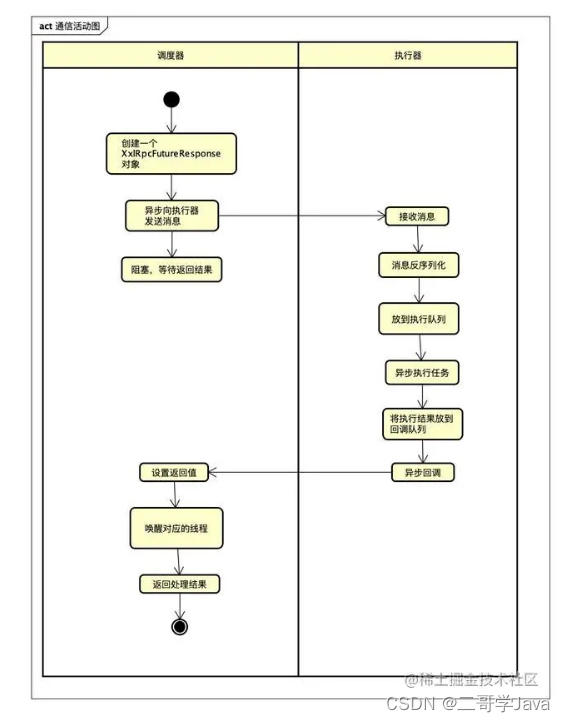
How can people not love the amazing design of XXL job

Development guidance document of CMDB
Two way process republication + routing policy
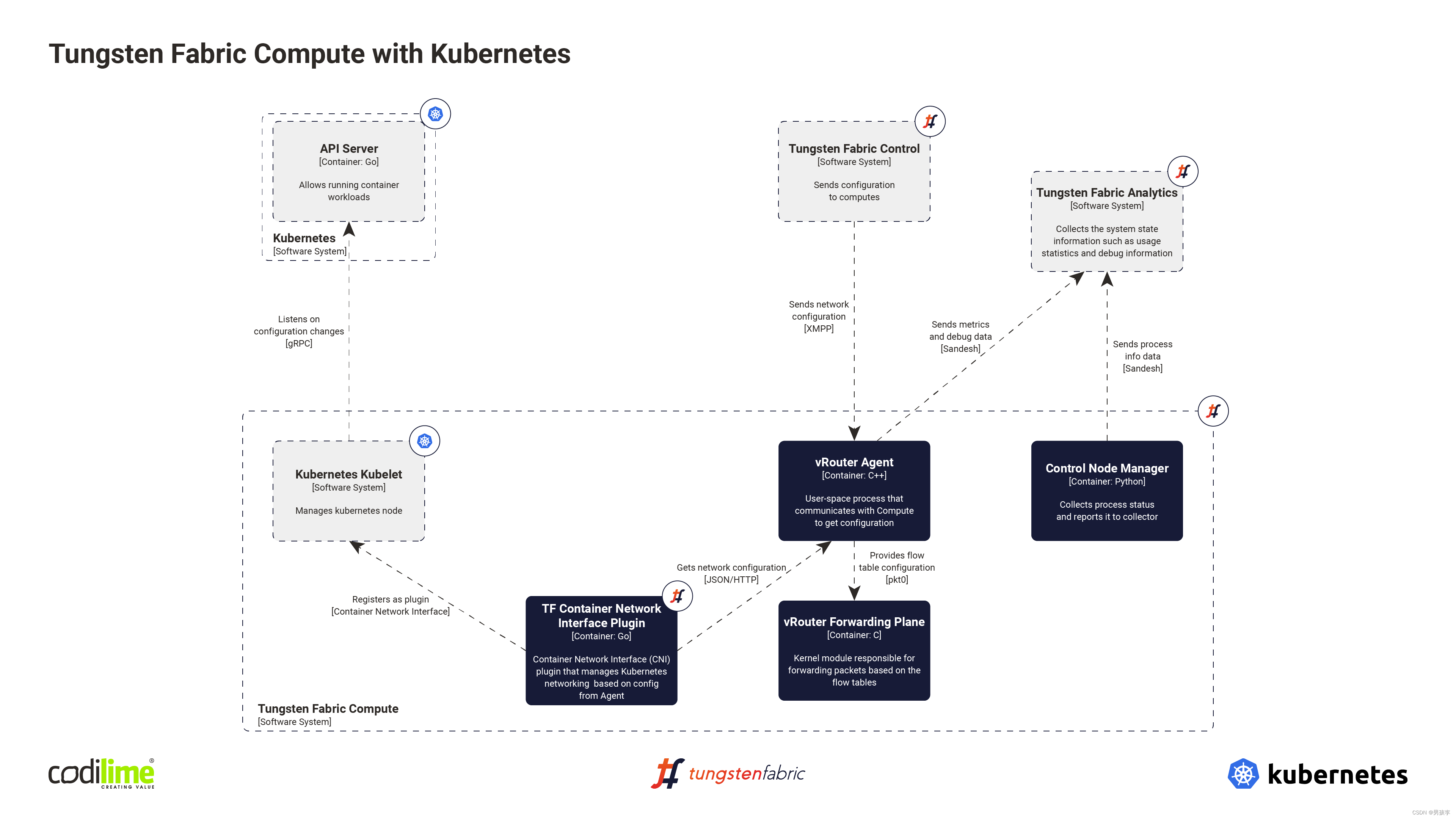
Fabric of kubernetes CNI plug-in
Hands on deep learning (40) -- short and long term memory network (LSTM)

Servlet基本原理与常见API方法的应用
![[200 opencv routines] 218 Multi line italic text watermark](/img/3e/537476405f02f0ebd6496067e81af1.png)
[200 opencv routines] 218 Multi line italic text watermark
Reasons and solutions for the 8-hour difference in mongodb data date display

5g/4g wireless networking scheme for brand chain stores
Summary of reasons for web side automation test failure
随机推荐
Realsense d435 d435i d415 depth camera obtains RGB map, left and right infrared camera map, depth map and IMU data under ROS
Leetcode48. Rotate image
Does any teacher know how to inherit richsourcefunction custom reading Mysql to do increment?
转载:等比数列的求和公式,及其推导过程
Vs201 solution to failure to open source file HPP (or link library file)
OSPF comprehensive experiment
Machine learning -- neural network (IV): BP neural network
View CSDN personal resource download details
Lavel document reading notes -how to use @auth and @guest directives in lavel
Si vous ne connaissez pas ces quatre modes de mise en cache, vous osez dire que vous connaissez la mise en cache?
BGP advanced experiment
Hands on deep learning (40) -- short and long term memory network (LSTM)
Latex arranges single column table pictures in double column format articles
Exercise 7-8 converting strings to decimal integers (15 points)
Matlab tips (25) competitive neural network and SOM neural network
Golang Modules
Exercise 9-4 finding books (20 points)
Normal vector point cloud rotation
Baidu R & D suffered Waterloo on three sides: I was stunned by the interviewer's set of combination punches on the spot
Pcl:: fromrosmsg alarm failed to find match for field 'intensity'
