当前位置:网站首页>Initial experience of cache and ehcache "suggestions collection"
Initial experience of cache and ehcache "suggestions collection"
2022-07-07 19:08:00 【Full stack programmer webmaster】
Hello everyone , I meet you again , I'm the king of the whole stack .
1. The meaning of caching
The caching mechanism is to take out the data often used in the database and put it into memory . When the program is called, it fetches directly from memory , Use every time Data access database , This improves efficiency .
2. Caching needs attention
1) Cache update
The data in the cache must be consistent with the data in the database .
2) Cache hit rate
Improve the utilization of cached data , The cache stores data that users often use , Suppose that the cache stores something that users don't often use . Then the hit rate of cache is not high . Sometimes , It is the high utilization rate of some cached data at a certain time , Low utilization at a certain time , So it needs to be updated constantly , To improve cache hit ratio .
Hibernate Cache mechanism
• The first level cache is Session The cache of . because Session The life cycle of an object usually corresponds to a database transaction or an application transaction , So its cache is a transaction wide cache . First level caching is necessary , Disagree and can't be removed . In the first level cache . Each instance of a persistent class has a unique OID. • The second level cache is a pluggable cache plug-in , It consists of SessionFactory Responsible for managing the . because SessionFactory The life cycle of the object corresponds to the whole process of the application , So the second level cache is Process wide cache . This cache stores the bulk data of the object .
The second level cache is optional . The second level cache can be configured on the granularity of each class or collection .
remarks :
L1 cache may cause repeated data queries , thus , We introduced the second level cache mechanism .
The first level cache is used by user threads . The L2 cache is shared by everyone .
What we need to learn is how to control the L2 cache , To this end, we need to ensure 2 spot :
1). How to update the data in the L2 cache Suppose the user does not change the data of the database , We need to update the cache immediately 2). Ensure the hit rate of data in L2 cache Change space for time .
Data in L2 cache
When necessary, we use frequent data .
3.EhCache
1. Brief introduction
EhCache It's pure. Java In process caching framework for . With high speed 、 Characteristics such as ability . yes Hibernate In the default CacheProvider.
2. stay Hibernate Use in EhCache
Change profile Hibernate.cfg.xml
<property name="hibernate.cache.provider_class">
org.hibernate.cache.EhCacheProvider
</property>3. The configuration file ehcache.xml
The meanings of parameters are • maxElementInMemory Indicates how many objects can be placed in the cache , Here is 10000 individual , It can be configured according to the amount of memory • eternal Indicates whether to set these data objects put into the L2 cache to be permanent ( Put it in and save it . No longer clear ) Typically for false • timeToIdleSeconds=120 It is assumed that 120 Seconds . The placed object is not accessed again , Just clear it out • timeToLiveSeconds=120 Indicates the time the object survives in the cache , An object enters this cache 120 Seconds later , It will be cleared away by itself ( Generally, the setting time will be longer than timeToIdleSeconds Long time ).
This property is set to allow many other active objects to enter From cache . • overflowToDisk=”true” Indicates that the assumed active object has exceeded maxElementInMemory Set the maximum value of , Exceeded objects are written Save it on your hard disk . Ease the situation with more active users .
4. Change the detailed mapping file xxx.hbm.xml
Join the familiar :<property region=”default” usage=”read-write”>
• region attribute Indicates which L2 cache to use • usage attribute Indicates how L2 cache is used There are two kinds of :read-only and read-write read-only Let's say it's read-only. Then it cannot be changed . such ehcache There is no need to consider the operation of changes and updates . read-write Set to read-write,ehcache Also consider updates and changes . This will reduce efficiency .
therefore . Set up usage Attributes are very important , It is necessary to infer that the stored objects use L2 cache based on the actual situation .
Welcome to discuss and study together !
Practical self collection !
Record and share . Let us grow together ! Welcome to my other blogs . My blog address :http://blog.csdn.net/caicongyang
Publisher : Full stack programmer stack length , Reprint please indicate the source :https://javaforall.cn/116611.html Link to the original text :https://javaforall.cn
边栏推荐
- Flipping Game(枚举)
- Cloud security daily 220707: Cisco Expressway series and telepresence video communication server have found remote attack vulnerabilities and need to be upgraded as soon as possible
- RISCV64
- What is the general yield of financial products in 2022?
- Simple configuration of single arm routing and layer 3 switching
- PTA 1102 教超冠军卷
- Redis cluster and expansion
- Redis
- App capture of charles+postern
- 强化学习-学习笔记8 | Q-learning
猜你喜欢
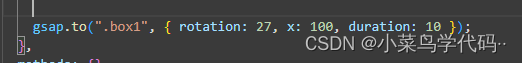
GSAP animation library
微信网页调试8.0.19换掉X5内核,改用xweb,所以x5调试方式已经不能用了,现在有了解决方案
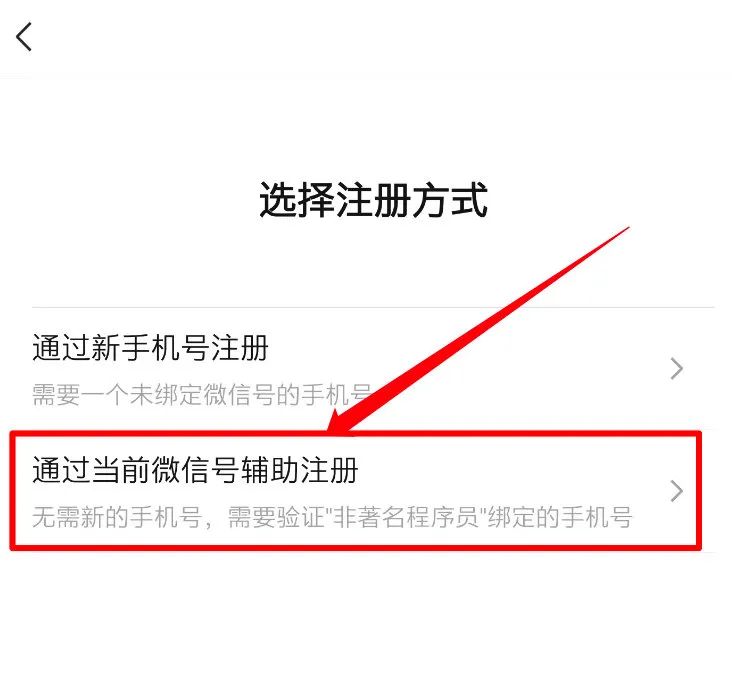
我感觉被骗了,微信内测 “大小号” 功能,同一手机号可注册两个微信
![[software test] from the direct employment of the boss of the enterprise version, looking at the resume, there is a reason why you are not covered](/img/73/cbbe82fd6bdfa8177f5bfcf683010d.jpg)
[software test] from the direct employment of the boss of the enterprise version, looking at the resume, there is a reason why you are not covered
![[Tawang methodology] Tawang 3W consumption strategy - U & a research method](/img/63/a8c08ac6ec7d654159e5fc8b4423e4.png)
[Tawang methodology] Tawang 3W consumption strategy - U & a research method
![[information security laws and regulations] review](/img/da/c9318ea8999c3ee629b0e48ab78581.png)
[information security laws and regulations] review
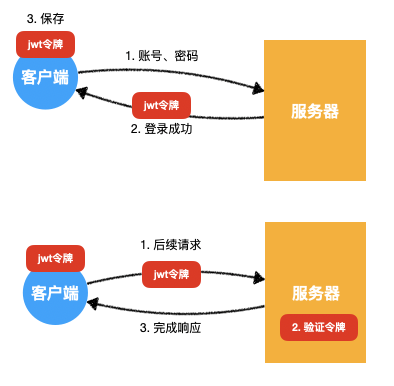
6. About JWT
链式二叉树的基本操作(C语言实现)
基于图像和激光的多模态点云融合与视觉定位
Mathematical analysis_ Notes_ Chapter 11: Fourier series
随机推荐
POJ 2392 Space Elevator
Redis cluster and expansion
UVALive – 4621 Cav 贪心 + 分析「建议收藏」
AI来搞财富分配比人更公平?来自DeepMind的多人博弈游戏研究
Thread pool and singleton mode and file operation
[tpm2.0 principle and Application guide] Chapter 9, 10 and 11
Differences between rip and OSPF and configuration commands
3. About cookies
Complete e-commerce system
The moveposition function of rigidbody2d of unity2d solves the problem of people or screen jitter when moving
如何给“不卖笔”的晨光估值?
10 schemes to ensure interface data security
Flipping Game(枚举)
Wireshark analyzes packet capture data * cap
Cadre de validation des données Apache bval réutilisé
LeetCode 890(C#)
Thread factory in thread pool
行业案例|数字化经营底座助力寿险行业转型
Charles+drony的APP抓包
CVPR 2022丨学习用于小样本语义分割的非目标知识