当前位置:网站首页>Data security -- 12 -- Analysis of privacy protection
Data security -- 12 -- Analysis of privacy protection
2022-07-07 04:23:00 【Follow also】
One 、 Data security and privacy
Privacy compliance is an important part of data security , In addition to meeting the data security requirements within the enterprise , It also needs to meet all applicable legal and regulatory requirements . The definition of privacy , It refers to the personal affairs enjoyed by natural persons 、 The right not to be known by others , And the right not to be disturbed or monitored .
Usually, the privacy we refer to here is mainly the privacy of the online world , These privacy are based on data , So it is also called personal information or personal data . Personal data is Have been identified perhaps Recognizable Any data related to natural persons .
Identified data , It refers to the data that can uniquely identify a natural person , Such as name 、 Well known network ID、 ID number, etc .
Recognizable data , It refers to data that does not contain data that can directly determine a natural person , But through the existing information , Through analysis or reasoning, the data of a natural person can be determined .
Two 、 Compliance and legal compliance
So far N Countries and regions have enacted laws related to privacy protection , But we don't all need to comply , For these laws and regulations :
First , Only when we do business in the corresponding country , Their laws and regulations come into force for us , For many domestic companies , We only need to pay attention to a few laws and regulations . It should be noted that , If you provide network services , For example, the website involves the registration and access of unspecified users , This may involve processing personal data of local residents .
second , The requirements of laws and regulations related to privacy protection in various countries are also learning from each other , So most of the clauses are similar or repeated , Therefore, we only need to comply with a relatively strict regulation to meet most compliance requirements , A small number of inconsistencies only need a single processing of the involved business .
3、 ... and 、 From external regulation to internal regulation
The first step from external regulation to internal regulation , The most important external laws and regulations applicable to the business 、 Best practice framework for decomposition and reorganization , In decomposition and reorganization , Split these terms by field , Then summarize and reorganize , Remove duplicates . for example , Group all role definition classes , All data lifecycle classes are grouped together, and so on . This is actually a process of integrating all regulations .
After decomposition and reorganization , Form a compliance benchmark within the enterprise , Then all internal work is carried out based on this compliance benchmark .
Next , These compliance benchmarks need to be used as input to the development of internal document systems , Will comply with the requirements of the benchmark , Return one by one in the internal document system , For example, put it in the general policy outline 、 Management regulations 、 Internal standards 、 Technical specifications, etc . This is actually a process of integrating into internal documents .
This mode , To a large extent, it avoids the risk of external mandatory requirements without internal documents . The business is in the process of compliance improvement , You only need to find a few policy documents corresponding to your field to carry out the work , Improve the efficiency of the business department .
meanwhile , The bridge in the middle needs to change according to the outside , Such as the new legislation 、 New practice 、 New risks, etc , Make regular updates , As the input of all other privacy protection work . In fact, it's not just a document system , The work of the whole privacy protection system , Can be based on such decomposition and reorganization results .
Four 、 Reference material
For the implementation of privacy protection , You can refer to the blogger's 【 Privacy compliance 】 special column .
边栏推荐
- Pyqt5 out of focus monitoring no operation timer
- 2022电工杯A题高比例风电电力系统储能运行及配置分析思路
- Opencv third party Library
- EasyCVR集群重启导致其他服务器设备通道状态离线情况的优化
- idea gradle lombok 报错集锦
- [written to the person who first published the paper] common problems in writing comprehensive scientific and Technological Papers
- easyui出口excel无法下载框弹出的办法来解决
- Different meat customers joined hands with Dexter to launch different hamburgers in some stores across the country
- Food Chem|深度学习根据成分声明准确预测食品类别和营养成分
- Imitate Tengu eating the moon with Avatar
猜你喜欢

In cooperation with the research team of the clinical trial center of the University of Hong Kong and Hong Kong Gangyi hospital, Kexing launched the clinical trial of Omicron specific inactivated vacc
【编码字体系列】OpenDyslexic字体
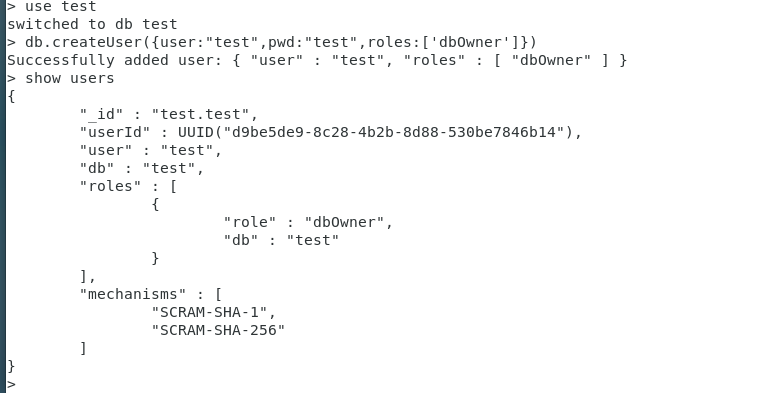
The most complete security certification of mongodb in history
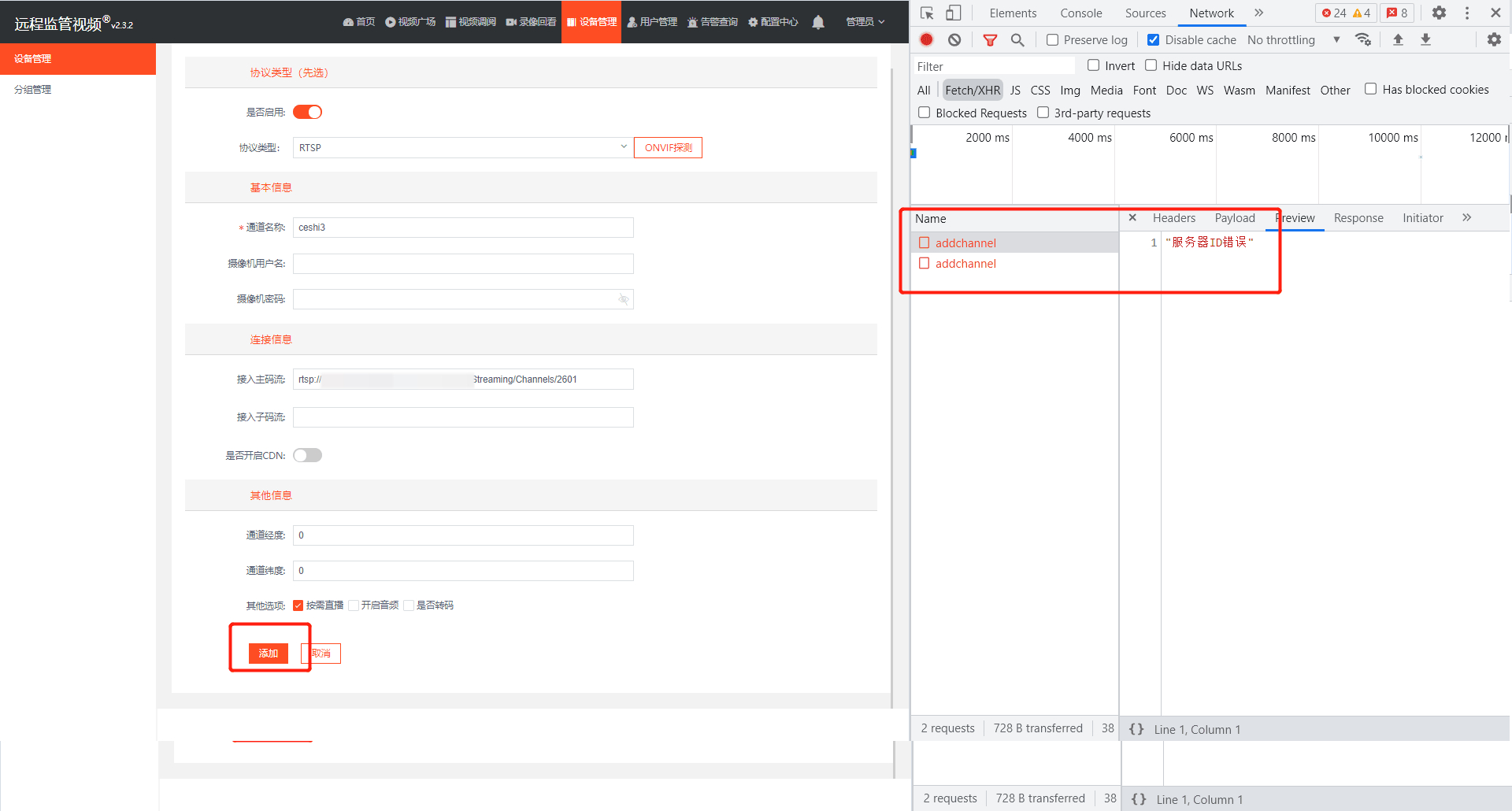
EasyCVR集群版本添加RTSP设备提示服务器ID错误,该如何解决?

See Gardenia minor
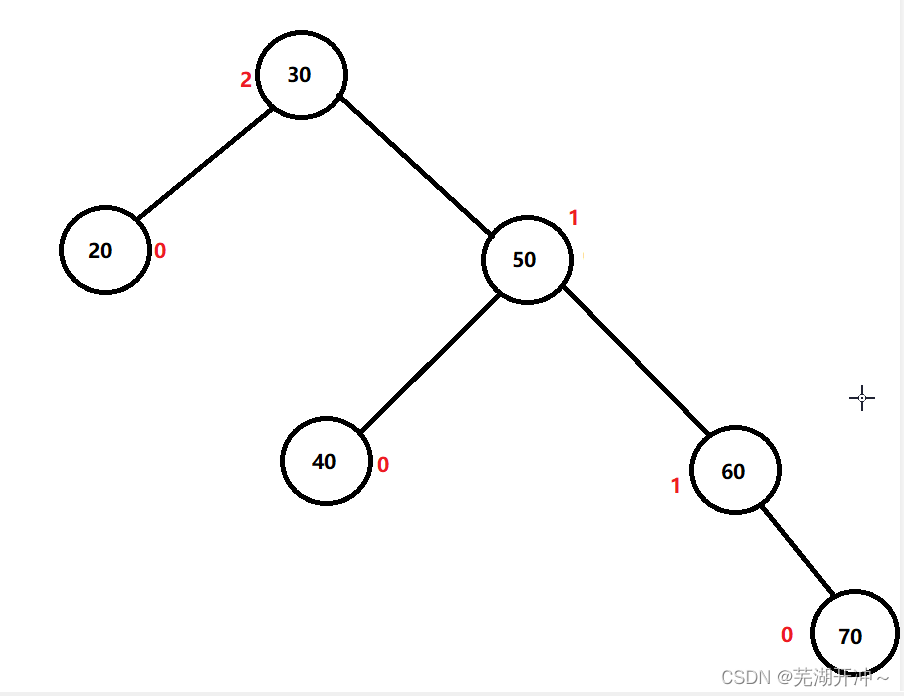
Simple implementation of AVL tree insertion and verification operations
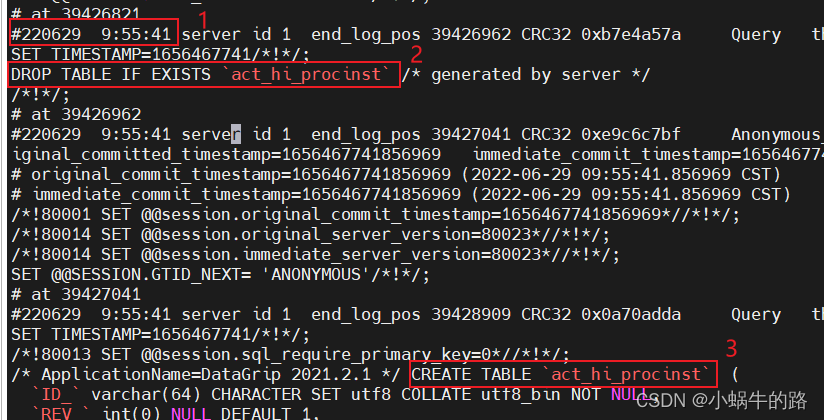
MySQL data loss, analyze binlog log file
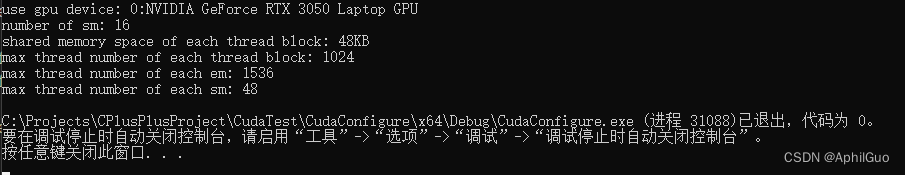
CUDA Programming
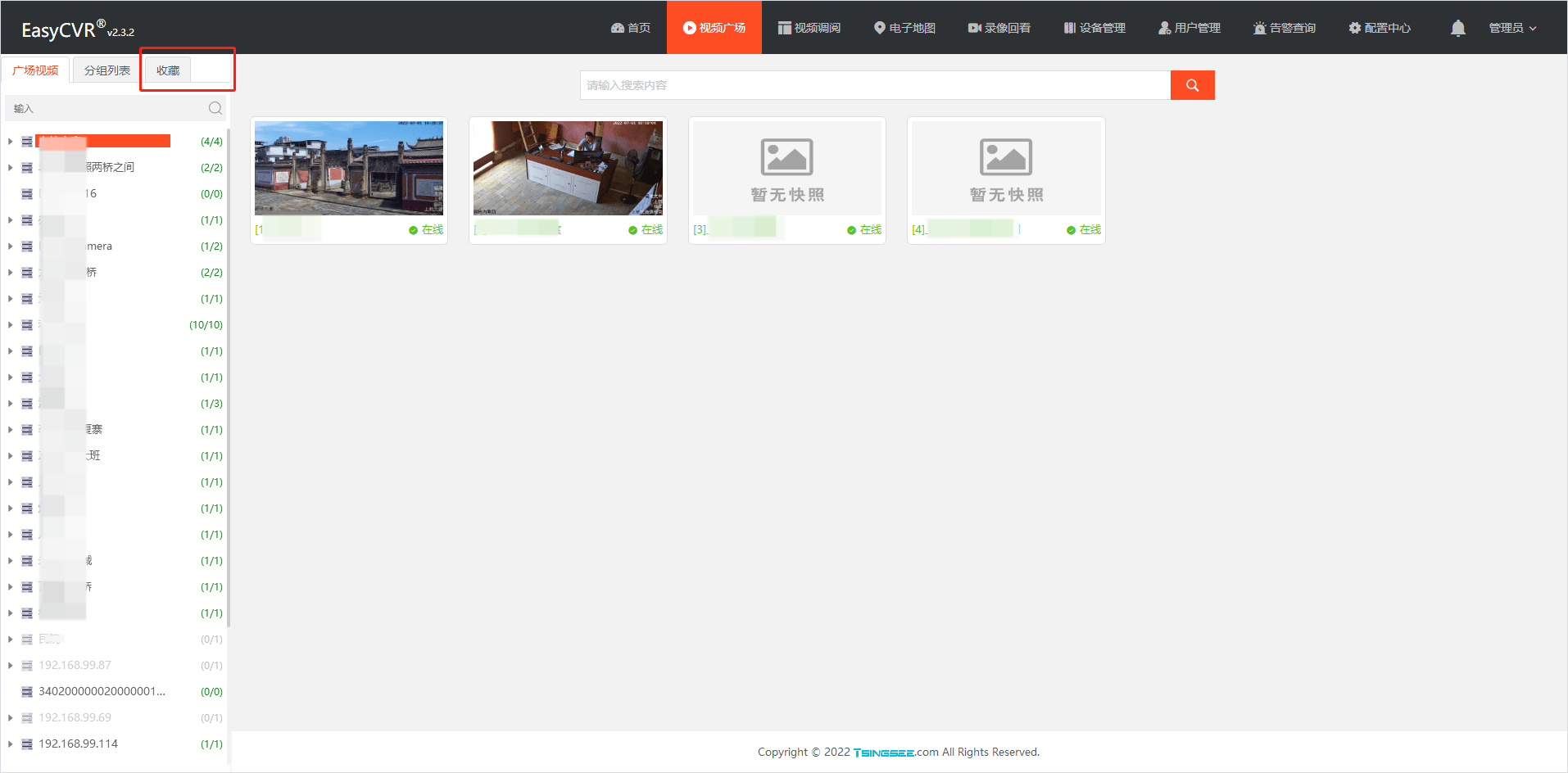
Video fusion cloud platform easycvr video Plaza left column list style optimization
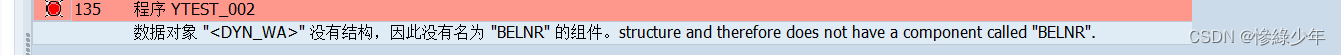
ABAP 动态内表分组循环
随机推荐
See Gardenia minor
手机号国际区号JSON格式另附PHP获取
[system management] clear the icon cache of deleted programs in the taskbar
别样肉客联手德克士在全国部分门店推出别样汉堡
Storage of data
Some thoughts on cross end development of kbone and applet
测试/开发程序员怎么升职?从无到有,从薄变厚.......
buildroot的根文件系统提示“depmod:applt not found”
机械臂速成小指南(十):可达工作空间
见到小叶栀子
Implementation of JSTL custom function library
案例大赏:英特尔携众多合作伙伴推动多领域AI产业创新发展
Easycvr cannot be played using webrtc. How to solve it?
Mongo shell, the most complete mongodb in history
leetcode 53. Maximum subarray maximum subarray sum (medium)
[written to the person who first published the paper] common problems in writing comprehensive scientific and Technological Papers
Zero knowledge private application platform aleo (1) what is aleo
The most complete learning rate adjustment strategy in history LR_ scheduler
这项15年前的「超前」技术设计,让CPU在AI推理中大放光彩
Class constant pool and runtime constant pool