当前位置:网站首页>Xray and burp linkage mining
Xray and burp linkage mining
2022-07-06 14:03:00 【Lazy and talented】
Catalog
0x0A xray Basic introduction and use
0x0b Installation configuration
0x0c xray( Community Edition ) Basic use of
0x01 Active scanning ( Remember to authorize )
0x01 Sub domain name collection
0x0B burp And xray The linkage of
0x03 burp by xray Downstream of :( install jar plug-in unit )
0x0A xray Basic introduction and use
0x0a xray Official website
xray Community Edition xray - A powerful security assessment tool
0x01 function : Subdomain scanning 、 common web Vulnerability detection 、 Service Vulnerability Detection 、
Reptile detection 、 Special detection ability 、Xray linkage
0x02 Pattern : Active scanning (edu gov Site Don't try to ) Passive scanning ( Crawl web page cache scanning )
0x03 difference burp:xray Is to monitor packets burp Is to intercept packets
0x04 xray Community Edition and Red Team Edition For daily testing, the community version can meet ( The red team poc Quick update )
Advanced version xray Support struts、fastjson、thinkphp、shiro One click detection of high-risk historical vulnerabilities in the framework

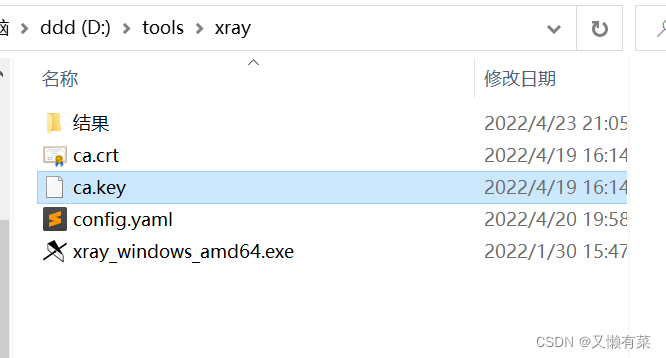
0x0b Installation configuration
0x01powershell cd Get into xray root directory
0x02 command xray_windows_amd64.exe genca, Can generate ca certificate , How to detect this machine HTTPS Traffic .
( monitor cer The certificate needs to be installed on the local computer If you use firefox The browser also imports the browser )
0x03 Certificate name :ca.cer
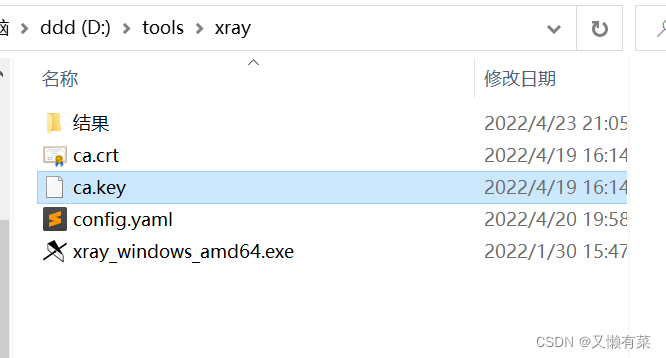
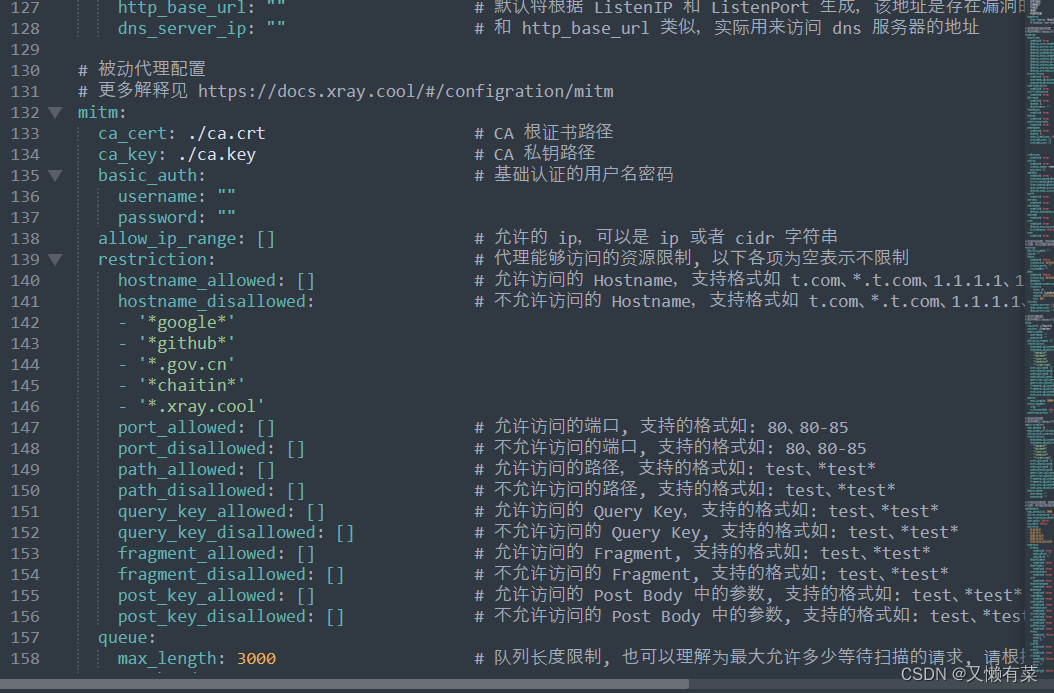
0x04 yaml file analysis disallowed The domain name that is not allowed to be scanned by default
All in all Two places Just delete this line
0x05 double-click Certificate installation
double-click --> Installation certificate --> Default yes
0x0c xray( Community Edition ) Basic use of
0x01 Active scanning ( Remember to authorize )
xray_windows_amd64.exe webscan --url www.baidu.com --html-output test.html 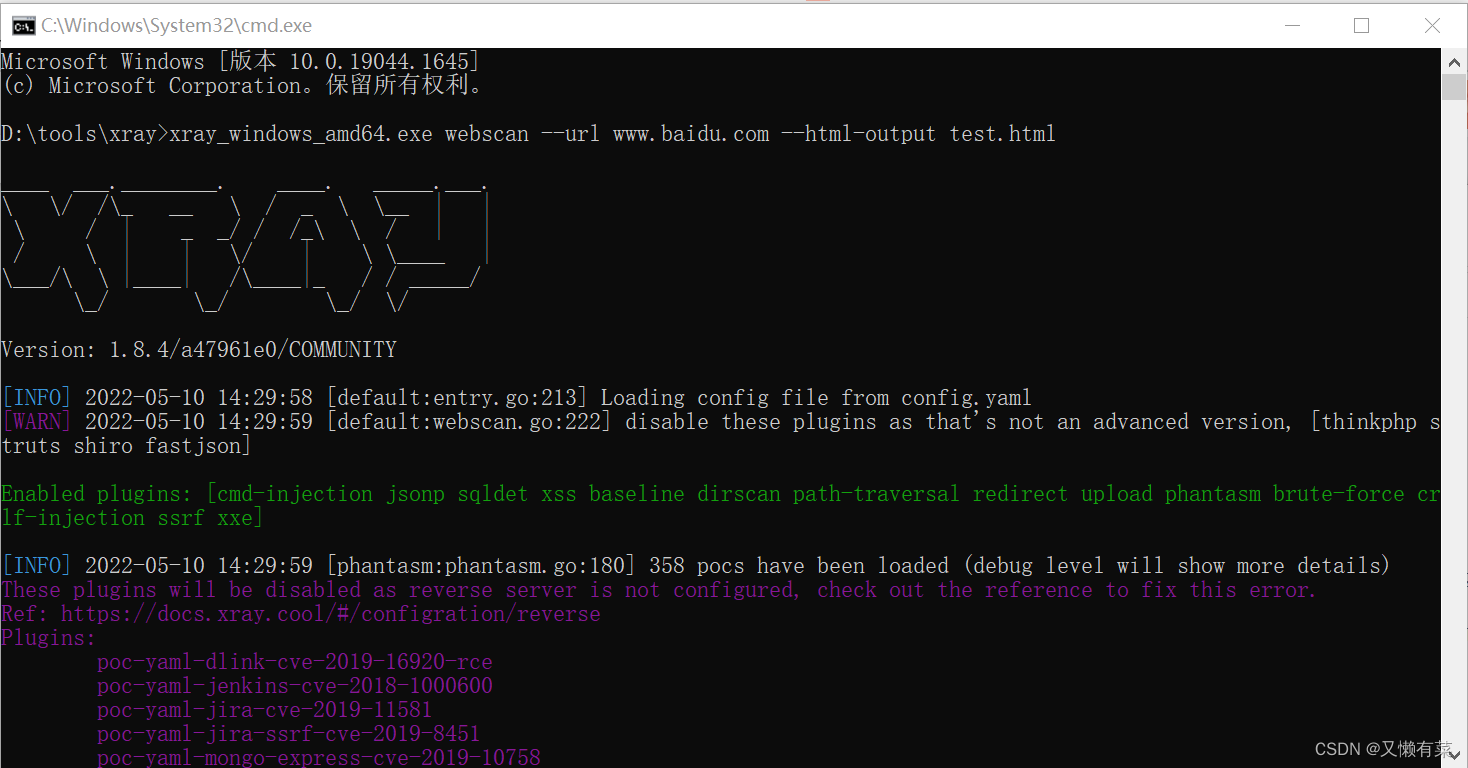
0x02 Passive scanning
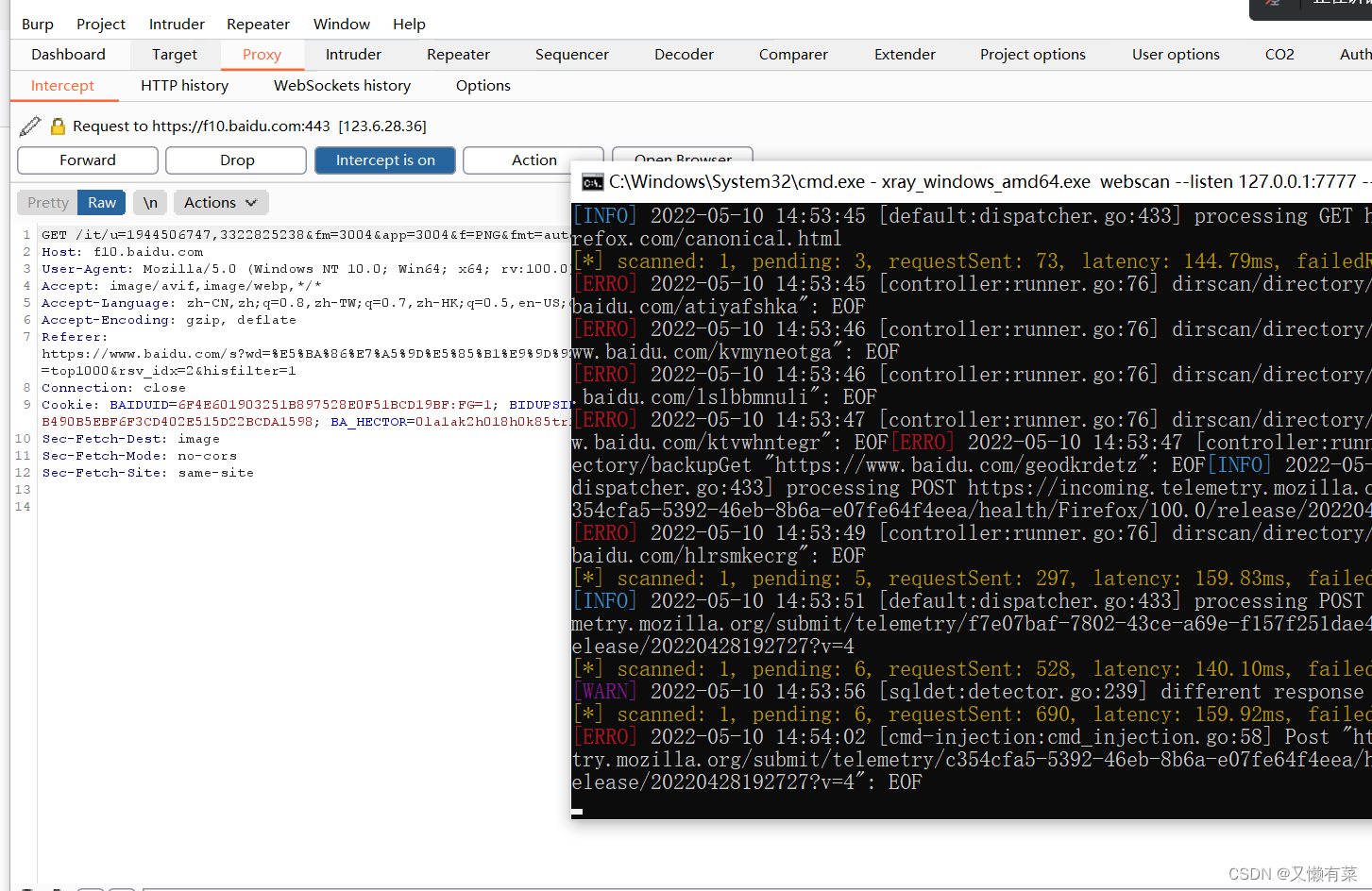
xray_windows_amd64.exe webscan--listen 127.0.0.1:7777 --html-output test.html 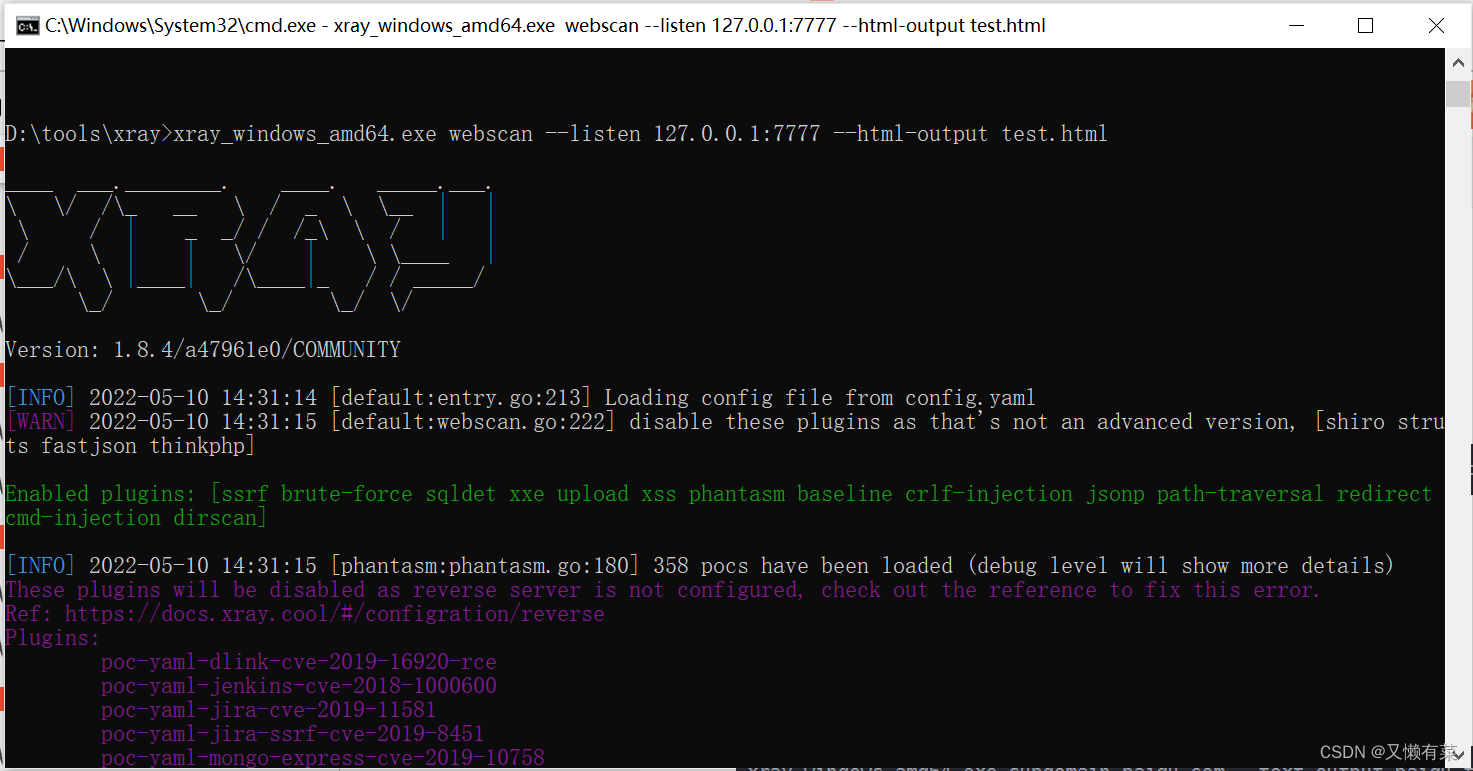
0x0d xray Red team version
0x01 Sub domain name collection
xray_windows_amd64.exe subdomain baidu.com --text-output baidu.txtThan wydomain、subDomainsBrute And other tools are more practical , Advanced version xray As information collection , Recommended .
0x02 Special scanning
shiro fastjson thinkphp struts
Don't forget to sweep it out Using one's own poc verification
wait ...
0x0B burp And xray The linkage of
effect :xray Not easy to see host use burp Of history Just solve
0X01 Grab https Traffic
If grab is needed https Flow needs brup as well as xray All installed https certificate .
Please visit
brup Install certificate grabbing https
brup Install certificate grabbing https - L0ading - Blog Garden
xray Install the certificate http as well as https scanning
xray Install the certificate http as well as https scanning - L0ading - Blog Garden
0x02 burp by xray Upstream :
browser --> burp -->xray --> testing ( Put the bag manually , Not very convenient )
On the basis of conventional packet capturing ,burp Configuring a downstream agent . Send traffic to xray scan . stay bp The following configuration can be carried out on the basis of catching website packets . here bp Send the traffic to the local 7777 port
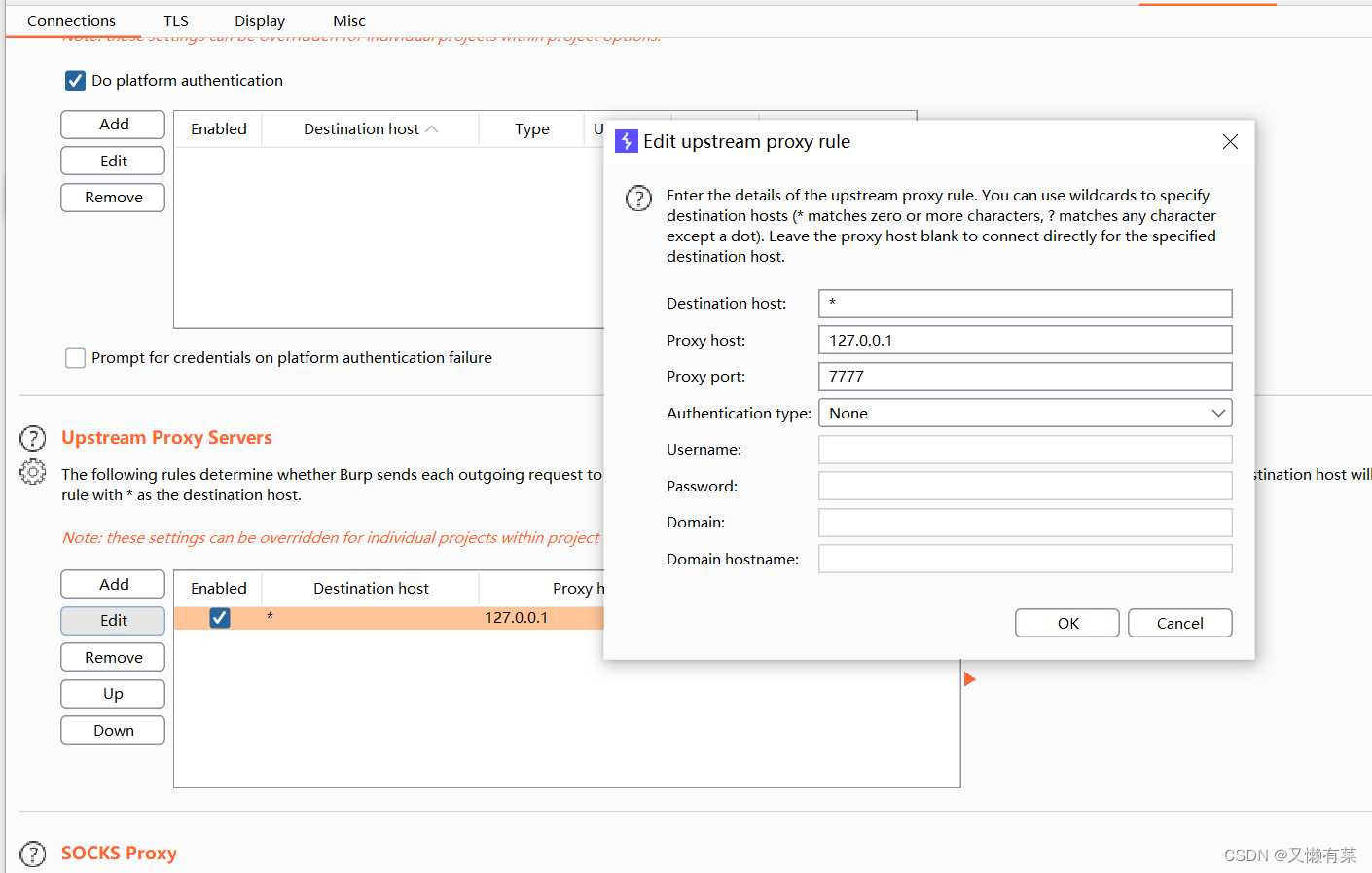
The browser opens 127.0.0.1:8080 burp Intercept port
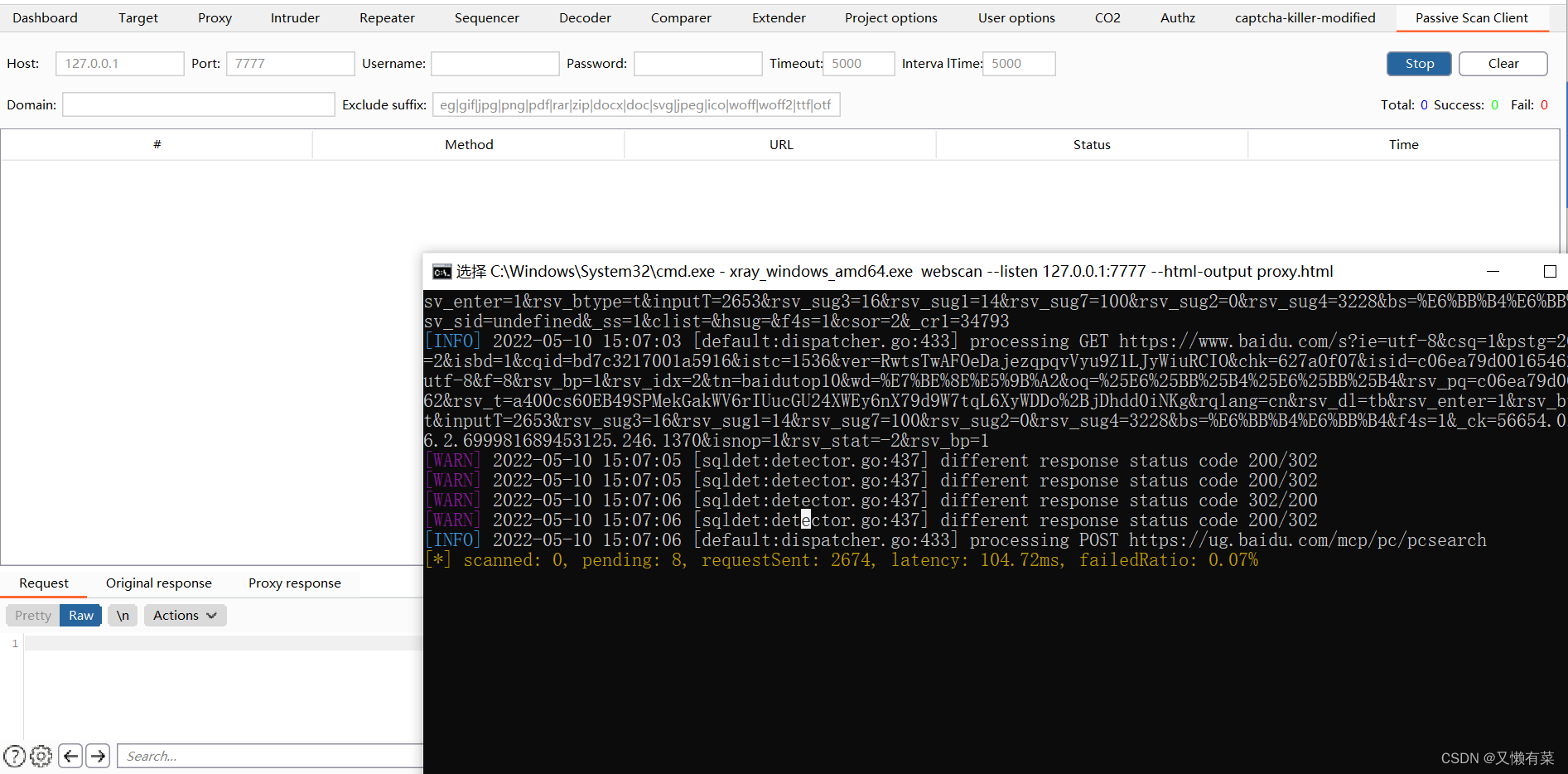
The effect is as shown in the picture
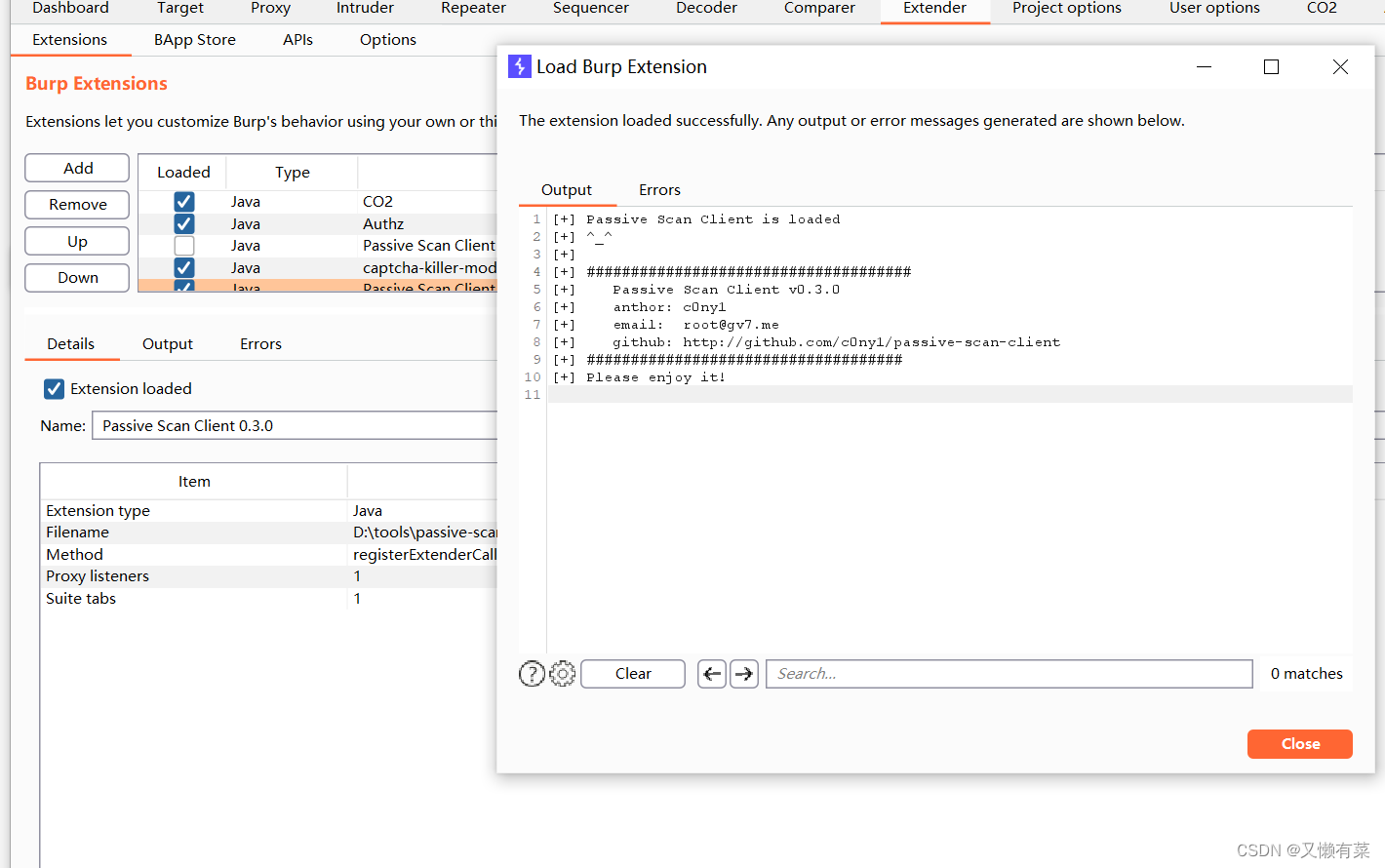
0x03 burp by xray Downstream of :( install jar plug-in unit )
error: Remember to turn off burp As upstream Set up user-options Set up
Releases · c0ny1/passive-scan-client · GitHub
tips: First open xray Listen to the command stay run passive-scan-Clinet.jar modular
browser --> xray -->burp --> testing ( Automatic detection )
Set up xray Browser agent 127.0.0.1:7777

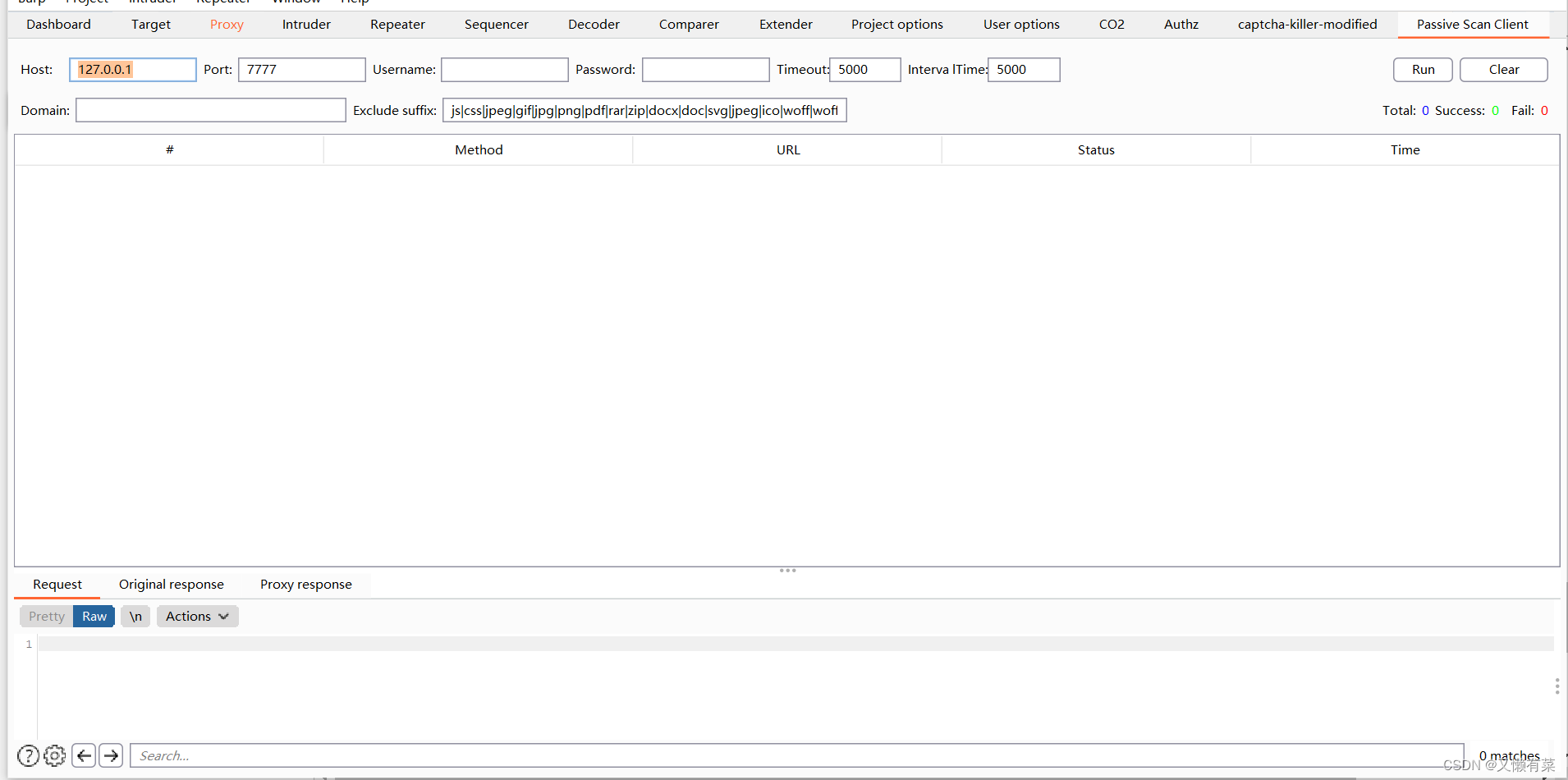
The effect is as shown in the picture Not very easy to use
summary ; No matter it is burp As xray The front and back of The effect is not very good ( It is recommended to have authorization Active scanning )
Share next issue :
xray+rad Linkage passive scanning
Fully automatic Deep climb
边栏推荐
- Reinforcement learning series (I): basic principles and concepts
- 使用Spacedesk实现局域网内任意设备作为电脑拓展屏
- It's never too late to start. The tramp transformation programmer has an annual salary of more than 700000 yuan
- 强化学习基础记录
- 强化学习基础记录
- 7-6 local minimum of matrix (PTA program design)
- 实验七 常用类的使用
- 3. Input and output functions (printf, scanf, getchar and putchar)
- 强化学习基础记录
- 中间件漏洞复现—apache
猜你喜欢
Wei Shen of Peking University revealed the current situation: his class is not very good, and there are only 5 or 6 middle-term students left after leaving class
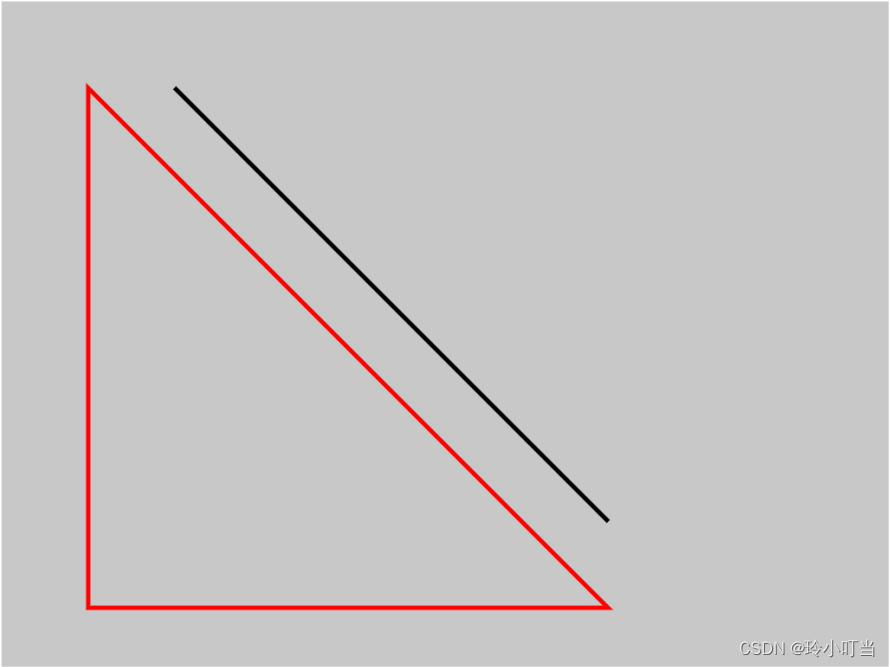
canvas基础1 - 画直线(通俗易懂)
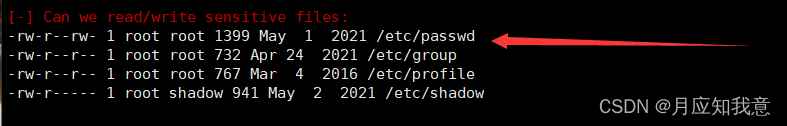
Hackmyvm target series (7) -tron

Hackmyvm Target Series (3) - vues

SRC挖掘思路及方法
xray與burp聯動 挖掘
7-7 7003 组合锁(PTA程序设计)
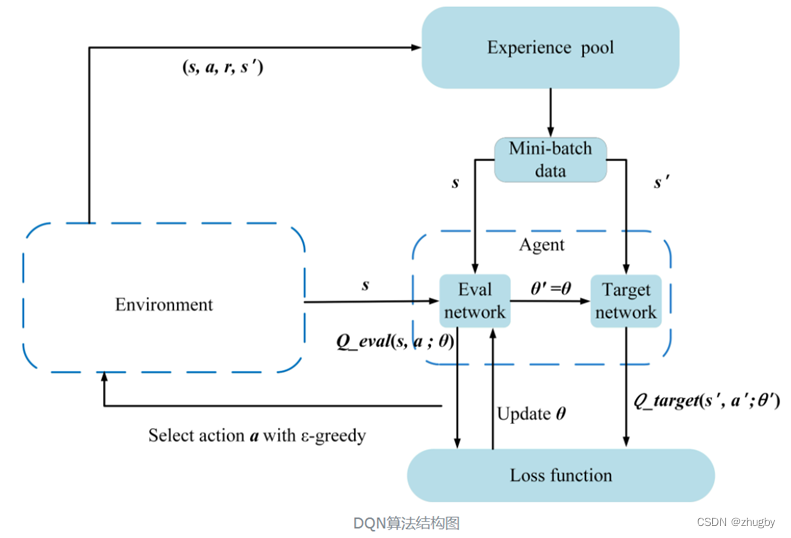
Intensive literature reading series (I): Courier routing and assignment for food delivery service using reinforcement learning
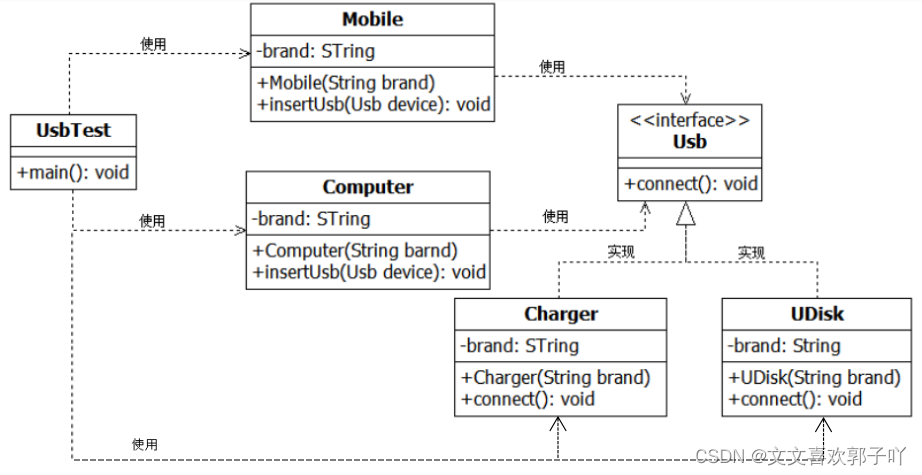
Experiment 6 inheritance and polymorphism
2022泰迪杯数据挖掘挑战赛C题思路及赛后总结
随机推荐
记一次,修改密码逻辑漏洞实战
7-3 构造散列表(PTA程序设计)
Force deduction 152 question multiplier maximum subarray
Read only error handling
7-4 hash table search (PTA program design)
Experiment five categories and objects
HackMyvm靶机系列(1)-webmaster
FAQs and answers to the imitation Niuke technology blog project (III)
Safe driving skills on ice and snow roads
Hackmyvm target series (7) -tron
TypeScript快速入门
7-14 错误票据(PTA程序设计)
HackMyvm靶机系列(2)-warrior
7-1 输出2到n之间的全部素数(PTA程序设计)
Miscellaneous talk on May 27
HackMyvm靶机系列(6)-videoclub
How to understand the difference between technical thinking and business thinking in Bi?
7-15 h0161. Find the greatest common divisor and the least common multiple (PTA program design)
Yugu p1012 spelling +p1019 word Solitaire (string)
7-6 矩阵的局部极小值(PTA程序设计)