当前位置:网站首页>Performance analysis of user login TPS low and CPU full
Performance analysis of user login TPS low and CPU full
2022-07-06 03:07:00 【zuozewei】
User login is just a common function , But its logic is not simple at all . Because the login process needs to compare and verify personal information , During the verification process, the corresponding encryption algorithm must be called , Encryption algorithm is a function that requires high performance . The complex encryption algorithm has high security , But the performance is poor ; Uncomplicated encryption algorithm has good performance , But it's safe , This is a question of trade-offs .
Follow the design steps of the benchmark scenario of the test scheme , First, test the benchmark scenario of this interface .
● Problem phenomenon
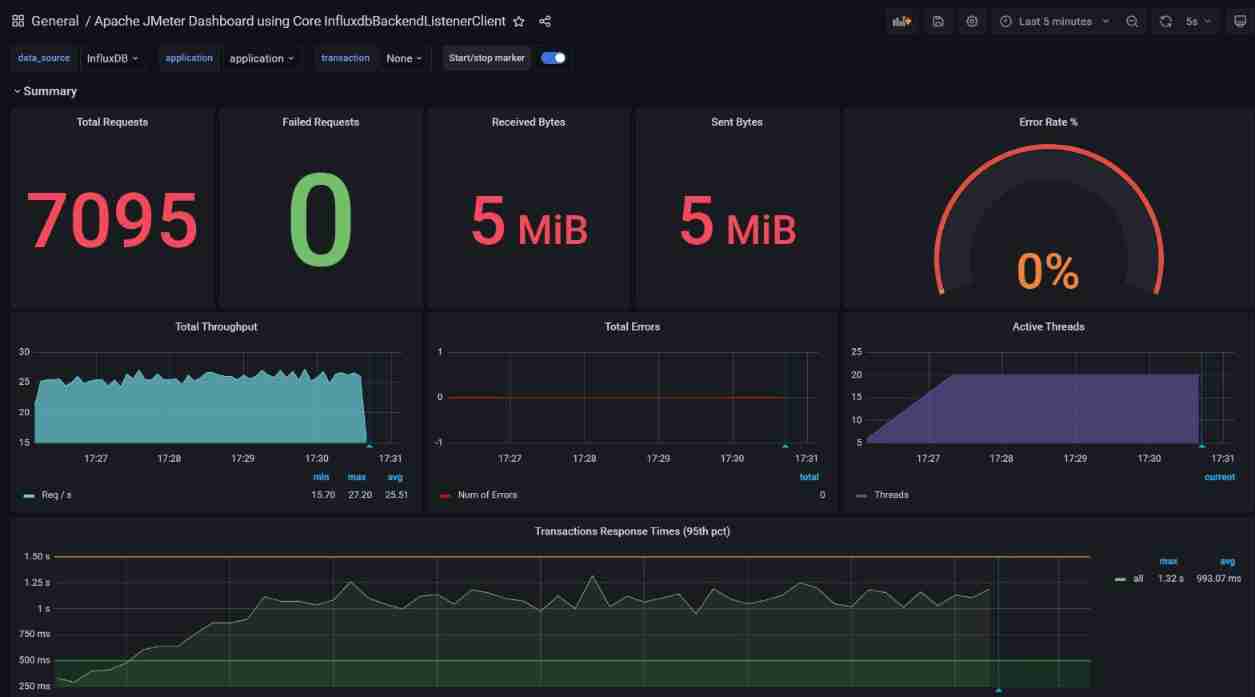
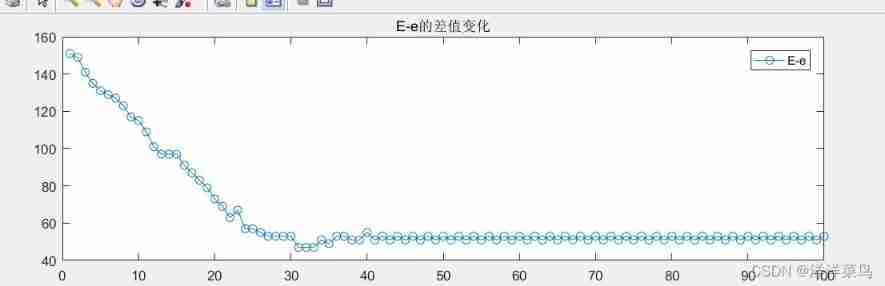
As shown in the figure above , This phenomenon is becoming more and more obvious .
In the pressure measurement results TPS The average is 25 The average response time reached 993 ms.
● The analysis process
In terms of performance analysis logic , For the problem of long response time , The first thing to do is to split the time . Since this system has been deployed SkyWalking, Use it to see where time is mainly spent .
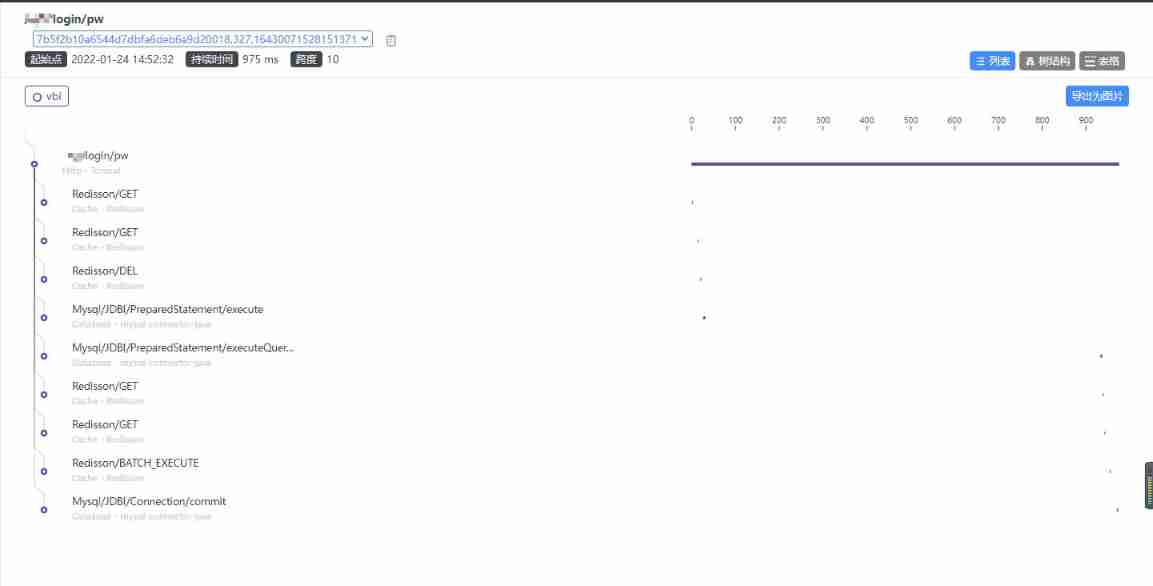
Look at the picture ,Tomcat Of SelfDuration The most. , In other words, time is almost consumed in the service itself .
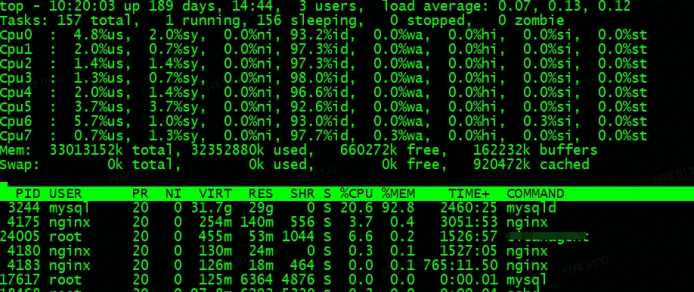
● Global monitoring
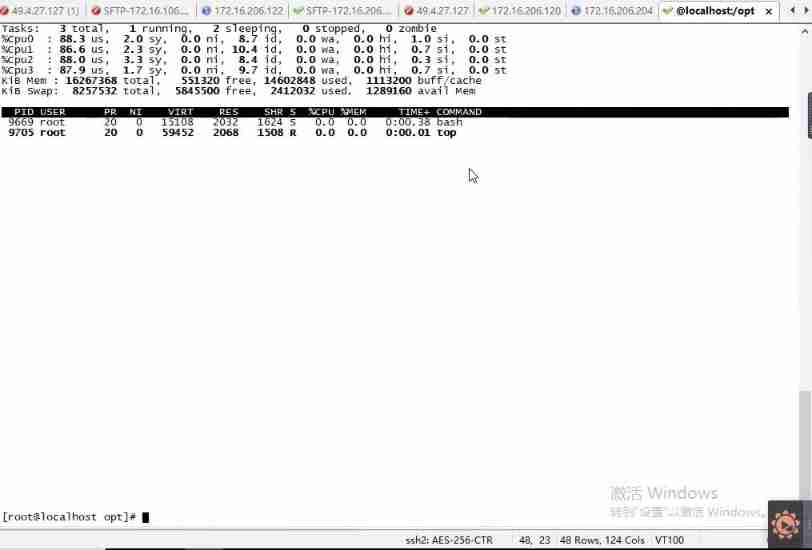
First, check the resource level of the application server :

You can see 4C Of CPU Resources have been exhausted .
The container deployed here , Let's take a look at the resource usage of each container :

You can see that resources are mainly consumed by the service container .
● Service orientation analysis
First, enter the service container to view the resource consumption :
stay SkyWaking You can't see the complete call stack in , Consider connecting directly to the service Java The time consumption of the method in the process . Here we use Arthas Follow up .
Check out the busiest previous N Thread and print stack :
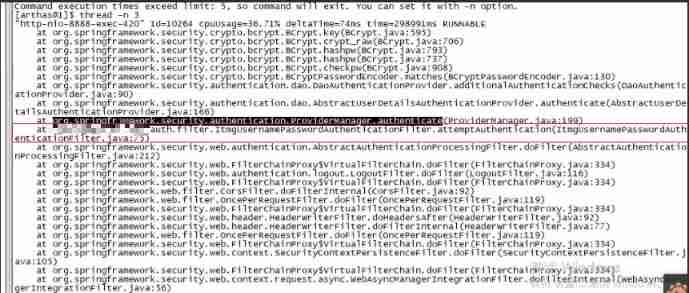
Here is the business code of the program .
therefore trace attemptAuthentication This method .
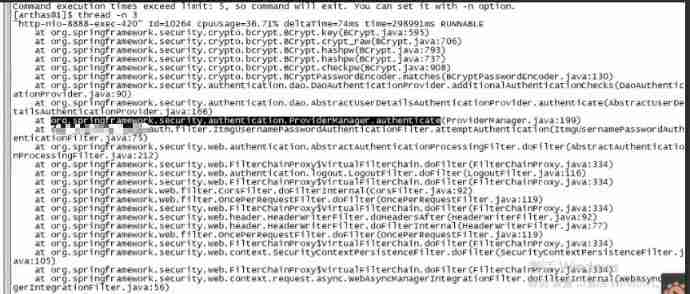
next trace authenticate This method .

Follow it layer by layer , Finally came here :
Since the crypt_raw The method takes a long time , Then decompile the source code to see what this paragraph is .

As you can see, here is an encryption algorithm BCrypt, So the conclusion is obvious BCrypt Although the encryption algorithm has high security , But the performance is poor .
● demo verification
Use here SpringBoot Realization MD5 Encryption and BCrypt Encrypted instance .
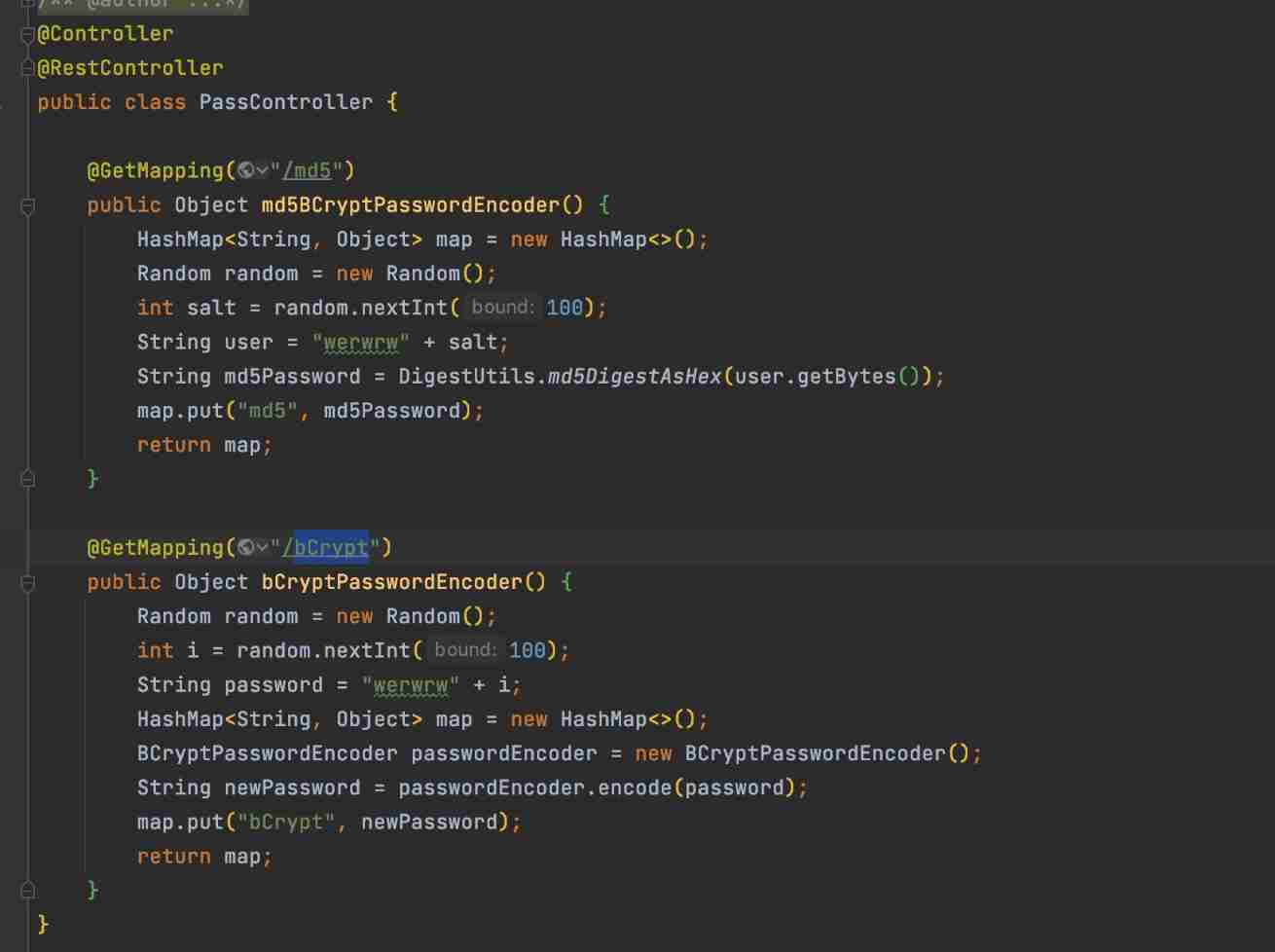
JMeter Concurrent 20 MD5 Encryption result :

JMeter Concurrent 20 BCrypt Encryption result :

● Suggested optimization direction
Here's an explanation ,Bcrypt When encrypting , every time HASH The values are different , So it's very slow !
What exactly is Bcrypt Algorithm , You can refer to this article :https://www.jianshu.com/p/2b131bfc2f10
So that's the analysis , The optimization scheme is actually clear , That is to use faster encryption , Or remove the encryption algorithm .
边栏推荐
- 原型图设计
- Yyds dry inventory comparison of several database storage engines
- Communication between microservices
- Linear regression and logistic regression
- Redis SDS principle
- Pure QT version of Chinese chess: realize two-man, man-machine and network games
- 故障分析 | MySQL 耗尽主机内存一例分析
- [Yu Yue education] basic reference materials of digital electronic technology of Xi'an University of Technology
- 【paddle】加载模型权重后预测报错AttributeError: ‘Model‘ object has no attribute ‘_place‘
- Daily question brushing plan-2-13 fingertip life
猜你喜欢
Fault analysis | analysis of an example of MySQL running out of host memory
Web security SQL injection vulnerability (1)
Game theory matlab

codeforces每日5题(均1700)-第六天
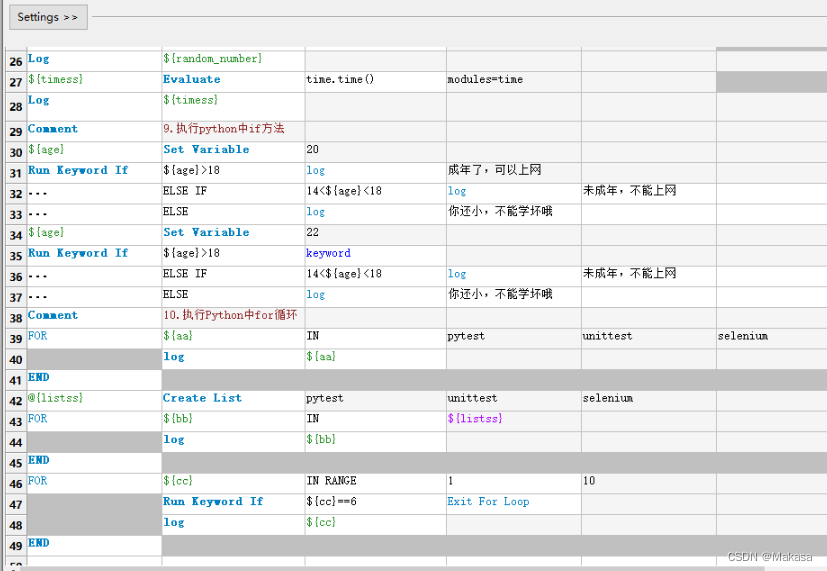
RobotFramework入门(一)简要介绍及使用
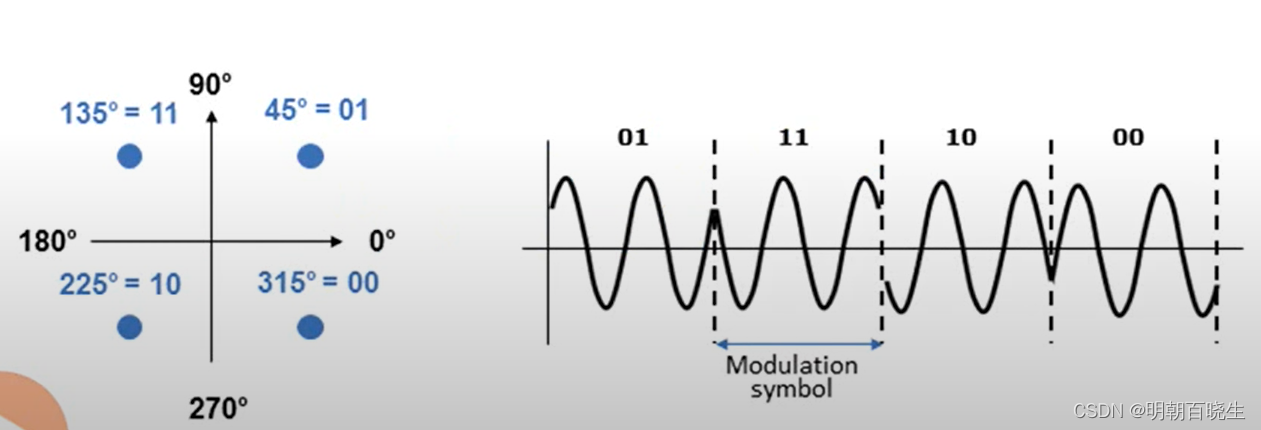
NR modulation 1
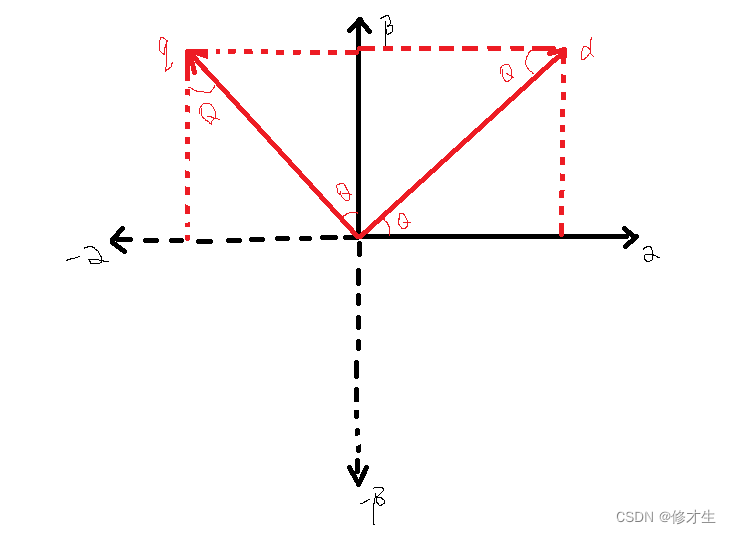
Derivation of anti Park transform and anti Clarke transform formulas for motor control
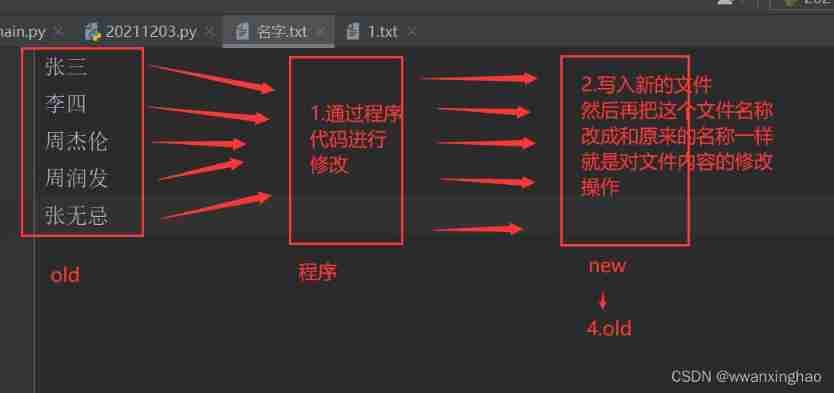
4. File modification
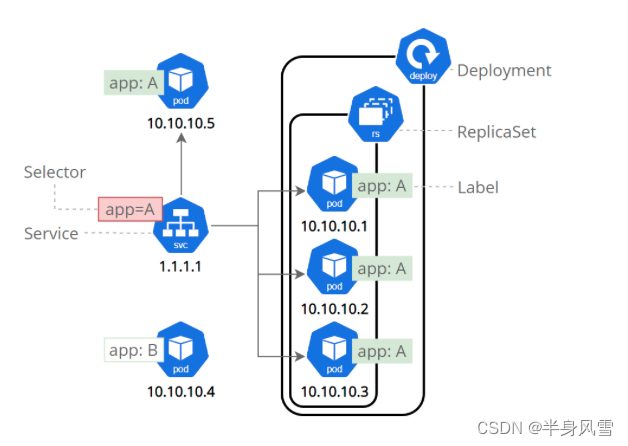
【 kubernets series】 a Literature Study on the Safe exposure Applications of kubernets Service

Reverse repackaging of wechat applet
随机推荐
[Chongqing Guangdong education] higher mathematics I reference materials of Southwest Petroleum University
Analyze 菜单分析
How to improve the enthusiasm of consumers when the member points marketing system is operated?
Who is the winner of PTA
JS regular filtering and adding image prefixes in rich text
Descriptor implements ORM model
Pat 1046 shortest distance (20 points) simulation
Which ecology is better, such as Mi family, graffiti, hilink, zhiting, etc? Analysis of five mainstream smart brands
Web security SQL injection vulnerability (1)
NR modulation 1
I sorted out a classic interview question for my job hopping friends
Introduction to robotframework (III) Baidu search of webui automation
MySQL advanced notes
Universal crud interface
Data and Introspection__ dict__ Attributes and__ slots__ attribute
2345 file shredding, powerful file deletion tool, unbound pure extract version
js 正则过滤和增加富文本中图片前缀
07 singleton mode
电机控制反Park变换和反Clarke变换公式推导
淘宝焦点图布局实战