当前位置:网站首页>[learn microservices from 0] [03] explore the microservice architecture
[learn microservices from 0] [03] explore the microservice architecture
2022-07-07 12:46:00 【lpruoyu】
Continuous learning & Ongoing update …
Keep breaking away
【 from 0 Start learning about microservices 】【03】 Explore the microservice architecture
A normal service invocation process
First, the service provider ( It's the service provider ) In a certain format The service description , towards Registry Center Registration service , State what services you can provide and what the address of the service is , Complete service release .
Next, serve consumers ( It's the party that invokes the service ) Ask the registry , Query the address of the service to be called , Then, a request is made to the service provider with the agreed communication protocol , After getting the request result, parse the result according to the agreed protocol .
And during the invocation of the service , Service requests take time 、 The call volume, success rate and other indicators will be recorded as monitor , The link information of the call will be recorded , be used for Fault location and problem tracking . in the meantime , If the call fails , You can try again Service governance Means to ensure the success rate .
To sum up , Microservices architecture , Service invocation relies on the following basic components : The service description 、 Registry Center 、 Service Framework 、 Service monitoring 、 Service tracking 、 Service governance
The service description
The first problem to be solved by service invocation is how to describe the service externally . such as , You have provided a service , What is the service name of this service ? What information needs to be provided to call this service ? What format is the result returned by calling this service ? How to analyze ? These are the problems to be solved by the service description .
Common service descriptions include RESTful API、XML The configuration and IDL There are three kinds of documents .
among ,RESTful API The method is usually used for HTTP Service description of the agreement , And often Wiki perhaps Swagger To manage .
XML Configuration mode is mostly used as RPC Service description of the agreement , adopt *.xml Configuration file to define the interface name 、 Parameters and return value types .
IDL File mode is usually used for Thrift and gRPC In this kind of cross language service invocation framework , such as gRPC It is through Protobuf File to define the interface name of the service 、 Parameters and the data structure of the return value .
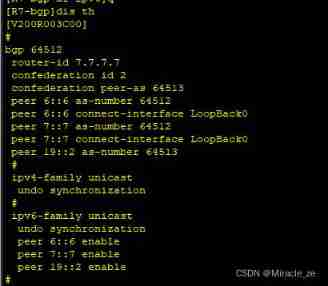
Registry Center
With the interface description of the service , The next step is to solve the problem of service publishing and subscription , That means you provide a service , How to let external people who want to call your service know . At this time, you need a role similar to the registry , Service providers register their services and addresses with the registry , The service consumer queries the registry for the address of the service to be called , Then make a request .
In general , The workflow of the registry is :
The service provider at startup , Register your own service with the registry according to the publishing information configured in the service publishing file .
Service consumers at startup , According to the service information configured in the consumer profile, subscribe to the registry for the services you need .
The registry returns the service provider address list to the service consumer .
When the service provider changes , For example, nodes are added or destroyed , The registry notifies the service consumer of the change .
Service Framework
Through the registry , The service consumer can get the address of the service provider , When you have an address, you can initiate a call . But before you start the call, you need to solve the following problems .
What protocol is used for service communication ? That is to say, what kind of protocol is used for network communication between service provider and service consumer , It's four layers TCP、UDP agreement , Or seven layers HTTP agreement , Or other agreements ?
What is the method of data transmission ? That is to say, which method is adopted for data transmission between service provider and service consumer , Synchronous or asynchronous , It's on a single connection , Or multiplexing .
What format does data compression use ? Data transmission usually compresses data , To reduce the amount of data transmitted over the network , Thus reducing bandwidth consumption and network transmission time , For example, the common JSON serialize 、Java Object serialization and Protobuf Serialization, etc .
…
This is the work of the service framework
Service monitoring
Once the service consumer and service provider can normally initiate service invocation , You need to monitor the call , To find out if the service is normal . Generally speaking , Service monitoring mainly includes three processes .
Index collection . It is to collect the time-consuming and successful requests of each service call , And upload it to the centralized data processing center .
Data processing . With the time-consuming and successful information of each call , You can calculate the number of service requests per second 、 Average time and success rate .
Data presentation . Data collection , After processing , It also needs to be displayed in a friendly way , In order to play a value . The data is usually displayed in Dashboard Panel , And every 10s Auto refresh at equal intervals , Used for business monitoring and alarm etc .
Service tracking
In addition to the need to monitor service invocation , You also need to record every link that the service calls through , For problem tracking and fault location .
The working principle of service tracking is as follows :
Before the service consumer initiates the call , Will generate a... Locally according to certain rules requestid, When the call is initiated , take requestid As part of the request parameters , Pass it on to the service provider .
After the service provider receives the request , Record the requested requestid, Then process the request . If the service provider continues to request other services , It will generate its own requestid, Then put these two requestid All continue to pass down as request parameters .
And so on , Through this layer by layer transmission , One request , No matter how many service calls it depends on finally 、 How many service nodes have passed , Can be generated through the first requestid Concatenate all nodes , So as to achieve the purpose of service tracking .
Service governance
Service monitoring can find problems , Service tracking can locate the problem , And solving the problem depends on Service Management . Service governance is to ensure that in all kinds of unexpected situations , Service calls still work .
In the production environment , You should often encounter the following situations .
Single machine failure . Usually encounter single machine failure , All rely on operation and maintenance to find and restart services or remove faulty nodes from the line . However, the larger the cluster , The more likely it is to encounter single machine failure , When the scale of the machine is more than 100 , It is obviously difficult to cope with the traditional human flesh operation and maintenance . Service governance can be achieved through certain strategies , Automatic removal of faulty nodes , There is no need for human intervention , It can ensure that single machine failure will not affect the business .
single IDC fault . You should often hear so and so App, Because of the serious failure that a large number of users cannot use due to the excavation of optical cables during construction . Service governance can be achieved through automatic failover IDC The flow to other normal IDC, Can avoid because of single IDC A large number of businesses affected by the failure .
Dependent services are not available . For example, your service depends on another service , When another service has a problem , It will slow down or even bring down your service . And service governance can be achieved through fusing , In the case of a dependency service exception , Stop calling for a period of time and return to . On the one hand, this ensures that service consumers will not be dragged down , On the other hand, it also reduces the pressure on service providers , To enable it to recover as soon as possible .
The above are the three most common scenarios that require the introduction of service governance , Of course, there are other means of service governance, such as automatic capacity expansion and contraction , It can be used to solve the problem of service capacity .
summary
- These basic components together form a micro service architecture , In the production environment, it is indispensable
- So before introducing microservice architecture , Your team must master the principles of these basic components and have the corresponding development ability .
- In the way of realization , Open source solutions can be introduced ; If there are enough senior technicians , You can also choose to develop each component of the microservice architecture by yourself . But for most small and medium-sized teams , I think using open source implementation is a wiser choice , On the one hand, you can save the investment of relevant technicians and focus more on the business , On the other hand, you can also take fewer detours and step on fewer pits .
- Whether you use open source solutions or develop your own , Must understand the working principle of each component and be able to carry out secondary development on this basis .
Reference resources
Geek time : from 0 Start learning about microservices -- First line practical experience of microblog service experts
The end of this paper , Thank you for your attention and support !
边栏推荐
- ip2long与long2IP 分析
- Sorting, dichotomy
- AirServer自动接收多画面投屏或者跨设备投屏
- Day-20 file operation, recursive copy, serialization
- 普乐蛙小型5d电影设备|5d电影动感电影体验馆|VR景区影院设备
- Idea 2021 Chinese garbled code
- Guangzhou held work safety conference
- OSPF exercise Report
- IPv6 experiment
- Talk about four cluster schemes of redis cache, and their advantages and disadvantages
猜你喜欢
随机推荐
leetcode刷题:二叉树21(验证二叉搜索树)
SQL lab 21~25 summary (subsequent continuous update) (including secondary injection explanation)
Configure an encrypted web server
Cookie
ip2long与long2IP 分析
Preorder, inorder and postorder traversal of binary tree
About sqli lab less-15 using or instead of and parsing
Talk about four cluster schemes of redis cache, and their advantages and disadvantages
Master formula. (used to calculate the time complexity of recursion.)
普乐蛙小型5d电影设备|5d电影动感电影体验馆|VR景区影院设备
Several ways to clear floating
Utiliser la pile pour convertir le binaire en décimal
Day-20 file operation, recursive copy, serialization
Day-15 common APIs and exception mechanisms
用mysql查询某字段是否有索引
【二叉树】删点成林
test
[statistical learning method] learning notes - support vector machine (Part 2)
How much does it cost to develop a small program mall?
Common knowledge of one-dimensional array and two-dimensional array

![[爬虫]使用selenium时,躲避脚本检测](/img/3a/85ea729be2aa76c3de4a822ca6939b.png)