当前位置:网站首页>[vulnerability warning] cve-2022-26134 conflict Remote Code Execution Vulnerability POC verification and repair process
[vulnerability warning] cve-2022-26134 conflict Remote Code Execution Vulnerability POC verification and repair process
2022-07-05 16:09:00 【yuanfan2012】
【 Vulnerability warning 】CVE-2022-26134 Confluence Remote code execution vulnerability POC Verification and repair process
One 、 Vulnerability Details
Atlassian Confluence yes Atlassian Professional products of the company wiki Program . It can be used as a tool for knowledge management , It enables collaboration and knowledge sharing among team members .
2022 year 6 month 3 Japan ,Atlassian Official announcement , Disclosure exists CVE-2022-26134 Confluence Remote Code Execution Vulnerability wild attack vulnerability event . Vulnerability exploitation does not require identity authentication , It can directly execute arbitrary code remotely in the foreground .
Vulnerability Details :
https://confluence.atlassian.com/doc/confluence-security-advisory-2022-06-02-1130377146.html
Atlassian It's official Confluence Server and Data Center OGNL Inject holes (CVE-2022-26134) Safety notice of , Remote attackers without authentication , Constructible OGNL Expression injection , Realize in Confluence Server or Data Center Execute arbitrary code on ,CVSS The score is 10.
Currently, the details of this vulnerability are PoC Has been publicly disclosed , And it is detected that there is wild utilization . Please take measures for protection as soon as possible .
( Click to enlarge the picture )
Two 、 Vulnerability detection
1、 Manual inspection
Users can view the current Confluence Is the version within the affected range , Check whether the current service is affected by this vulnerability .
Click on the image , choice “ About Confluence”, You can view the current version .
( Click to enlarge the picture )
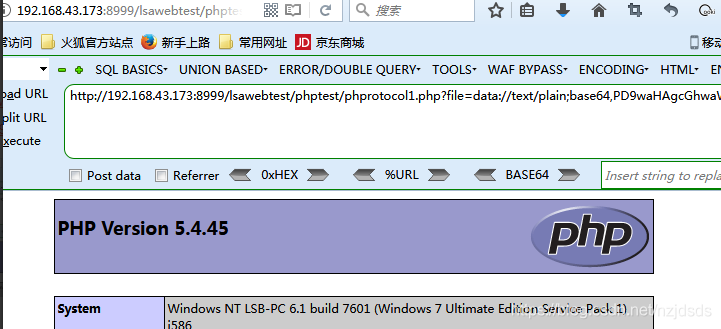
2、POC testing
As shown in the figure below ,POC Script for attack testing
It can be seen that arbitrary code execution can be carried out , Get it directly to the server Shell Background permissions
( Click to enlarge the picture )
3、 ... and 、 Vulnerability protection measures
3.1 Officially upgrade to the safe version
The official recommends that users upgrade to the latest version , To ensure the security and stability of the service .
( Click to enlarge the picture )
Download link :https://www.atlassian.com/software/confluence/download-archives
3.2、 Temporary protective measures
about Confluence 7.15.0 - 7.18.0:aaa
( Click to enlarge the picture )
about Confluence 7.0.0 - Confluence 7.14.2:
( Click to enlarge the picture )
disclaimer : The above vulnerability information is collected on the Internet , If there is something wrong , Please kindly understanding . If there is infringement , Please contact the author of this article to delete .
Four 、 Vulnerability repair process practice
Let's say 7.4.1 Version as an example , Use temporary protective measures to repair
First download the following three files and upload them to confluence The server
https://packages.atlassian.com/maven-internal/opensymphony/xwork/1.0.3-atlassian-10/xwork-1.0.3-atlassian-10.jar
https://packages.atlassian.com/maven-internal/opensymphony/webwork/2.1.5-atlassian-4/webwork-2.1.5-atlassian-4.jar
https://confluence.atlassian.com/doc/files/1130377146/1137639562/3/1654274890463/CachedConfigurationProvider.class
Repair process
[[email protected] ~]# cd /opt/CVE-2022-26134_repair/
[[email protected] CVE-2022-26134_repair]# ll
total 524
-rw-r--r--. 1 root root 7186 Jun 5 10:55 CachedConfigurationProvider.class
-rw-r--r--. 1 root root 352630 Oct 14 2021 webwork-2.1.5-atlassian-4.jar
-rw-r--r--. 1 root root 170369 Jun 2 16:39 xwork-1.0.3-atlassian-10.jar
[[email protected] CVE-2022-26134_repair]#
[[email protected] CVE-2022-26134_repair]#
[[email protected] CVE-2022-26134_repair]#
[[email protected] CVE-2022-26134_repair]# cd /opt/atlassian/confluence/
[[email protected] confluence]# ll
total 1340
-rw-r--r--. 1 root root 975517 Jun 5 10:33 atlassian-agent.jar
drwxr-xr-x. 3 root root 4096 Jun 5 10:35 bin
-rw-r--r--. 1 root root 19540 Jun 11 2020 BUILDING.txt
drwxr-xr-x. 3 root root 4096 Jun 5 10:31 conf
drwxr-xr-x. 27 root root 4096 Jun 5 10:31 confluence
-rw-r--r--. 1 root root 5545 Jun 11 2020 CONTRIBUTING.md
-rw-r--r--. 1 root root 128417 Jun 5 10:31 install.reg
drwxr-xr-x. 7 root root 4096 Jun 5 10:31 jre
drwxr-xr-x. 2 root root 4096 Jun 5 10:31 lib
-rw-r--r--. 1 root root 58153 Jun 11 2020 LICENSE
drwxr-xr-x. 2 root root 69632 Jun 5 10:31 licenses
drwx------. 2 confluence root 4096 Jun 5 10:35 logs
-rw-r--r--. 1 root root 2401 Jun 11 2020 NOTICE
-rw-r--r--. 1 root root 2291 Jun 11 2020 README.html
-rw-r--r--. 1 root root 3334 Jun 11 2020 README.md
-rw-r--r--. 1 root root 1202 Jun 11 2020 README.txt
-rw-r--r--. 1 root root 7072 Jun 11 2020 RELEASE-NOTES
-rw-r--r--. 1 root root 16738 Jun 11 2020 RUNNING.txt
drwxr-xr-x. 4 root root 4096 Jun 5 10:31 synchrony-proxy
drwx------. 3 confluence root 4096 Jun 5 10:39 temp
-rwx------. 1 root root 13586 Jun 11 2020 uninstall
drwxr-xr-x. 2 root root 4096 Jun 11 2020 webapps
drwx------. 3 confluence root 4096 Jun 5 10:35 work
[[email protected] confluence]# cd confluence/WEB-INF/lib/
[[email protected] lib]# mkdir /opt/old_backup
[[email protected] lib]# mv xwork-1.0.3.6.jar /opt/old_backup/
[[email protected] lib]# mv webwork-2.1.5-atlassian-3.jar /opt/old_backup/
[[email protected] lib]# cp /opt/CVE-2022-26134_repair/xwork-1.0.3-atlassian-10.jar /opt/atlassian/confluence/confluence/WEB-INF/lib/
[[email protected] lib]# cp /opt/CVE-2022-26134_repair/webwork-2.1.5-atlassian-4.jar /opt/atlassian/confluence/confluence/WEB-INF/lib/
[[email protected] lib]#
[[email protected] lib]# cd /opt/atlassian/confluence/confluence/WEB-INF/classes/com/atlassian/confluence/setup/
[[email protected] setup]# ll
total 732
-rw-r--r--. 1 root root 280 Jun 11 2020 atlassian-bundled-plugins.zip
-rw-r--r--. 1 root root 737335 Jun 11 2020 demo-site.zip
-rw-r--r--. 1 root root 15 Jun 11 2020 hsqldb-server.acl
[[email protected] setup]# mkdir webwork
[[email protected] setup]# cd webwork/
[[email protected] webwork]# cp /opt/CVE-2022-26134_repair/CachedConfigurationProvider.class ./
[[email protected] webwork]#
( Click to enlarge the picture )
restart confluence service
/opt/atlassian/confluence/bin/stop-confluence.sh
/opt/atlassian/confluence/bin/start-confluence.sh ( Click to enlarge the picture )
POC It can be seen from the verification that code vulnerability execution is no longer possible , The vulnerability was repaired successfully
边栏推荐
- 20.[STM32]利用超声波模块和舵机实现智能垃圾桶功能
- Which keywords will conflict with the abstract keyword
- 漫画:什么是服务熔断?
- Data Lake (XIV): spark and iceberg integrated query operation
- Dataarts studio data architecture - Introduction to data standards
- Verilog realizes the calculation of the maximum common divisor and the minimum common multiple
- 企业级备份软件Veritas NetBackup(NBU) 8.1.1服务端的安装部署
- How difficult is it to pass the certification of Intel Evo 3.0? Yilian technology tells you
- Noi / 1.3 01: a+b problem
- 20. [stm32] realize the function of intelligent garbage can by using ultrasonic module and steering gear
猜你喜欢

Five common negotiation strategies of consulting companies and how to safeguard their own interests

降本40%!Redis多租户集群的容器化实践
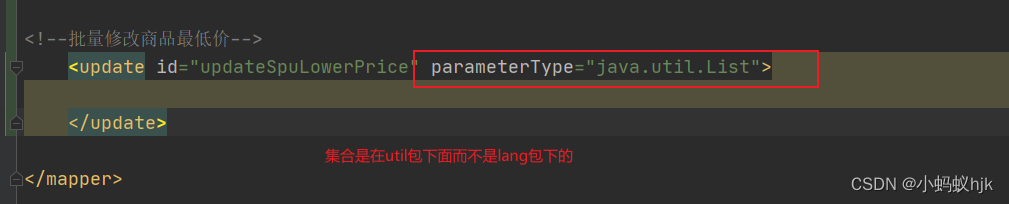
项目sql中批量update的时候参数类型设置错误
![[Netease Yunxin] research and practice of super-resolution technology in the field of real-time audio and video](/img/69/3aedcdafb2b4e83087dc1ce593dc38.png)
[Netease Yunxin] research and practice of super-resolution technology in the field of real-time audio and video
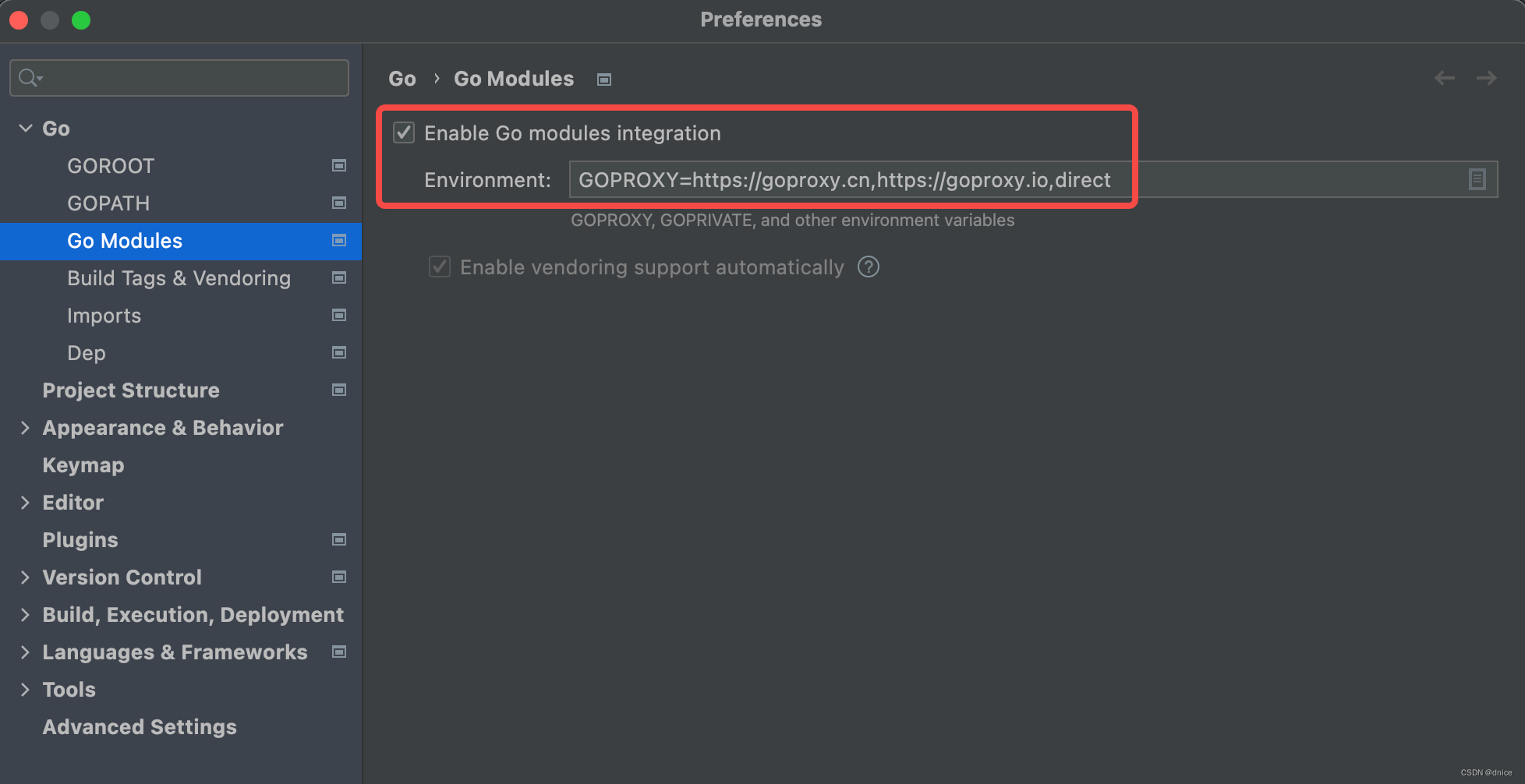
【簡記】解决IDE golang 代碼飄紅報錯
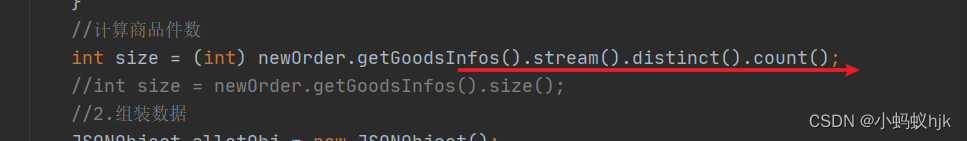
List de duplication and count the number

五种常见的咨询公司谈判策略以及如何维护自己的利益
CISP-PTE之PHP伪协议总结
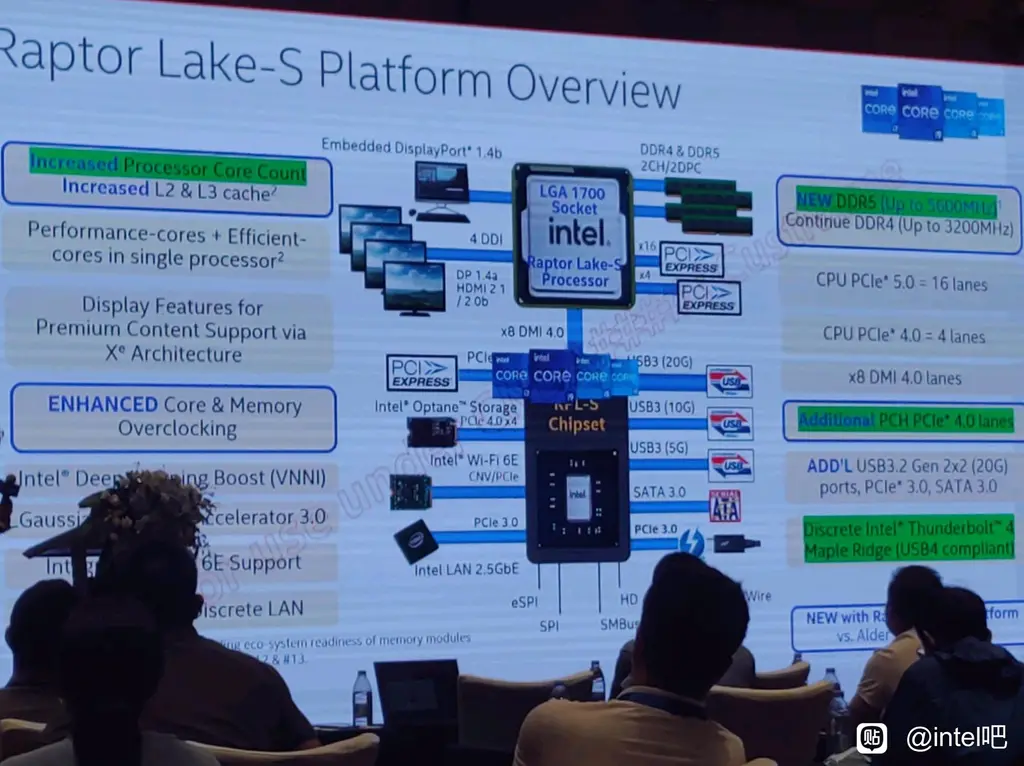
Intel 13th generation Raptor Lake processor information exposure: more cores, larger cache
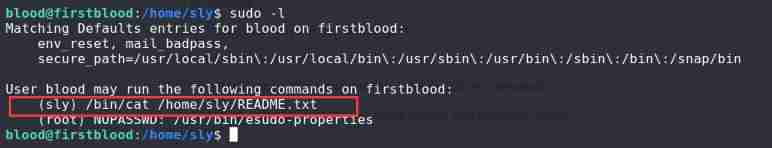
vulnhub-FirstBlood
随机推荐
Modify PyUnit_ Time makes it support the time text of 'xx~xx months'
求解汉诺塔问题【修改版】
Data communication foundation smart_ Link_&_ Monitor_ Link
视觉体验全面升级,豪威集团与英特尔Evo 3.0共同加速PC产业变革
How difficult is it to pass the certification of Intel Evo 3.0? Yilian technology tells you
This article takes you through the addition, deletion, modification and query of JS processing tree structure data
MySQL table field adjustment
ES6 deep - ES6 class class
18.[stm32] read the ROM of DS18B20 temperature sensor and realize multi-point temperature measurement
Noi / 1.5 06: element maximum span value of integer sequence
17.[STM32]仅用三根线带你驱动LCD1602液晶
五种常见的咨询公司谈判策略以及如何维护自己的利益
List uses stream flow to add according to the number of certain attributes of the element
Cartoon: what is MapReduce?
Data communication foundation ACL access control list
Quick completion guide for manipulator (IX): forward kinematics analysis
sql中set标签的使用
修改pyunit_time使得其支持‘xx~xx月’的时间文本
《MongoDB入门教程》第04篇 MongoDB客户端
项目中批量update